当前位置:网站首页>Explain the volatile keyword
Explain the volatile keyword
2022-07-01 22:55:00 【Keyboard singer】
One 、 brief introduction
1.Volatile Memory semantics
1. When you write a volatile variable ,JMM The shared variable value in the local memory corresponding to the thread will be immediately refreshed back to the main memory .
2. When reading a volatile variable ,JMM Will set the local memory corresponding to this thread to be invalid , Go back to main memory and read the latest shared variable .
3. therefore volatile The write memory semantics of is to refresh directly into main memory , The memory semantics of reading is to read directly from main memory .
2. Two characteristics
1. visibility : Flush back to main memory immediately after writing and send notification in time , You can go to the main memory to get the latest version , The previous changes are visible to all subsequent threads !
2. Prohibit command rearrangement : Reordering is a means by which compiler and processor reorder instruction sequences in order to optimize program performance , Sometimes it will change the sequence of program statements . There is no data dependency , You can reorder ; There is a data dependency , No reordering . But the rearranged instructions can never change the original serial semantics ! This must be taken into account in concurrent design !
3. The above prohibition of instruction rearrangement is based on memory barrier :
Roughly divided into two kinds
1. Reading barrier : Insert a read barrier before reading instructions , Let working memory or CPU The cached data in the cache is invalid , Go back to jade memory to get the latest data .
2. Write barriers : Insert a write barrier after writing instructions , Force data written to the buffer to be flushed back to main memory .
stay Java Level of Unsafe Classes have the following native Method :
边栏推荐
- twenty million two hundred and twenty thousand seven hundred and one
- Using securecrtportable to remotely connect virtual machines
- 【无标题】
- 正则系列之组和范围(Groups and Ranges)
- Favorite transaction code management tool in SAP GUI
- Delete AWS bound credit card account
- Happy number [fast and slow pointer of ring PROBLEMS]
- Pytorch nn.functional.unfold()的简单理解与用法
- 447 Bili Bili noodles warp 1
- There is no signal in HDMI in computer games caused by memory, so it crashes
猜你喜欢

ESP自动下载电路设计

分享一个一年经历两次裁员的程序员的一些感触

Genicam gentl standard ver1.5 (4) Chapter 5 acquisition engine
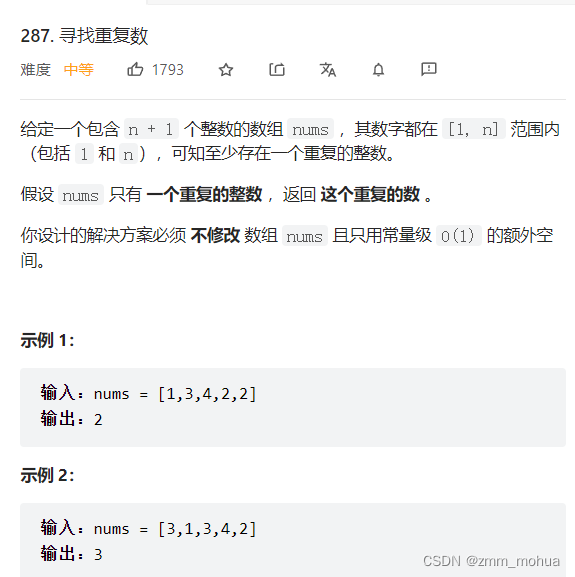
leetcode - 287. Find duplicates
14年本科毕业,3个月转行软件测试月薪13.5k,32的岁我终于找对了方向

Réimpression de l'article csdn
Turn -- the underlying debugging principle of GDB is so simple

MySQL -- deduction of index storage model

Appium自动化测试基础 — 补充:Desired Capabilities参数介绍

Stimulate new kinetic energy and promote digital economy in multiple places
随机推荐
pytorch训练自己网络后可视化特征图谱的代码
利用SecureCRTPortable远程连接虚拟机
Arlo's thinking after confusion
Selection of all-optical technology in the park - Part 2
[literacy] deep / shallow, local / global features in machine learning image processing
leetcode - 287. Find duplicates
Deep learning -- data operation
Rust language - Introduction to Xiaobai 05
Origin2018 installation tutorial "recommended collection"
Explain kubernetes network model in detail
SAP 智能机器人流程自动化(iRPA)解决方案分享
Configure filter
Reprint CSDN article operation
使用 Three.js 实现'雪糕'地球,让地球也凉爽一夏
Using securecrtportable to remotely connect virtual machines
SAP GUI 里的收藏夹事务码管理工具
[daily training] 326 Power of 3
Resttemplate remote call tool class
Metauniverse may become a new direction of Internet development
聊一聊Zabbix都监控哪些参数