当前位置:网站首页>How to keep the source code confidential in the development under the burning scenario
How to keep the source code confidential in the development under the burning scenario
2022-08-04 04:15:00 【Cnsidna.No.1】
How to keep source code confidential in the development of burning scenarios
All kinds of embedded R&D and platform software R&D industries have their own core data, core documents, user data and other sensitive information, which have the following commonalities:
It belongs to the core confidential information, if it is leaked, it will have a bad impact
There are many core data types, source code data, and high level of employee computers
A lot of data is in business systems, not files
If it is not controlled, designers and users can easily copy the data through various channels, resulting in leakage.
- Secrets-related methods commonly used by R&D personnel
Because R&D personnel are more proficient in computers than ordinary office personnel, in addition to the common network, email, U disk, QQ and other data diffusion methods, there are many methods that are very easy for R&D personnel (not all listed):
Physical Methods:
Direct connection of the network cable, that is, unplug the network cable from the wall plug and connect it directly to an uncontrolled computer;
boot from winPE, boot from winPE from CD or U disk, or even boot from ISO image directly.
Virtual machine, by installing VMWare virtual machine, use peripheral U disk, network in the virtual machine.
Transfer to other uncontrolled computers, that is, copy the data to other uncontrolled computers in the network, and transfer them
Online upload, bypass the Internet behavior management by building an upload server on the public network
Data warping:
Write a console program, print the code to the DOS console and save the screen information;
Write the code to the Log log file, or write the code to shared memory and then read it away by another program.
Write an inter-process communication program, send the code through inter-process communication methods such as socket, message, LPC, COM, mutex, clipboard, pipeline, etc., and transfer the data away;
Transfer through a web parser such as IIS/Tomcat, publish the code data as a web page, and then save it as a browser after browsing, or simply write a txt box, and copy the code in during initialization;
Peripheral transfer
For embedded development scenarios, you can burn the code to the device through the serial port, U port, and network port to transfer leaks
- SDC Sandbox Anti-Leakage Software
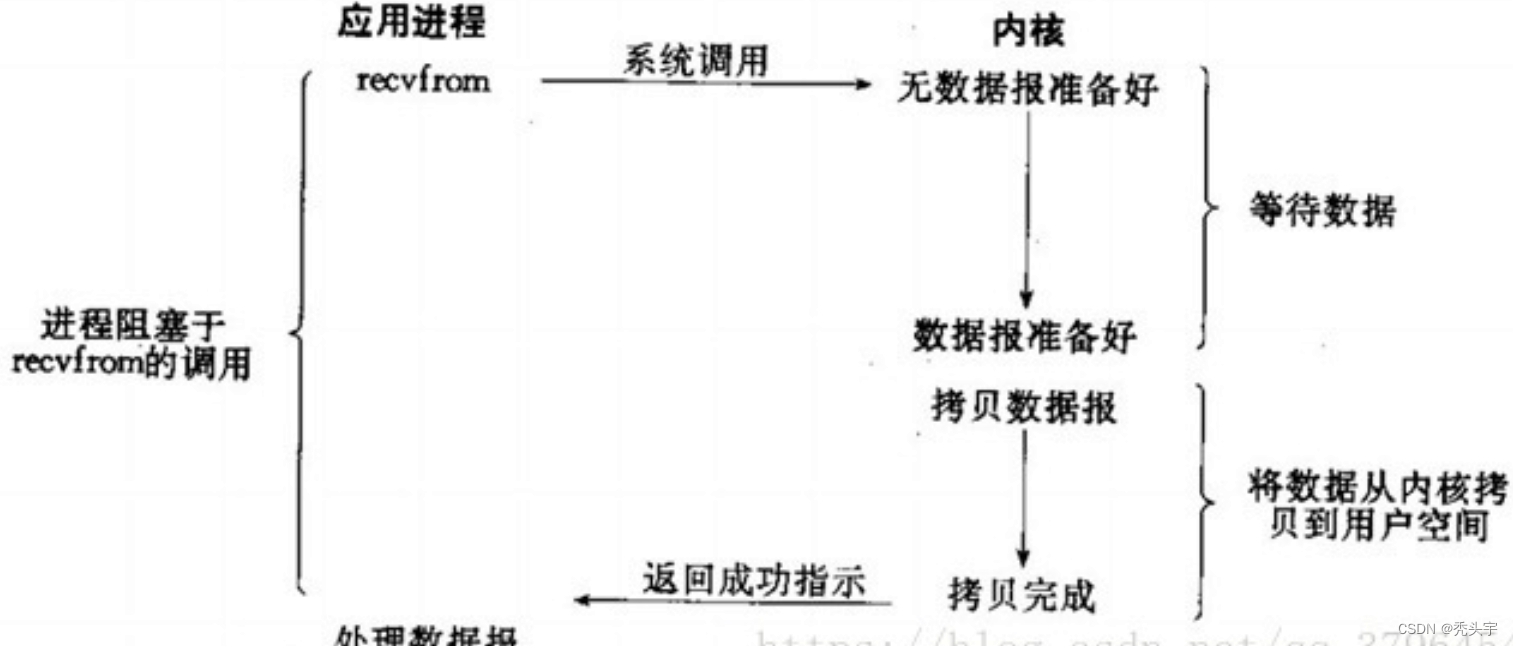
The SDC sandbox anti-leakage product independently developed by Shenxinda adopts the kernel-level defense in depth and is a driver-level anti-leakage software.Without encrypting files, the sandbox is like a container with our confidential information.The files we work on are all in the sandbox.The sandbox is completely isolated from normal computers.You may ask, what should I do if I want to access the Internet, all programs that need to access the Internet are started from the tray, such as browsers, chat software, etc.The SDC sandbox is divided into the following parts: management end, confidential end, file outgoing, and client end.
Management side: sandbox control center, which controls all clients.Control over the client covers all aspects.Then I will cite a few control functions: Anti-screenshot When someone wants to view some confidential information of the company by remote to the employee's computer, the SDC client will control the remote software, and the remote person will see a black screen.However, the computer on the employee's side is working normally.If you can control it, you can let go.Clipboard In sandbox mode, employees want to copy and paste company information such as files to the external network through the clipboard. The SDC sandbox is controlled and can control the maximum number of clipped words.
Confidential: escort the server, ordinary computers have no right to access the confidential server.Only sandbox computers can access, and no encryption is performed on company information, so that information is protected to the greatest extent possible.
Client: normal mode and sandbox mode.All software installations must be in sandbox mode.The job must be in sandbox mode, because all work data is on the encrypted disk, and only the sandbox mode can access the encrypted disk.The sandbox mode is isolated from the outside world.To access the external network, only programs that are started from the tray can access the external network, and follow the principle of only access and no access. Files can be obtained from the external network to the sandbox computer, but to send files from the local computer to the external network, only file approval is required.
File outgoing: A file outgoing system is installed on a computer.The ip of this computer is the address from which the file is sent.Each sandbox employee matches an account to which the file is sent.The specific approval method is not redundant here.

边栏推荐
- 【21天学习挑战赛】图像的旋转问题(二维数组)
- 目标检测-中篇
- 劝退背后。
- 2 Gigabit Optical + 6 Gigabit Electric Rail Type Managed Industrial Ethernet Switch Supports X-Ring Redundant Ring One-key Ring Switch
- JVM Notes
- 2.15 keil使用电脑端时间日期
- y86.第四章 Prometheus大厂监控体系及实战 -- prometheus存储(十七)
- [Medical Insurance Science] To maintain the safety of medical insurance funds, we can do this
- 数据集类型转换—TFRecords文件
- Polygon zkEVM network node
猜你喜欢
随机推荐
2022 Hangzhou Electric Power Multi-School League Game 5 Solution
软件测试如何系统规划学习呢?
7-1 LVS+NAT 负载均衡群集,NAT模式部署
【21天学习挑战赛】顺序查找
帮助企业实现数字化转型成功的八项指导原则
元宇宙“吹鼓手”Unity:疯狂扩局,悬念犹存
Mobile payment online and offline payment scenarios
嵌入式数据库开发编程MySQL(全)
Shell 函数
2003. 每棵子树内缺失的最小基因值 DFS
MySQL query optimization and tuning
Tensors - Application Cases
Reproduce 20-character short domain name bypass
哎,又跟HR在小群吵了一架!
【 observe 】 super fusion: the first mention of "calculate net nine order" evaluation model, build open prosperity of power network
4路双向HDMI综合业务高清视频光端机8路HDMI高清视频光端机
看DevExpress丰富图表样式,如何为基金公司业务创新赋能
typescript type 和 interface 的区别
仿牛客论坛项目梳理
初识Numpy

![The video of machine learning to learn [update]](/img/e7/c9a17b4816ce8d4b0787c451520ac3.png)
![[Medical Insurance Science] To maintain the safety of medical insurance funds, we can do this](/img/d0/6ac51d0d51c907ed0e1578e038fffd.jpg)