当前位置:网站首页>Common penetration tools -goby
Common penetration tools -goby
2022-07-01 09:53:00 【beirry】
Common tools for penetration -Goby
Preface
I haven't updated this column for a long time , Today, let's introduce the tools that are often used :Goby
Novice security friends may not be familiar with this tool , This is mainly used as a tool to scan assets for vulnerabilities , There are many built-in POC( Vulnerability verification ) package , After the test, a detailed report will be sent to the user .
Goby download
goby Link to the official website of :https://gobies.org/
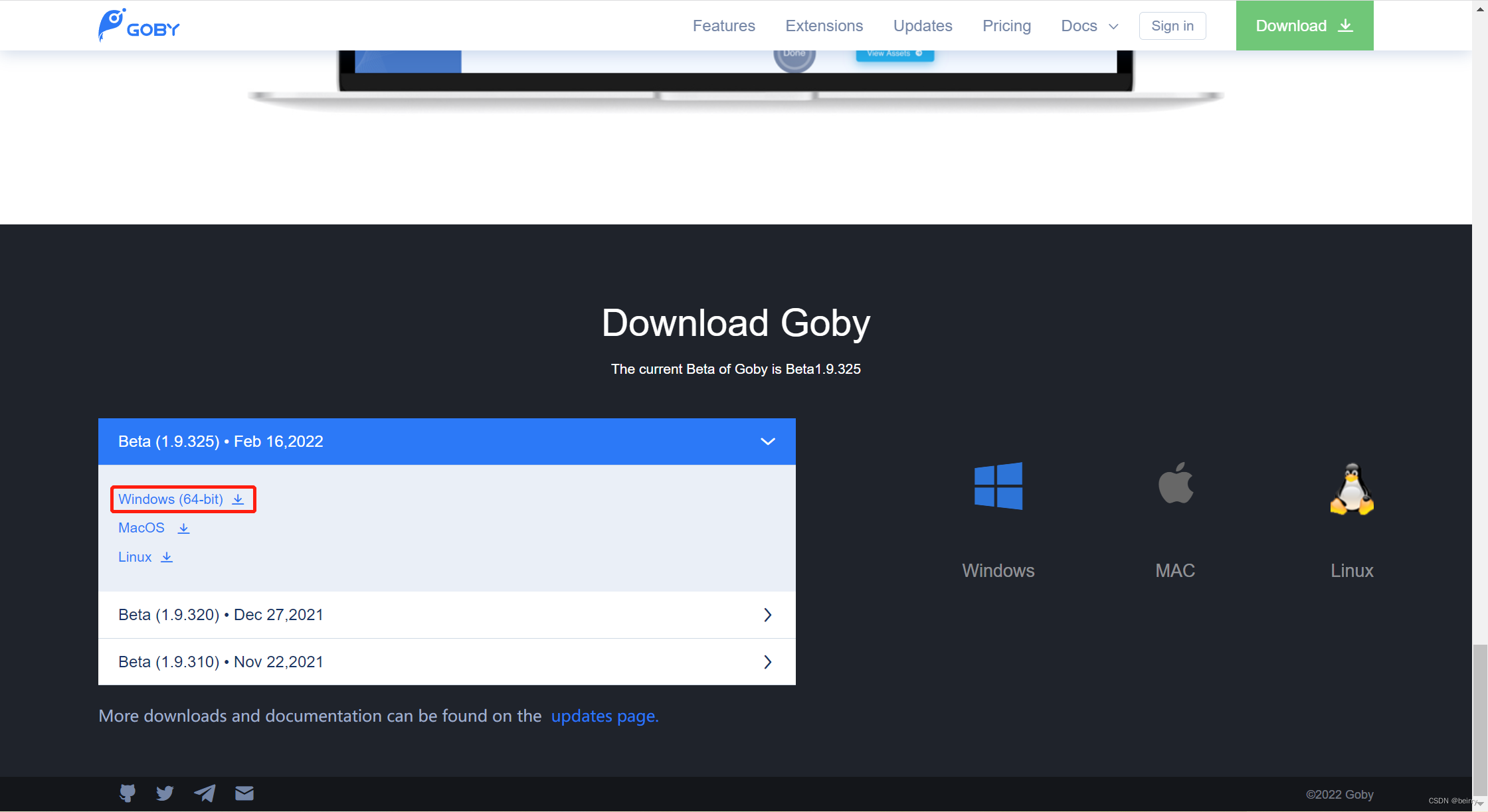
Download the corresponding version according to your own operating system , I am here windows edition , So the download is the first one .
Download and get a compressed package , After unzipping, you can see the following files , open Goby.exe file 
Goby Use
In the lower left corner, you can set the language to Chinese .
New scan task
Click on Scan You can create a scan task .
After establishing the scanning task, you can see the scanning information 
Asset information :
Vulnerability information :
Scan report :
So the above is what you can get from creating a new scanning task , Next, let's talk about components
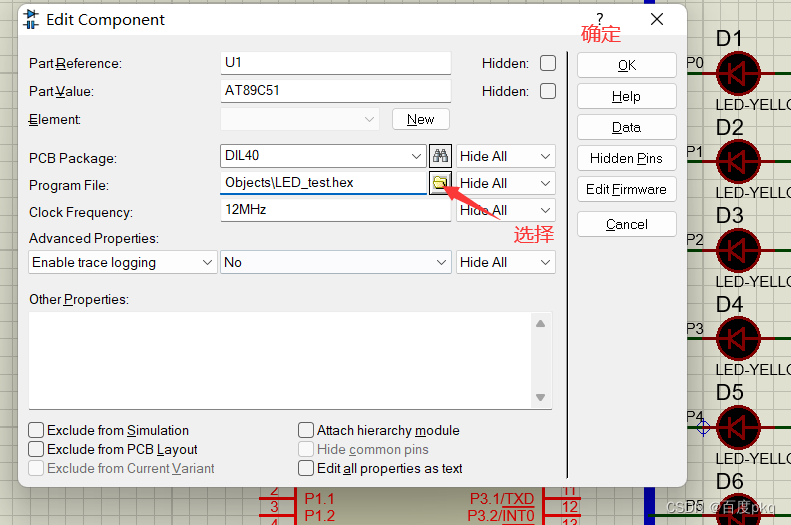
Add the component
Adding components is nothing more than to make us better use Goby, such as fofa Components , Can pass fofa To obtain possible vulnerable hosts in the whole network .
and Xray It can be done to Web Scan the page , Give Way Goby More comprehensive scanning of .
Components are a good thing , Cousins can download components and use them through their own needs .
Goby Red team version
Goby To get the red team version, you can see this article :https://zhuanlan.zhihu.com/p/361351060
Finally, I would like to invite my cousins to do the penetration test , It must be authorized to penetrate , This article is only for learning and communication , If there is any illegal event, it has nothing to do with me .
边栏推荐
- 架构实战营 模块九:设计电商秒杀系统
- Ubuntu系统安装与配置MySQL
- Some tools used in embedded development
- Get the list of a column in phpexcel get the letters of a column
- SQL learning notes (04) - data update and query operations
- 富文本实现插值
- button按钮清除边框
- Strange, why is the ArrayList initialization capacity size 10?
- [unity rendering] customized screen post-processing
- A quietly rising domestic software, low-key and powerful!
猜你喜欢

TC8:UDP_USER_INTERFACE_01-08

Huawei accounts work together at multiple ends to create a better internet life

Cortex M4 systick details

LVGL V8.2字符串显示在Keil MDK上需要注意的事项(以小熊派为例)

遇到女司机业余开滴滴,日入500!

Swag init error: cannot find type definition: response Response

HMS core audio editing service 3D audio technology helps create an immersive auditory feast

Can you afford to buy a house in Beijing, Shanghai, Guangzhou and Shenzhen with an annual salary of 1million?

新数据库时代,不要只学 Oracle、MySQL
【无标题】
随机推荐
SSH服务器拒绝密码,再试一次;PermitRootLogin yes无效问题
Huawei accounts work together at multiple ends to create a better internet life
历史上的今天:九十年代末的半导体大战;冯·诺依曼发表第一份草案;CBS 收购 CNET...
HMS core audio editing service 3D audio technology helps create an immersive auditory feast
Introduction to mt7628k eCos development
In terms of use
数据中台咋就从“小甜甜”变成了“牛夫人”?
Import and export of power platform platform sharepointlist
微信表情符号写入判决书,你发的OK、炸弹都可能成为“呈堂证供”
[untitled]
Problems caused by delete and delete[]
Flinkv1.13实现金融反诈骗案例
请问有没有人知道clickhouse 中 limit语句执行的逻辑,图片中,上面的SQL可以执行成功
Configure load balancing
Strange, why is the ArrayList initialization capacity size 10?
Upload labs for file upload - white box audit
遇到女司机业余开滴滴,日入500!
超标量处理器设计 姚永斌 第4章 分支预测 --4.1 小节摘录
Swag init error: cannot find type definition: response Response
Solution of EPS image blur by latex insertion