当前位置:网站首页>Notes, continuation, escape and other symbols
Notes, continuation, escape and other symbols
2022-07-06 05:14:00 【Cloud C】
List of articles
Annotation symbols
basic dos and don'ts
There are two kinds of annotation symbols :
- C The style is
/* Content */ - C++ The style is
// Content
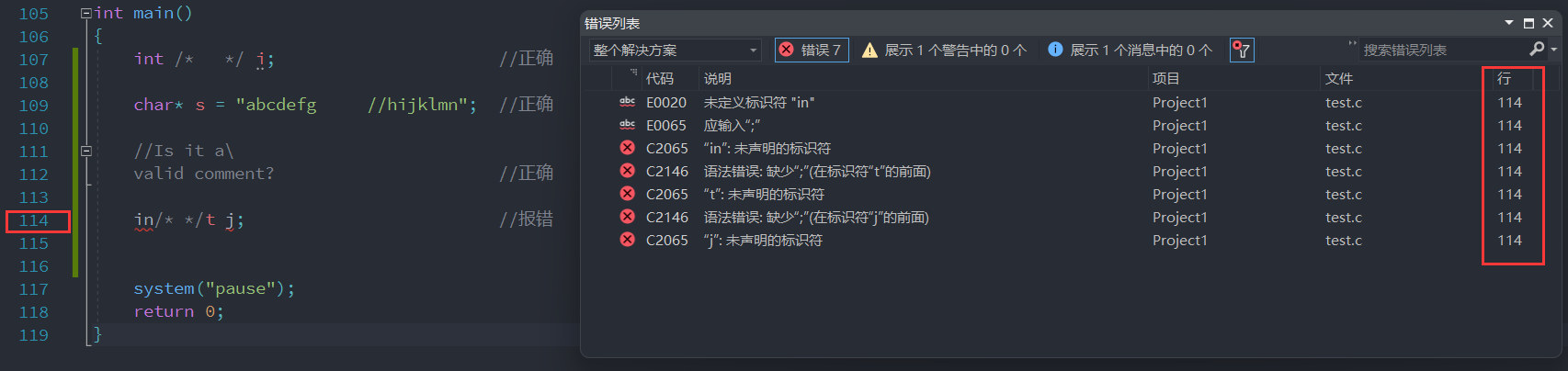
Look at the four situations above , Only the fourth is wrong .
The commented content will be replaced with spaces in the preprocessing stage .
So the fourth situation becomes in t j;, And put keywords int Separation is not supported by the compiler , So there's an error .
You can also see the second situation , Annotation symbols are not valid in strings .
# and define Can there be spaces between ?
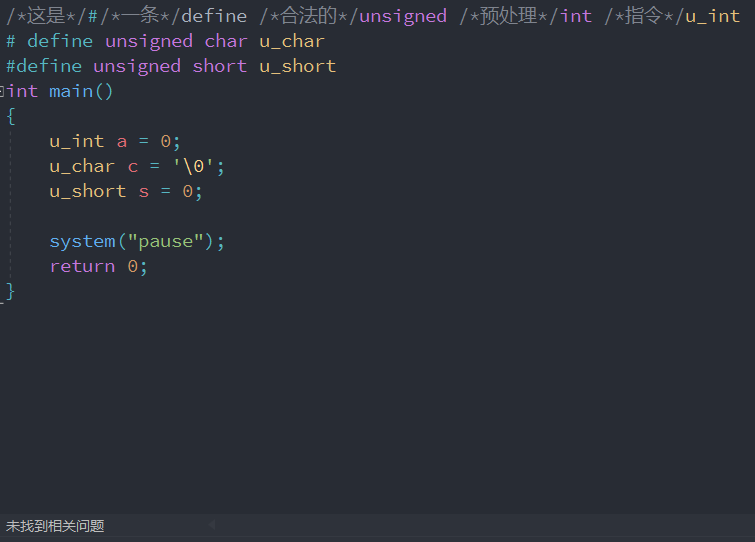
The answer is yes .
C Styles cannot be nested
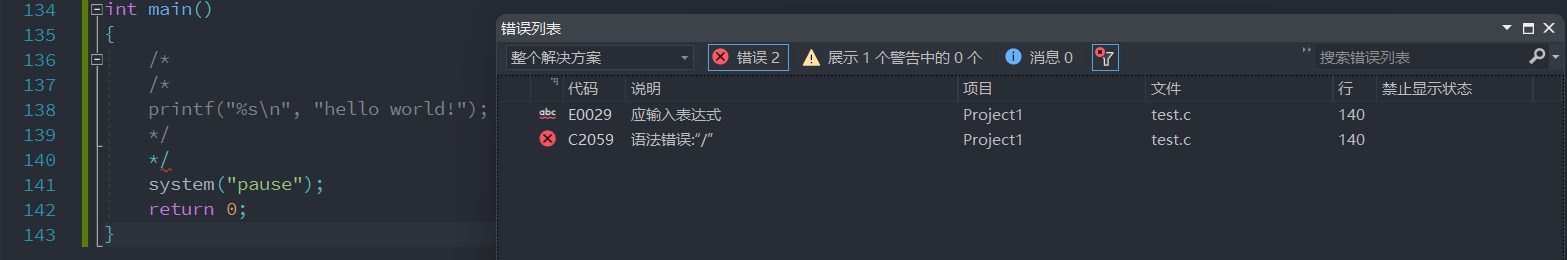
You can see in the 140 There's a mistake , This is because the compiler will only look for the first /* And the first */, therefore C Style annotations cannot be nested .
y = x/*p
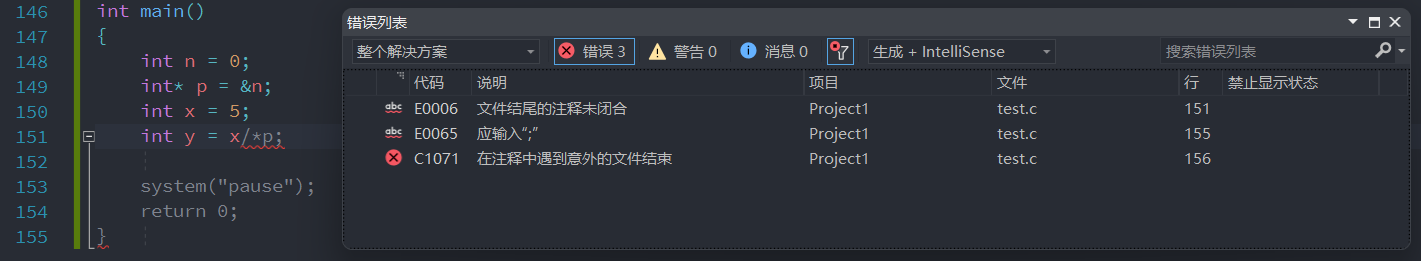
When divided by the pointer , It is very easy to make such mistakes , There are two solutions
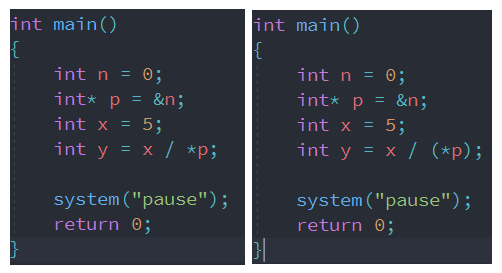
The second bracketed method is strongly recommended .
Basic requirements of notes
The notes should be accurate 、 Understandability , Prevent ambiguity . Wrong annotation is not only useless but also harmful .
Write code and comment , Modify the corresponding comments while modifying the code , To ensure the consistency of comments and code . Comments that are no longer useful should be deleted in time .
Comments are about code “ Tips ”, Not documents . The notes in the procedure should be simple and clear , Too many notes can be dazzling .
A clear statement without comments .
for example :
i++; //i Add 1,i Add 1 Completely superfluous comments .For global data ( Global variables 、 Constant definition, etc ) It must be annotated .
The notes are in English , Try to avoid abbreviations in comments , Especially the less commonly used abbreviations .
Some compilers cannot display Chinese , So when the code that appears in Chinese is opened by the compiler, it will be a mess ( Such compilers are rare nowadays ).
For people with poor English , Or in Chinese , Otherwise, it's better not to write wrong notes in English .
The position of the comment should be adjacent to the code being described , It can be on the same line as the statement , You can also go up , But it can't be placed below . The notes of different fields in the same structure should be aligned .
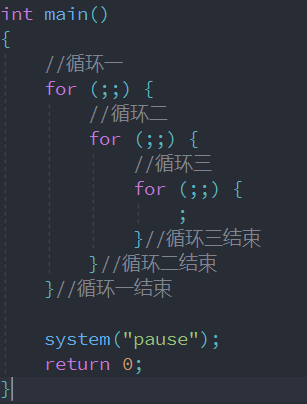
When the code is long , Especially when there are multiple nesting , There should be a note at the end of some paragraphs , Easy to read .
The indentation of comments should be consistent with that of code .
When commenting code snippets, pay attention to “ Why do (why)”, instead of “ How do you do it? (how)”.
Notes explaining how to do it usually stay at the level of programming language , Not to illustrate the problem . Try to explain “ How do you do it? ” The comments of generally do not tell us the intention of the operation , And specify “ How do you do it? ” Comments for are usually redundant .
The unit of value must be noted .
The note should explain what the unit of a certain value means , such as : For length, it must be stated that the unit is millimeter 、 rice 、 Or kilometers .
Comment on the scope of the variable , Especially parameters .
Comment on a series of numerical numbers , Especially when writing the underlying driver ( Such as pin number ).
For function entry / Export data 、 Conditional statements 、 Branch statements give comments .
Conditions and branch statements are often the key to a program to achieve a specific function . For maintenance personnel , Good comments can help better understand the program , Sometimes even better than looking at design documents .
Avoid inserting comments in the middle of a line of code or expression .
Unless necessary , Comments should not be inserted in between code or expressions , Otherwise, it is easy to make the code incomprehensible .
In complex functions , In branch statement 、 Appropriate comments are required after the loop statement ends , It is convenient to distinguish each branch or cycle .
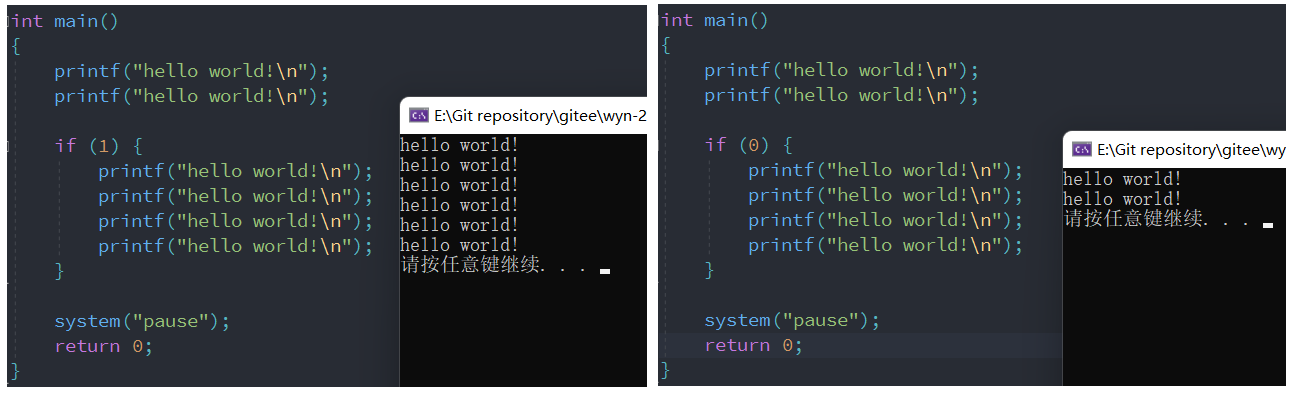
For areas that do not need to be compiled, use conditional compilation .( Not recommended )
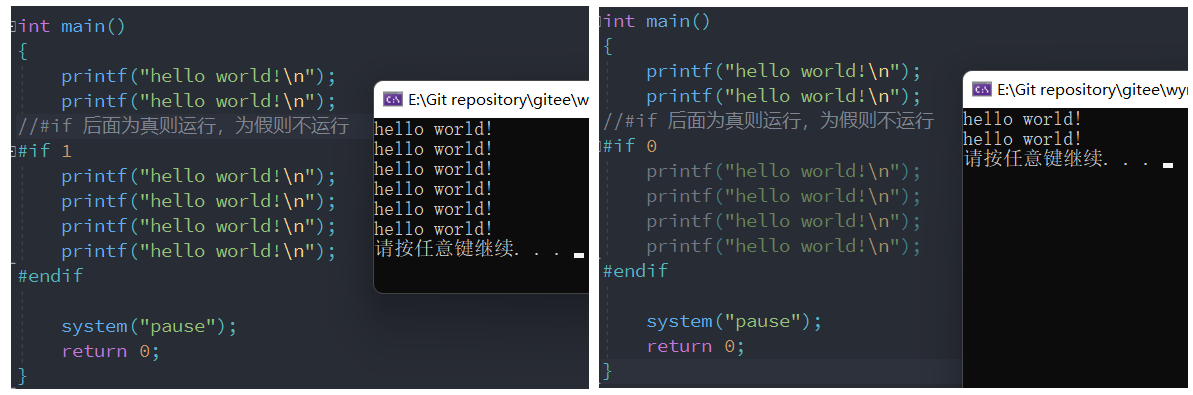
Another is based on if Judge , Processing during code run . Seriously not recommended
Continuation and escape characters
Continuation function
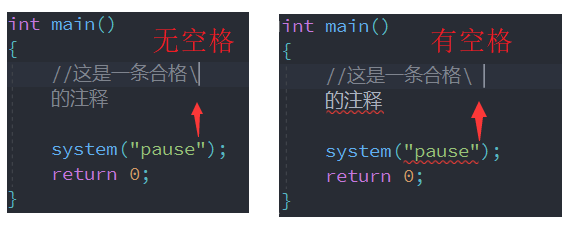
C Use backslash in language \ Identify line breaks . The compiler will remove the backslash , The character following the backslash is automatically continued to the previous line . But notice : No space after backslash . Let's test it :
Be careful. : stay VS2022 in , Sometimes even without \, Line breaks are also effective . But this coding style is not recommended , When such code appears , It is impossible to clearly tell the user whether the code is connected or written incorrectly . therefore , When we need to connect , Be sure to use a continuation \.
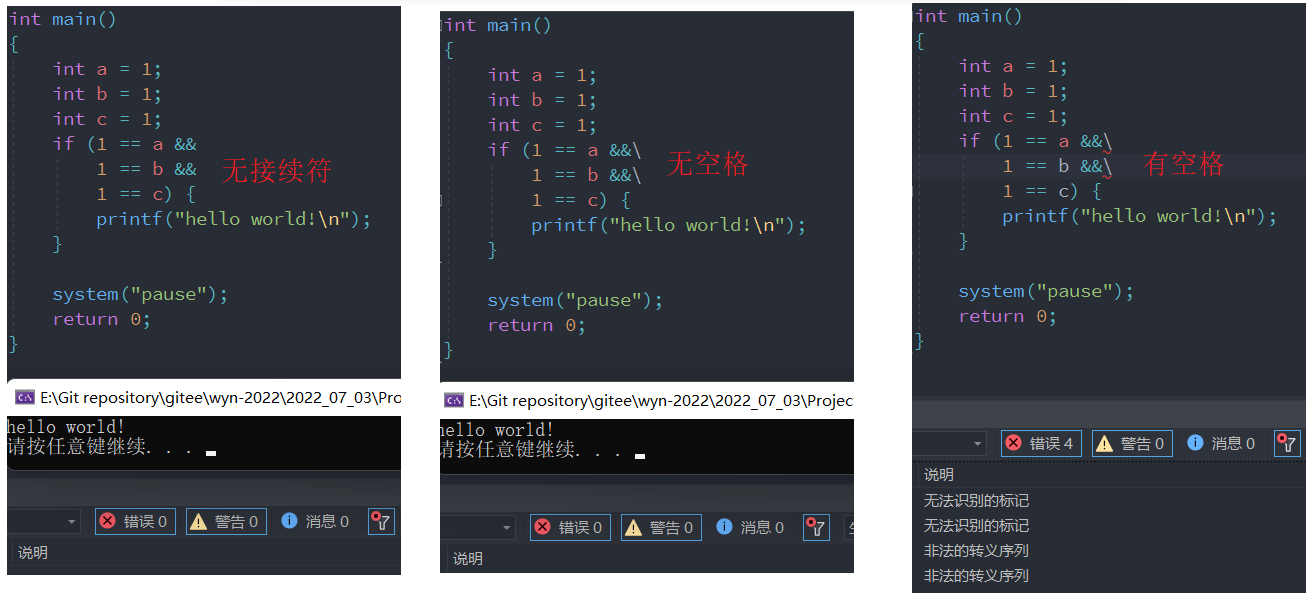
It is incorrect to add a space after the continuation , The effect of not adding a connector is exactly the same as that of adding a connector , But the coding style without connectors is not recommended !
escape
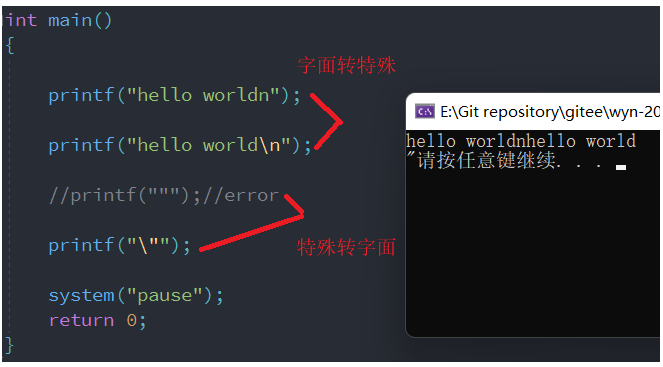
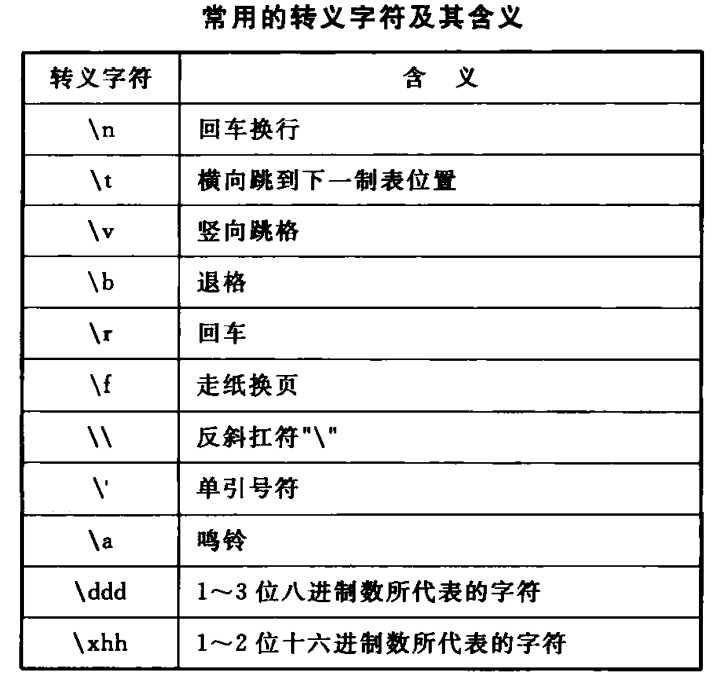
The backslash can be used as a continuation , It can also be used as the start identifier of escape characters .
C in , There are some characters , Is its literal meaning , such as a 、b、c. There are also some characters , Ability means something special , such as “、'、\.
The essential meaning of escape is : Literally to special , Or special to literal .
Single and double quotes
Basic understanding
We know that double quotation marks are all string constants , Single quotation marks are all character constants . To be more precise , Single quotation marks are all integer character constants , Why do you say that , Here's an example .
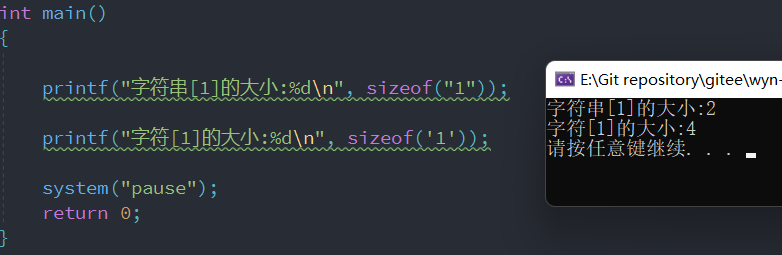
For the size of the string , We must be very clear , There is a hidden at the end of the string \0, So when you calculate the size, you actually calculate two characters 1 and \0, Size is 2. So why is the size of characters not 1 It is 4 Well ?
Actually , When the compiler allocates memory for characters , The allocated size is 4 Bytes , The size of characters is 4 Bytes . So we often say that characters are actually integers .
But character variables are not 4 It is 1, because char The memory size of type is 1, you 're right , We are in the process of assigning character constants to character variables , In fact, they are intercepting , Intercept the low byte of the four bytes of the integer , Then assign it to the character variable . Look at the next example .

Because when intercepting , Is to intercept from the low byte , and char Type variables can only intercept one byte , Therefore, only the character of the low byte of the character constant will be intercepted , There will also be the phenomenon of the above figure .
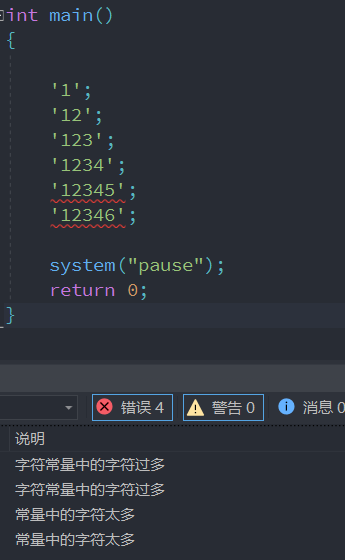
Because the character constant is actually four bytes , in other words , A character constant can only have four characters .
Empty characters and empty strings
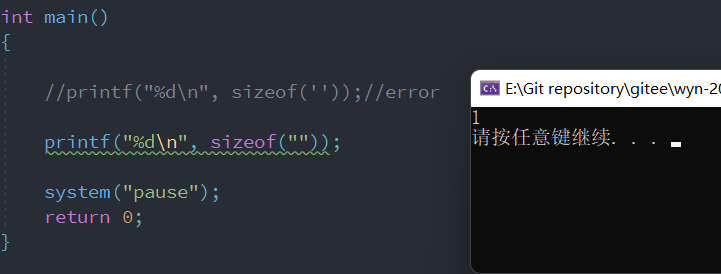
Null character , That is, the character constant is empty , This in itself is meaningless , So the compiler reports an error .
An empty string , But in fact, there is a hidden \0, So empty characters make sense , And the size is 1.
Why do computers need characters
The essence of computer only knows binary , So why do computers need characters ? Doesn't it smell good directly ?
Because computers are designed to solve human problems , But , How do people know that computers solve people's problems ? When the computer outputs binary results , Ordinary people can't understand it directly .
therefore , Why do computers need characters ? The essence is to make people understand .
Then why is it in English ? Doesn't Chinese smell good ?
The earliest computer was invented by Americans , Their language is English , Only by 26 English letters and a bunch of punctuation marks , And computers are just beginning to be invented , Americans only need to solve their problems , So there are now simple characters .
Because computers only know binary , And people only know characters . therefore , There must be a set of rules , Used for binary and character conversion , This is called ASCII clock .

Logical operators
&&
Cascade two ( Multiple ) Logical expression , It has to be true at the same time , The result is true . And &( Bitwise AND ) It's a completely different concept .
||
Cascade two ( Multiple ) Logical expression , At least one must be true , The result is true . And |( Press bit or ) It's a completely different concept .
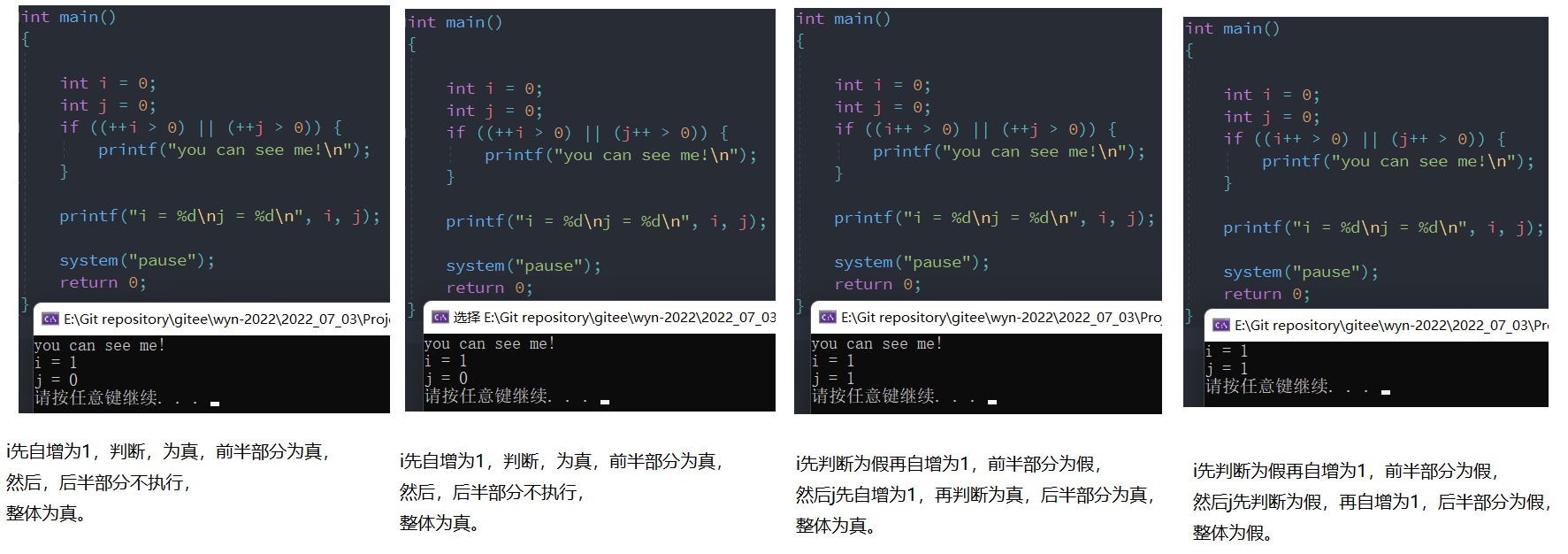
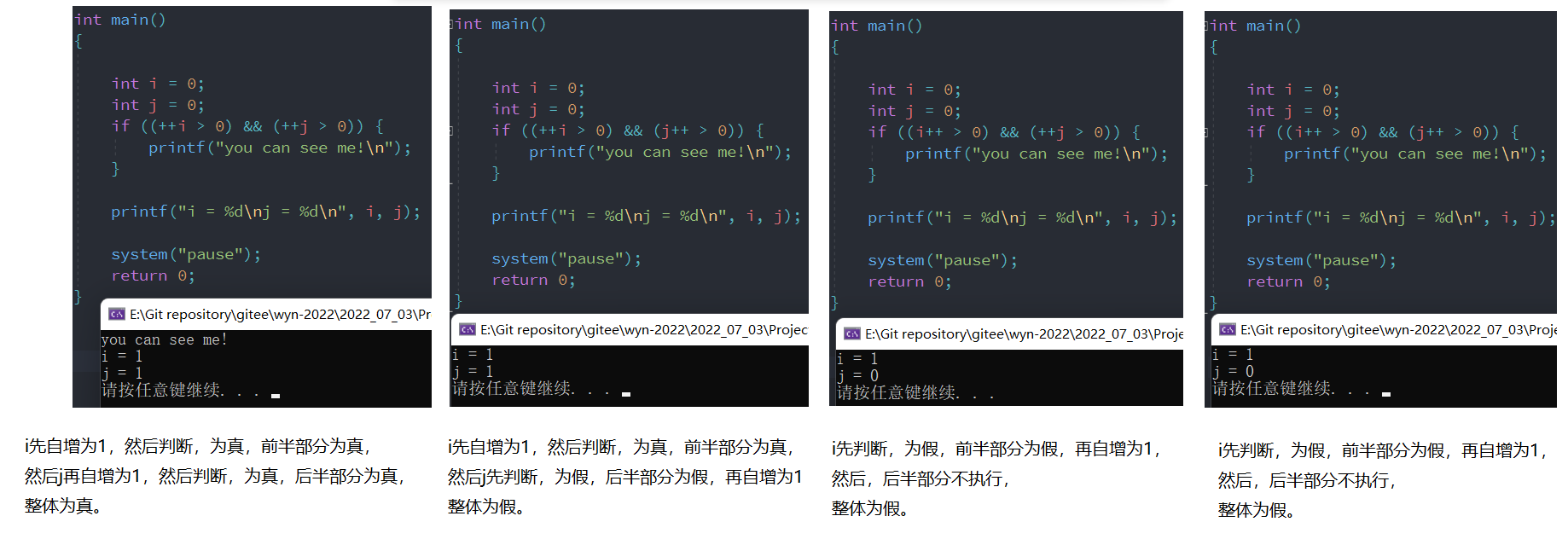
A short circuit
&& The number of operations ( sentence ), As long as one is false , Other operands ( sentence ) No longer .
|| The number of operations ( sentence ), As long as one is true , Other operands ( sentence ) No longer .
This is the short circuit .
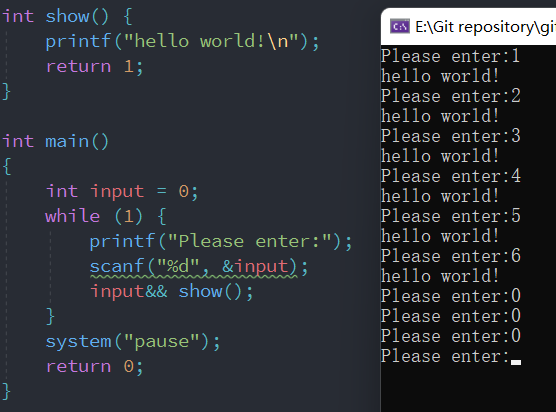
Use the characteristics of short circuit , The above can be achieved similar to if The function of .
An operator
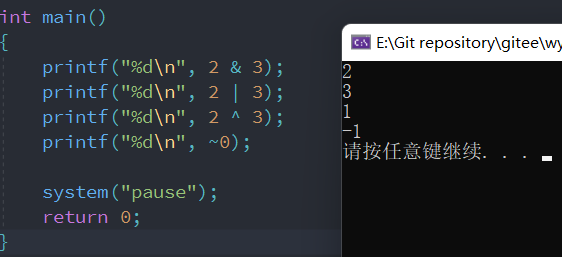
Basic concepts
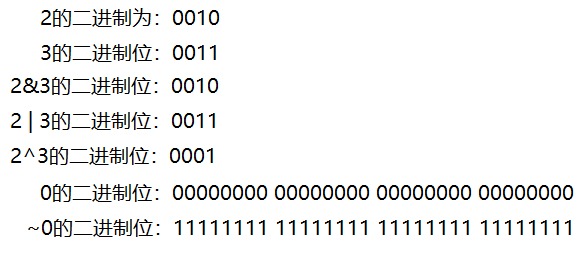
& The corresponding bits of the binary of two numbers are 1 when , The result is 1; conversely , The result is 0.
| At least one of the corresponding bits of the binary of two numbers is 1 when , The result is 1; conversely , The result is 0.
^ Is when the corresponding bits of two binary numbers are different , The result is 1; Phase at the same time , The result is 0.
~ Is to negate all the binary bits of the number .
&& 、|| VS &、 |
&&,|| Cascading are multiple logical expressions , What is needed is the true and false results .
&,| Cascading is multiple data , Bit by bit operation .
Logical result : Did you have your meal? ?
data structure : How much did you eat ?
About ^
Yes ^ Three understandings of
- Bit by bit , Same as false , Difference is true
- Any number and 0 Exclusive or , It's all about itself
- Support the law of association and the law of exchange
The first understanding is shown in the figure above , Next, let's look at the last two understandings
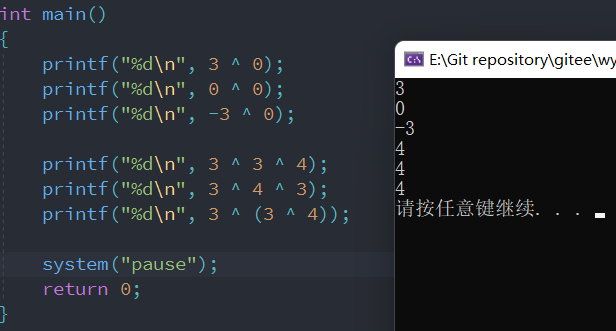
First look at the first three lines , Any number and 0 Exclusive or is itself , It's easy to understand , because 0 Of 32 Every bit is 0, and 3 Of the bits is 0 Is the same after XOR , The result is still the 0, and 3 Of the bits is 1 After XOR of , The result is 1, In fact, the overall result is 3 In itself . So we can draw this conclusion .
Look at the last three lines , First, 3 and 3 Exclusive or , Two identical numbers , The bits also correspond to the same , The result is 0, and 0 and 4 Exclusive or , The result is still 4 了 . Look at the last two lines , See the result is still 4, It is also verified that the XOR operator satisfies the commutative law and the associative law .
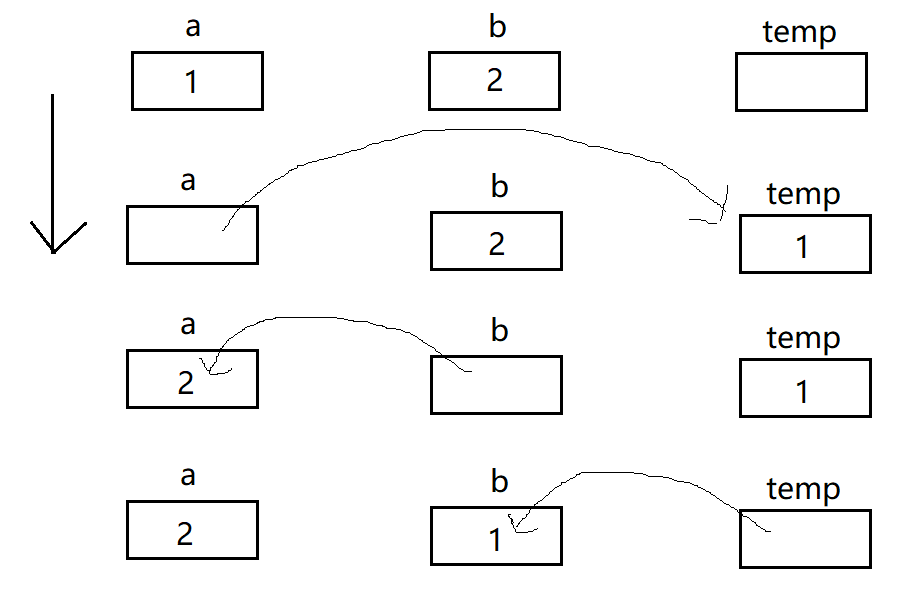
Swap two integers
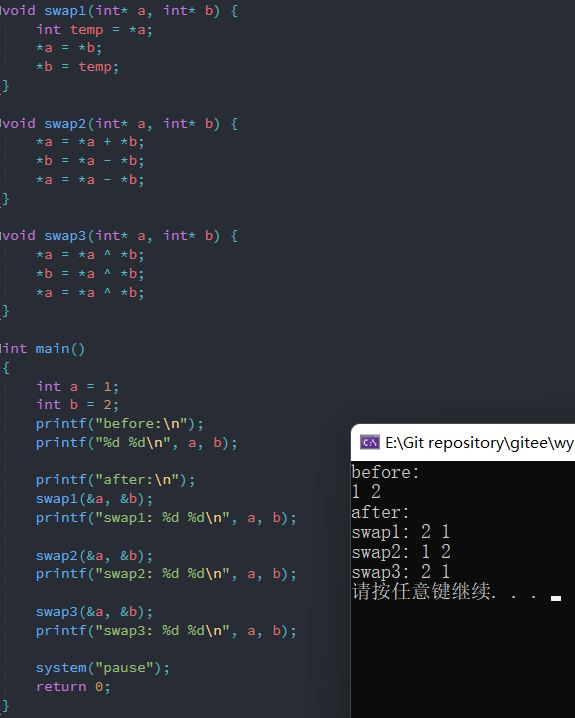
There are three ways to exchange two numbers , The first is the most common :
Next is the second one :
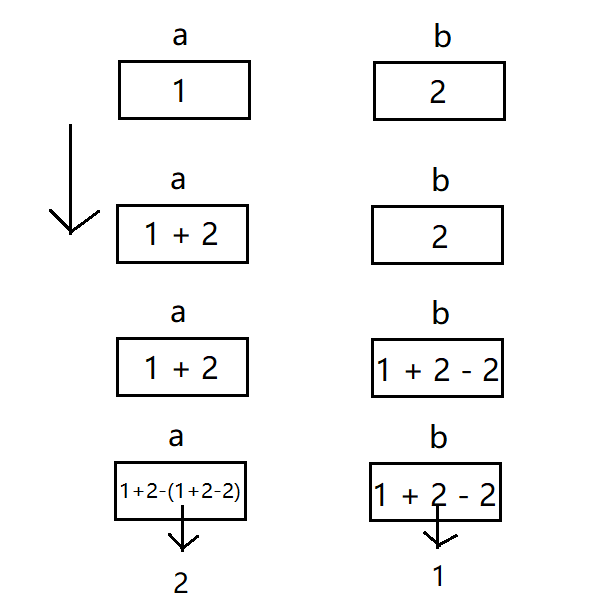
But this method is likely to go wrong , Because when two variables of the same type are added , The result may exceed the maximum value of this type , The result is the result after interception , And then something will go wrong .
Finally, method 3 :
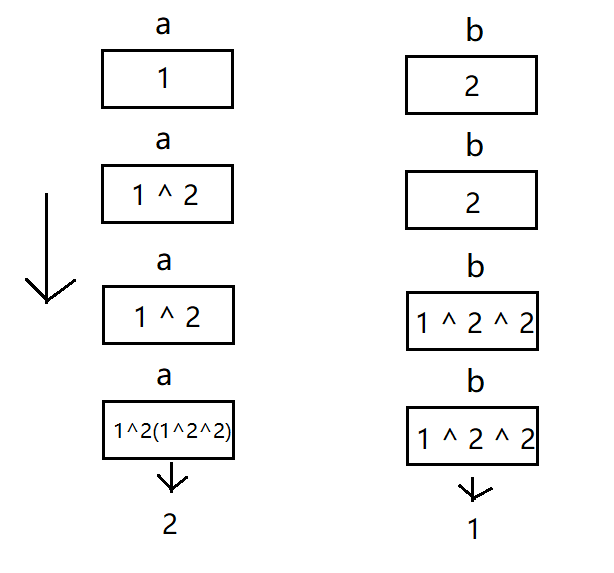
This method combines the right ^ Three understandings of , And it's a method that won't make any mistakes .
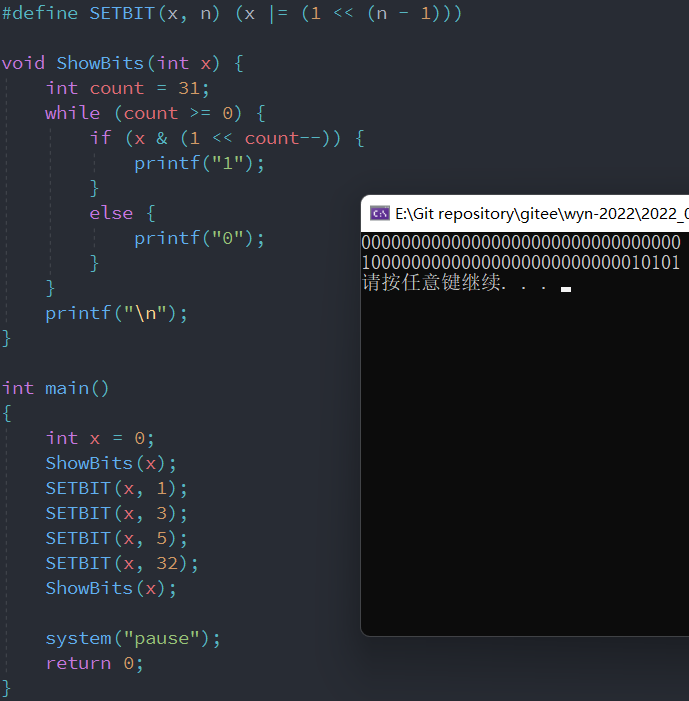
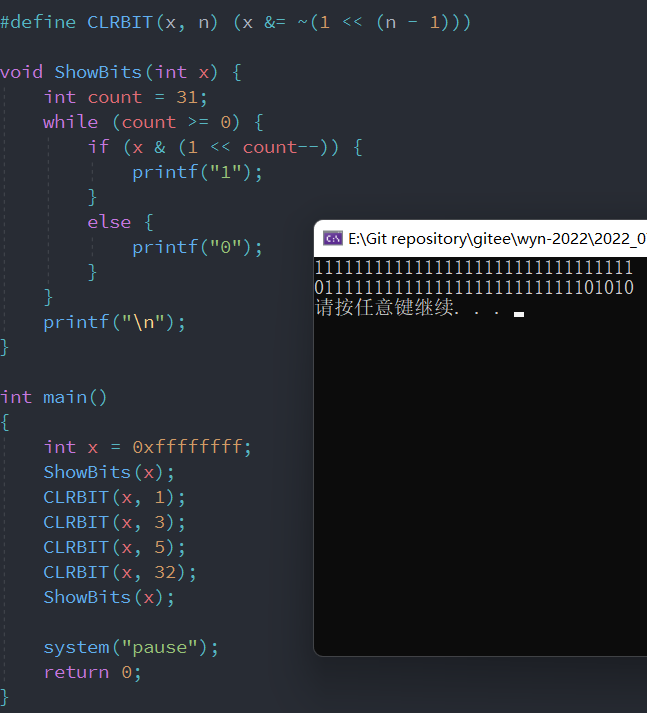
Bit operators need to be defined with macros before using .
The specified bit position is 1
The specified bit position is 0
【 The rules 2-19】 In fact, it is an integer improvement problem
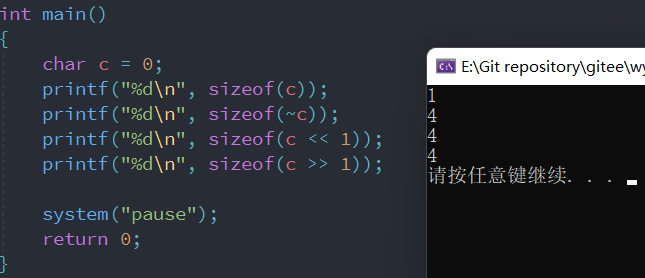
Regardless of any bitwise operator , The goals are calculated by the computer , And there are only CPU Have computing ability ( It's easy to understand ), But the calculated data , It's all in memory . so , Before calculation ( No matter what operation ), Must get the data from memory CPU in , Get CPU Where ? without doubt , stay CPU In the register of .
And the register itself , With the number of bits in the computer , The number of bits in the register is also different . commonly , stay 32 Place below , The number of bits in the register is 32 position .
But char The type data is only 8 A bit , Read to register , Can only fill the low 8 position , And the rest is high 24 position , It needs to be done “ Improve the overall shape ” 了 .
Move left and right
<< Move left : The highest bit is discarded , The lowest point is made up of 0
>> Move right :
- An unsigned number : The lowest bit is discarded , Highest complement 0( Logical shift right )
- Signed number : The lowest bit is discarded , The highest complement sign ( Arithmetic shift right )
How to understand “ discarded ”?
Basic understanding chain :
<<perhaps>>It's all calculation , All in CPU In the middle of , But the variables involved in the movement , It's in memory . So you need to move the data to CPU And then move it in the register of . In the process of actual movement , Is done in a register , That is, in a unit with a fixed size , that , Move left and right, there must be a place to run ==“ outside ”== The situation of .
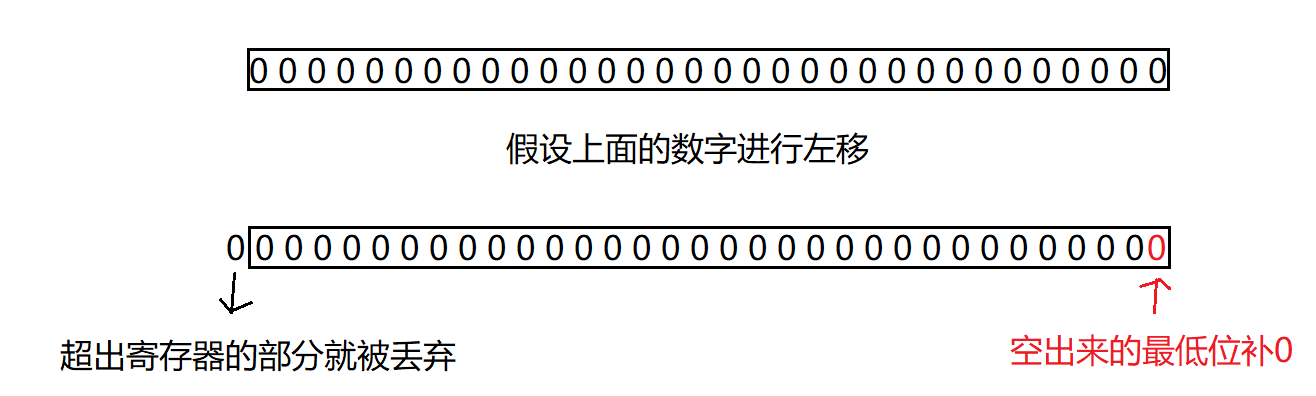
Deep understanding of shift left and right
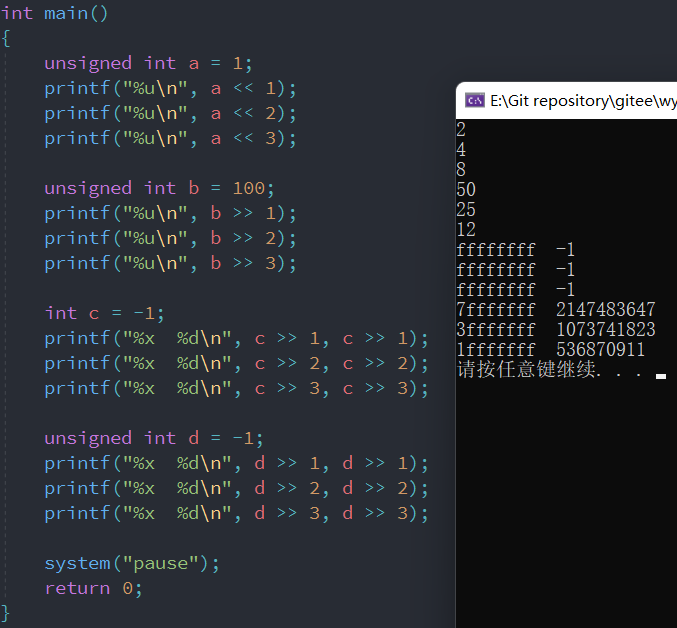
Look at the picture above , We can conclude that :
Move left : No brain tonic 0
Move right : First judge whether it is arithmetic right shift or logical right shift . The basis of judgment : Look at your own type , It has nothing to do with the content of the variable .
边栏推荐
- Codeforces Round #804 (Div. 2)
- UCF(暑期团队赛二)
- Nacos TC setup of highly available Seata (02)
- 集合详解之 Map + 面试题
- Compilation et connexion de shader dans games202 - webgl (comprendre la direction)
- The video in win10 computer system does not display thumbnails
- Summary of redis basic knowledge points
- Yolov5 tensorrt acceleration
- Leetcode 186 Flip the word II in the string (2022.07.05)
- Fluent implements a loadingbutton with loading animation
猜你喜欢
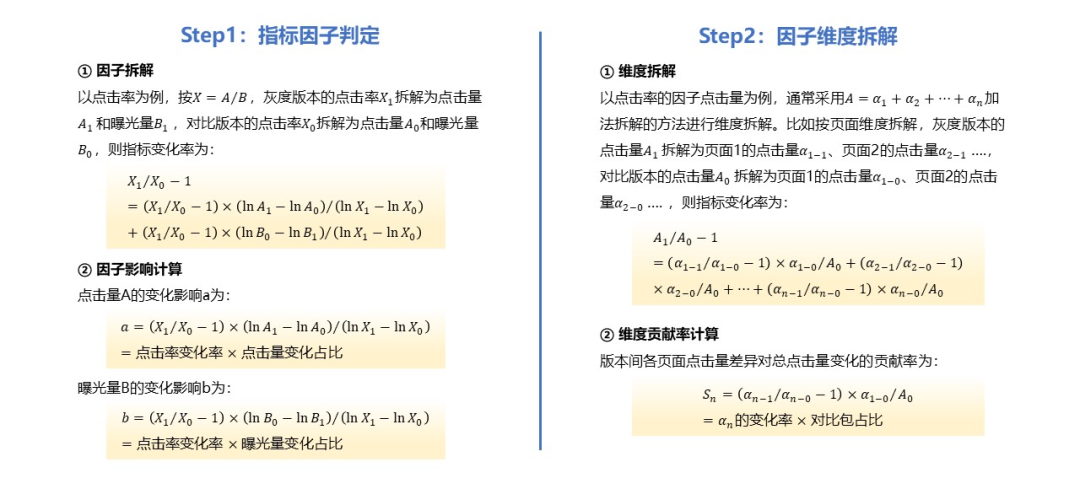
从0到1建设智能灰度数据体系:以vivo游戏中心为例
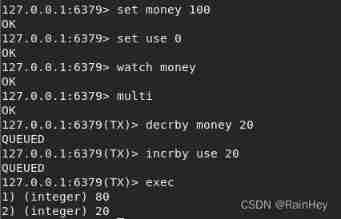
Crazy God said redis notes
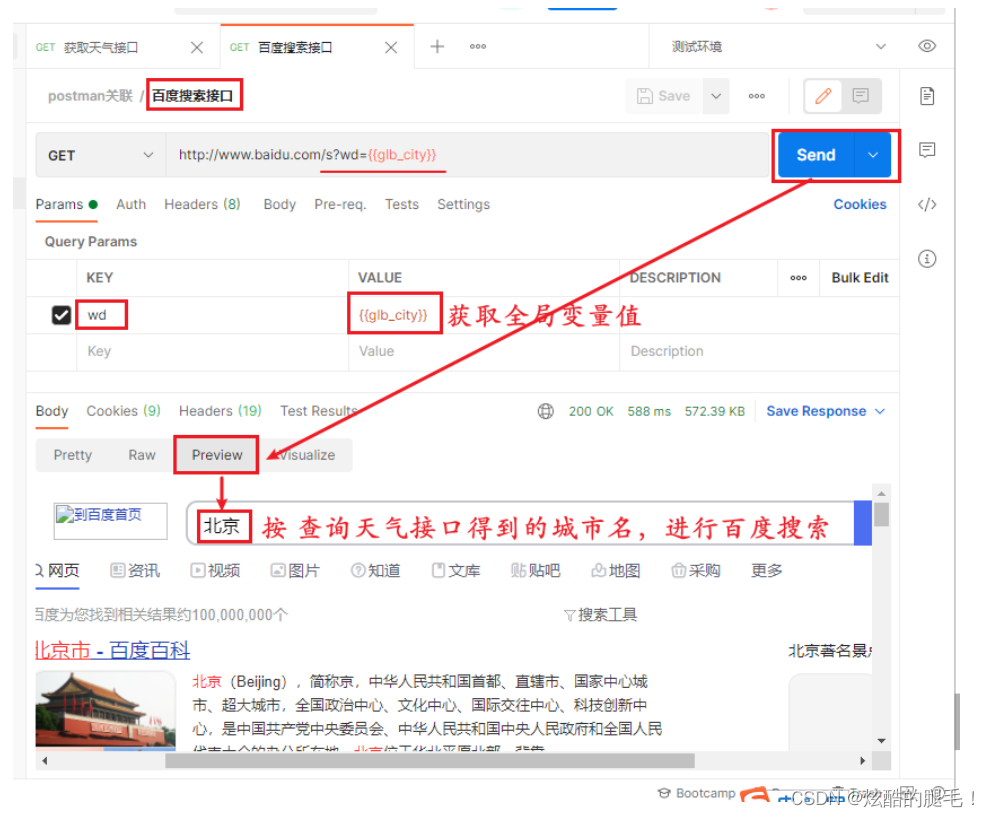
Postman Association
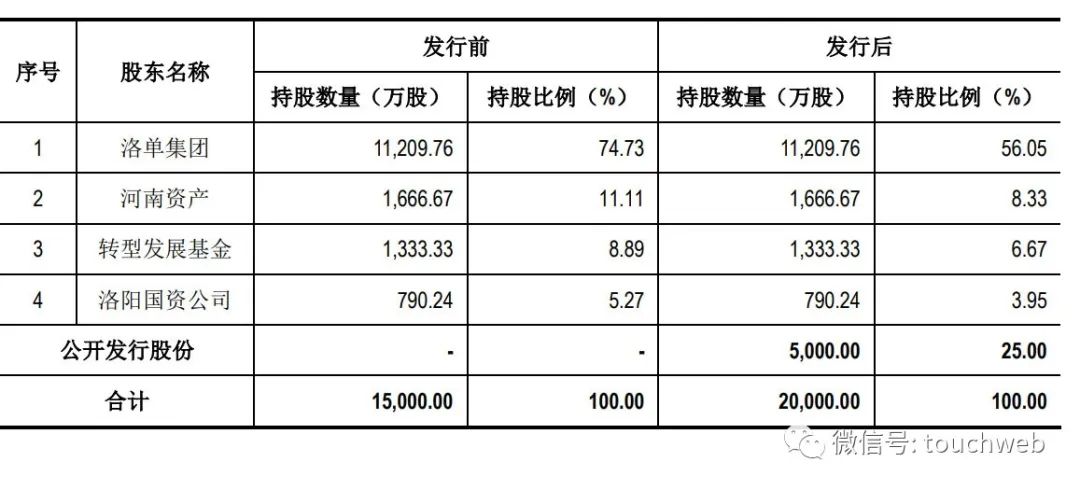
麦斯克电子IPO被终止:曾拟募资8亿 河南资产是股东
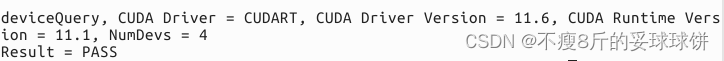
Cuda11.1 online installation

The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower

Pagoda configuration mongodb
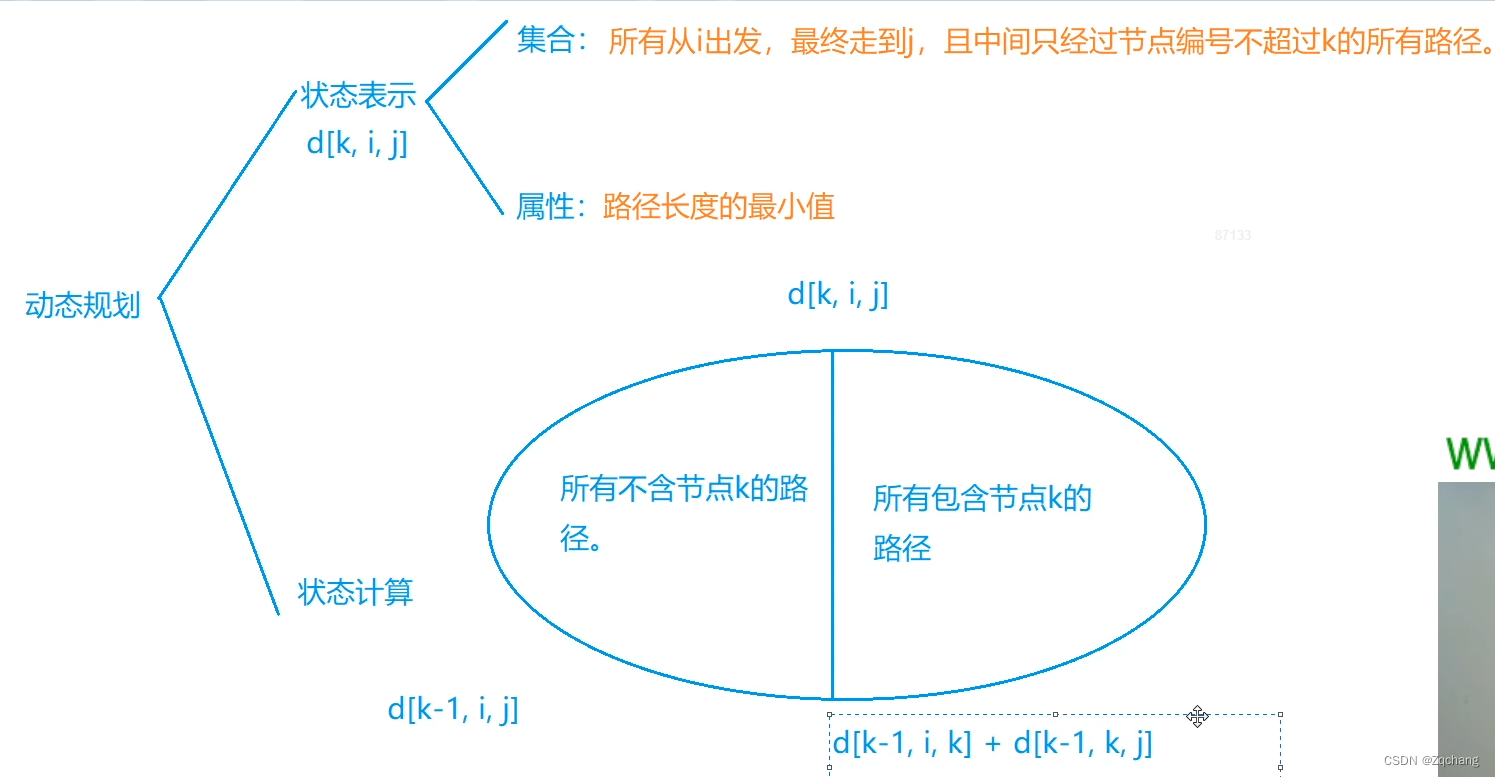
Flody的应用
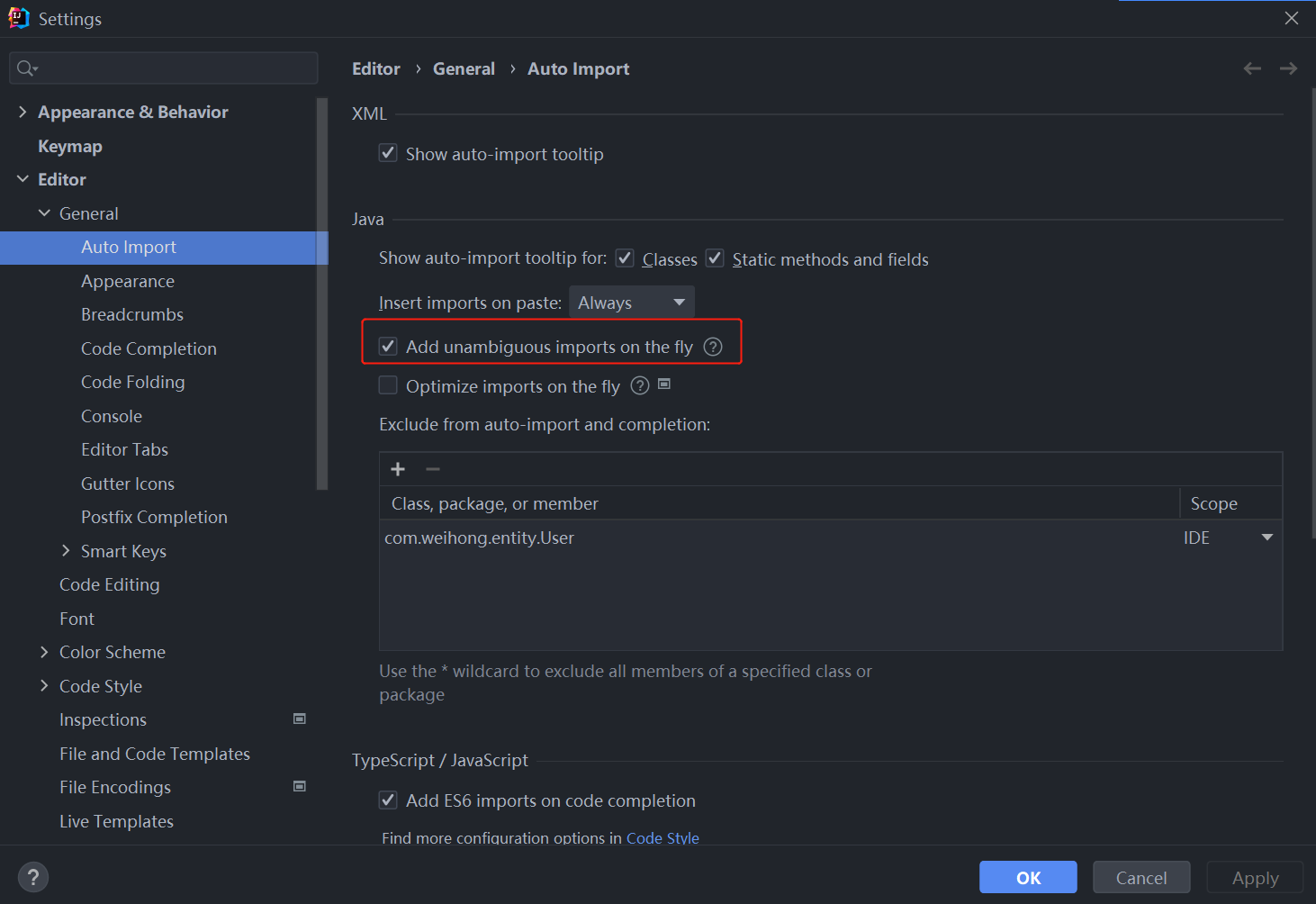
idea一键导包

浅谈镜头滤镜的类型及作用
随机推荐
[noip2008 improvement group] stupid monkey
Lepton 无损压缩原理及性能分析
关于Unity Inspector上的一些常用技巧,一般用于编辑器扩展或者其他
2021RoboCom机器人开发者大赛(初赛)
Flody的应用
Postman assertion
A little knowledge of CPU, disk and memory
Sorting out the knowledge points of multicast and broadcasting
Force buckle 1189 Maximum number of "balloons"
Postman关联
Postman Association
Cuda11.1 online installation
Extension of graph theory
Configuration file converted from Excel to Lua
Oracle query table index, unique constraint, field
Yolov5 tensorrt acceleration
The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower
[effective Objective-C] - memory management
Compilation and connection of shader in games202 webgl (learn from)
Yyds dry inventory SSH Remote Connection introduction