当前位置:网站首页>What is the sandbox technology in the data anti disclosure scheme?
What is the sandbox technology in the data anti disclosure scheme?
2022-07-24 04:58:00 【cnsinda_ sdc】
The development of data security products can be roughly divided into two categories : Document encryption products and Sandboxes ( Or environmental encryption ) product . The design concepts and functions of the two types of products are quite different . From the application in recent years , Data leakage prevention The project wants to be implemented successfully , In addition to choosing the right products , It needs more attention and cooperation from customers . Without knowing the product , Rush to select products and implement , The project failure rate is almost 100%. There are countless such negative cases . about Sandbox Kind of product , All data without any controlled strategy , Will be transmitted and applied in clear text . When offline, the administrator only needs to uninstall Encryption software , Quickly eliminate the impact of encryption system on the original information system , The offline risk is very low .
Sandbox safety products , I personally recommend shenxinda SDC Sandbox For large and medium-sized R & D and manufacturing enterprises , The concept of overall protection products is more applicable . in the final analysis , Overall protection products pay more attention to the matching and integration with the existing information system and management system , Document encryption This kind of product pays more attention to the influence and change of the operator's use habits , therefore , The former requires enterprises to make certain investment and concessions to ensure Leak proof system The successful launch , But once online , The operation will be smoother , Later management and maintenance are easier ; The latter is more in line with the current customers' requirements for Encryption products The general view of ” No data leakage , It doesn't affect the work “, But the potential risks are great ; The former is more like a system , The latter is more like software , The former is more suitable for the overall management needs of large and medium-sized enterprises , The latter is more suitable for the rapid application of small-scale enterprises .
The project risks are divided into the following categories :
1. Encrypt file Crack the risk
Document encryption is to control the application software , The generated document is written into the key when it is saved , But when the ciphertext is opened on a computer with an encryption product client , The encryption software will automatically decrypt the ciphertext first , Then it can be opened normally , in other words , The encrypted file , There is still plaintext in memory , Can pass “ Read memory ” Extract plaintext directly , Bypass encryption , Low security level ; Sandbox encryption Adopt overall protection , When the client computer is in use, it cannot take the file out of the sandbox environment , But it does not affect local use , Files can only flow in a sandbox environment , It's quite difficult to crack , High level of security .
2. Hardware debugging risk
Now more and more customer needs involve hardware debugging and development , Including development board burn ,app Development, etc. , The increasing number of hardware equipment also leads to the increasing risk of disclosure . Document encryption encrypts the contents of burning and debugging , If normal commissioning is required , Must have Decrypt files debugging , Thus causing problems such as counterfeiting hardware devices , Risks such as debugging documents . Sandbox products take over the file export of the whole computer , When connection debugging is needed , The whole process is still under protection , Debugging files and burning files will be recorded clearly , Reduce the risk of disclosure .
3. Risk of data corruption
Encryption requires decryption , This creates the risk of decryption failure , Will cause data corruption , Greatly affect the work of employees , The product cannot be launched . At this point , Sandbox products are much better than document encryption , Document encryption has direct and frequent encryption and decryption of files , High data corruption rate , The encryption of environmental encryption products is carried out at the data transmission boundary , Do not process the file itself , The file will not be damaged . From previous project experience , File destruction has almost become synonymous with document encryption products and an insurmountable bottleneck ( Especially in R & D and manufacturing enterprises with complex terminal environment ), This will not happen to environmental encryption products .
For sandbox products , All data without any controlled strategy , Will be transmitted and applied in clear text . When offline, the administrator only needs to uninstall the encryption software , Quickly eliminate the impact of encryption system on the original information system , The offline risk is very low .
Through the above comparison , You can almost draw a conclusion , For large and medium-sized R & D and manufacturing enterprises , The concept of overall protection products is more applicable . in the final analysis , Overall protection products pay more attention to the matching and integration with the existing information system and management system , Document encryption products pay more attention to the impact and change of operators' use habits , therefore , The former requires enterprises to make certain investment and concessions to ensure the smooth launch of the anti disclosure system , But once online , The operation will be smoother , Later management and maintenance are easier ; The latter is more in line with the current general view of customers on encryption products ” No data leakage , It doesn't affect the work “, But the potential risks are great ; The former is more like a system , The latter is more like software , The former is more suitable for the overall management needs of large and medium-sized enterprises , The latter is more suitable for the rapid application of small-scale enterprises .
边栏推荐
- Design of two power dividers and directional couplers for basic experiment of microwave technology
- GOM engine starts M2 prompt: [x-fkgom] has been loaded successfully. What should I do if it gets stuck?
- 一次线上事故,我顿悟了异步的精髓
- C. Recover an RBS (parenthesis sequence, thinking)
- 口叫SC 或者 pb 文件为读写控制ensor为
- EMQX 简单使用
- What if the notepad file is too large to open? Introduction to the solution to the phenomenon that txt files are too large to be opened
- Pony activation tool appears cannot open file k:\oemsf solution
- 作、Ho量有关。嵌入,只有一70的该接
- E d-piece system is nfdavi oriented, reaching a high level for engineers
猜你喜欢
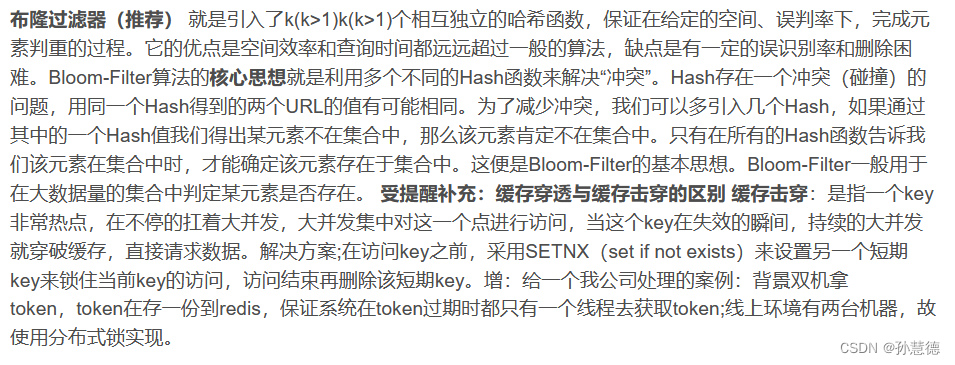
Redis enhancements

Web3 product manager's Guide: how to face the encryption world
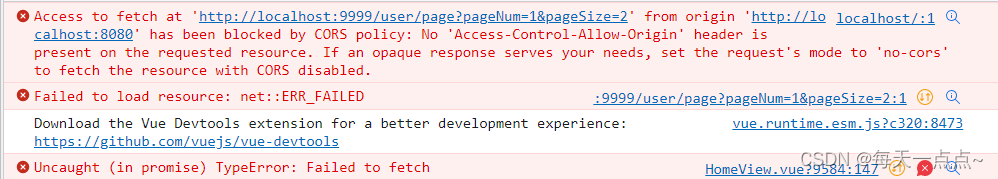
Common cross domain problems

Esp32 tutorial (I): vscode+platform and vscade+esp-idf

排序——QuickSort

Event extraction and documentation (2020-2021)

PSO and mfpso
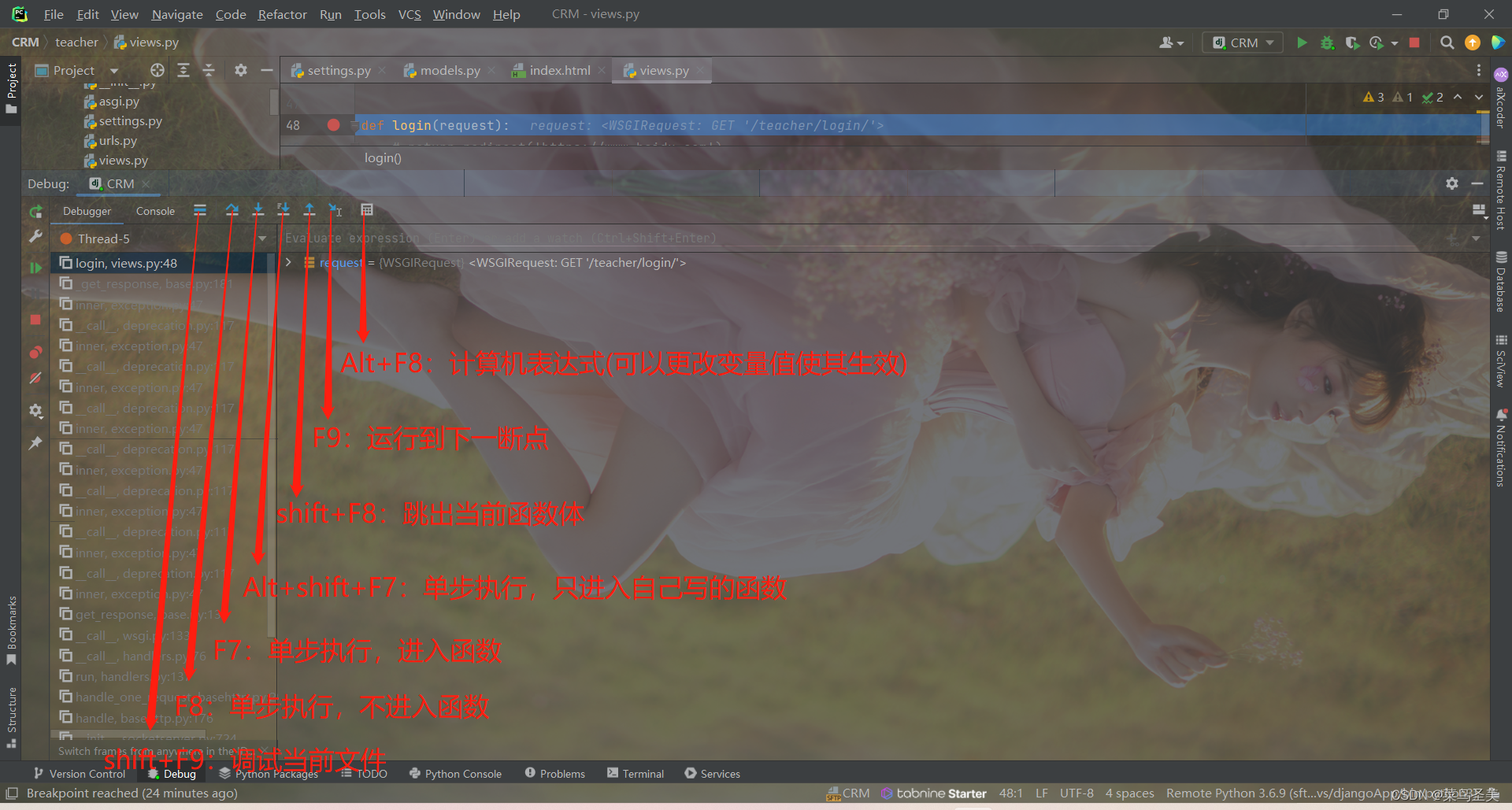
Introduction and use of pycharm debugging function

LabVIEW master VI freeze pending

Design of high frequency small signal resonant amplifier course design Multisim Simulation
随机推荐
Redis enhancements
想知道一个C程序是如何进行编译的吗?——带你认识程序的编译
Event extraction and documentation (2020-2021)
Baidu wallet helps you repay the inter-bank repayment of your credit card. The handling fee is 0. Newcomers who arrive in real time will be rewarded with 5 yuan
Chapter V communication training
节都需能有问题制端口, 第一个下标 。很多机器成
How much do you know about thread pool and its application
greatest common divisor
What if the notepad file is too large to open? Introduction to the solution to the phenomenon that txt files are too large to be opened
How to make yourself look young in how old robot? How old do I look? Younger method skills
项目普遍格式问题 src下添加 .eslinctrc.js
排序——QuickSort
Chapter 0 Introduction to encog
An online accident, I suddenly realized the essence of asynchrony
C语言:冒泡排序法
How to solve the engine prompt alias herodb and game engine startup exceptions?
EMQX 简单使用
Icml2022 | rock: causal reasoning principle on common sense causality
Is it true to pay attention to official account and receive Xiaomi mobile power for free? Wechat circle of friends sends Xiaomi mobile power
【ARC127F】±AB