当前位置:网站首页>Transfinite hacker cognition
Transfinite hacker cognition
2022-07-03 07:58:00 【Safety brother】
Hacker cognition
Real hackers are like the month in the death note , The beginning of the month is to promote good and eliminate evil , But the practice is extremely evil , treason and heresy , Not accepted by the world , So don't expose yourself , Can only act in the dark , The extremely morbid sense of achievement is indescribable .
Of course , If you walk into the sun , You are no longer a hacker , But you can still continue the hacker spirit .

frenemy
Hackers' opponents are also hackers .
The one who knows the month best is L.
Just like attack and defense , If there is no opponent , Attack and defense are always empty talk .
therefore , You know what your opponent is thinking , Do something ?
Most people don't even know who their opponents are ~?

Magic rules
Magicians and hackers are interlinked , Need to keep a secret . Saston's three principles apply to hackers :
1. Never reveal the secret of magic to the audience .
2. Before the show , Never explain to the audience what to perform next .
3. Never at the same time 、 In the same place 、 Perform the same magic for the second time with the audience .

边栏推荐
- Wechat applet taro learning record
- Unity XR realizes interaction (grasping, moving, rotating, transmitting, shooting) -pico
- Zohocrm deluge function application time verification
- Quality blog——
- Redis配置文件
- HDMI2.1与HDMI2.0的区别以及转换PD信号。
- Clip Related Script
- PHP常用排序算法
- Quelle est la définition? Qu'est - ce qu'une déclaration? Quelle est la différence?
- Ventuz Foundation Series "one step at the door"
猜你喜欢

Pulitzer Prize in the field of information graphics - malofiej Award

Free use until 2015 -- viz artist multi touch plug-in package

一个实习生的CnosDB之旅

WPF:解决MaterialDesign:DialogHost 无法关闭问题

Professor Zhang Yang of the University of Michigan is employed as a visiting professor of Shanghai Jiaotong University, China (picture)
![[step on the pit series] MySQL failed to modify the root password](/img/d0/f975baf18bac506208abff3713ac03.png)
[step on the pit series] MySQL failed to modify the root password
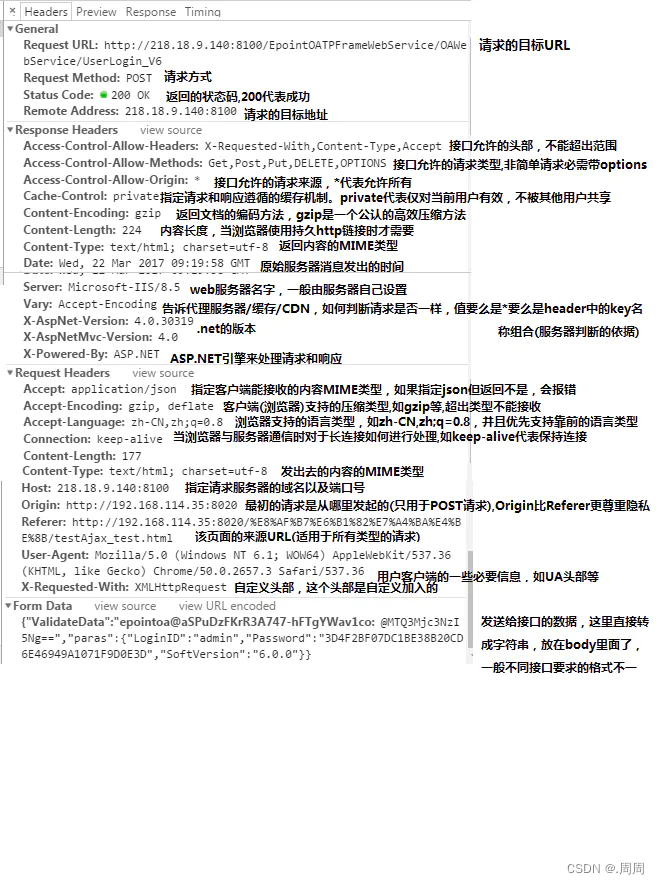
What to do after the browser enters the URL
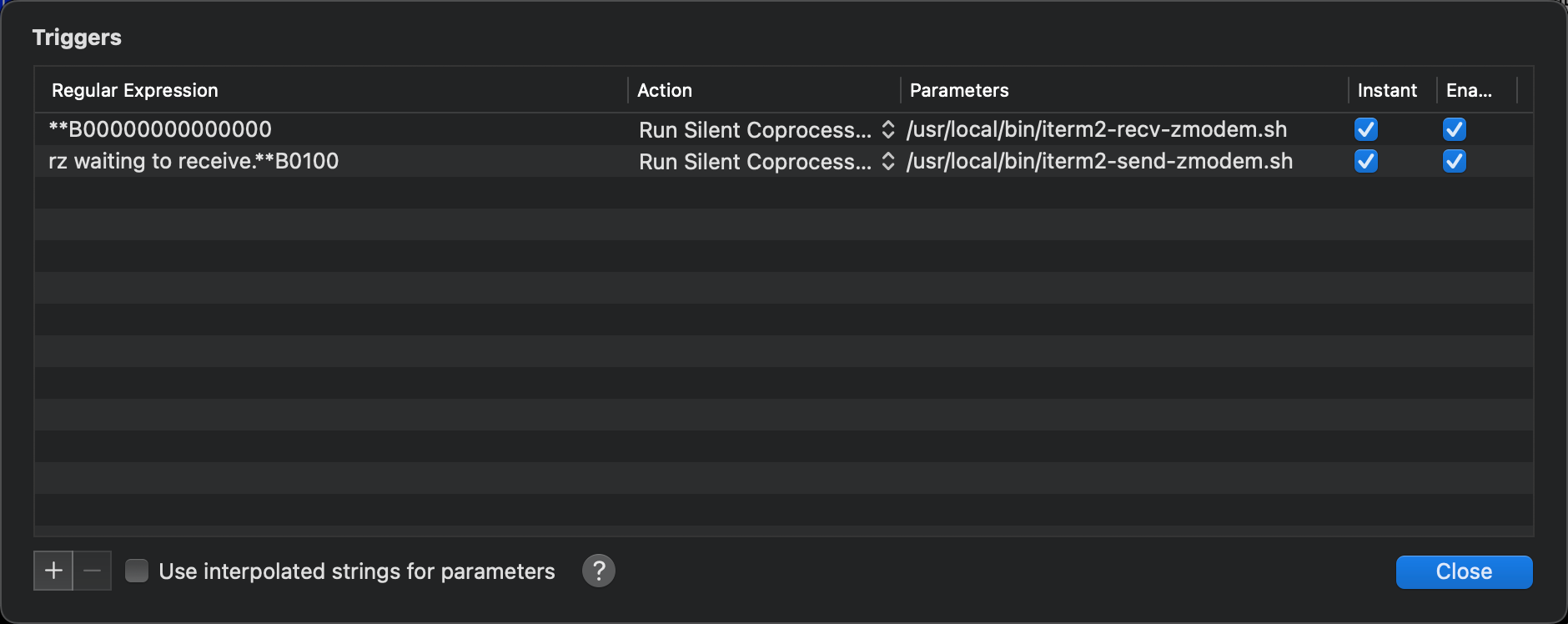
Iterm2 setting
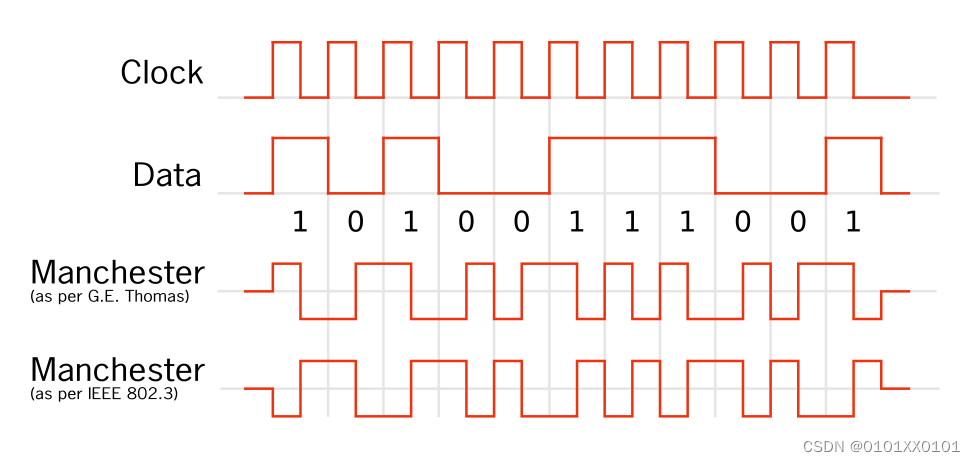
An article for you to understand - Manchester code

Viz artist advanced script video tutorial -- stringmap use and vertex operation
随机推荐
Quelle est la définition? Qu'est - ce qu'une déclaration? Quelle est la différence?
LwIP learning socket (application)
How to configure GDAL under idea
PDO and SDO concepts
the installer has encountered an unexpected error installing this package
[USACO12MAR]Cows in a Skyscraper G(状态压缩dp)
Research shows that breast cancer cells are more likely to enter the blood when patients sleep
What to do after the browser enters the URL
C2 several methods of merging VCF files
Clip Related Script
Uniapp learning records
HDMI2.1与HDMI2.0的区别以及转换PD信号。
vcs import src < ros2. Repos failed
register关键字
Redis查看客户端连接
My touch screen production "brief history" 1
华为S5700交换机初始化和配置telnet,ssh用户方法
Oracle queries grouped by time
【LeetCode】4. Best time to buy and sell stock
Iterm2 setting