当前位置:网站首页>Hijacking a user's browser with beef
Hijacking a user's browser with beef
2022-07-01 08:08:00 【Cwillchris】
BeEF( The Browser Exploitation Framework) By Wade Alcorn( Wade · Alcon ) stay 2006 Started in , It is still under maintenance . By ruby Language development framework for browser attacks .

The process of execution , Like this malicious pop-up :

zombie( Corpse ) The victim browser .zombie Be being hook( Hook up ) Of , If the browser accesses a tick ( from js To write ) The page of , Will be hook, The linked browser will execute the initial code and return some information , next zombie Every once in a while Time ( The default is 1 second ) Will go to BeEF Server sends a request , Ask if there is new code to execute .BeEF The server itself It's like a Web application , Divided into front end UI, Back end . The front end will poll the back end for new data to be updated , At the same time, the front end can also send instructions to the back end , BeEF Holders can log in through a browser BeEF Back office management UI.
Click application launch beef , If not, input at the terminal beef-xss install
边栏推荐
- Analysis of slice capacity expansion mechanism
- 【入门】输入n个整数,输出其中最小的k个
- Five combination boxing, solving six difficult problems on campus and escorting the construction of educational informatization
- Uni hot update
- [introduction] approximate value
- Implementation and encapsulation of go universal dynamic retry mechanism
- PHP laravel wechat payment
- 【批处理DOS-CMD命令-汇总和小结】-Cmd窗口中常用操作符(<、<<、&<、>、>>、&>、&、&&、||、|、()、;、@)
- She is the "HR of others" | ones character
- Anddroid 文本合成语音TTS实现
猜你喜欢

SharePoint - modify web application authentication using PowerShell

【入门】输入整型数组和排序标识,对其元素按照升序或降序进行排序
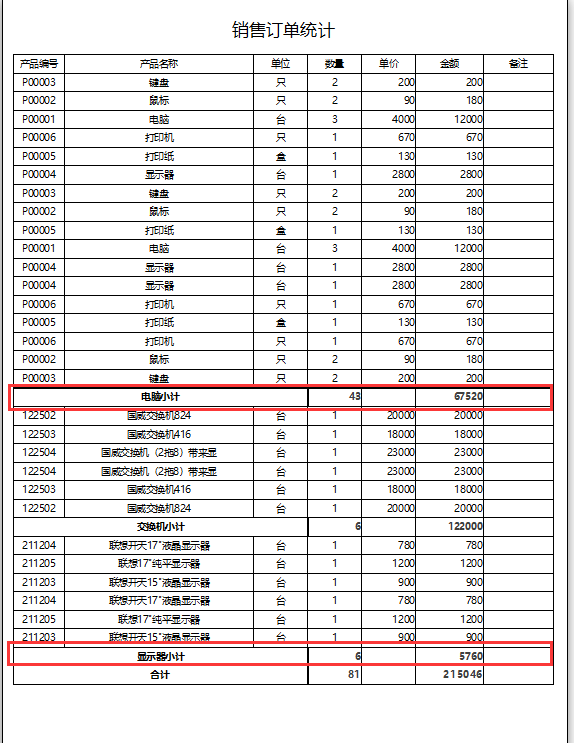
Access报表实现小计功能
Soft keyboard height error

web254

Day5: scanner object, next() and nextline(), sequential structure, selection structure, circular structure

Significance and measures of source code encryption
![[redis] it takes you through redis installation and connection at one go](/img/ca/89cb18f0eeb835f021d6a2489681a1.png)
[redis] it takes you through redis installation and connection at one go

Tupu software has passed CMMI5 certification| High authority and high-level certification in the international software field
![[introduction] approximate value](/img/6b/597178d848dd21110f36601fc31092.png)
[introduction] approximate value
随机推荐
[getting started] enter the integer array and sorting ID, and sort its elements in ascending or descending order
038 network security JS
Insufficient executors to build thread pool
[kv260] generate chip temperature curve with xadc
Aardio - 自己构造的getIconHandle的方法
[MySQL learning notes27] stored procedure
Scala语言学习-07-构造器
一套十万级TPS的IM综合消息系统的架构实践与思考
OJ输入输出练习
图扑软件通过 CMMI5 级认证!| 国际软件领域高权威高等级认证
Tupu software has passed CMMI5 certification| High authority and high-level certification in the international software field
[getting started] intercepting strings
Chinese font Gan: zi2zi
slice扩容机制分析
Microsoft stream - how to modify video subtitles
QT -- 1. QT connection database
Contenttype comparison of all types
Day5: scanner object, next() and nextline(), sequential structure, selection structure, circular structure
sqlalchemy创建MySQL_Table
Li Kou daily question - day 31 -1790 Can a string exchange be performed only once to make two strings equal