当前位置:网站首页>Penetration tool - sqlmap
Penetration tool - sqlmap
2022-07-04 05:27:00 【In a word, the Trojan horse (the growth road of Wang an Xiaobai)】
One 、SQLMap Introduction to
1.SQLMap It's an open source SQL Injection tool , It can be used for automatic detection , You can even use SQL Inject vulnerabilities to directly obtain the permissions of the target database server . It has a powerful detection engine , Function options of penetration testing for different types of databases , Including getting the data stored in the database , Accessing operating system files can even execute operating system commands through an external data connection .
2. Supported databases :MySQL, Oracle, PostgreSQL, Microsoft SQL Server, MicrosoftAccess,IBM DB2, SQLite, Firebird, Sybase and SAP MAXDB.
Two 、SQLMap Five injection methods
- Joint injection
- An error injection
- Bull's blind note
- Time blind note
- Stack Injection
3、 ... and 、SQLMap An important parameter of
1. Parameters :-u /
Format :sqlmap -u " Target site url "
sqlmap -u "http://192.168.1.5/sqlilabs/Less-1/?id=1" id For web server IP Address
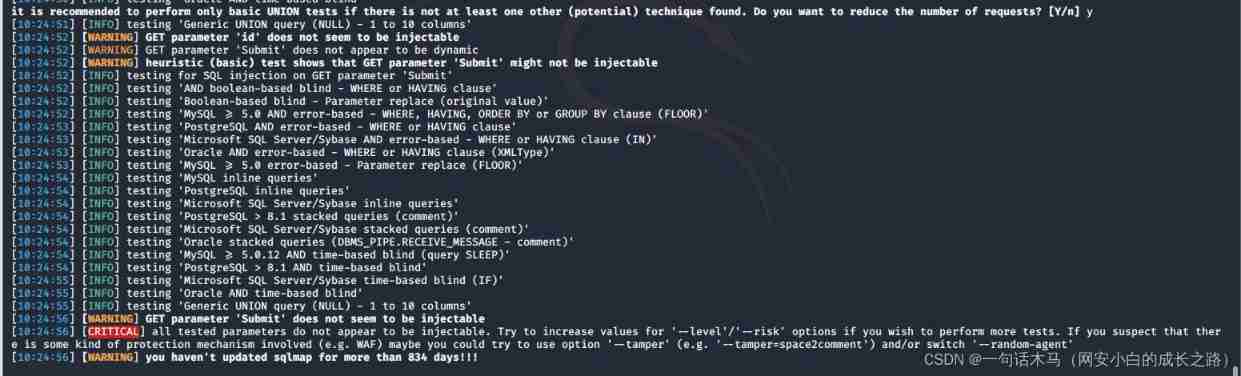
Results screenshots :

2. Parameters -m
Format :sqlmap -m file name
sqlmap -m 1.txt
Will be executed successively from the file url, You can only write one in a line url

2. Parameters :-r
Indicates loading from a file http request , Put the request packet into a file

sqlmap -r 2.txt

4. Set echo level
Parameters -v The default is 1
0: Echo only Python error message
1: Echo basic information and warning information at the same time
2: Echo at the same time debug Information
3: It also shows the injected payload
4: Show at the same time http request
5: Show at the same time http Response head
6: Show at the same time http Response request
grammar :sqlmap -u "http://192.168.1.5/sqlilabs/Less-1/?id=1" -v 3

5. Set detection level
Parameters --level
There are five levels Default level is 1,
level>=2 test http cookie
level>=3 test http user-agent/referer
level =5 test http host
The basic format :[email protected]:~/Desktop# sqlmap -r 2.txt --level 2

6. Set up http Packet related parameters
Parameters :--data hold data The following data is in post Mode submission
The basic format :[email protected]:~/Desktop# sqlmap -u "http://192.168.1.5/sqlilabs/Less-12/" --data "id=1"

7. Parameters --cookie hold cookie Parameter copy added to --cookie Back
The basic format :sqlmap -u "http://192.168.1.5/DVWA/vulnerabilities/sqli/?id=1&Submit=Submit#" --cookie = "Cookie: security=low; PHPSESSID=c799t8hil8934arhoeipuhep54"
8. Specify test parameters
-p :sqlmap All... Will be tested by default GET and POST Parameters , When -level Is greater than or equal to 2 When it's time Can test HTTP Cookie Head value , When it is greater than or equal to 3 Will also test when User- Agents HTTP Referer Head value .
9. Set the detection risk level
Parameters :--risk There are three levels of risk ,
1-3: The default is 1 Will test most of the test statements ,
2 Time based test statements will be added ,
3 Will increase OR Of the statement SQL Injection test .
Be careful : In some cases , For example, in UPDATE, DELETE The statement of , Into a OR Test statement of , The entire table that may cause an update , May cause great risks .
10. Column data
(1)--dbs view the database
Operation format :[email protected]:~/Desktop# sqlmap -u "http://192.168.1.5/sqlilabs/Less-7/?id=1" --dbs

(2)--users View all users --password View all passwords Can be used together
Operation format :[email protected]:~/Desktop# sqlmap -u "http://192.168.1.5/sqlilabs/Less-7/?id=1" --dbs --users --password
Entry directory :cd /root/.sqlmap/output/192.168.1.5
11. Use shell command :
Parameters :--os-shell Bounce interaction shell
Premise : Need the physical path of the website , The second is the need to have FILE read-write permission
12.--tamper Bypass the injection limit
usqlmap-u"http://url/news?id=1" --tamper "base64encode.py"
边栏推荐
- VB. Net calls ffmpeg to simply process video (class Library-6)
- KMP匹配字符串
- Flutter ‘/usr/lib/libswiftCore. dylib‘ (no such file)
- LM小型可编程控制器软件(基于CoDeSys)笔记二十二:错误4268/4052
- JS string splicing
- Simulated small root pile
- [matlab] matlab simulates digital bandpass transmission systems - QPSK and OQPSK systems
- How to use postman to realize simple interface Association [add, delete, modify and query]
- Solar insect killing system based on single chip microcomputer
- 云原生架构实战案例及优化解决方案
猜你喜欢

KMP match string

Flutter calls Gaode map app to realize location search, route planning and reverse geocoding

Appearance of LabVIEW error dialog box

KMP匹配字符串

Flask

C language simple student management system (including source code)

VB. Net simple processing pictures, black and white (class library - 7)

Void convolution, deformable convolution, deformable ROI pooling

Two sides of the evening: tell me about the bloom filter and cuckoo filter? Application scenario? I'm confused..

模拟小根堆
随机推荐
企业级日志分析系统ELK(如果事与愿违那一定另有安排)
[matlab] matlab simulation modulation system FM system
flink1.13 sql基础语法(一)DDL、DML
KMP match string
[untitled]
Evolution of system architecture: differences and connections between SOA and microservice architecture
如何使用postman实现简单的接口关联【增删改查】
[paper summary] zero shot semantic segmentation
National vocational college skills competition (secondary vocational group) network security competition questions - Analysis
谷歌 Chrome 浏览器将支持选取文字翻译功能
We believe that the development of consumer Internet will still be limited to the Internet industry itself
[QT] create mycombobox click event
laravel 中获取刚刚插入的记录的id
Letter meaning and parameter abbreviation of optical module Daquan
Redis realizes ranking function
When using flash to store parameters, the code area of flash is erased, which leads to the interrupt of entering hardware error
flink1.13 sql基础语法(二)join操作
简易零钱通
[matlab] general function of communication signal modulation - generation of narrow-band Gaussian white noise
Get the ID of the record just inserted from laravel