当前位置:网站首页>Process of manually encrypt the mass-producing firmware and programming ESP devices
Process of manually encrypt the mass-producing firmware and programming ESP devices
2022-07-04 17:16:00 【25March】
The requirements are as follows
Encrypting the mass-produced firmware, after encryption you can use the tool to erase the old firmware, and it support repeated flashing the firmware.
Required tools:
- esptool , you can refer to Introduction and use of esptool.py
- Flash download tool
Reference Documentation:
solution
Specify the Flash encryption key (
key.bin), i.e. each module uses the same Flash encryption key (key.bin). Firstly using the Flash encryption key (key.bin) to encrypt the separate binary plaintext firmware that compiled by project, then you can flash the encrypted ciphertext firmware directly using the Flash Download Tool. After the ciphertext firmware flashed, you need to use esptool to falsh the Flash encryption key (key.bin) to the Efuse, then turn on the Control Bit of Flash Encryption in Efuse to make sure the encrypted firmware boots properly. The steps are as follows:
1 Use the esptool tool to generate a Flash encryption key (key.bin) for production firmware, for example, the generated encryption key is key.bin:
espsecure.py generate_flash_encryption_key key.bin
2 Encrypt each firmware (bin file) to be flashed, using the hello-world as an example
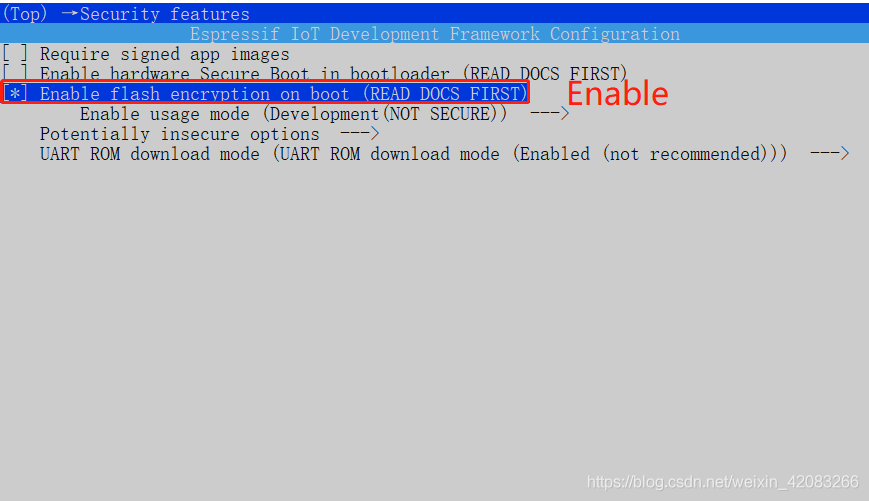
- **Turned on the Flash encryption option in menuconfig, as follows: **
menuconfig -> Security features -> Enable flash encryption on boot
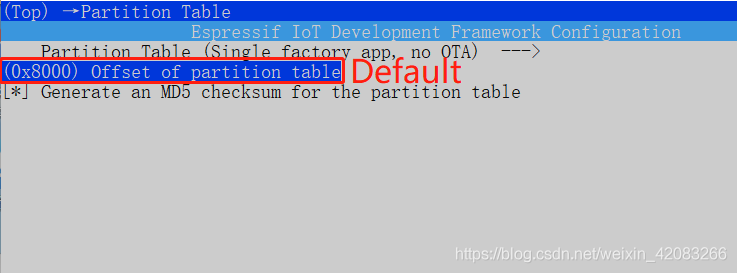
- **Since Flash encryption increases the size of the bootloader .bin firmware, the offset of the default partition table needs to be adjusted, which is 0x8000, can be adjusted to 0xa000. You can modify the settings for partition_table in menuconfig. As follows: **
menuconfig -> Partition Table -> Offset of partition table
- Then compile the project and check the firmware download address corresponding to the compiled firmware. You can find that the download address of hello-world.bin becomes 0x20000
Project build complete. To flash, run this command:
E:.espressif\python_env\idf4.3_py3.8_env\Scripts\python.exe …\components\esptool_py\esptool\esptool.py -p (PORT) -b 460800 --before default_reset --after no_reset --chip esp32c3 write_flash --flash_mode dio --flash_size detect --flash_freq 80m 0x0 build\bootloader\bootloader.bin 0xa000 build\partition_table\partition-table.bin 0x20000 build\hello-world.bin
or run ‘idf.py -p (PORT) flash’
3 Using the generated Flash encryption key (key.bin file) to encrypt each individual firmware (bin file) that compiled by project. As follows:
- ) to encrypt bootloader.bin, and the encrypted bootloader.bin becomes key_bootloader.bin**
espsecure.py encrypt_flash_data --keyfile key.bin --address 0x1000 -o key_bootloader.bin build/bootloader/bootloader.bin
- Using the generated Flash encryption key (
key.bin) to encrypt partition-table.bin, and the encrypted partition-table.bin becomes key_partition-table.bin
espsecure.py encrypt_flash_data --keyfile key.bin --address 0xa000 -o key_partition-table.bin build/partition_table/partition-table.bin
- Using the generated Flash encryption key (
key.bin) to encrypt hello_world.bin, and the encrypted hello_world.bin becomes key_hello-world.bin
espsecure.py encrypt_flash_data --keyfile key.bin --address 0x20000 -o key_hello-world.bin build/hello_world.bin
4 **According to the corresponding download address of the firmware compiled by project, program the encrypted firmware (encrypted bin file), use the esptool to download the encrypted firmware as follows: **
esptool.py -b 460800 --before default_reset --after no_reset --chip esp32 write_flash --flash_mode dio --flash_size detect --flash_freq 40m 0x1000 key_bootloader.bin 0xa000 key_partition-table.bin 0x20000 key_hello-world.bin
note:
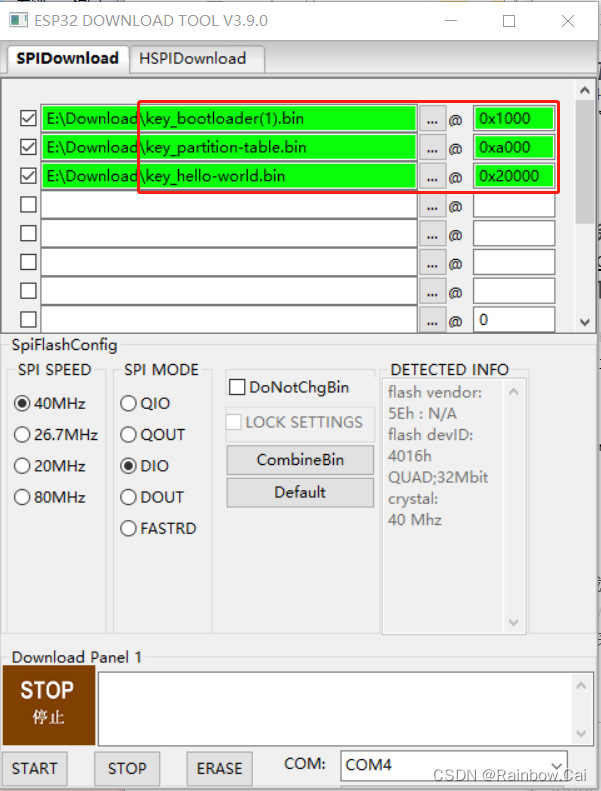
This step to download the encryption firmware can also be downloaded directly using the Flash Download Tool as follows:
5 Program the Flash encryption key (key.bin) to Efuse:
espefuse.py burn_key flash_encryption key.bin
6 Use the esptool tool to turn on the Control Bits for Flash Encryption in Efuse:
espefuse.py burn_efuse FLASH_CRYPT_CONFIG 0xF FLASH_CRYPT_CNT 1
Instructions
If the Flash encryption key (
key.bin) is not written in Efuse or not turn on the Control Bits for Flash encryption in Efuse, the encrypted “firmware” (bin file) does not boot properly.After Flash encryption is enabled, the Flash Download Tool cannot be used to reprogram the firmware and erase the firmware, but the esptool tool is supported to reprogram the firmware and erase the firmware.
**For encrypted modules encrypted by Flash to reprogram firmware, the reprogram firmware requires to turn on the configuration option of “
Flash Encryption” in menuconfig, and use the same encryption key (key.bin) as the old firmware to encrypt and flash, so that the reprogram firmware can boot properly. ****Burning encryption keys in Efuse is non-erasable, so new keys cannot be reprogrammed. **
This solution meets the requirements that it can also use the esptool tool to
reprogram the firmware, erase, read Flashoperation on the module after the module production firmware is encrypted, but the read firmware is encrypted firmware. If the new module does not flash the key (key.bin) corresponding to the encryption firmware, only reprogram the encrypted firmware to the new module, it can’t boot properly.
边栏推荐
- 激进技术派 vs 项目保守派的微服务架构之争
- Wanghongru research group of Institute of genomics, Chinese Academy of Agricultural Sciences is cordially invited to join
- The block:usdd has strong growth momentum
- Grain Mall (I)
- Machine learning concept drift detection method (Apria)
- Halcon模板匹配
- 【云端心声 建议征集】云商店焕新升级:提有效建议,赢海量码豆、华为AI音箱2!
- 爬虫初级学习
- [cloud native] what is the "grid" of service grid?
- Scala basic tutorial -- 14 -- implicit conversion
猜你喜欢
ByteDance dev better technology salon was successfully held, and we joined hands with Huatai to share our experience in improving the efficiency of web research and development
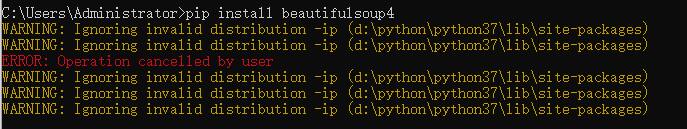
爬虫(6) - 网页数据解析(2) | BeautifulSoup4在爬虫中的使用

What types of Thawte wildcard SSL certificates provide
Grain Mall (I)
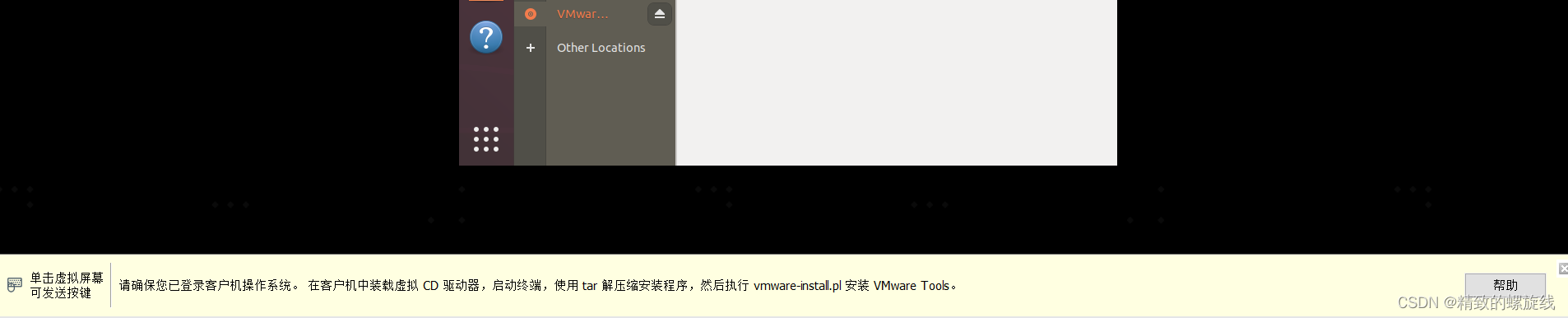
Installation and use of VMware Tools and open VM tools: solve the problems of incomplete screen and unable to transfer files of virtual machines
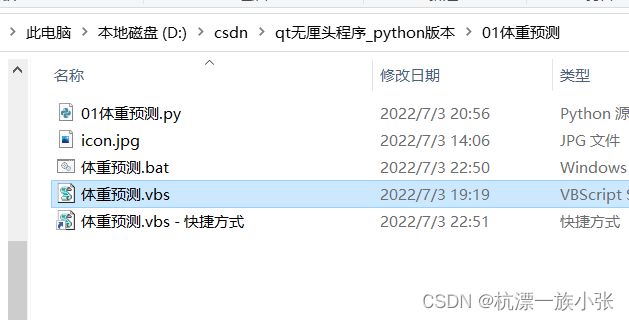
How to modify icons in VBS or VBE
Nature Microbiology | 可感染阿斯加德古菌的六种深海沉积物中的病毒基因组
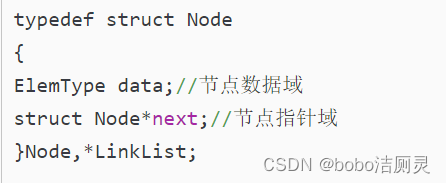
Li Kou brush question diary /day3/2022.6.25
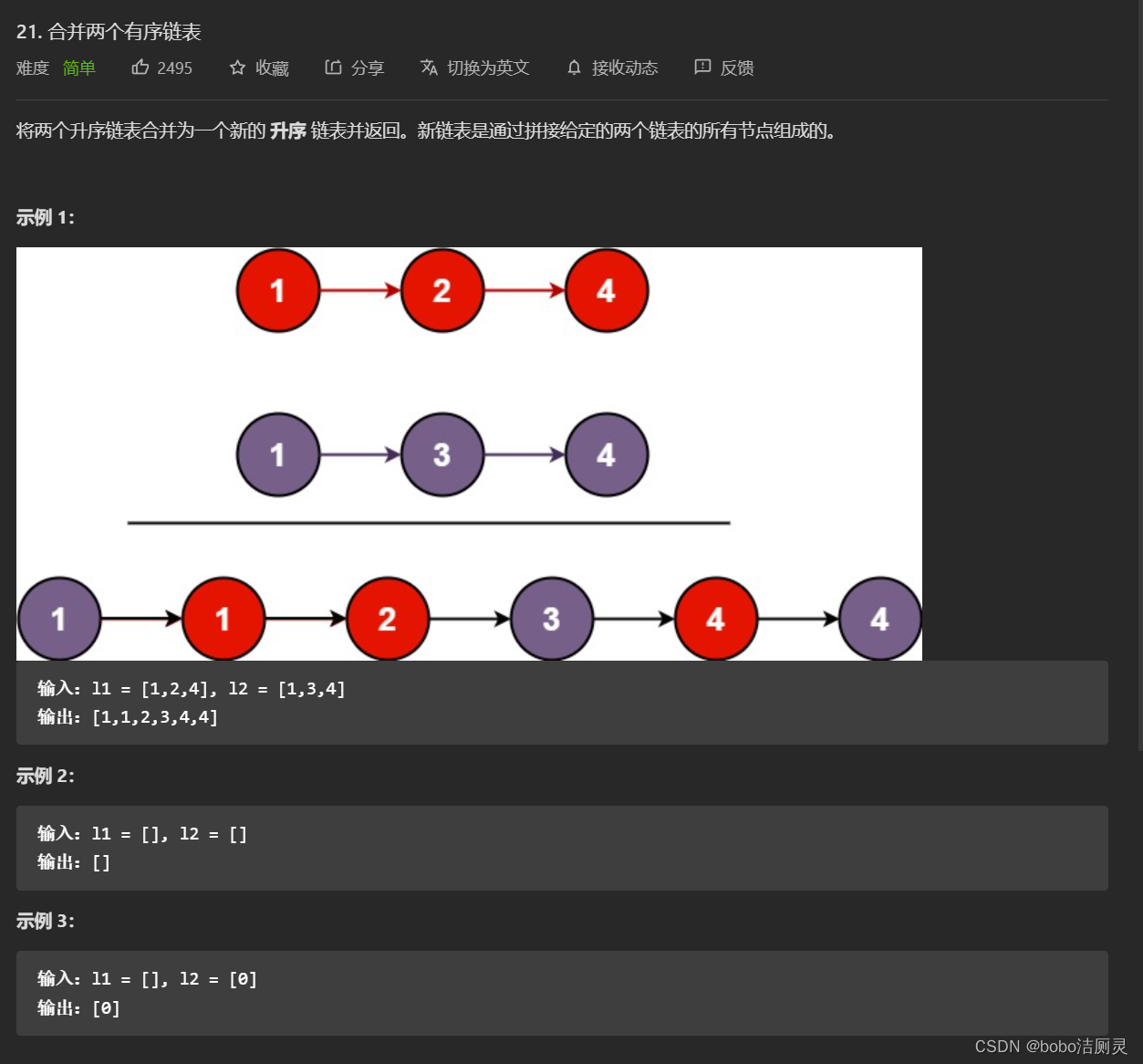
力扣刷题日记/day7/2022.6.29
TorchDrug教程
随机推荐
Journal des problèmes de brosse à boutons de force / day6 / 6.28
一种将Tree-LSTM的强化学习用于连接顺序选择的方法
Scala基础教程--19--Actor
.NET ORM框架HiSql实战-第二章-使用Hisql实现菜单管理(增删改查)
如何提高开发质量
Li Kou brush question diary /day7/6.30
Wireshark packet capturing TLS protocol bar displays version inconsistency
[2022 Jiangxi graduate mathematical modeling] curling movement idea analysis and code implementation
Learning path PHP -- phpstudy "hosts file does not exist or is blocked from opening" when creating the project
The block:usdd has strong growth momentum
未来几年中,软件测试的几大趋势是什么?
被忽视的问题:测试环境配置管理
Nature microbiology | viral genomes in six deep-sea sediments that can infect Archaea asgardii
ThreadLocal原理与使用
Scala basic tutorial -- 14 -- implicit conversion
Angry bird design based on unity
MXNet对GoogLeNet的实现(并行连结网络)
vbs或vbe如何修改图标
2022 ByteDance daily practice experience (Tiktok)
How to improve development quality