当前位置:网站首页>Resumption of attack and defense drill
Resumption of attack and defense drill
2022-07-01 23:44:00 【weixin_ forty-eight million one hundred and seventy thousand fo】
Recently, I participated in a two-week offensive and defensive drill , It is also the first time to participate in offensive and defensive activities , It feels quite different from usual .
When I first arrived at the scene, I said that I mainly did the work of the blue team , But Party A's assets are not clear , So I asked Party A for a balance sheet at the first time , And understand the distribution of assets in the network area , But how many assets are there , Maybe Party A can't figure it out .
replay :
1, Understand the release of assets and network topology
I feel this is a very important point , It can be determined that the attacker hit that position , If assets are uncertain , I don't even know about the stolen house .
2, When analyzing threat logs, read more with cookie,session,token,refer Information about
Generally, when the attack team can't score , I will get my account and password by fishing , So as to enter the backstage , At this time, our threat detection system may not find . however , Generally, the attack team will find the upload point after entering the backstage , See if you can upload it webshell, Or launch other attacks , At this time, there is a record . By combining the request header cookie,session,token,refer Information to determine whether the attacker has entered the background and the specific time point , In order to trace the application log .
In addition to the basis ip Inquire about , It can also be based on UA Inquire about , Or look for the tool logo
3, Don't panic when there is a vulnerability alarm
Generally, when a vulnerability alarm occurs, it is not necessarily an attack , It may also be the normal request of business personnel . such as , Developers' development behavior is not standardized , Request that the headband be partially sql sentence , This may be reported sql Inject successful vulnerability . Whether it is an attack depends on the context of the log , such as : When there is a directory list vulnerability , We can query attacks IP Logging of , If there are a lot of sensitive file requests after the directory list , Then it may be data removal , At this time, we need to start the troubleshooting and disposal process .
4, The traceability process pays more attention to command execution , Attack messages such as code execution
Generally, such messages will have rebound IP Address or domain name . About IP You can go to fofa Search such websites , Some will have to IP The corresponding domain name . Domain name can check the record information ,whois Check whether there is personal information . At the same time, this information can also be thrown into the threat intelligence collection website , See if there is any other information . Email counter check ,GitHub Inquire about ,ip Longitude and latitude positioning , Website forgot password function , Register function, locate account number, etc , All these things can be used .
边栏推荐
- Various global files related to [.Net core] program
- Reproduction process and problems of analog transformer (ICLR 2022 Spotlight)
- .env.xxx 文件,加了常量,却undefined
- TS初次使用、ts类型
- 常见的积分商城游戏类型有哪些?
- Similarities and differences between the defined identity execution function authid determiner and PostgreSQL in Oracle
- golang中的iota
- 力扣今日题-241. 为运算表达式设计优先级
- Huawei HMS core joins hands with hypergraph to inject new momentum into 3D GIS
- De PIP. Interne. CLI. Main Import main modulenotfounderror: No module named 'PIP'
猜你喜欢

Why is PHP called hypertext preprocessor
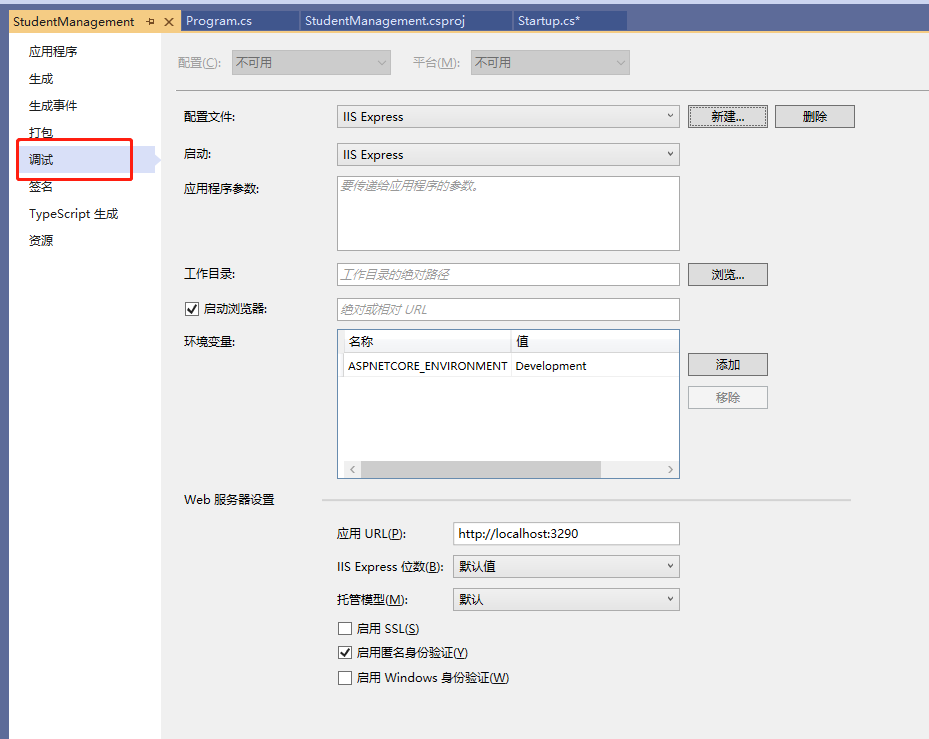
【.Net Core】程序相关各种全局文件
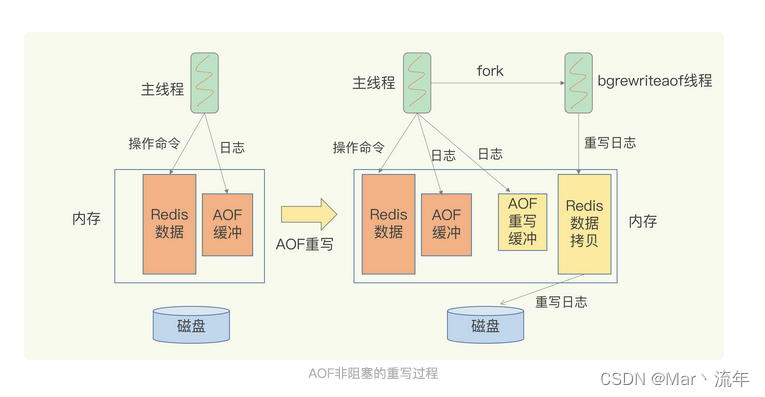
Redis AOF log

物联网应用技术专业是属于什么类
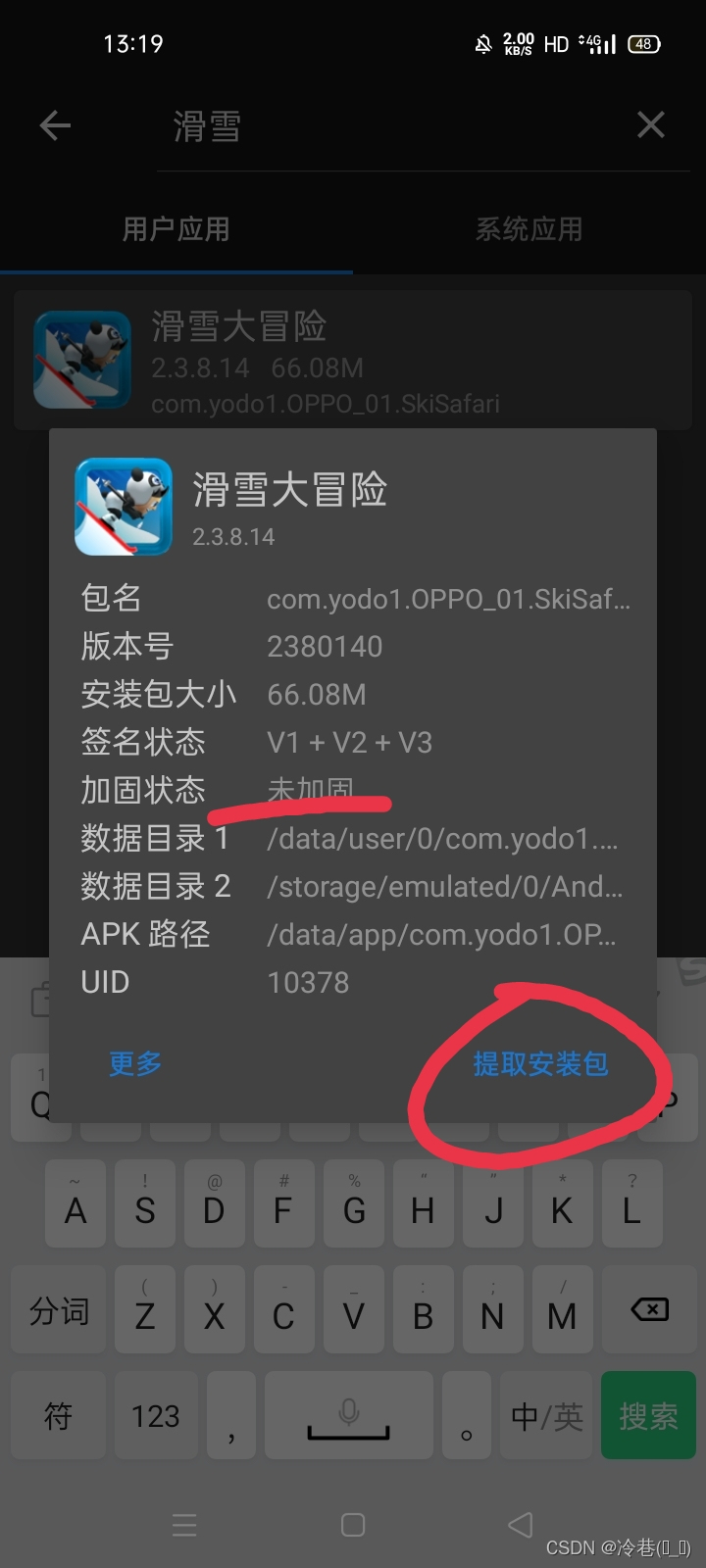
MT manager test skiing Adventure

Redis RDB快照

kubernetes资源对象介绍及常用命令(三)

使用uni-simple-router,动态传参 TypeError: Cannot convert undefined or null to object

Notblank and notempty
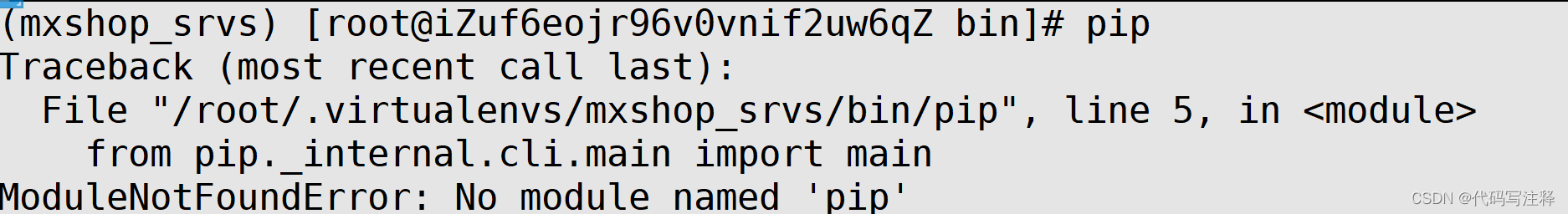
De PIP. Interne. CLI. Main Import main modulenotfounderror: No module named 'PIP'
随机推荐
SecurityUtils. getSubject(). How to solve the problem that getprincipal() is null
MySQL Replication中并行复制怎么实现
ADO.NET之SqlDataAdpter对象
Distance measurement - Hamming distance
【ES实战】ES上的安全性运行方式
Paramètres communs de matplotlib
Reproduction process and problems of analog transformer (ICLR 2022 Spotlight)
golang中的iota
mysql:insert ignore、insert和replace区别
sql 优化
物联网技术应用属于什么专业分类
[understanding of opportunity-35]: Guiguzi - flying clamp - the art of remote connection, remote control and remote testing
Depth first search and breadth first search of graph traversal
Kubernetes resource object introduction and common commands (III)
Zero foundation tutorial of Internet of things development
Huawei HMS core joins hands with hypergraph to inject new momentum into 3D GIS
问题随记 —— /usr/bin/perl is needed by MySQL-server-5.1.73-1.glibc23.x86_64
Notblank and notempty
2022-07-01:某公司年会上,大家要玩一食发奖金游戏,一共有n个员工, 每个员工都有建设积分和捣乱积分, 他们需要排成一队,在队伍最前面的一定是老板
cookie、session、tooken