当前位置:网站首页>Dongle data collection
Dongle data collection
2022-07-01 06:15:00 【Tom】
Dongle data collection
Product selection
San Marino offers developers a variety of options , From hard lock series 、 Soft lock ( Soft authorization ) Authorization to the cloud , Developers can design products according to their needs 、 The needs of the scenario or the preferences of the user , Choose the ideal protection 、 Authorization scheme .
The following are the common types of selection preferences :
Suitable for choosing hard lock : In an offline environment , Want plug and play , And will not be affected by system reinstallation or hardware replacement ; I hope to equip my software product with a physical hardware lock ; Or with a protective lock with a clock chip , It can accurately control the running time of software and other scenarios .
It is suitable for the scenario of choosing soft authorization : In virtualization 、 Software deployed in a container environment ; You want to bind the software to a specific hardware device ; No, USB Interface devices ; For expanding overseas business ( End users don't like hard locks ); I hope it is easier to set and manage licenses ; Those who do not want to incur hardware inventory management or mailing costs ; We hope to avoid the situation that hard locks cannot be delivered to users in time during the epidemic .
It is suitable for the scenario of cloud authorization : On-line + Offline mixed application scenarios ; You need to verify your license online , Scenarios that require frequent offline use ; Need to deploy in containerization 、 virtualization 、 Scenarios in public or private cloud environments ; It is hoped that the client can 、 Cross device use of software anywhere ; System reinstallation or hardware replacement are relatively frequent ( No software license is required for migration work ); It is hoped that the administrator can pass the web A scenario in which the page performs a series of permission management operations on the user identity ; I hope I can understand the product usage and other scenarios in real time .
General application encryption scheme
Write the encrypted code into the source code , That is, embedded encryption . Embedded encryption effectively integrates the encrypted code with the source code , Make the code look more complex , Thus increasing the difficulty of cracking . therefore , Embedded encryption is our preferred encryption method . You can choose the following encryption process :
- Find out if the dongle exists
- Random numbers are generated by the system X, Take this as the one-time verification factor
- Divide random numbers into two paths : All the way with the user input key Value operation , Get the check value ; Send the other way to the dongle , Get the return value by writing data in the chip .
- Compare the check value with the return value , Continue the program when the two values are equal , Otherwise exit the program
The above scheme is the basic encryption process of dongle , Of course, users can use the secondary development zone of dongle to implement flexible encryption schemes .
Application recommendation for secondary development zone
Using the secondary development zone can not only realize simple data 、 Character reading and writing function , It can also realize the commercial sales mode of multiple schemes . Sub module sales : Divide the software into several modules according to functions , Set the password of each module and write it into the dongle storage area , When accessing this function module, you need to enter the correct corresponding password . Rental sales : The Golden Shield dongle chip comes with Counter The interface function , Automatically subtract one for each call , It can realize the limited time function of the software , And the remote termination period . For powerful hardware clock lock , Using interface functions , It can strictly control the time of software use , It is especially suitable for the software with strict time limit, such as the examination system .
Encryption suggestions
Information encryption is not just about how to use ! It's more about how to encrypt ? We may not be able to understand and learn the encryption source code , But we can understand and skillfully use various skills of encryption program ! Suzhi technology dongle has sorted out some skills in the use of dongles and shared them with you !
- Call cryptographic locks in rarely used code . Then the program that seems to have been decoded will often have abnormal phenomena .
- Call the encryption lock according to the time . Such as : Data invoked in the morning and in the afternoon ( Or the next day ) Use . It takes a day or several days for the decipherer to analyze the data . This can drag the interpreter .
- The encryption lock return value is deleted immediately after use .
- Take the return value of the encryption lock as the index of the array 、 Constant 、 Calculation unit and check code .
- The return value of the encryption lock is used as a pointer to control program execution or as an index to jump in different tables .
- Use the return value of the encryption lock to encrypt or decrypt part of the code or data .
- If the return value of the encryption lock is found to be wrong , Do not display error messages .
- The cryptographic lock verification function does not have to be defined as a separate function , And it can be defined as several small functions for decentralized use .
- Check the checksum of the program code , In case of illegal modification .
- Cover real encrypted lock access with various random access . Handle responses to random queries , But don't really use it .
Reference documents
thalesgroup
Qinzhi technology
common problem
Solution
Learn about dongles
Software protection scheme
Get to know soft authorization for the first time
About soft licensing
边栏推荐
- IT服务管理(ITSM)在高等教育领域的应用
- SystemVerilog learning-08-random constraints and thread control
- Database problems, how to optimize Oracle SQL query statements faster and more efficient
- 【企业数据安全】升级备份策略 保障企业数据安全
- SystemVerilog learning-06-class encapsulation
- Skywalking integrated Nacos dynamic configuration
- 端口扫描工具对企业有什么帮助?
- 数据库er图组成要素
- ManageEngine卓豪助您符合ISO 20000标准(四)
- 1034 Head of a Gang
猜你喜欢

相同区域 多源栅格数据 各个像元行列号一致,即行数列数相同,像元大小相同

Tidb single machine simulation deployment production environment cluster (closed pit practice, personal test is effective)

Tidb database characteristics summary

Understanding of C manualresetevent class

freeswitch拨打分机号

高阶-二叉平衡树

π disk, turning your computer into a personal private cloud

【企业数据安全】升级备份策略 保障企业数据安全

机械臂速成小指南(六):步进电机驱动器
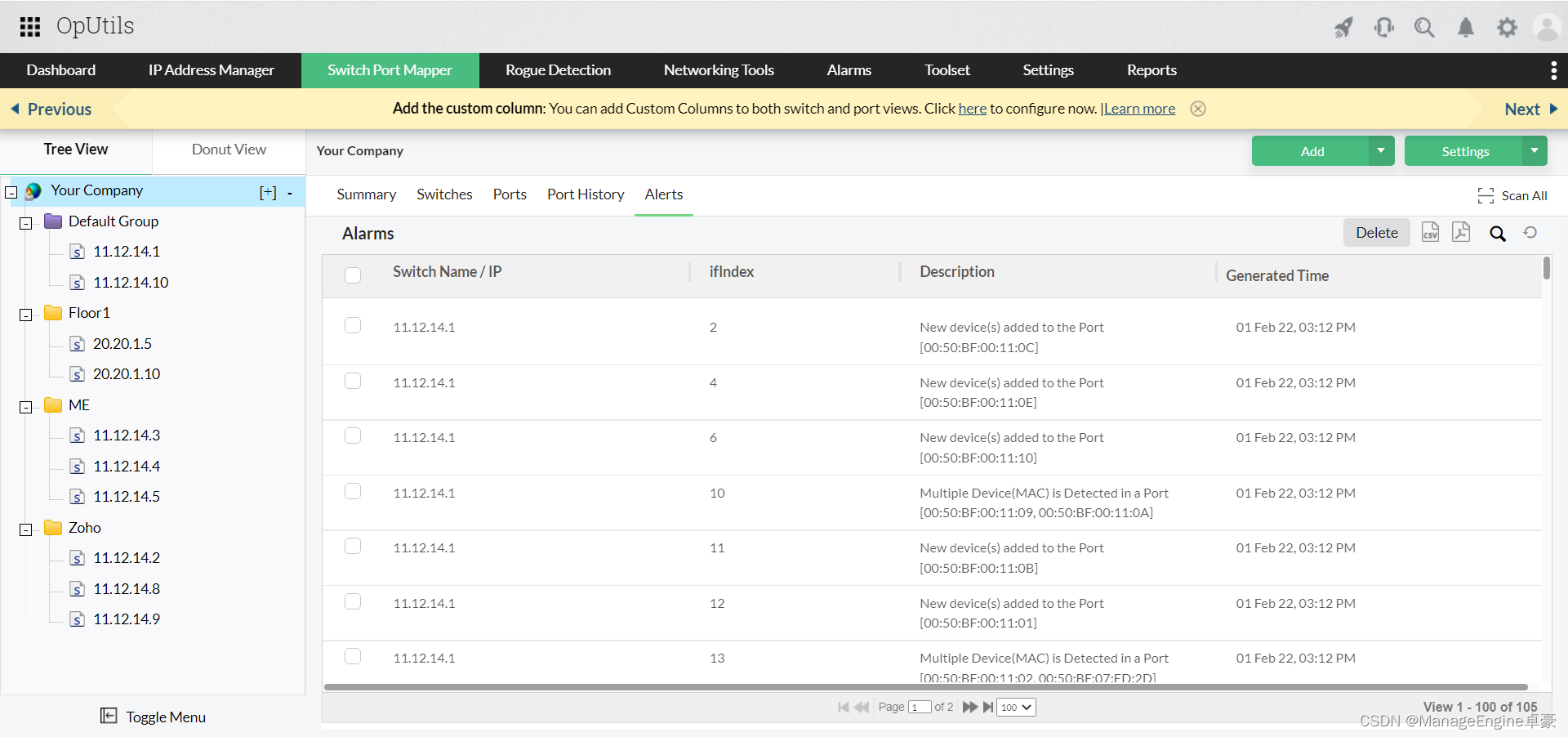
端口扫描工具对企业有什么帮助?
随机推荐
Timer based on LabVIEW
PLA不粘贴在床上:6个简单的解决方案
69 Cesium代码datasource加载geojson
HDU - 1501 zipper (memory deep search)
阶乘约数(唯一分解定理)
【LeetCode】Day91-存在重复元素
让田头村变甜头村的特色农产品是仙景芋还是白菜
highmap gejson数据格式转换脚本
Excel dynamic chart
Projects and dependencies in ABP learning solutions
1034 Head of a Gang
three. JS summary
高阶-二叉平衡树
Using Baidu map to query national subway lines
【网络安全工具】USB控制软件有什么用
Tidb database characteristics summary
One of the characteristic agricultural products that make Tiantou village, Guankou Town, Xiamen into a "sweet" village is
Primary application case of Excel DuPont analyzer
MinIO纠错码、分布式MinIO集群搭建及启动
Elements of database ER diagram