当前位置:网站首页>Public key \ private SSH avoid password login
Public key \ private SSH avoid password login
2022-07-07 01:42:00 【Full stack programmer webmaster】
Hello everyone , I meet you again , I'm the king of the whole stack
I've seen it before , Never mind , Before using public key management , The filing machine of Tencent virtual machine , It's very hair like , Check the relevant information , Here's a summary :
character a:192.168.7.188 (ubuntu)
character b:192.168.7.17 (centos)
Hope from a land b When , No need to enter password. My original idea was to b The public key of a Of key In the document , This way a Use public key and b The private key Match . The result is just the opposite ,
The actual operation is to a The public key of b Of key In the document .
stay a Generate key on , command
ssh-keygen -t rsa ( The encryption type here is also the public key choice dsa)
The default will be ~/.ssh A pair of keys exist under the folder
We will id_rsa.pub Copy content from to b Mechanical authorized_keys Go on ok 了 , Assuming that the file does not exist, create another
Here is how to use public key and key management server User rights , Like a server Many developers use , When an employee leaves the company , We all need to change password What? , This is troublesome for everyone , With the key , We usually require everyone to use their own public key to log in server, When employees leave , The administrator only needs to delete the public key of the resigned employee .
If it appears Agent admitted failure to sign using the key. function :ssh-add ~/.ssh/id_rsa
Copyright notice : This article is the original article of the blogger , Blog , Do not reprint without permission .
Publisher : Full stack programmer stack length , Reprint please indicate the source :https://javaforall.cn/116905.html Link to the original text :https://javaforall.cn
边栏推荐
- 前置机是什么意思?主要作用是什么?与堡垒机有什么区别?
- Reptile practice (VI): novel of climbing pen interesting Pavilion
- Can't you understand the code of linked list in C language? An article allows you to grasp the secondary pointer and deeply understand the various forms of parameter passing in the function parameter
- Baidu flying general BMN timing action positioning framework | data preparation and training guide (Part 1)
- AcWing 904. 虫洞 题解(spfa求负环)
- AcWing 1140. Shortest network (minimum spanning tree)
- Gin introduction practice
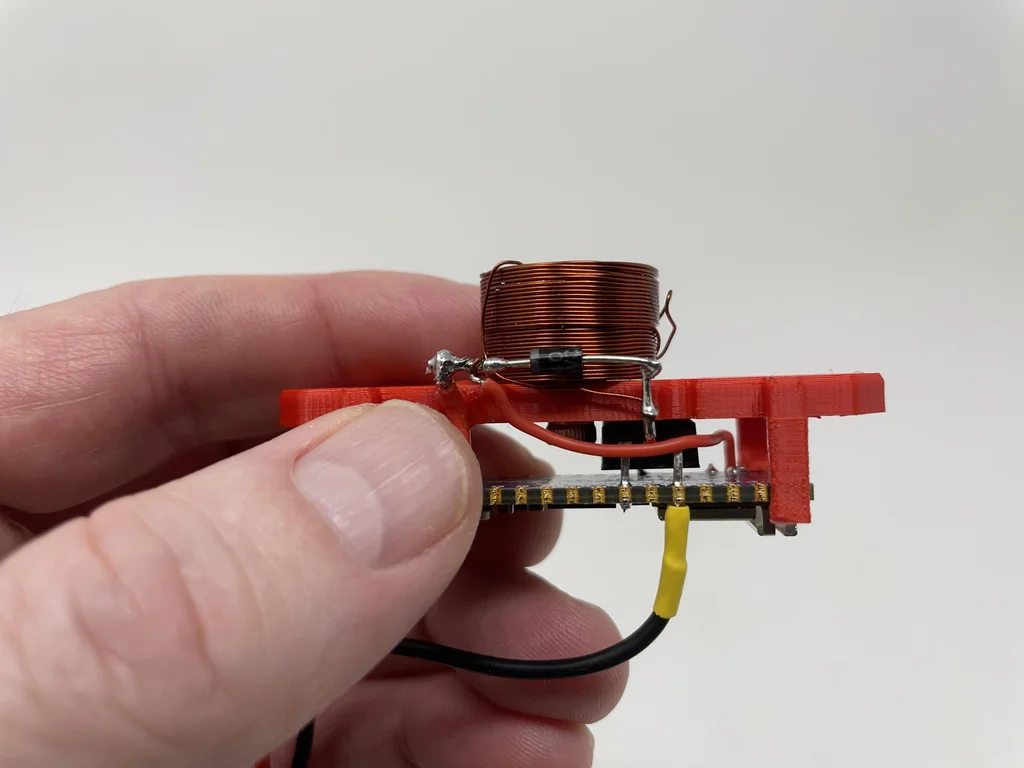
- 【芯片方案设计】脉搏血氧仪
- C语言实例_5
- Baidu flying general BMN timing action positioning framework | data preparation and training guide (Part 2)
猜你喜欢
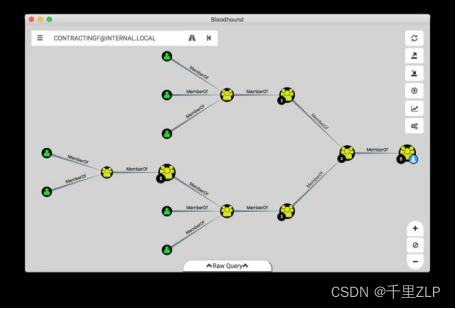
Instructions for using the domain analysis tool bloodhound
Make Jar, Not War
454-百度面经1

Typical problems of subnet division and super network construction
永久的摇篮
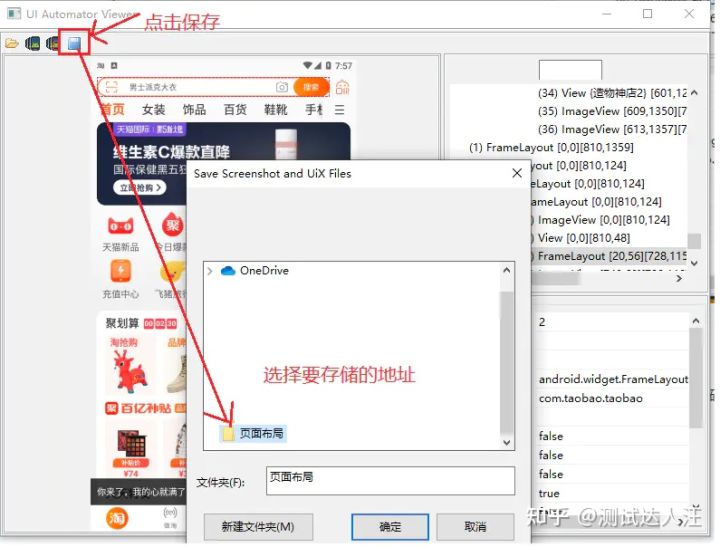
Appium自动化测试基础 — uiautomatorviewer定位工具
tansig和logsig的差异,为什么BP喜欢用tansig

Yunna - work order management system and process, work order management specification

云呐-工单管理制度及流程,工单管理规范
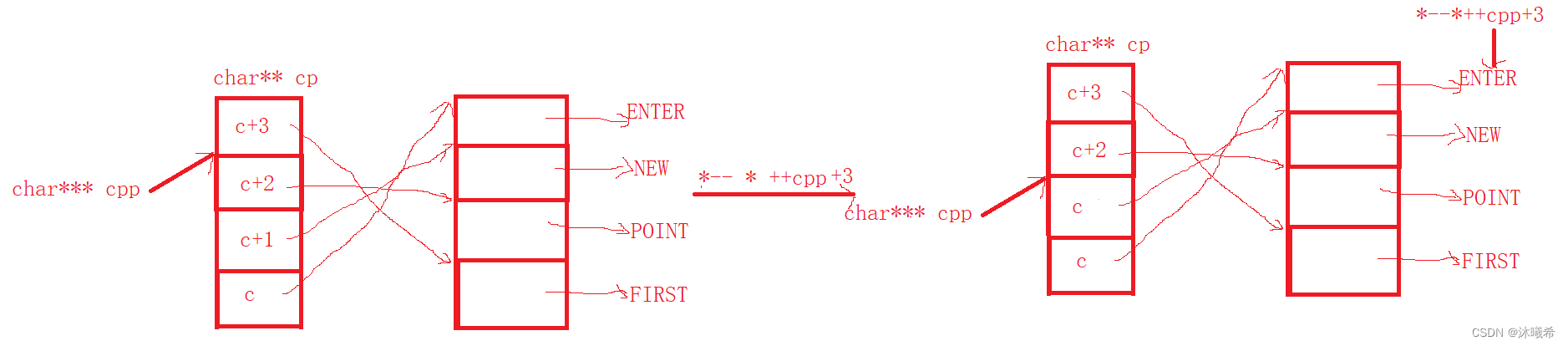
【C语言进阶篇】指针的8道笔试题
随机推荐
C语言实例_4
curl 命令
json学习初体验–第三者jar包实现bean、List、map创json格式
C language - array
IDEA常用的快捷键
THREE. AxesHelper is not a constructor
字符串的相关编程题
糊涂工具类(hutool)post请求设置body参数为json数据
交叉验证如何防止过拟合
JS ES5也可以創建常量?
Appium自动化测试基础 — uiautomatorviewer定位工具
2022 Google CTF SEGFAULT LABYRINTH wp
454-百度面经1
Baidu flying general BMN timing action positioning framework | data preparation and training guide (Part 2)
AcWing 1141. LAN problem solving (kruskalkruskal finding the minimum spanning tree)
AcWing 1142. 繁忙的都市 题解(最小生成树)
Vocabulary in Data Book
Comparison of picture beds of free white whoring
mongodb查看表是否导入成功
云呐-工单管理制度及流程,工单管理规范