当前位置:网站首页>Common penetration test range
Common penetration test range
2022-07-03 09:00:00 【qfliweimin】
1.DVWA
As a rookie , Usually, the first shooting range I hear of is DVWA, Deploy and simply install the corresponding version PAM(PHP-Apache-MySQL), After simple configuration, you can use .
1、DVWA Range testable vulnerability : Brute force (Brute Force)、 Command injection (Command Injection)、 Cross-site request forgery (CSRF)、 File contains (File Inclusion)、 Upload files (File Upload)、 Insecure verification code (Insecure CAPTCHA)、SQL Inject (SQL Injection)、SQL Blind note (SQL Injection Blind)、 Reflective cross site scripting attack (XSS Reflected)、 Storage type cross site scripting attack (XSS Stored)
2、 It contains many common Web Loophole , The page is very compact , Integrate vulnerabilities in different business environments , Abstract it and summarize it into an integrated shooting range , It's also easy to use , And each vulnerability page can view the current source code , To some extent, it can improve 、 Proficiency in code auditing .
3、 The range includes four levels, from easy to difficult :Low、Medium、High、Impossible.
The following figure shows the vulnerability pages mentioned above 、 View the source code function 、 Vulnerability level .

summary : Environment installation is simple 、 There are many information available online 、 You can directly view the source code, which is convenient for learning 、 Different grade gradients are more conducive to mastering vulnerabilities , It is common to learn and understand as a novice web The vulnerability is very suitable , Writing programs at ordinary times can also learn from the relevant parts of the code . But only php Language related vulnerabilities , Only common web Loophole .
2、OWASP Broken Web Applications Project
The shooting range can be directly downloaded on the official website vm Open in , Use root owaspbwa Logging in will return to the shooting range address , You can directly access the shooting range .
Range by OWASP Specially for Web A shooting range developed by safety researchers and beginners , It contains a large number of training and experimental environments with known security vulnerabilities and real Web Applications
There are many environments involved , relative DVWA It is more close to actual combat , The shooting range is not only specially designed web Vulnerability application scenarios , It also includes some common open source web Applications , relative dvwa It's not just PHP, There's also Jsp、Asp、Python Dynamic scripting language environment , And the types of vulnerabilities are also very rich , In addition to the usual web Out of the hole , It also includes access control 、 Thread safety 、 Operations hide fields 、 Control parameters 、 Weak conversation cookie、web service 、Open Authentication invalid 、 dangerous HTML Notes, etc. , Perfect for learning and practicing .
Click on ”+“ You can see some information about the corresponding module , Here's the picture .

summary : Simple installation , Rich environment , There are many kinds of coverage vulnerabilities , Close to the real environment , Suitable for practical learning .dvwa Suitable for understanding vulnerabilities and simple vulnerability exploitation ,owaspbwa It is closer to the actual complex business environment . The only regret is that it hasn't been updated since a long time ago , Now I download the old version , There is not much collection of new vulnerabilities .
3、sqli-labs
sqli-labs Contains most sql Injection type , In a breakthrough mode , about sql Inject to exploit the vulnerability . The range vulnerability type is single , But yes. sql Injection class vulnerability exploitation is very comprehensive . Installation complexity and dvwa almost , Simple installation .

4、VulHub
Vulhub It's based on docker and docker-compose A collection of vulnerability environments , Enter the corresponding directory and execute a statement to start a new vulnerability environment , Make it easier to replicate vulnerabilities , Let security researchers focus more on the vulnerability principle itself .
When you build your own environment , because linux Problems with various versions , Failed many times , One click installation basic useless , The manual installation process is also very complicated , But finally reinstall a pure linux after , Installation successful . So follow the steps , It starts a phpxxe Of docker, After the test, I found that there was no problem with the installation .
Except that the installation process took a lot of time , But it's very comfortable to use . Different environments only need to execute a command to successfully build the environment . During the installation process, I know that this is an open source vulnerability environment project , It includes many different environments , yes owaspbwa in the future , There are many kinds of vulnerabilities , A shooting range with rich environment , And the vulnerabilities collected are relatively new , Suitable for a long-term study 、 Live range . Compared with other shooting ranges , Don't care web Server version 、 Download and install , Just install one docker You can run various vulnerability environments smoothly .
边栏推荐
- 推荐一个 yyds 的低代码开源项目
- Get the link behind? Parameter value after question mark
- 常见渗透测试靶场
- 浅谈企业信息化建设
- Find the combination number acwing 885 Find the combination number I
- Concurrent programming (VI) ABA problems and solutions under CAS
- Alibaba canaladmin deployment and canal cluster Ha Construction
- 教育信息化步入2.0,看看JNPF如何帮助教师减负,提高效率?
- Memory search acwing 901 skiing
- [rust notes] 11 practical features
猜你喜欢

22-06-28 西安 redis(02) 持久化机制、入门使用、事务控制、主从复制机制

Try to reprint an article about CSDN reprint
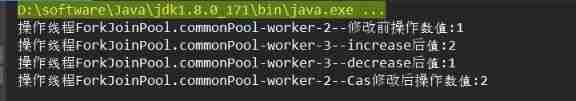
Concurrent programming (VI) ABA problems and solutions under CAS

Monotonic stack -84 The largest rectangle in the histogram

求组合数 AcWing 885. 求组合数 I

低代码起势,这款信息管理系统开发神器,你值得拥有!

记忆化搜索 AcWing 901. 滑雪

即时通讯IM,是时代进步的逆流?看看JNPF怎么说

求组合数 AcWing 886. 求组合数 II

Gaussian elimination acwing 883 Gauss elimination for solving linear equations
随机推荐
PHP mnemonic code full text 400 words to extract the first letter of each Chinese character
Notes and bugs generated during the use of h:i:s and y-m-d
SQL statement error of common bug caused by Excel cell content that is not paid attention to for a long time
Baidu editor ueeditor changes style
浅谈企业信息化建设
Alibaba canal actual combat
Dom4j遍历和更新XML
Methods of checking ports according to processes and checking processes according to ports
Dom4j traverses and updates XML
Debug debugging - Visual Studio 2022
20220630学习打卡
Using variables in sed command
即时通讯IM,是时代进步的逆流?看看JNPF怎么说
LeetCode 508. 出现次数最多的子树元素和
22-06-28 Xi'an redis (02) persistence mechanism, entry, transaction control, master-slave replication mechanism
Slice and index of array with data type
22-06-28 西安 redis(02) 持久化机制、入门使用、事务控制、主从复制机制
Introduction to the usage of getopts in shell
Concurrent programming (V) detailed explanation of atomic and unsafe magic classes
TP5 multi condition sorting