当前位置:网站首页>Is Dao safe? Build finance encountered a malicious governance takeover and was looted!
Is Dao safe? Build finance encountered a malicious governance takeover and was looted!
2022-07-01 19:44:00 【Chengdu Lianan】
today 2 month 15 Japan , First of all, I wish you a happy Lantern Festival ! Get together every day !
And in the early hours of this morning , Chengdu Lianan Chain Bing - Blockchain security situation awareness platform Public opinion monitoring shows that , Wind pitch DAO organization Build Finance The project is under governance attack . About this attack , Chengdu chain security technical team conducted analysis for the first time .
#1 Event overview
It is reported that ,Build Finance Is a self described as “ Decentralized risk builders ”, The goal is to encourage new projects by rewarding tokens . The idea is to use its original BUILD Tokens fund the project , In return , These projects will use BUILD Tokens to increase demand for them . Besides , The project consists of DAO maintain , That is, a decentralized organization participates in governance .( Extended reading :“DAO” What is it ?)
however , Hackers are quietly doing things , The project was maliciously managed by attackers , Hackers successfully control by getting enough votes Build The token contract , More than... Were cast in three transactions 10 Billions of BUILD Tokens, , And exhausted Balancer and Uniswap Most of the funds in the liquidity pool . After the incident , On twitter, the project team advised users not to buy... On any platform BUILD Tokens, , Project team members try to have a direct conversation with the attacker , But the other person doesn't seem interested in talking .

It seems that the project side has met another “ Capricious ” Hackers of . below , Let's take a look at the specific analysis process of the event .
#2 Event specific analysis
Round 1
Through the transaction tracking of the project , We found that 2022 year 2 month 12 Japan Build Finance The project has been stolen by an attacker , Then to 0xdcc8A38A The address was cast in three times for more than 10 Billions of BUILD Tokens, .



then 0xdcc8A38A The address will be 10 Billion tokens through Uniswap V2: BUILD The exchange will empty the transaction pool of the project party .

After observing the details of the transaction , We found that calling Build The token contract mint The address of the function coinage is also 0xdcc8A38A.

So let's look down , We observe the contract code of the project side in the figure below and find that it calls mint The address of a function can only be governance Address . The address of the coinage is 0xdcc8A38A, In other words, the contract is now governance Permission has been 0xdcc8A38A Got the address .

You can see the original from the code governance The permission belongs to the creator of the contract, that is, the 0x2Cb037BD6B7Fbd78f04756C99B7996F430c58172 Address .


We can't help but ask , that governance How permissions are transferred to 0xdcc8A38A What about it? ?
Round 2
By checking , We go through 2020 year 9 month 4 A transaction on the th found a clue , The attacker can only pass setGovernance Function to steal governance Authority . So during this period, the contract Creator 0x2Cb037BD Must have used setGovernance Function performs permission transfer .
By looking for 0x2Cb037BD The transaction record of the address is visible , On the same day, the creator used setGovernance function . transaction hash by 0xe3525247cea81ae98098817bc6bf6f6a16842b68544f1430926a363e790d33f2.


By looking inside Storage Visible permissions have been transferred to 0x38bce4b45f3d0d138927ab221560dac926999ba6 Address instead of the above 0xdcc8A38A Attack address . The transaction hash is :
0xe3525247cea81ae98098817bc6bf6f6a16842b68544f1430926a363e790d33f2.
By following up 0x38bce4b Address , Discovery is a Timelock contract , The contract can be called build Of token contract function setGovernance Function only executeTransaction function .

We follow up executeTransaction The function found one of Storage.

As can be seen from the above figure 0x38bce4b45f3d0d138927ab221560dac926999ba6 The address transfers the permission to 0x5a6ebeb6b61a80b2a2a5e0b4d893d731358d888583 Address , The transaction hash is 0x9a0c9d5d3da1019edf234d79af072c1a6acc93d21daebae4ced97ce5e41b2573, Call time is 2021 year 1 month 25 Japan .
By following up 0x5a6ebeb6 Address , As can be seen in the figure below 2022 year 2 month 9 Day by suho.eth The proposal launched ,0xdcc8A38A The attack address is 2022 year 2 month 11 The vote passed on the th . stay 4 Days ago will governance Permission changed to 0xdcc8A38A.

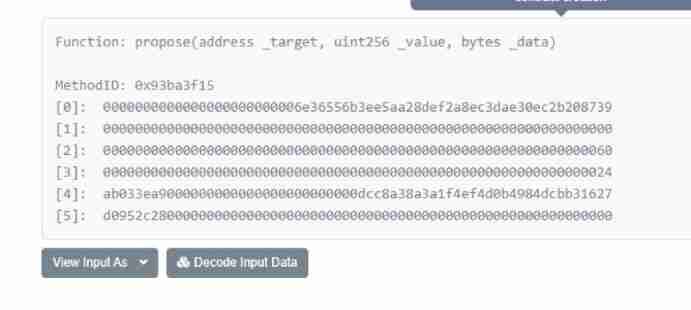
suho.eth Proposed changes initiated governance, The lower threshold set by the vote led to the proposal being passed , adopt call Call will build The contract governance Change to 0xdcc8A38A Address .



0x5a6ebeb6b61a80b2a2a5e0b4d893d731358d888583 Address part code .

Get... From this address governance After permission ,0xdcc8A38A Address through build Token contract mint The function casts itself about 10 Billions of build Tokens, , Then go to the trading pool to empty out liquidity .
The flow chart of obtaining permission is :

The attacker used a similar technique , The token assets held by the governance contract are transferred from another governance contract . The total profit this time is 162 individual ETH、20014 individual USDC 481405 individual DAI、75719 individual NCR about 112 Thousands of dollars .
Last , Chengdu Lianan reminds :DAO The contract should set an appropriate voting threshold , Achieve real decentralized governance , Avoiding a small number of votes will enable the proposal to be passed and successfully implemented , Suggestions can refer to openzeppelin The realization of officially provided Governance Contracts .
边栏推荐
猜你喜欢
A brief understanding of white box encryption technology
今日群里分享的面试题

Actual combat of flutter - fast implementation of audio and video call application
研究了11种实时聊天软件,我发现都具备这些功能…
![[AI server setup] CUDA environment](/img/ca/2acfc42ea3ba24934a89472a8632f6.png)
[AI server setup] CUDA environment
HLS4ML报错The board_part definition was not found for tul.com.tw:pynq-z2:part0:1.0.
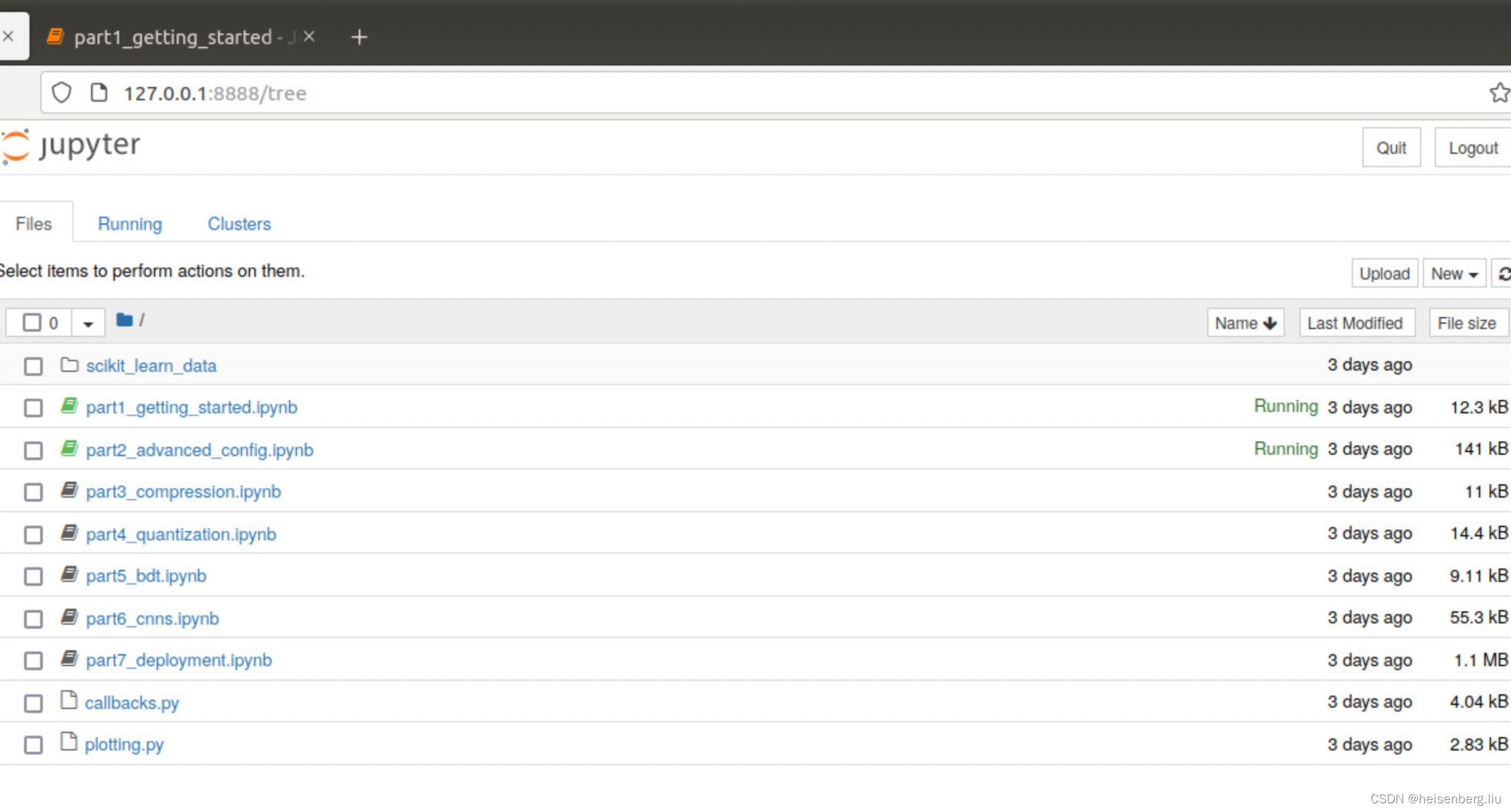
HLS4ML进入方法

类加载机制

Cookie和Session的相关概念
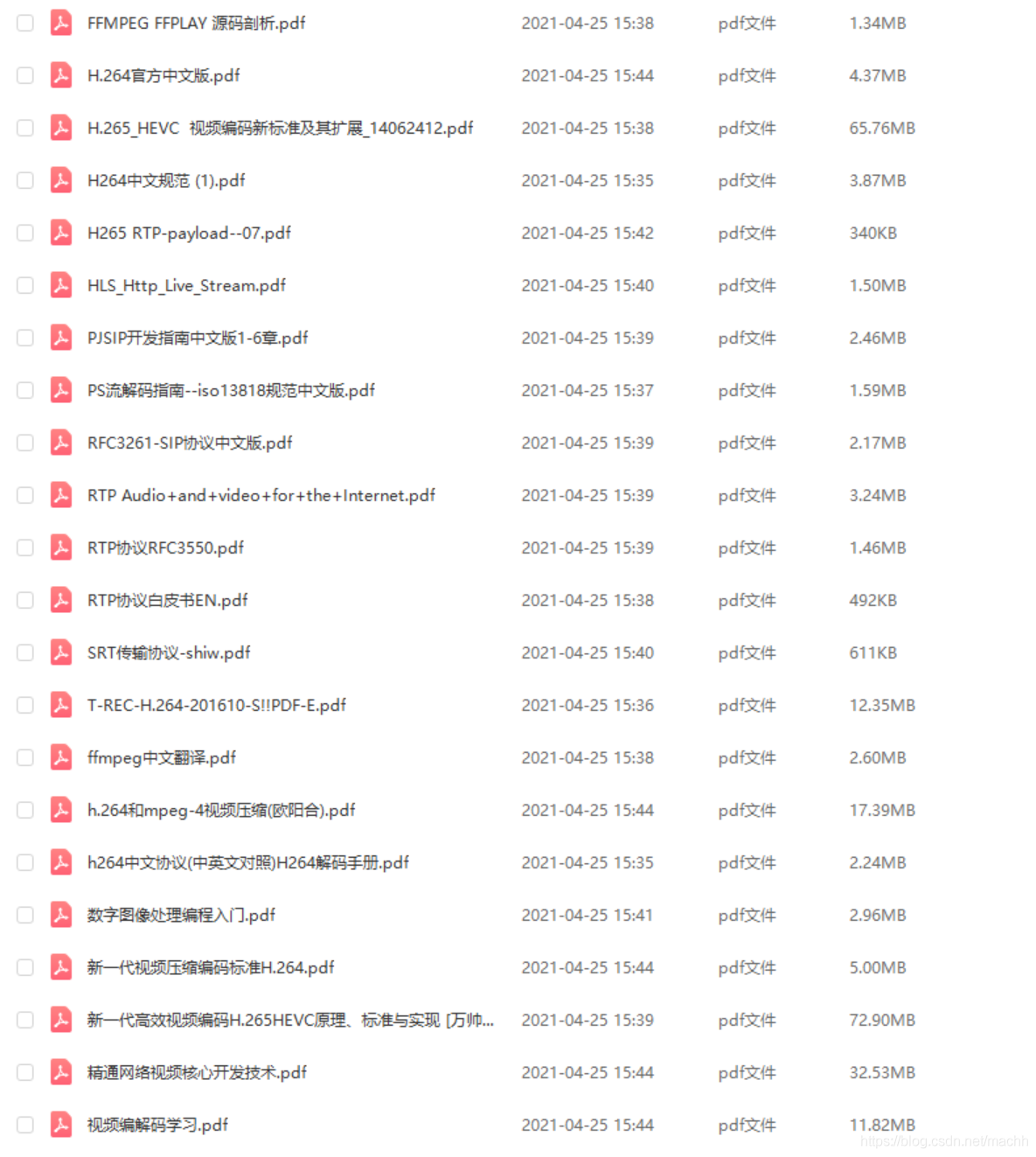
Audio and video, encoding and decoding related e-books, gadgets, packaged for free!
随机推荐
mysql 报错 Can‘t create table ‘demo01.tb_Student‘ (errno: 150)*
Shell advanced
Unreal Engine packaging project
PowerDesigner设计Name和Comment 替换
如何正确使用Vertx操作Redis(3.9.4带源码分析)
简版拼多多商品数据
Shell高级进阶
Opencv video quality diagnosis - VIDEO occlusion diagnosis
ddr4测试-2
GC垃圾回收
Nat penetration of gb28181
Leetcode 1380 lucky numbers in matrix [array] the leetcode path of heroding
mysql 報錯 Can‘t create table ‘demo01.tb_Student‘ (errno: 150)*
【let var const】
axure不显示元件库
HLS4ML/vivado HLS 报错解决方案
为定时器和延时器等其它情况的回调函数绑定当前作用域的this
通过js实现金字塔(星号金字塔,回文对称数字金字塔)
uni-app微信小程序一键登录获取权限功能
Actual combat of flutter - fast implementation of audio and video call application