当前位置:网站首页>Firewall basic transparent mode deployment and dual machine hot standby
Firewall basic transparent mode deployment and dual machine hot standby
2022-07-04 17:22:00 【51CTO】
Firewall transparent mode deployment and dual machine hot standby
Principle overview :
A firewall ( English :Firewall) Technology is through the organic combination of all kinds of software and hardware equipment for safety management and screening , Help the computer network in it 、 Build a relatively isolated protective barrier between the external networks , A technology to protect user data and information security .
The function of firewall technology is to discover and deal with the possible security risks when the computer network is running 、 Data transmission and so on , The treatment measures include isolation and protection , At the same time, it can record and test all operations in computer network security , To ensure the security of computer network operation , Guarantee the integrity of user data and information , Better for users 、 More secure computer network experience .
So-called “ A firewall ” It refers to an intranet and public access network ( Such as Internet) The way of separation , It is actually an applied security technology based on modern communication network technology and information security technology , Isolation technology . It is more and more used in the interconnection environment of private network and public network , Especially with access Internet The Internet is the most important .
Firewall is a protective barrier between the internal and external network environment with the help of hardware and software , So as to block the unsafe network factors of the computer . Only with the consent of the firewall , Users can enter the computer , If you don't agree, you'll be blocked out , The alarm function of firewall technology is very powerful , When an external user wants to enter the computer , The firewall will quickly send out the corresponding alarm , And remind users of their behavior , And make self judgment to decide whether to allow external users to enter the interior , As long as the user is in the network environment , This kind of firewall can carry out effective query , At the same time, the information found will be displayed to the user , Then users need to implement corresponding settings for the firewall according to their own needs , Block the disallowed user behavior . Through the firewall, you can also effectively view the traffic of information data , And it can also master the speed of uploading and downloading data information , It is convenient for users to have good control judgment on the use of computers , The internal situation of the computer can also be viewed through this firewall , It also has the function of starting and closing the program , And the internal log function of the computer system , In fact, it is also a summary of the real-time situation of the firewall and the internal security of the computer system .
Firewall is a kind of access control scale which is executed when two networks communicate , It can prevent hackers from accessing your network to the maximum extent . It's set up on different networks ( Such as trusted intranet and untrusted public network ) Or a combination of components between network security domains . It is the only access to information between different networks or network security domains , Be able to control according to the safety policy of the enterprise ( allow 、 Refuse 、 monitoring ) Information flow in and out of the network , And it has strong anti attack ability . It's about providing information security services , Infrastructure for network and information security . Logically , The firewall is a separator , A limiter , It's also an analyzer , Effectively monitored the intranet and Internet Any activity between , Ensure the security of the internal network .
The firewall scans its network traffic , This will filter out some attacks , In case it is executed on the target computer . Firewalls can also shut down unused ports . And it can also disable outgoing traffic on specific ports , Block the Trojan horse . Last , It can disable access from special sites , To prevent all communications from unknown intruders .
The barrier of network security
A firewall ( As a blocking point 、 The control points ) It can greatly improve the security of an internal network , And reduce risk by filtering unsafe Services . Because only carefully selected application protocols can pass through the firewall , So the network environment becomes more secure . For example, firewalls can prohibit such as well-known unsafe NFS Protocol access to protected network , In this way, it is impossible for external attackers to use these fragile protocols to attack the internal network . Firewalls can also protect the network from routing based attacks , Such as IP Source routing attacks and ICMP Redirection path in redirection . The firewall should be able to reject all messages of the above types of attacks and notify the firewall administrator .
Strengthen network security strategy
Configure through a firewall centric security scheme , All security software ( Like a password 、 encryption 、 Identity Authentication 、 Audit, etc ) Configure on the firewall . Compared with dispersing network security issues to various hosts , Centralized security management of firewall is more economical . For example, during network access , The one-time password system and other identity authentication systems do not have to be scattered on each host , And focus on the firewall .
Monitoring audit
If all access passes through the firewall , that , The firewall can record these accesses and log them , At the same time, it can also provide statistical data of network usage . When something suspicious happens , The firewall can give appropriate alarm , And provide detailed information on whether the network is monitored and attacked . in addition , It is also very important to collect the usage and misuse of a network . The first reason is to know whether the firewall can resist the detection and attack of attackers , And know whether the control of firewall is sufficient . Network usage statistics are also very important for network demand analysis and threat analysis .
Prevent the leakage of internal information
By using firewall to divide the internal network , It can realize the isolation of key network segments of intranet , Thus, the impact of local key or sensitive network security issues on the global network is limited . also , Privacy is an issue of great concern to the intranet , An unnoticed detail in an internal network may contain clues about security and attract the interest of external attackers , Some security vulnerabilities of the internal network have even been exposed . Using a firewall, you can hide those internal details, such as Finger,DNS Etc .Finger Displays the registered names of all users of the host 、 real name , Last login time and use shell Type, etc . however Finger The information displayed is very easy for attackers to learn . An attacker can know how often a system is used , Whether there are users connecting to the Internet in this system , Whether the system is noticed when being attacked, etc . Firewalls can also block information about internal networks DNS Information , The domain name of such a host and IP The address will not be known to the outside world . In addition to safety , The firewall also supports Internet Service enterprise internal network technology system VPN( Virtual private network ).
Logging and event notification
All data entering and leaving the network must pass through the firewall , The firewall records it through logs , It can provide detailed statistical information of network use . When a suspicious event occurs , The firewall can alarm and notify according to the mechanism , Provide information on whether the network is threatened .
The topology :
Basic configuration :
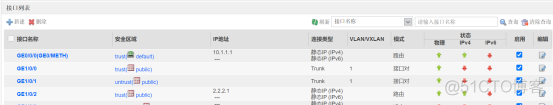
Firewall configuration interface :
FW1:
#
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 10.1.1.1 255.255.255.0
alias GE0/METH
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
#
interface GigabitEthernet1/0/0
portswitch
undo shutdown
port link-type trunk
link-group 1
detect-mode inline
#
interface GigabitEthernet1/0/1
portswitch
undo shutdown
port link-type trunk
link-group 1
detect-mode inline
#
interface GigabitEthernet1/0/2
undo shutdown
ip address 2.2.2.1 255.255.255.0
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
- 20.
- 21.
- 22.
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
- 30.
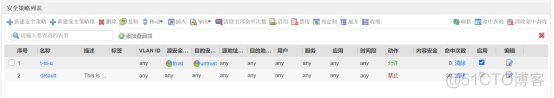
Configure security policy ;
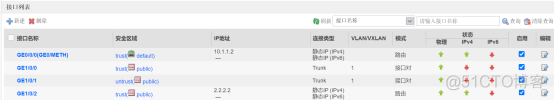
FW2:
#
interface GigabitEthernet0/0/0
undo shutdown
ip binding vpn-instance default
ip address 10.1.1.2 255.255.255.0
alias GE0/METH
service-manage http permit
service-manage https permit
service-manage ping permit
service-manage ssh permit
service-manage snmp permit
service-manage telnet permit
#
interface GigabitEthernet1/0/0
portswitch
undo shutdown
port link-type trunk
link-group 1
detect-mode inline
#
interface GigabitEthernet1/0/1
portswitch
undo shutdown
port link-type trunk
link-group 1
detect-mode inline
#
interface GigabitEthernet1/0/2
undo shutdown
ip address 2.2.2.2 255.255.255.0
- 1.
- 2.
- 3.
- 4.
- 5.
- 6.
- 7.
- 8.
- 9.
- 10.
- 11.
- 12.
- 13.
- 14.
- 15.
- 16.
- 17.
- 18.
- 19.
- 20.
- 21.
- 22.
- 23.
- 24.
- 25.
- 26.
- 27.
- 28.
- 29.
- 30.
Configure security policy ;

R1:
R2:
Configure high reliability :
FW1:

FW2:

End of experiment ;
remarks : If there is a mistake , Please understand !
This article is my study notes , For reference only ! If there is a repetition !!! Please contact me
边栏推荐
- 矿产行业商业供应链协同系统解决方案:构建数智化供应链平台,保障矿产资源安全供应
- kaili不能输入中文怎么办???
- How can programmers improve the speed of code writing?
- What grade does Anxin securities belong to? Is it safe to open an account
- Kunming Third Ring Road Closure project will pass through these places. Is there one near your home?
- Load test practice of pingcode performance test
- 2022年国内云管平台厂商哪家好?为什么?
- VMware Tools和open-vm-tools的安装与使用:解决虚拟机不全屏和无法传输文件的问题
- Is it safe for Great Wall Securities to open an account? How to open a securities account
- 散列表
猜你喜欢
How can programmers improve the speed of code writing?
Solution of commercial supply chain coordination system in the mineral industry: build a digital intelligent supply chain platform to ensure the safe supply of mineral resources
Can you really use MySQL explain?

第十八届IET交直流輸電國際會議(ACDC2022)於線上成功舉辦
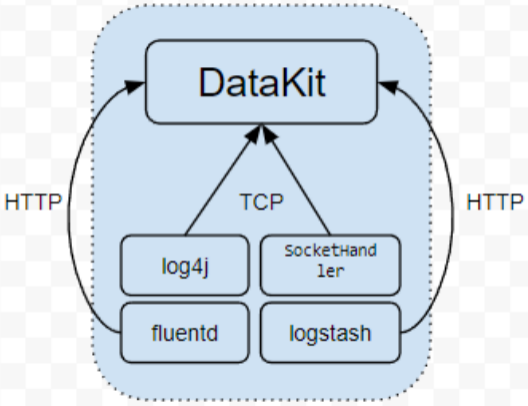
Datakit -- the real unified observability agent

World Environment Day | Chow Tai Fook serves wholeheartedly to promote carbon reduction and environmental protection
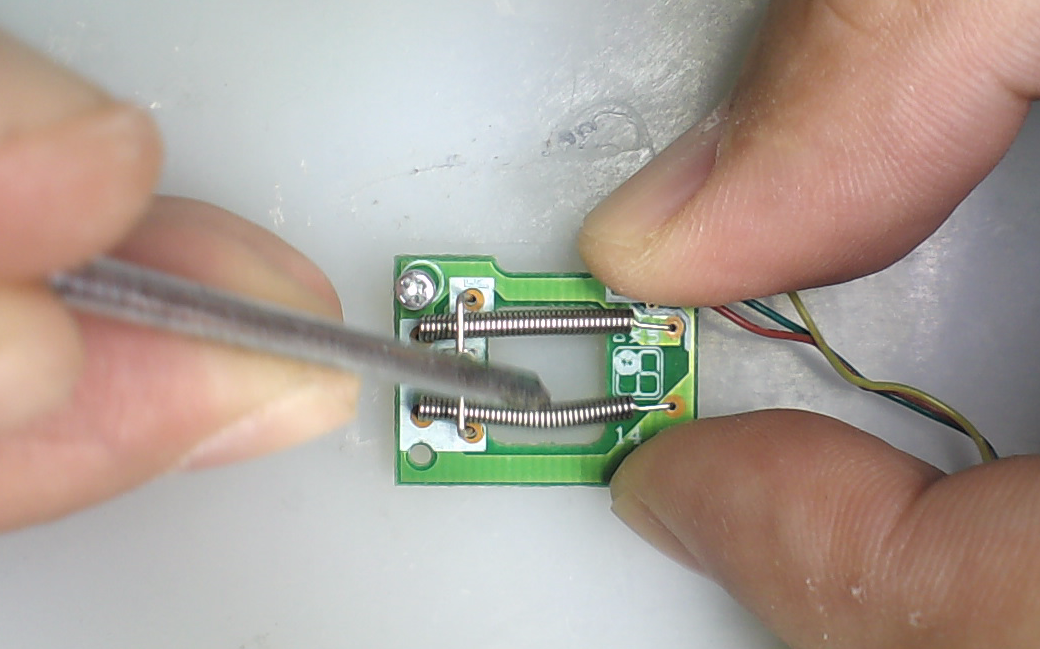
电子宠物小狗-内部结构是什么?
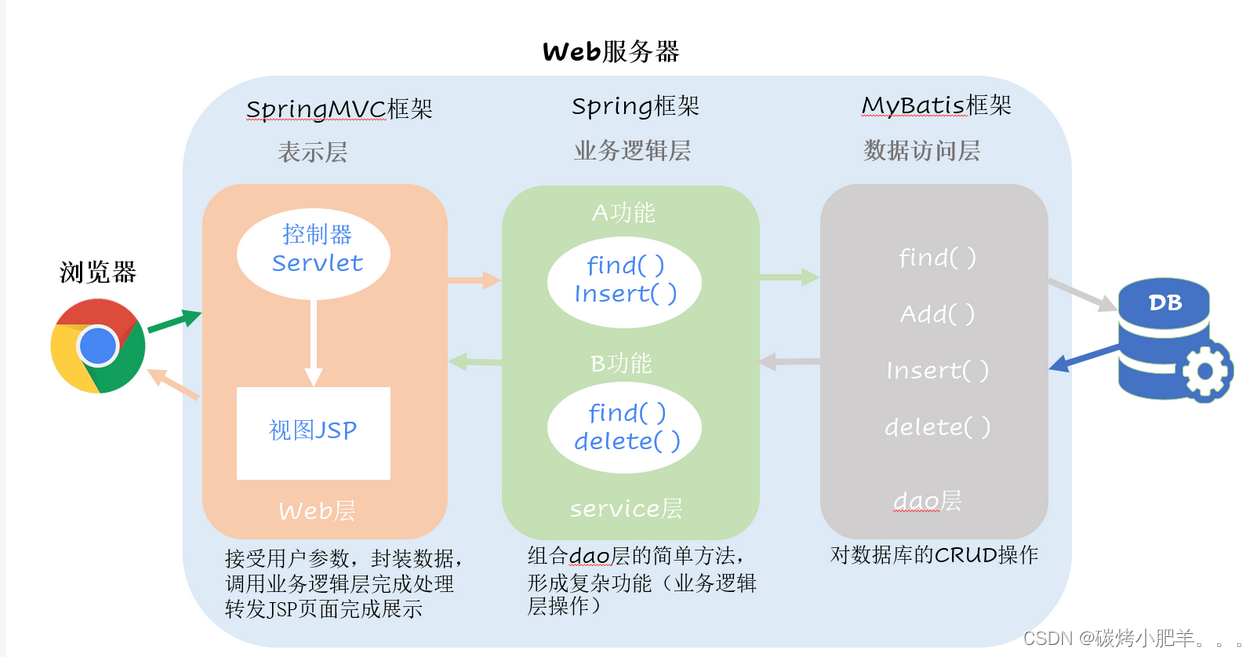
MVC模式和三层架构
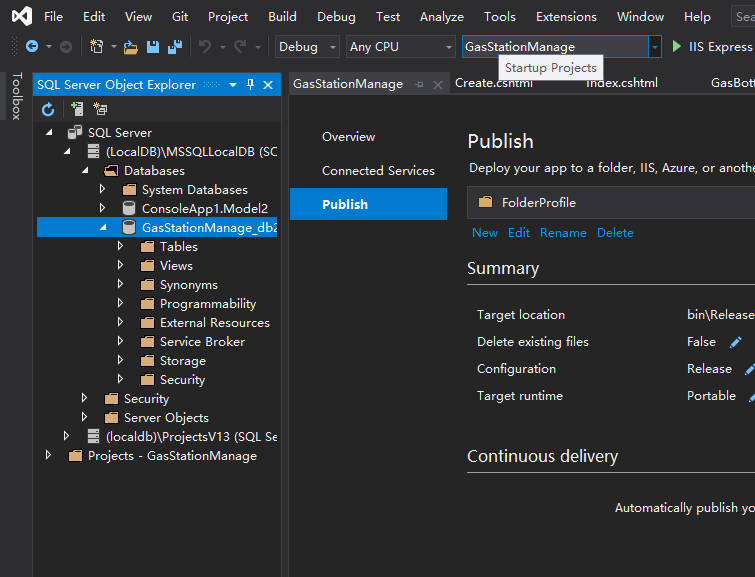
Visual Studio 2019 (LocalDB)MSSQLLocalDB SQL Server 2014 数据库版本为852无法打开,此服务器支持782
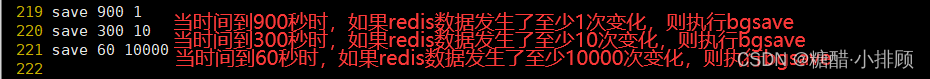
Readis configuration and optimization of NoSQL (final chapter)
随机推荐
GO开发:如何利用Go单例模式保障流媒体高并发的安全性?
智慧物流園區供應鏈管理系統解决方案:數智化供應鏈賦能物流運輸行業供應鏈新模式
矿产行业商业供应链协同系统解决方案:构建数智化供应链平台,保障矿产资源安全供应
How to "use" Perl modules in directories that are not in @inc- How do I 'use' a Perl module in a directory not in @INC?
APOC custom functions and procedures
VMware Tools和open-vm-tools的安装与使用:解决虚拟机不全屏和无法传输文件的问题
电子宠物小狗-内部结构是什么?
What grade does Anxin securities belong to? Is it safe to open an account
NoSQL之readis配置与优化(终章)
Ble HCI flow control mechanism
一加10 Pro和iPhone 13怎么选?
detectron2安装方法
【Unity UGUI】ScrollRect 动态缩放格子大小,自动定位到中间的格子
It's too convenient. You can complete the code release and approval by nailing it!
Chow Tai Fook fulfills the "centenary commitment" and sincerely serves to promote green environmental protection
网页游戏引擎
跳跃表实例
一文掌握数仓中auto analyze的使用
Is it safe for Anxin securities to open an account online? Is the account opening fee charged
太方便了,钉钉上就可完成代码发布审批啦!