当前位置:网站首页>Sentinel source code analysis part I sentinel overview
Sentinel source code analysis part I sentinel overview
2022-07-03 19:12:00 【Age people】
List of articles
Architecture diagram
The whole source code part is based on the use of the production environment
- 1.1 Sentinel Contains console : Configure current limiting rules [ System rules , Authority, etc ]
- 1.2 The console pushes rules to the data source (zookeeper etc. ) to ground
- 1.3 User process installation sentinel Module monitor zk To configure
- 2.1 Request to enter and hand it over to sentinel-adapter Intercept each module
- 2.2 According to Adapter Analytic contextName structure context
- 2.3 according to contextName structure EntranceNode
- 2.4 Find resources ResourceWrapper Corresponding ProcessorSlotChain
- 2.5 ProcessorSlotChain Handle [ Statistics , Current limiting , Rule verification, etc ]

| Object name | explain |
|---|---|
| EntranceNode | Entry node |
| StatisticNode | Statistics node , It contains two sliding window structures of second level and minute level |
| DefaultNode | Link nodes , It is used to count the data of a resource on the call link , Maintain the tree structure |
| ClusterNode | Cluster link information |
| Entry | every time Adapter Module resource calls will create a Entry, Trestle Structure [ Enter the first ]Entry1->Entry2->Entry3[ Exit first ], Contains the resource name 、curNode( Current statistics node ) When the call of information resources ends, you need entry.exit Restore call stack |
| Context | Call link context , Maintaining the entry node ,Entry link ,curNode |
One context Maintenance request link Entry, Every entry Both contain node, Maintain the tree relationship between resources and the storage of flow limiting information
Schematic diagram of current limiting
- The whole working mechanism of current limiting is handled through the responsibility chain
- Each resource corresponds to a ProcessorSlotChain
- This work chain passes Spi Mechanism discovery , Users can customize the corresponding implementation , And pass @SpiOrder Orchestration priority

context And entry Relationship
- context Represents the current thread context
- Unlike cross process tracing , Here we do not consider cross thread and cross process processing
- Multiple resource calls in the same thread , Will form the entry chain ,context Hold the relevant chain
- context Is the thread dimension . but context The name of is resource ResourceWrapper dimension
context And node Relationship
- According to the resource name, it will build EntranceNode
- context Will hold EntranceNode
node Self relationship tree maintenance
- Call resource throttling multiple times in a thread , be node Form a tree structure
- entry Form a linked list stack [ First in, then out ] structure
See the relationship between the three from the dimension of request and resource
- x Axis indicates request , The thread of each request builds a context, but context Could be the same , Generally, it is the resource name
- Each creation context Will get or build from the cache entranceNode, The same resource name corresponds to the same Node
- node It will build a tree structure , Indicates current statistics node Tree structure current limiting information
That's why ProcessorSlotChain Instantiate by resource dimension , Instead of singleton mode
Because of the statistics Slot Statistics are based on resource dimensions , If singleton is used, the current limit statistics of all resources are in the same node

- Above picture Node The same color means the same object
Expansion point - Official schematic diagram
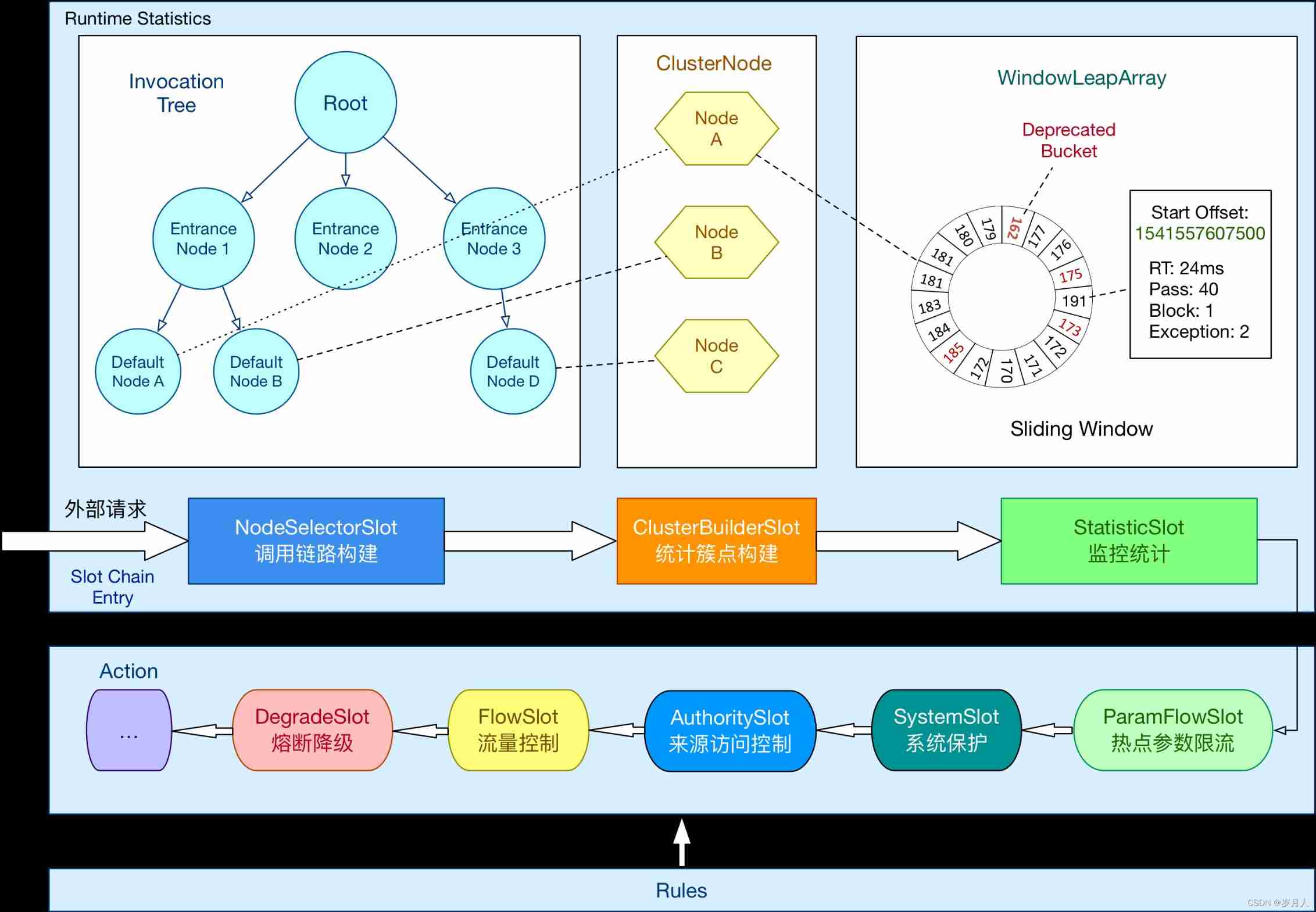
Expand a little bit node Class diagram

边栏推荐
- __ Weak and__ The difference between blocks
- Add control at the top of compose lazycolumn
- If the warehouse management communication is not in place, what problems will occur?
- In addition to the prickles that pierce your skin, there are poems and distant places that originally haunt you in plain life
- php-fpm的max_chindren的一些误区
- ActiveMQ的基础
- leetcode:556. Next larger element III [simulation + change as little as possible]
- Simple solution of physical backup and restore of Damon database
- [proteus simulation] a simple encrypted electronic password lock designed with 24C04 and 1602LCD
- Bad mentality leads to different results
猜你喜欢
Free sharing | linefriends hand account inner page | horizontal grid | not for sale
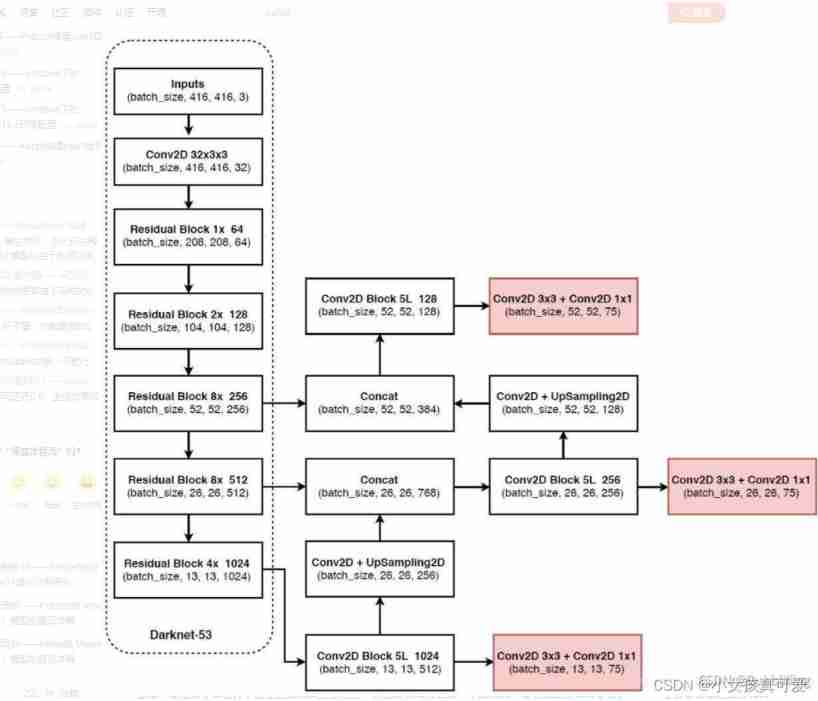
Yolov3 network model building
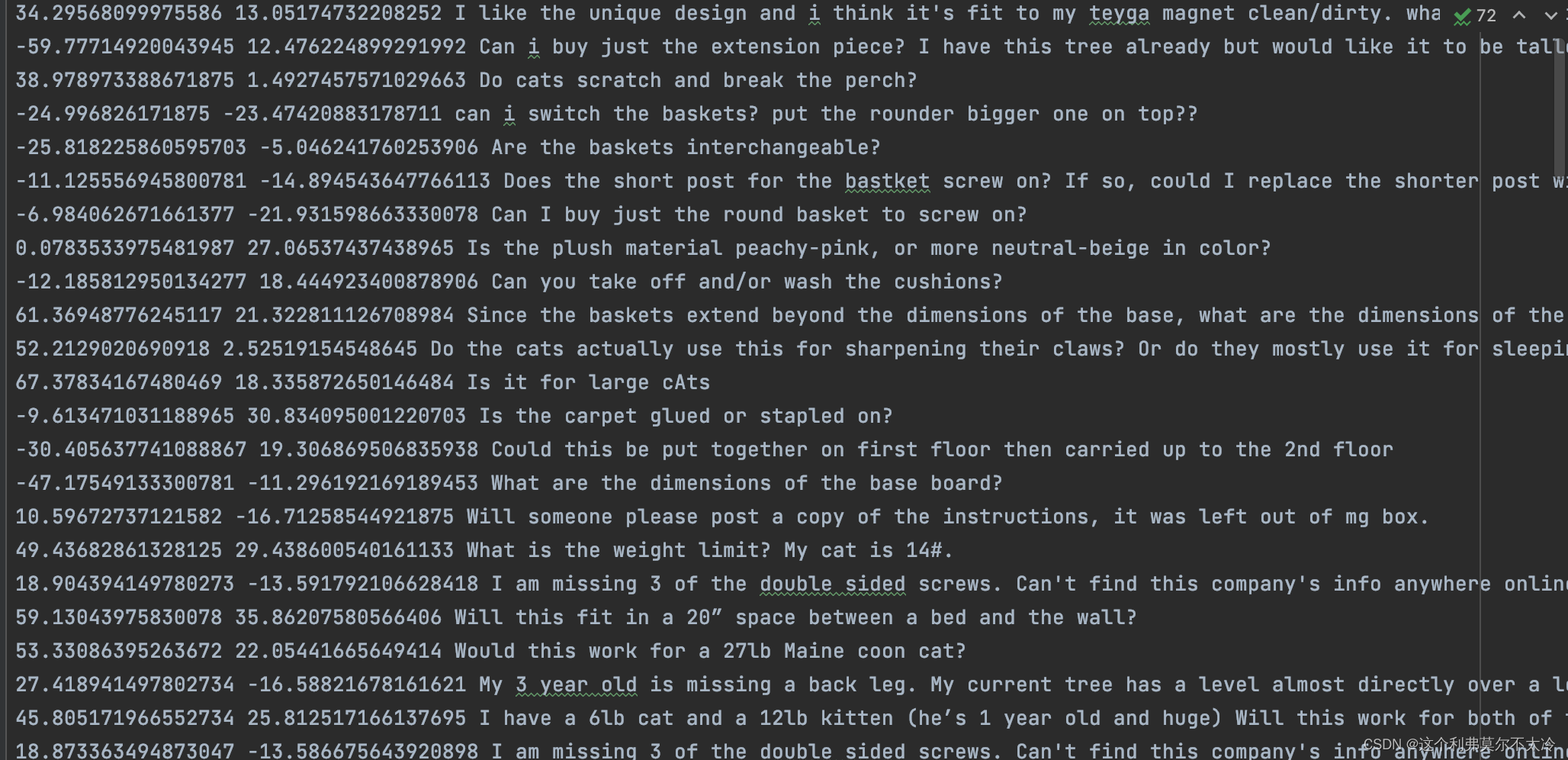
利用可视化结果,点击出现对应的句子

Integrated easy to pay secondary domain name distribution system

Recommend a GIF processing artifact less than 300K - gifsicle (free download)

我眼中真正优秀的CTO长啥样
This Chinese numpy quick look-up table is too easy!
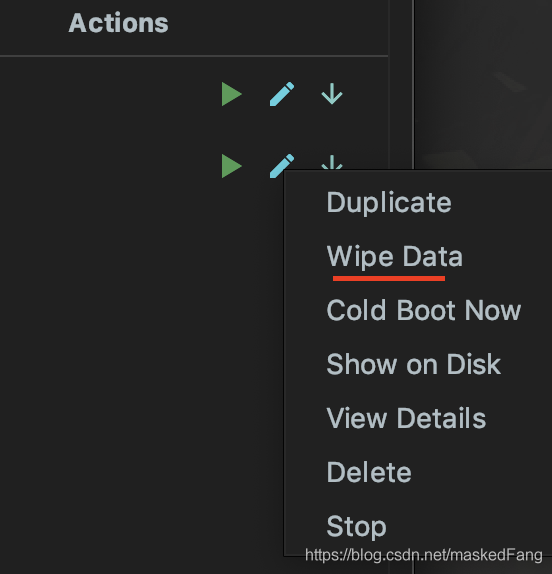
Record the errors reported when running fluent in the simulator

A green plug-in that allows you to stay focused, live and work hard
![[optics] vortex generation based on MATLAB [including Matlab source code 1927]](/img/9b/b7f462e2ecbff0cee35e7de5c80cf7.jpg)
[optics] vortex generation based on MATLAB [including Matlab source code 1927]
随机推荐
235. Ancêtre public le plus proche de l'arbre de recherche binaire [modèle LCA + même chemin de recherche]
What does a really excellent CTO look like in my eyes
235. 二叉搜索樹的最近公共祖先【lca模板 + 找路徑相同】
Record: solve the problem that MySQL is not an internal or external command environment variable
【学术相关】顶级论文创新点怎么找?中国高校首次获CVPR最佳学生论文奖有感...
硬盘监控和分析工具:Smartctl
“google is not defined” when using Google Maps V3 in Firefox remotely
Free sharing | linefriends hand account inner page | horizontal grid | not for sale
These problems should be paid attention to in the production of enterprise promotional videos
Php based campus lost and found platform (automatic matching push)
Pytorch introduction to deep learning practice notes 13- advanced chapter of cyclic neural network - Classification
Help change the socket position of PCB part
Record: MySQL changes the time zone
Summary of composition materials for 2020 high-frequency examination center of educational resources
Introduction to SSH Remote execution command
Recommend a GIF processing artifact less than 300K - gifsicle (free download)
php-fpm的max_chindren的一些误区
【光学】基于matlab涡旋光产生【含Matlab源码 1927期】
SQL injection for Web Security (1)
Zhengda futures news: soaring oil prices may continue to push up global inflation