当前位置:网站首页>Hash these knowledge you should also know
Hash these knowledge you should also know
2022-08-05 07:11:00 【code and thinking】
What is Hash
Hash is translated as hash in Chinese, and it is also called "hash". It is a general term for a class of functions.The input of any length (also known as pre-map, pre-image) is transformed into a fixed-length output through a hashing algorithm, and the output is the hash value.This transformation is a compressed map, that is, the space of the hash value is usually much smaller than the space of the input, and different inputs may hash to the same output, so it is impossible to determine the unique input value from the hash value.
Simply put, it is a function that compresses a message of any length into a message digest of a fixed length.
The role of Hash
hash is a function of compressing a message of any length into a message digest of a certain length.Equivalent to the fingerprint of a file.
Because the file is unlimited, the number of bits that can be represented by the mapped string is limited.Therefore, there may be different keys corresponding to the same Hash value.That's the possibility of a collision.
Hash storage data
The essence of the hash table is actually an array, and the key-value pair Entry is usually stored in the hash table.
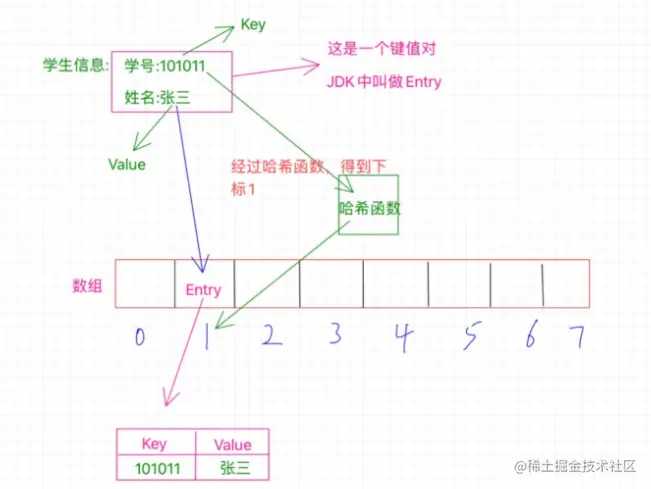
The student number here is a key, and the hash table uses the hash function to calculate a value based on the key value. This value is the subscript value, which is used to determine where in the hash table the entry should be stored.
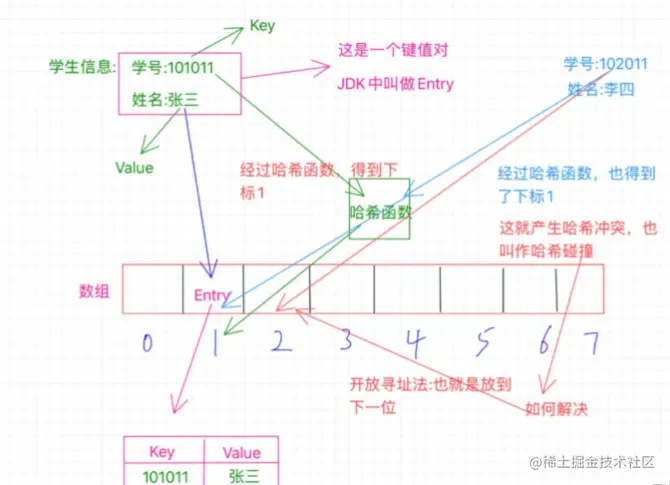
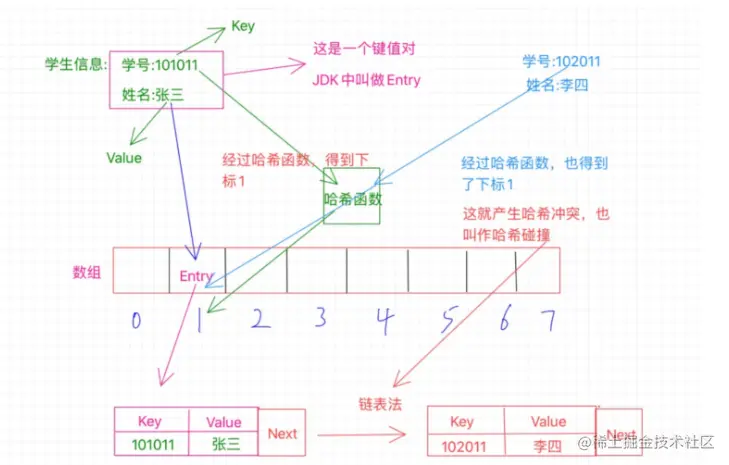
Hash collision solution
The solution to hash collision is open addressing method and zipper method.
Open addressing means that if the current array position 1 is occupied, it will be placed in the next position 2. If 2 is also occupied, it will continue to search until an empty position is found.
The zipper method uses a linked list. At this time, position 1 does not only store the Entry. At this time, the Entry also saves an additional next pointer, pointing to another position outside the array, and arranges Li Si in theHere, the next pointer in Zhang San's Entry points to Li Si's location, which is the stored memory address of this location.If there is still a conflict, put the conflicting Entry in a new position, and then Li Si's Entry points to it, thus forming a linked list.
Open addressing and zipping both try to find the next empty location to store the conflicting value.
Practical uses of Hash
Unique verification
- In java, it is used to judge whether the variables are equal and put into hashCode(), and together generate an integer that will not collide as much as possible
Data integrity verification:
- After downloading a file from the Internet, you can confirm whether the downloaded file is damaged by comparing the Hash value (such as MD5, SHA1) of the file.If the Hash value of the downloaded file is consistent with the Hash value given by the file provider, it proves that the downloaded file is intact
Quick Find:
- HashMap
Privacy Protection:
- When important data must be exposed, someone can choose to expose its Hash value (such as MD5) to ensure the security of the original data.For example, when logging in to a website, you can only save the hash value of the user's password. In each login verification, you only need to compare the hash value of the entered password with the hash value saved in the database. The website does not need to knowUser's password.In this way, when the website data is stolen, the user will not endanger the security of other websites because of the theft of their own password.
Author: Arrom
Link: https://juejin.cn/post/7127862424887099406
Source: Rare Earth Nuggets
边栏推荐
猜你喜欢
(2022杭电多校六)1012-Loop(单调栈+思维)

re正则表达式
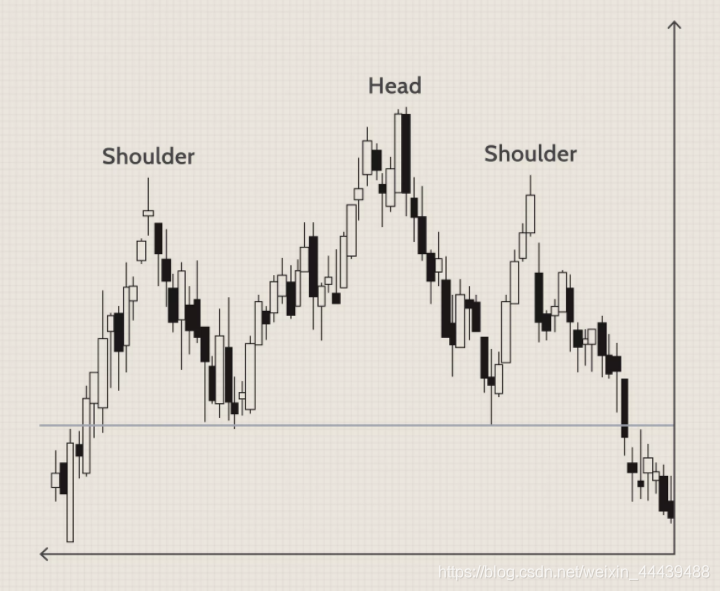
技术分析模式(十)头肩图案
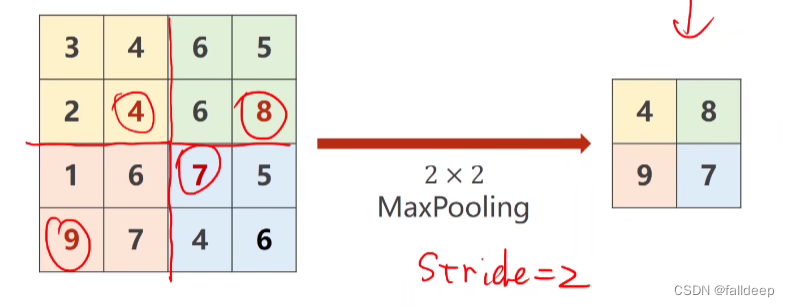
《PyTorch深度学习实践》第十课(卷积神经网络CNN)
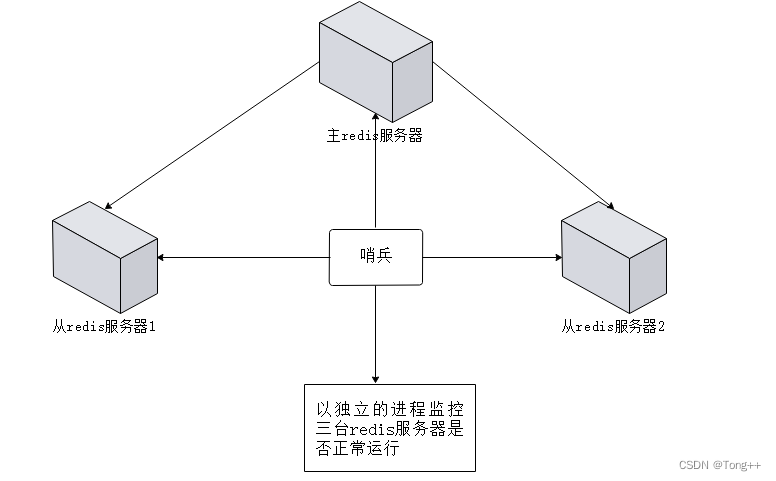
Advanced Redis
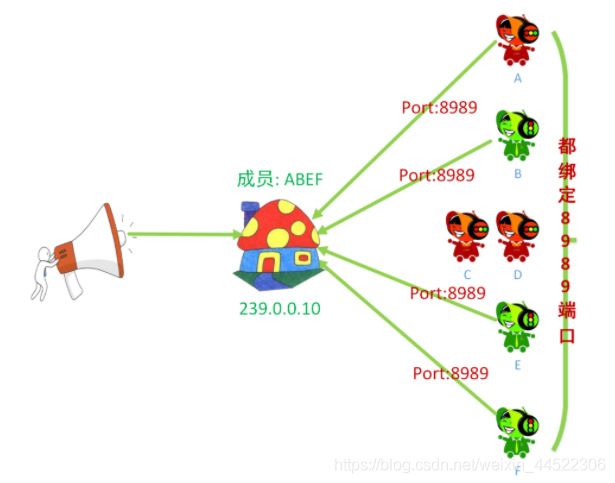
UDP组(多)播
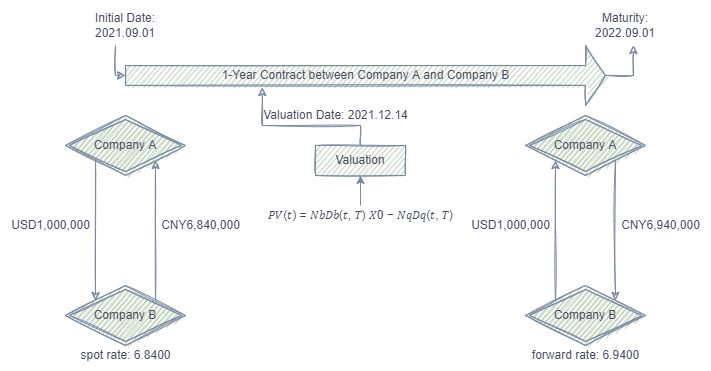
400 times performance improvement 丨 swap valuation optimization case calculation
HR:这样的简历我只看了5秒就扔了,软件测试简历模板想要的进。
RNote108---显示R程序的运行进度
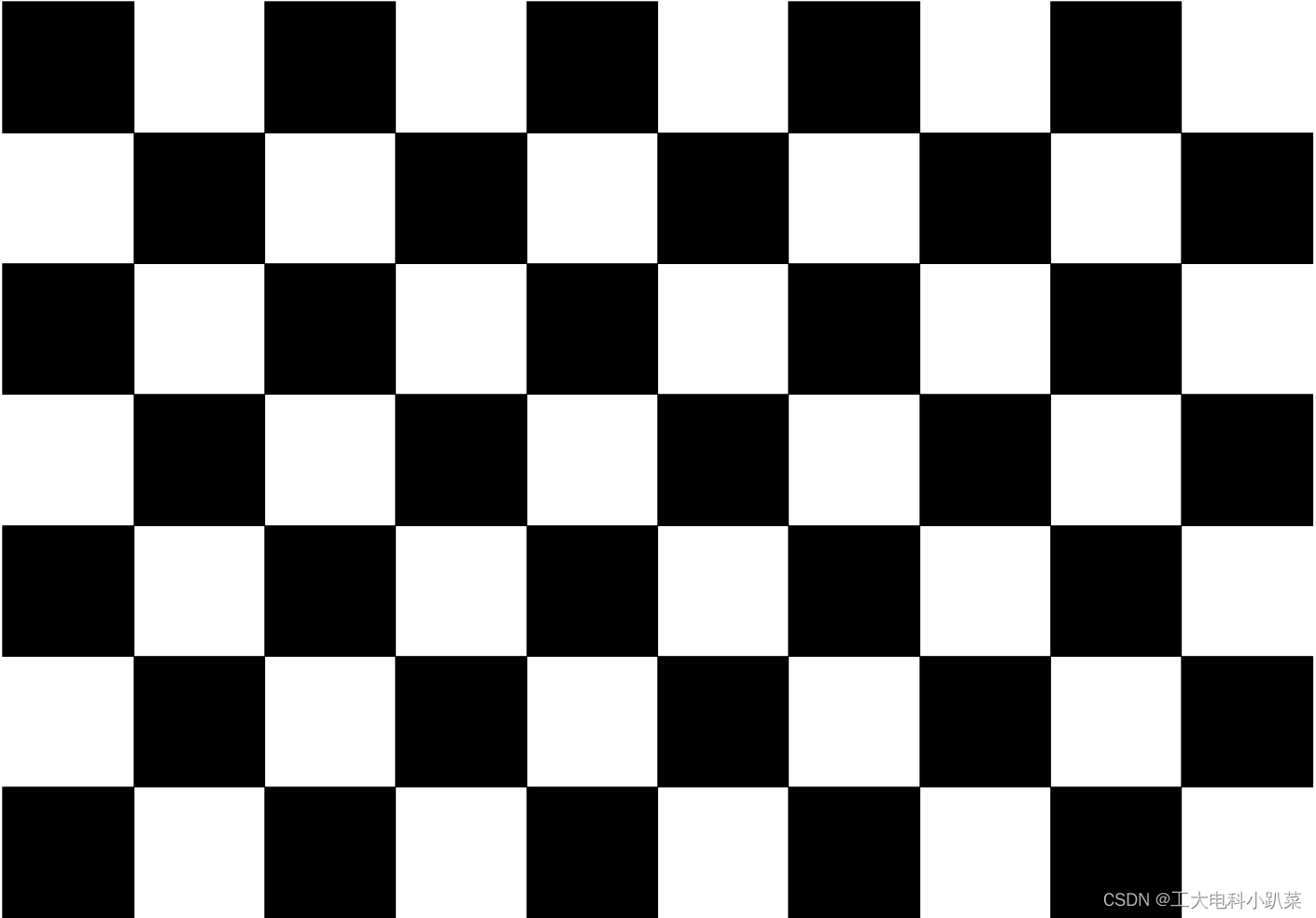
Day9 of Hegong Daqiong team vision team training - camera calibration
随机推荐
AH8669-AC380/VAC220V转降5V12V24V500MA内电源芯片IC方案
(2022杭电多校六)1012-Loop(单调栈+思维)
[instancetype type Objective-C]
Why does Mysql fail to create a database
mysql使用in函数的一个小问题
protobuf is compiled against the associated .proto file
PCI Pharma Services Announces Multi-Million Dollar Expansion of UK Manufacturing Facility to Meet Growing Demand for Global High Potency Drug Manufacturing Services to Support Oncology Treatment
typescript65-映射类型(keyof)
Rapid Medical's Ultra-Small and Only Adjustable Thromb Retriever Receives FDA Clearance
C# FileSystemWatcher
UDP broadcast
《PyTorch深度学习实践》第十课(卷积神经网络CNN)
(四)旋转物体检测数据roLabelImg转DOTA格式
自媒体人一般会从哪里找素材呢?
[Shanghai] Hiring .Net Senior Software Engineer & BI Data Warehouse Engineer (Urgent)
给网站套上Cloudflare(以腾讯云为例)
【网友真实投稿】为女友放弃国企舒适圈,转行软件测试12k*13薪
AI + video technology helps to ensure campus security, how to build a campus intelligent security platform?
Flink学习12:DataStreaming API
It turns out that Maya Arnold can also render high-quality works!Awesome Tips