当前位置:网站首页>Leetcode t34: find the first and last positions of elements in a sorted array
Leetcode t34: find the first and last positions of elements in a sorted array
2022-07-01 08:18:00 【Fan Qianzhi】
Title Description
Give you an array of integers in non decreasing order nums, And a target value target. Please find out the start position and end position of the given target value in the array .
If the target value does not exist in the array target, return [-1, -1].
You must design and implement a time complexity of O(log n) The algorithm to solve this problem .
Example 1:
Input :nums = [5,7,7,8,8,10], target = 8
Output :[3,4]
Example 2:
Input :nums = [5,7,7,8,8,10], target = 6
Output :[-1,-1]
Example 3:
Input :nums = [], target = 0
Output :[-1,-1]
Ideas
To meet the O ( log n ) O(\log n) O(logn) Complexity , To use binary search .
Can find (target-0.5) The location of , representative target The beginning of ;
By finding (target+0.5) The location of , find target At the end of .
however , Pay attention to the boundary situation . for example :
nums = [5,7,7,8,8,10], target = 8
If you want to find 7.5 The subscript i n d l ind_l indl, Then get the subscript 3; If you want to find 8.5 The subscript i n d r ind_r indr, Then get the subscript 5, So we need to add some operations :
If n u m s [ i n d l ] < t a r g e t nums[ind_l]<target nums[indl]<target, that i n d l + + ind_l++ indl++
If n u m s [ i n d l ] > t a r g e t nums[ind_l]>target nums[indl]>target, that i n d l − − ind_l-- indl−−
Code
int findInd(int[] nums, double target) {
int l = 0, r = nums.length-1;
while(l < r) {
int mid = (l+r) / 2;
int t = nums[mid];
if(t == target) {
return mid;
} else if (t < target){
l = mid+1;
} else {
r = mid-1;
}
}
return l;
}
public int[] searchRange(int[] nums, int target) {
if(nums.length == 0) {
int[] t = {
-1, -1};
return t;
}
int[] res = new int[2];
res[0] = findInd(nums, target-0.5);
res[1] = findInd(nums, target+0.5);
if(nums[res[0]] < target) res[0]+=1;
if(nums[res[1]] > target) res[1]--;
if(res[0] > res[1]) {
res[0] = -1;
res[1] = -1;
}
return res;
}
边栏推荐
- Connect timed out of database connection
- Using settoolkit to forge sites to steal user information
- [staff] key number (key number identification position | key number marking list | a major key identification principle | F, C, G position marking ascending | F major key identification principle | B
- Implementation and encapsulation of go universal dynamic retry mechanism
- 【入门】提取不重复的整数
- Find the nearest n-th power of 2
- getInputStream() has already been called for this request
- CPU design practice - Chapter 4 practical tasks - simple CPU reference design and debugging
- [untitled]
- Principle and process of embossing
猜你喜欢
![[batch dos-cmd command - summary and summary] - Common operators in the CMD window (<, < <, & <,>, > >, & >, & >, & &, ||, (),;, @)](/img/48/de19e8cc007b93a027a906d4d423b2.png)
[batch dos-cmd command - summary and summary] - Common operators in the CMD window (<, < <, & <,>, > >, & >, & >, & &, ||, (),;, @)

Aardio - Shadow Gradient Text

Set up file server Minio for quick use

Five combination boxing, solving six difficult problems on campus and escorting the construction of educational informatization
Lm08 mesh series mesh inversion (fine)
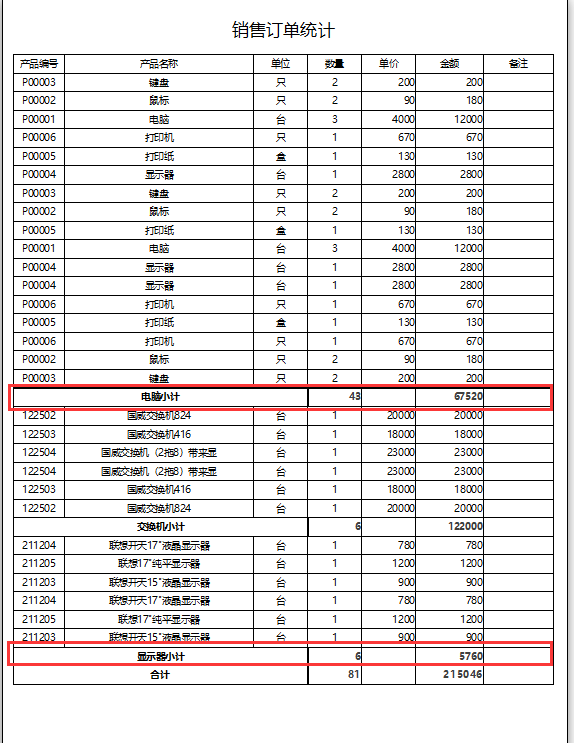
Access报表实现小计功能

Gdip - hatchbrush pattern table
![[getting started] intercepting strings](/img/16/363baa4982408f55493057200bcba5.png)
[getting started] intercepting strings

【Redis】一气呵成,带你了解Redis安装与连接

window c盘满了
随机推荐
程序员养生宝典
Php laraver Wechat payment
window c盘满了
[introduction] approximate value
Leetcode T34: 在排序数组中查找元素的第一个和最后一个位置
Transaction method call @transactional
01 numpy introduction
Luogu p3799 demon dream stick
Chinese font Gan: zi2zi
Adding color blocks to Seaborn clustermap matrix
getInputStream() has already been called for this request
Principle and process of embossing
[website architecture] solve 90% of distributed transactions in one move, and introduce the working principles and application scenarios of database transactions and distributed transactions
[staff] key number (key number identification position | key number marking list | a major key identification principle | F, C, G position marking ascending | F major key identification principle | B
【入门】截取字符串
How to troubleshoot SharePoint online map network drive failure?
[getting started] extract non repeating integers
Instead of houses, another kind of capital in China is rising
Burpsuite -- brute force cracking of intruder
0 basic introduction to single chip microcomputer: how to use digital multimeter and precautions