当前位置:网站首页>DC-1 target
DC-1 target
2020-11-06 21:13:00 【itread01】
版权声明
本文为[itread01]所创,转载请带上原文链接,感谢
边栏推荐
- Elasticsearch database | elasticsearch-7.5.0 application construction
- 2020-09-09:裸写算法:两个线程轮流打印数字1-100。
- An article will take you to understand CSS3 fillet knowledge
- 游戏开发中的新手引导与事件管理系统
- Markdown tricks
- Open source a set of minimalist front and rear end separation project scaffold
- image operating system windows cannot be used on this platform
- Why is the LS command stuck when there are too many files?
- Some operations kept in mind by the front end foundation GitHub warehouse management
- Digital city responds to relevant national policies and vigorously develops the construction of digital twin platform
猜你喜欢

Isn't data product just a report? absolutely wrong! There are university questions in this category

Unity performance optimization

How much disk space does a new empty file take?

How much disk space does a file of 1 byte actually occupy

Python basic data type -- tuple analysis

What kind of music do you need to make for a complete game?

Junit测试出现 empty test suite

Zero basis to build a web search engine of its own
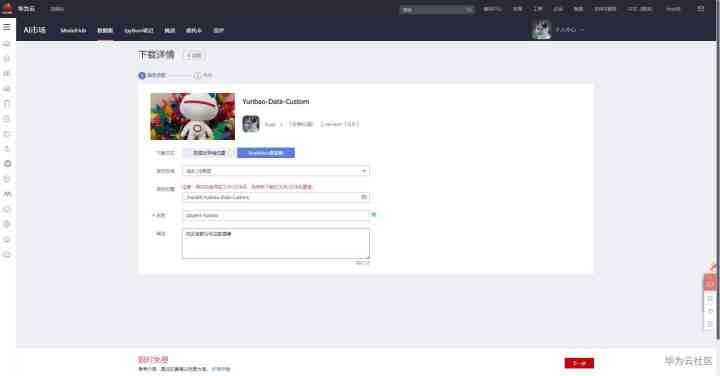
Use modelarts quickly, zero base white can also play AI!

Bitcoin once exceeded 14000 US dollars and is about to face the test of the US election
随机推荐
Zero basis to build a web search engine of its own
华为云微认证考试简介
2020-08-18:介绍下MR过程?
Summary of front-end interview questions (C, s, s) that front-end engineers need to understand (2)
Vue communication and cross component listening state Vue communication
面试官: ShardingSphere 学一下吧
Flink's datasource Trilogy 2: built in connector
Kubernetes and OAM to build a unified, standardized application management platform knowledge! (Internet disk link attached)
Swagger 3.0 brushes the screen every day. Does it really smell good?
StickEngine-架构11-消息队列(MessageQueue)
How to turn data into assets? Attracting data scientists
Python basic data type -- tuple analysis
Contract trading system development | construction of smart contract trading platform
【:: 是什么语法?】
hdu3974 Assign the task線段樹 dfs序
mongo 用户权限 登录指令
What are Devops
Share with Lianyun: is IPFs / filecoin worth investing in?
EOS founder BM: what's the difference between UE, UBI and URI?
统计项目代码行数