当前位置:网站首页>Infiltration learning diary day19
Infiltration learning diary day19
2022-07-04 01:10:00 【XiXioo1】
Here I added waf Knowledge
Combined with the safety dog learned before , I've seen a lot of simulated interview answers
1. Inline comments The first kind /*! The second kind /*! Add numbers , If it is greater than ( Still less than )mysql Version number of , The annotated statements here can also be used
2. Run keyword dictionary , Then run keyword combinations
3. Parameter pollution , False comment
Upload files :
1. The front-end verification can be passed directly burp Repackage , First upload his limited format , Then change the package to the suffix we want to write
2.content-type, through burp Repackage ,content-type This is based on the different content we upload type The type will change , But it can also be in burp Modify it into the format specified in
Blacklist detection : Write the suffix that is not allowed to upload in the array to match
Bypass :

upload-labs Methods that appear in
Add . .( Dot space dot )
Double write after the suffix ::$DATA
.htaceess File attack

.htaccess Two conditions for the successful operation of files as local variables
1.Allow Override All
2.LoadMoudule rewrite_module modules/mod_rewrite.so#rewrite The module is on
If you don't know which configuration file the above module is in , It can be used phpstorm open phpstudy File global search (ctrl+shift+F)
Implementation method
Create a new one .htaccess Name the file , Then add
<FilesMatch " A name ">
SetHandler application/x-httpd-php
</FilesMatch>
Then create a new one named above under this path .txt Text , Join in php The code can be parsed successfully
Add a link :
.htaccess Detailed explanation of file parsing vulnerability
边栏推荐
- MySQL - use of aggregate functions and group by groups
- swagger中响应参数为Boolean或是integer如何设置响应描述信息
- Function: find the approximate value of the limit of the ratio of the former term to the latter term of Fibonacci sequence. For example, when the error is 0.0001, the function value is 0.618056.
- On covariance of array and wildcard of generic type
- MySQL -- Introduction and use of single line functions
- OS interrupt mechanism and interrupt handler
- Swagger2 quick start and use
- Windos10 reinstallation system tutorial
- From functools import reduce -- see the use of reduce function from typical examples
- Unity Shader入门精要读书笔记 第三章 Unity Shader基础
猜你喜欢
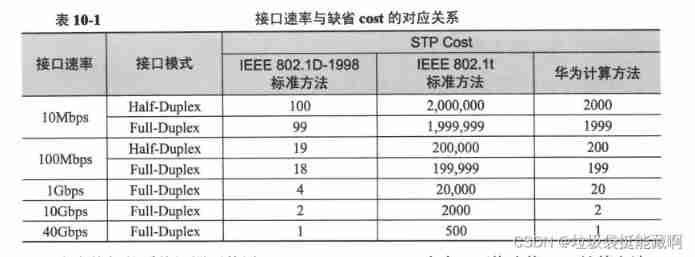
Some other configurations on Huawei's spanning tree
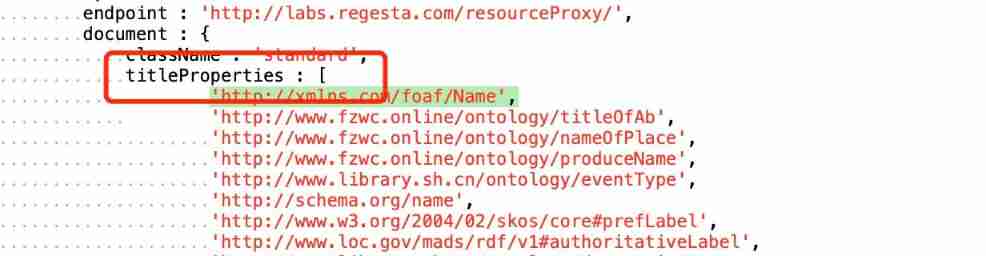
Release and visualization of related data

功能:将主函数中输入的字符串反序存放。例如:输入字符串“abcdefg”,则应输出“gfedcba”。

Sorry, Tencent I also refused

MySQL - use of aggregate functions and group by groups

1-redis architecture design to use scenarios - four deployment and operation modes (Part 1)

GUI application: socket network chat room
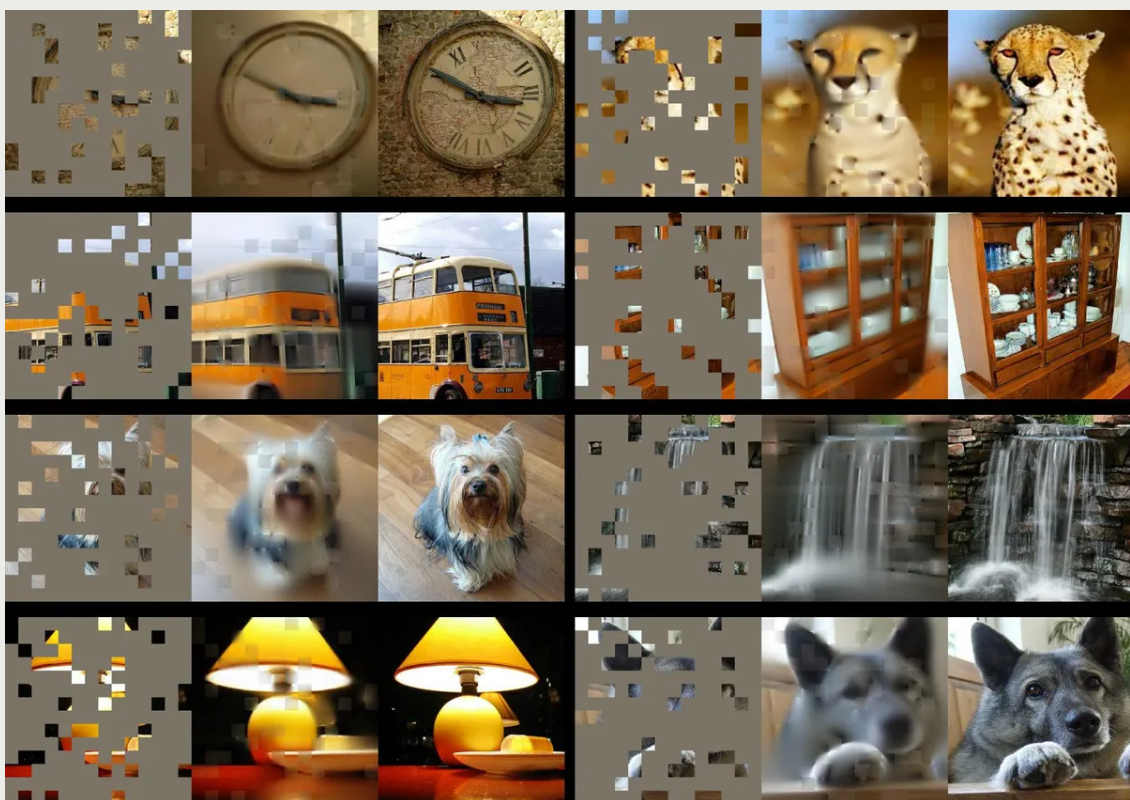
In the process of seeking human intelligent AI, meta bet on self supervised learning
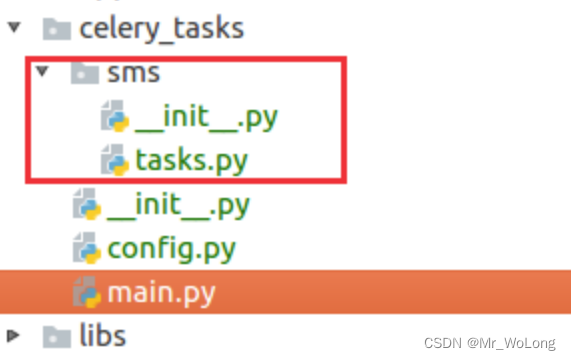
Mobile asynchronous sending SMS verification code solution -efficiency+redis

【.NET+MQTT】. Net6 environment to achieve mqtt communication, as well as bilateral message subscription and publishing code demonstration of server and client
随机推荐
不得不会的Oracle数据库知识点(二)
Thinkphp6 integrated JWT method and detailed explanation of generation, removal and destruction
Which insurance products can the elderly buy?
“疫”起坚守 保障数据中台服务“不打烊”
OS interrupt mechanism and interrupt handler
A malware detection method for checking PLC system using satisfiability modulus theoretical model
机器学习基础:用 Lasso 做特征选择
Oracle database knowledge points (IV)
Avoid playing with super high conversion rate in material minefields
0 basic learning C language - nixie tube dynamic scanning display
Att & CK actual combat series - red team actual combat - V
HackTheBox-baby breaking grad
HR disgusted interview behavior
CesiumJS 2022^ 源码解读[8] - 资源封装与多线程
Summary of JWT related knowledge
Mobile asynchronous sending SMS verification code solution -efficiency+redis
Severity code description the project file line prohibits the display of status error c4996 fopen ('fscanf ', StrCmp): this function or variable may be unsafe The most comprehensive solution
C library function int fprintf (file *stream, const char *format,...) Send formatted output to stream
How to use AHAS to ensure the stability of Web services?
Cesiumjs 2022^ source code interpretation [8] - resource encapsulation and multithreading