当前位置:网站首页>Sword finger offer 15 Number of 1 in binary
Sword finger offer 15 Number of 1 in binary
2022-07-03 12:59:00 【Hiccup~~~~】
The finger of the sword Offer 15. Binary 1 The number of
The difficulty is simple 251
Write a function , Input is an unsigned integer ( In the form of a binary string ), Returns the number of digits in its binary expression as ‘1’ The number of ( Also known as Hamming weight ).).
Tips :
- Please note that , In some languages ( Such as Java) in , There is no unsigned integer type . under these circumstances , Both input and output will be specified as signed integer types , And should not affect your implementation , Because whether integers are signed or unsigned , Its internal binary representation is the same .
- stay Java in , The compiler uses Binary complement Notation to represent signed integers . therefore , Above Example 3 in , The input represents a signed integer -3.
Example 1:
Input :n = 11 ( Console input 00000000000000000000000000001011) Output :3 explain : Binary string of input
00000000000000000000000000001011 in , There are three of them '1'.
Example 2:
Input :n = 128 ( Console input 00000000000000000000000010000000) Output :1 explain : Binary string of input 00000000000000000000000010000000 in , There is one in all for '1'.
Example 3:
Input :n = 4294967293 ( Console input 11111111111111111111111111111101, In some languages n = -3) Output :31 explain : Binary string of input 11111111111111111111111111111101 in , share 31 Position as '1'.
Tips :
- The input must be of length 32 Of Binary string .
Code
class Solution {
public:
int hammingWeight(uint32_t n) {
int flag=0;
while(n){
if(n&1==1)
flag++;
n=n>>1;
}
return flag;
}
};
边栏推荐
- Application of ncnn neural network computing framework in orange school orangepi 3 lts development board
- Deeply understand the mvcc mechanism of MySQL
- 剑指 Offer 14- II. 剪绳子 II
- C graphical tutorial (Fourth Edition)_ Chapter 13 entrustment: what is entrustment? P238
- Powerful avatar making artifact wechat applet
- C graphical tutorial (Fourth Edition)_ Chapter 18 enumerator and iterator: enumerator samplep340
- 2022-01-27 redis cluster brain crack problem analysis
- 低代码平台国际化多语言(i18n)技术方案
- Tensorflow binary installation & Failure
- 2022-01-27 use liquibase to manage MySQL execution version
猜你喜欢
![[ArcGIS user defined script tool] vector file generates expanded rectangular face elements](/img/39/0b31290798077cb8c355fbd058e4d3.png)
[ArcGIS user defined script tool] vector file generates expanded rectangular face elements

Application of ncnn neural network computing framework in orange school orangepi 3 lts development board
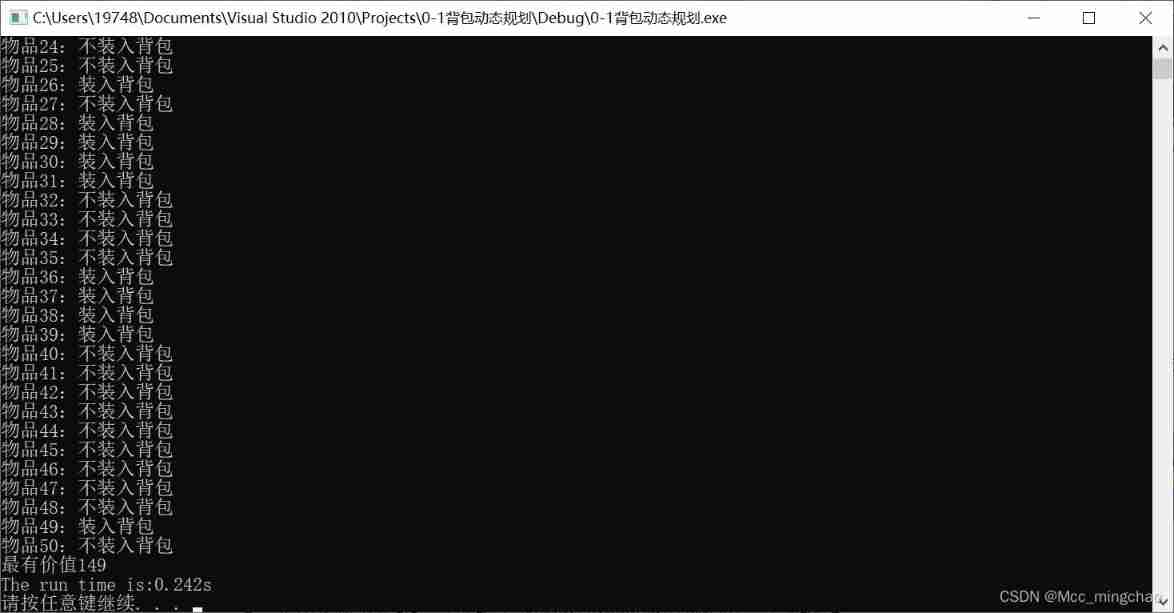
01 three solutions to knapsack problem (greedy dynamic programming branch gauge)

【数据挖掘复习题】

Harmonic current detection based on synchronous coordinate transformation

Sword finger offer14 the easiest way to cut rope
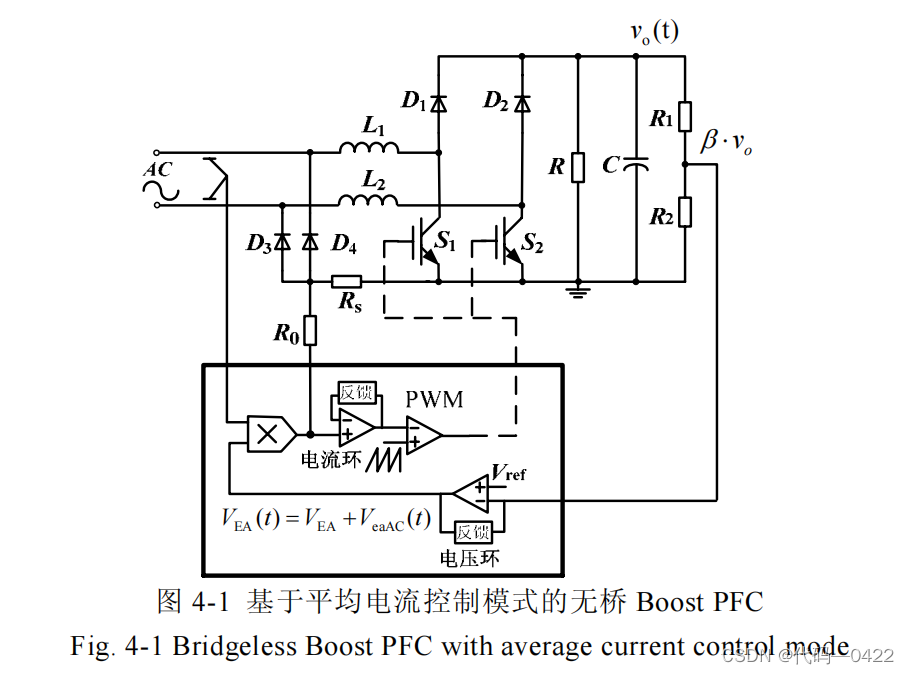
电压环对 PFC 系统性能影响分析

Huffman coding experiment report
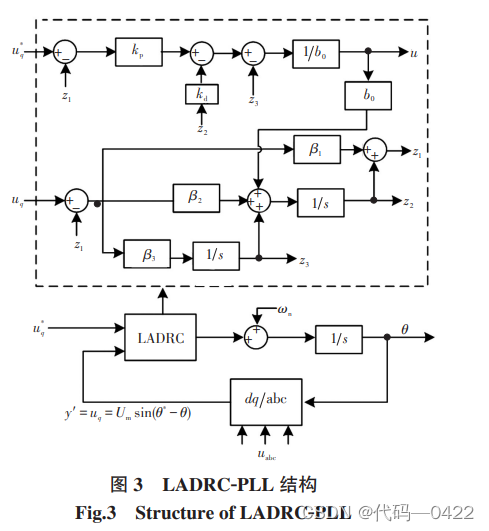
自抗扰控制器七-二阶 LADRC-PLL 结构设计
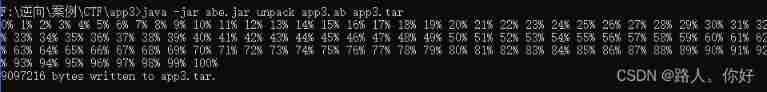
Xctf mobile--app3 problem solving
随机推荐
2022-02-09 survey of incluxdb cluster
如何在微信小程序中获取用户位置?
[combinatorics] permutation and combination (multiple set permutation | multiple set full permutation | multiple set incomplete permutation all elements have a repetition greater than the permutation
2022-01-27 redis cluster cluster proxy predixy analysis
Glide question you cannot start a load for a destroyed activity
sitesCMS v3.1.0发布,上线微信小程序
强大的头像制作神器微信小程序
Xctf mobile--app2 problem solving
[Exercice 5] [principe de la base de données]
An example of newtonjason
最新版抽奖盲盒运营版
Powerful avatar making artifact wechat applet
自抗扰控制器七-二阶 LADRC-PLL 结构设计
IDEA 全文搜索快捷键Ctr+Shift+F失效问题
Quick learning 1.8 front and rear interfaces
社交社区论坛APP超高颜值UI界面
[exercise 6] [Database Principle]
OpenHarmony应用开发之ETS开发方式中的Image组件
Detailed explanation of the most complete constraintlayout in history
【習題七】【數據庫原理】