当前位置:网站首页>Database auditing - an essential part of network security
Database auditing - an essential part of network security
2022-08-03 01:34:00 【Operations have XiaoDeng @】
Performing database log analysis allows you to audit all access to confidential or sensitive corporate data stored in the database.Auditing database logs can also enhance your internal security framework by answering questions about who changed critical data, when, and more.Database auditing can also help you meet increasingly demanding compliance requirements.
Log Analysis
1. EventLog Analyzer - comprehensive database auditing software
EventLog Analyzer implementation:
- Comprehensive management: EventLog Analyzer centrally collects database events from the entire network, provides rich reports for database auditing, account management and other user changes, server security reports, etc., alerts you to important events in real time and securely archives logs.
- Database activity monitoring: Monitor all user activities in the database, database transactions (including DDL and DML statements), etc.
- Database Server Log Monitoring: This tool provides information on server activity, user logins and logouts, account and permission changes in the database server through in-depth database server log analysis..
- Database Security Monitoring: Monitor the database for any common attack patterns to strengthen database security.Get instant alerts on any targeted attacks, such as SQL injection, and detailed reports on such attacks to aid incident investigation.
- In-depth Analysis: This tool facilitates deeper analysis by providing database server log analysis reports such as top and trend reports.This helps you better understand database server activity and get more value from the logs.
 EventLog Analyzer
EventLog Analyzer
Second, MS SQL server predefined reports
EventLog Analyzer's predefined Microsoft SQL Server reports and alerts cover:
- DDL Activities: Structure-level database changes, such as database creation.
- DML Activities: Functional level activities such as data access and modification.
- Account changes: new user creation, password changes, etc.
- Server activity: server startup, shutdown, creation of server-level objects (such as server audit and server audit specification objects), and server trends.Learn more
- Security Attacks: Common types of attacks such as SQL injection and denial of service attacks.

MS SQL Server
Three, Oracle database predefined reports
EventLog Analyzer's predefined Oracle database reports and alerts cover:
- Database Activities: All database user activities, such as creating tables and databases, executing procedures, etc.Learn more
- Account Management: Create and change profiles, roles, etc.
- Server activity: successful and failed server logins, startups and shutdowns, etc.
- Security Reports: Reports of common attacks such as SQL injection and denial of service.
边栏推荐
- 无代码开发平台表单样式设置步骤入门课程
- 数字化转型巨浪拍岸,成长型企业如何“渡河”?
- 记一次mysql查询慢的优化历程
- Yocto系列讲解[实战篇]85 - 制作ubi镜像和自动挂载ubifs文件系统
- 我为什么又能面试一次就拿到offer
- threejs dynamically adjust the camera position so that the camera can see the object exactly
- 思源笔记 本地存储无使用第三方同步盘,突然打不开文件。
- Week 7 - Distributional Representations(分布表示)
- 学习基因富集工具DAVID(2)
- Apache Doris 1.1 特性揭秘:Flink 实时写入如何兼顾高吞吐和低延时
猜你喜欢

用了 TCP 协议,数据一定不会丢吗?
![[论文总结] 深度学习在农业领域应用论文笔记10](/img/e8/0ba741980495cd81ca30bf269d1111.jpg)
[论文总结] 深度学习在农业领域应用论文笔记10
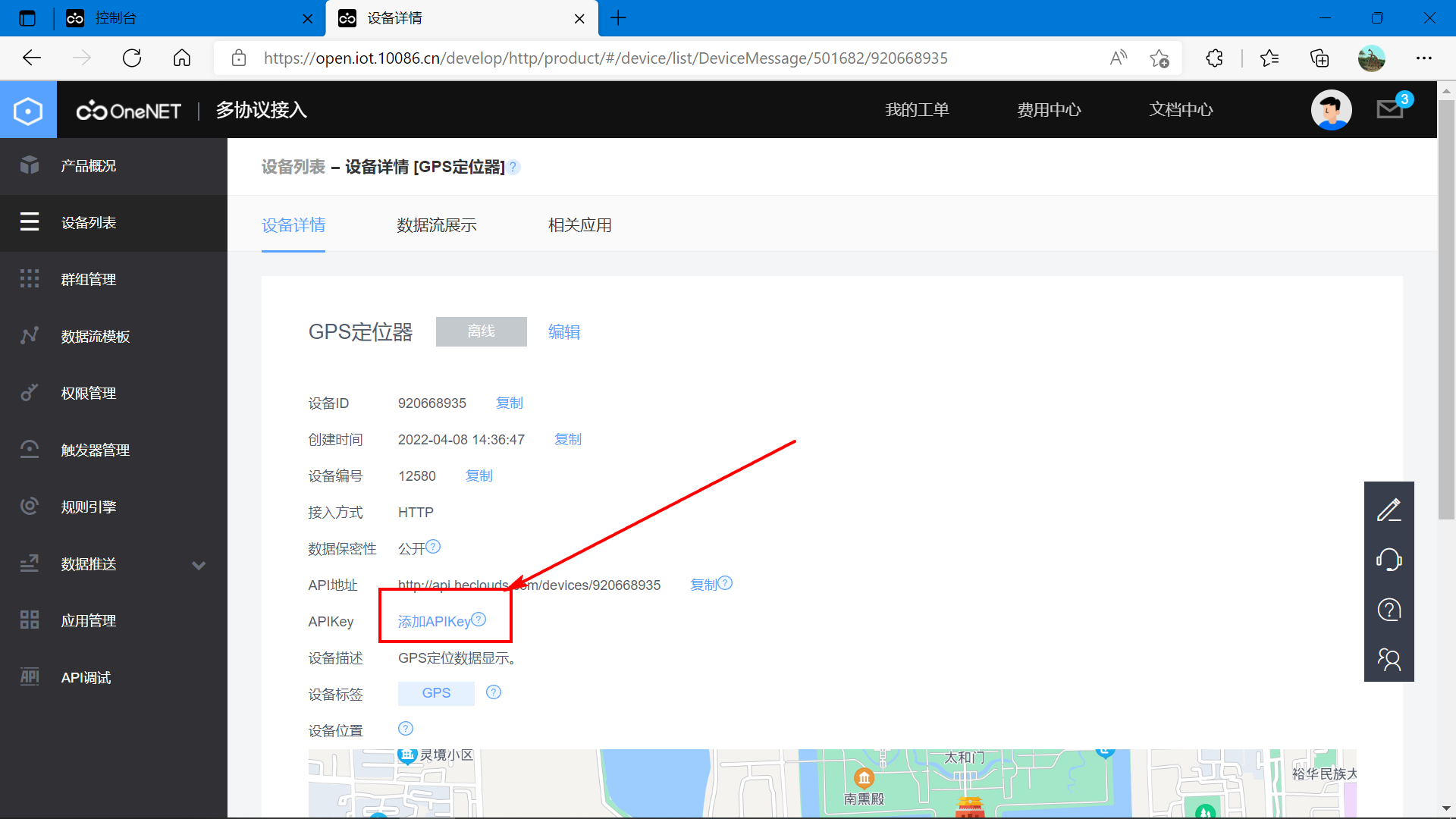
基于STM32设计的老人防摔倒报警设备(OneNet)
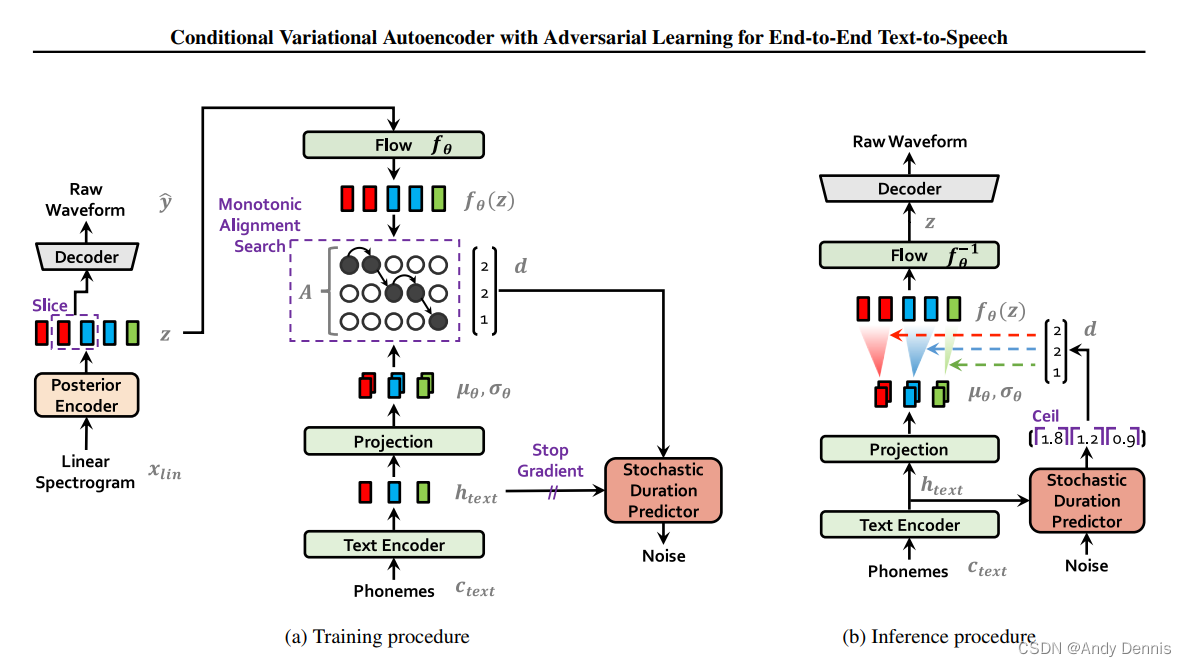
语音合成模型小抄(1)
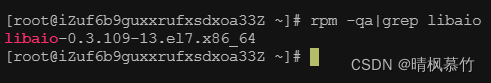
centos7安装mysql8

数据库审计 - 网络安全的重要组成部分
I have been in the software testing industry for nearly 20 years, let me talk to you about today's software testing
VMware workstation program starts slowly
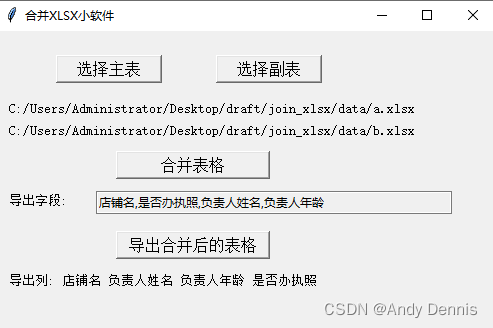
Merge two excel spreadsheet tools

【C语言】带头双向循环链表(list)详解(定义、增、删、查、改)
随机推荐
HCIP(17)
Find My技术|智能防丢还得看苹果Find My技术
C语言函数详解(2)【函数参数——实际参数(实参)&形式参数(形参)】
NLP常用Backbone模型小抄(1)
漫画:怎么证明sleep不释放锁,而wait释放锁?
CIO修炼手册:成功晋升CIO的七个秘诀
基于STM32的FLASH读写实验含代码(HAL库)
TCP三次握手与四次挥手
用大白话解释“什么是ERP?” 看完这篇就全明白了
HCIP(16)
技术分享 | 接口自动化测试中如何对xml 格式做断言验证?
CAS:1445723-73-8,DSPE-PEG-NHS,磷脂-聚乙二醇-活性酯两亲性脂质PEG共轭物
【代码扫描修复】MD5加密弱HASH漏洞
无代码开发平台数据ID入门教程
CKAN教程之在 AWS 上部署 CKAN 应用程序
基于奇异谱分析法和长短时记忆网络组合模型的滑坡位移预测
Image recognition from zero to write DNF script key points
threejs 动态调整相机位置,使相机正好能看到对象
Nlog自定义时间
Day117.尚医通:生成挂号订单模块
 EventLog Analyzer
EventLog Analyzer