当前位置:网站首页>Leetcode t40: combined sum II
Leetcode t40: combined sum II
2022-07-01 08:18:00 【Fan Qianzhi】
Title Description
Given a set of candidate numbers candidates And a target number target , find candidates All can make numbers and target The combination of .
candidates Each number in can only be used in each combination once .
Be careful : A solution set cannot contain duplicate combinations .
Example 1:
Input : candidates = [10,1,2,7,6,1,5], target = 8,
Output :
[
[1,1,6],
[1,2,5],
[1,7],
[2,6]
]
Example 2:
Input : candidates = [2,5,2,1,2], target = 5,
Output :
[
[1,2,2],
[5]
]
Tips
1 <= candidates.length <= 100
1 <= candidates[i] <= 50
1 <= target <= 30
Ideas
And the last question : Combinatorial summation I equally , Is to use dfs, however , If you still use the idea of the previous question , Despite the pruning , Still timeout . Here is another dfs Ideas .
Because each candidate[i] It's all in the range of [0, 50], So you can define an array to record the number of each element , Then proceed according to this array dfs Search for .
Code
List<List<Integer>> res = new ArrayList<List<Integer>>();
HashMap<List<Integer>, Integer> map = new HashMap<List<Integer>, Integer>();
int tar;
int[] nums = new int[51];
// Currently selected combination , Select the number , The present and , The rest and
void dfs(List<Integer> lis, int cur, int s, int ts) {
if(cur == 51) {
if(s == tar && map.getOrDefault(lis, -1)==-1) {
map.put(lis, 1);
}
} else {
// for(int x: lis) System.out.print(x+","); System.out.println("\t"+cur+","+s);
if(nums[cur] == 0) dfs(lis, cur+1, s, ts);
else {
// For the current number
// choose , See if it exceeds , prune
List<Integer> tmp = new ArrayList<Integer>(lis);
for(int i = 1; i <= nums[cur]; i++) {
if(s + i*cur <= tar) {
tmp.add(cur);
dfs(tmp, cur+1, s + i*cur, ts-i*cur);
}
}
// No election , If the rest is still not enough , Then prune
if(s+ts-cur >= tar) {
List<Integer> tmp2 = new ArrayList<Integer>(lis);
dfs(tmp2, cur+1, s, ts-cur);
}
}
}
}
public List<List<Integer>> combinationSum2(int[] candidates, int target) {
tar = target;
for(int x: candidates) nums[x]++;
int s = 0;
for(int x: candidates) s += x;
dfs(new ArrayList<Integer>(), 0, 0, s);
for(List<Integer> lis: map.keySet()) {
res.add(lis);
}
return res;
}
边栏推荐
- php laravel微信支付
- 01 numpy introduction
- Teach you how to apply for domestic trademark online step by step
- [redis] it takes you through redis installation and connection at one go
- 使用 setoolkit 伪造站点窃取用户信息
- Learn the knowledge you need to know about the communication protocol I2C bus
- [untitled]
- Use threejs simple Web3D effect
- How can beginners correctly understand Google's official suggested architectural principles (questions?)
- Set up file server Minio for quick use
猜你喜欢
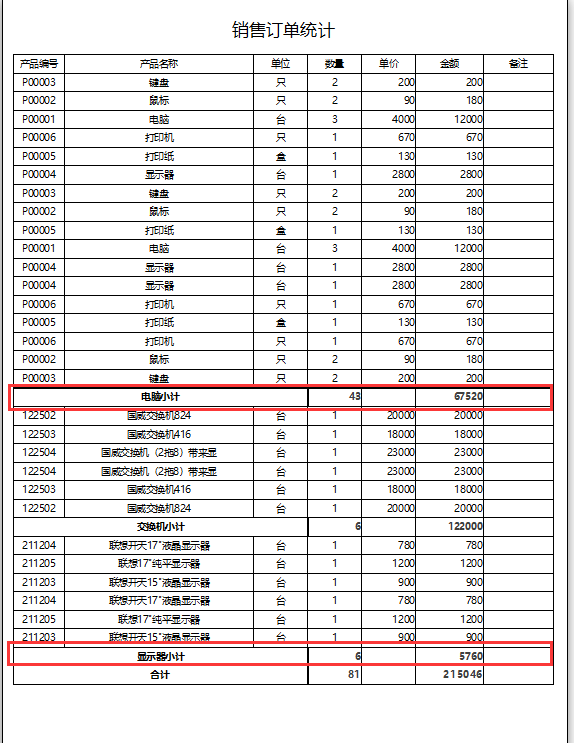
Access report realizes subtotal function

谈谈数字化转型的几个关键问题

Using settoolkit to forge sites to steal user information

Learn the knowledge you need to know about the communication protocol I2C bus
![[staff] high and low octave mark (the notes in the high octave mark | mark range are increased by one octave as a whole | low octave mark | mark range are decreased by one octave as a whole)](/img/ff/ebd936eaa6e57b1eabb691b0642957.jpg)
[staff] high and low octave mark (the notes in the high octave mark | mark range are increased by one octave as a whole | low octave mark | mark range are decreased by one octave as a whole)
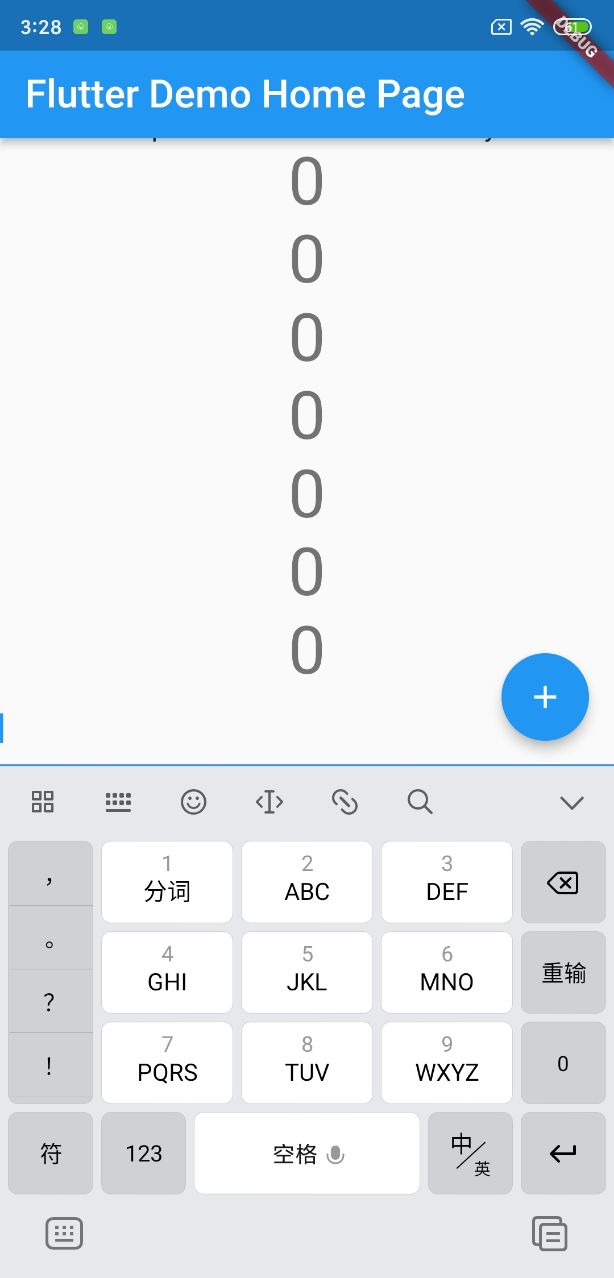
Soft keyboard height error

CPU設計實戰-第四章實踐任務一簡單CPU參考設計調試

The Windows C disk is full

Teach you how to apply for domestic trademark online step by step

SQL number injection and character injection
随机推荐
The Windows C disk is full
Insufficient executors to build thread pool
【刷题】字符统计【0】
5大组合拳,解决校园6大难题,护航教育信息化建设
Latex table
Source code analysis of open source API gateway APIs IX
To prevent "activation" photos from being muddled through, databao "live detection + face recognition" makes face brushing safer
Stack implementation calculator
Latex formula code
CPU设计实战-第四章实践任务一简单CPU参考设计调试
getInputStream() has already been called for this request
[staff] key number (key number identification position | key number marking list | a major key identification principle | F, C, G position marking ascending | F major key identification principle | B
Day5: scanner object, next() and nextline(), sequential structure, selection structure, circular structure
Luogu p1088 [noip2004 popularization group] Martians
Provincial election + noi Part III tree problems
Tupu software has passed CMMI5 certification| High authority and high-level certification in the international software field
Serial port oscilloscope software ns-scope
Aardio - Shadow Gradient Text
Book of quantitative trading - reading notes of the man who conquers the market
How to prevent the other party from saying that he has no money after winning the lawsuit?