当前位置:网站首页>Uva536 binary tree reconstruction tree recovery
Uva536 binary tree reconstruction tree recovery
2022-07-04 12:25:00 【Harmful Poems】
Enter the sequence of preorder traversal and middle order traversal of a binary tree , Output its post order traversal sequence .
#include<bits/stdc++.h>
using namespace std;
string preorder,inorder;
void postorder(string pre,string in){
if(pre.size() <= 0){
return ;
}
int len = 0;
len = in.find(pre[0]);
postorder(pre.substr(1,len),in.substr(0,len));
postorder(pre.substr(len+1).in.substr(len+1));
cout<<pre[0];
}
int mian(){
while(cin>>preorder>>inorder){
postorder(preorder,inorder);
cout<<endl;
}
return 0;
}
#include<bits/stdc++.h>
using namespace std;
string preorder,inorder;
void postorder(int l1,int l2,int n){
if(n <= 0){
return ;
}
int len = 0;
int len = inorder.find(preorder[l1]) - l2;
postorder(l1+1,l2,len);
postorder(l1+len+1,l2+len+1,n-len-1);
cout<<preorder[l1];
}
int mian(){
while(cin>>preorder>>inorder){
int len = preorder.size();
postorder(0,0,len);// Preamble start subscript , Middle order start subscript , length
cout<<endl;
}
return 0;
}
边栏推荐
- A few words explain redis cache penetration, breakdown, avalanche, and redis sentinel
- MySQL advanced review
- Xshell's ssh server rejected the password, failed to skip publickey authentication, and did not register with the server
- Simple understanding of seesion, cookies, tokens
- [Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 18
- Summary of Shanghai Jiaotong University postgraduate entrance examination module firewall technology
- Introduction of network security research direction of Shanghai Jiaotong University
- Btrace tells you how to debug online without restarting the JVM
- [Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 23
- How do std:: function and function pointer assign values to each other
猜你喜欢
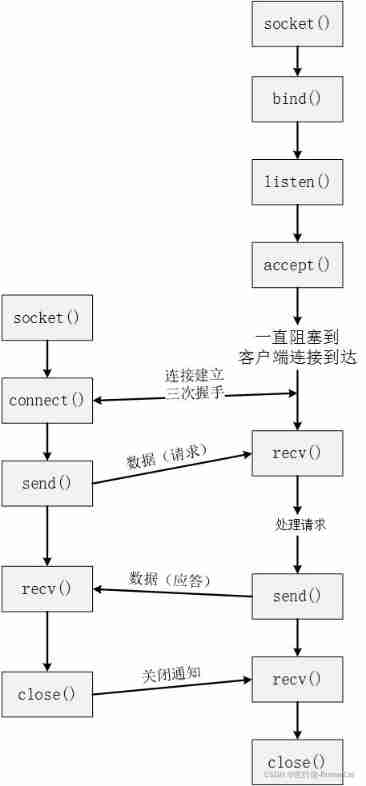
TCP slicing and PSH understanding
CSDN documentation specification

Exness: positive I win, negative you lose
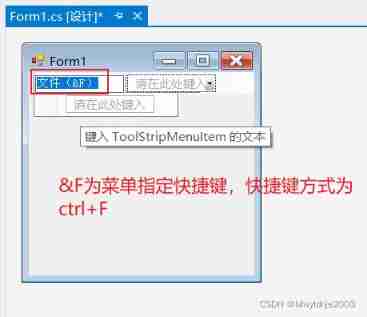
13、 C window form technology and basic controls (3)
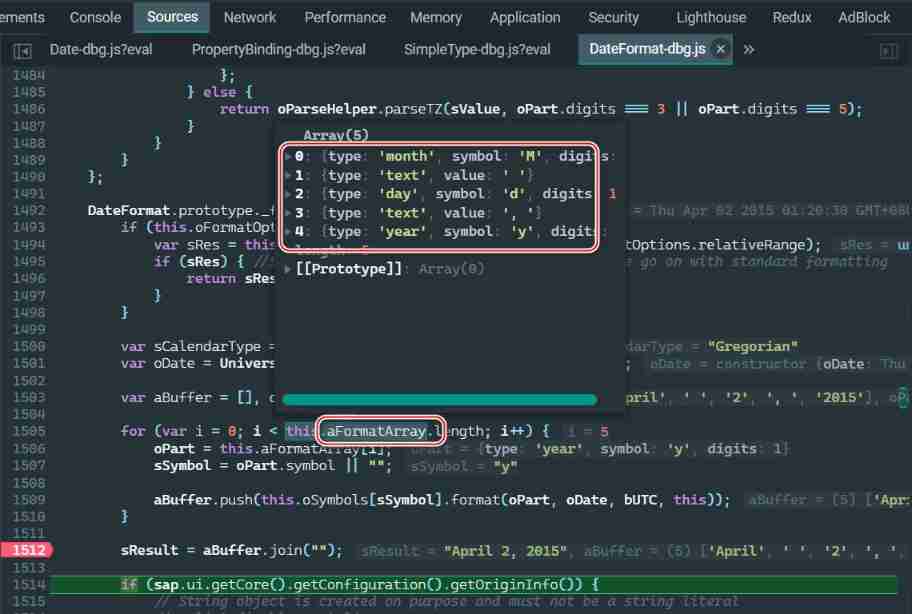
SAP ui5 date type sap ui. model. type. Analysis of the display format of date

Hongke case study on storm impact in coastal areas of North Carolina using lidar
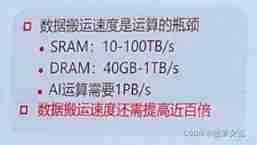
Memory computing integration: AI chip architecture in the post Moorish Era
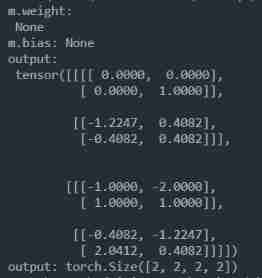
nn. Exploration and experiment of batchnorm2d principle
Some summaries of the 21st postgraduate entrance examination 823 of network security major of Shanghai Jiaotong University and ideas on how to prepare for the 22nd postgraduate entrance examination pr
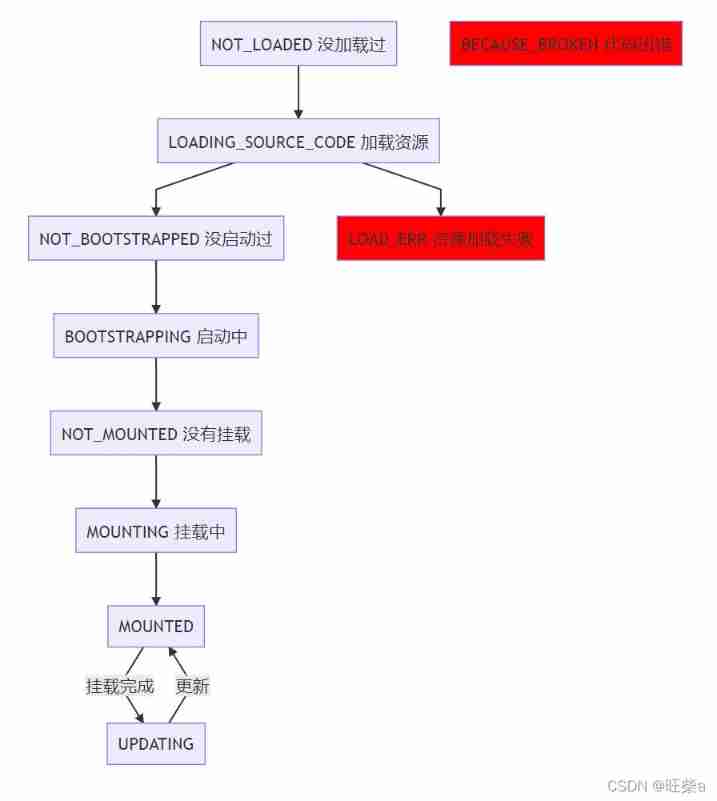
Single spa, Qiankun, Friday access practice
随机推荐
Interview question MySQL transaction (TCL) isolation (four characteristics)
QQ get group member operation time
Video analysis
Map container
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 17
[Yunju entrepreneurial foundation notes] Chapter II entrepreneur test 10
QQ get group settings
Azure solution: how can third-party tools call azure blob storage to store data?
Realize cross tenant Vnet connection through azure virtual Wan
DVC use case (VI): Data Registry
Ternsort model integration summary
Alibaba cloud server connection intranet operation
os. Path built-in module
Tableau makes data summary after linking the database, and summary exceptions occasionally occur.
(2021-08-20) web crawler learning 2
Entitas learning [3] multi context system
How to create a new virtual machine
Hongke case study on storm impact in coastal areas of North Carolina using lidar
QQ get group link, QR code
Memory computing integration: AI chip architecture in the post Moorish Era