边栏推荐
- 7. List of private messages
- How to build a private yum source
- Clustering index, and what is the difference between a clustering index
- Crypto Firms Offer Offer To Theft Hackers: Keep A Little, Give The Rest
- 编译Hudi
- 软件积累 -- 截图软件ScreenToGif
- 【异常】The field file exceeds its maximum permitted size of 1048576 bytes.
- 公司官网建站笔记(六):域名进行公安备案并将备案号显示在网页底部
- 接口测试关键技术
- 【C语言】三子棋(经典解法+一览图)
猜你喜欢
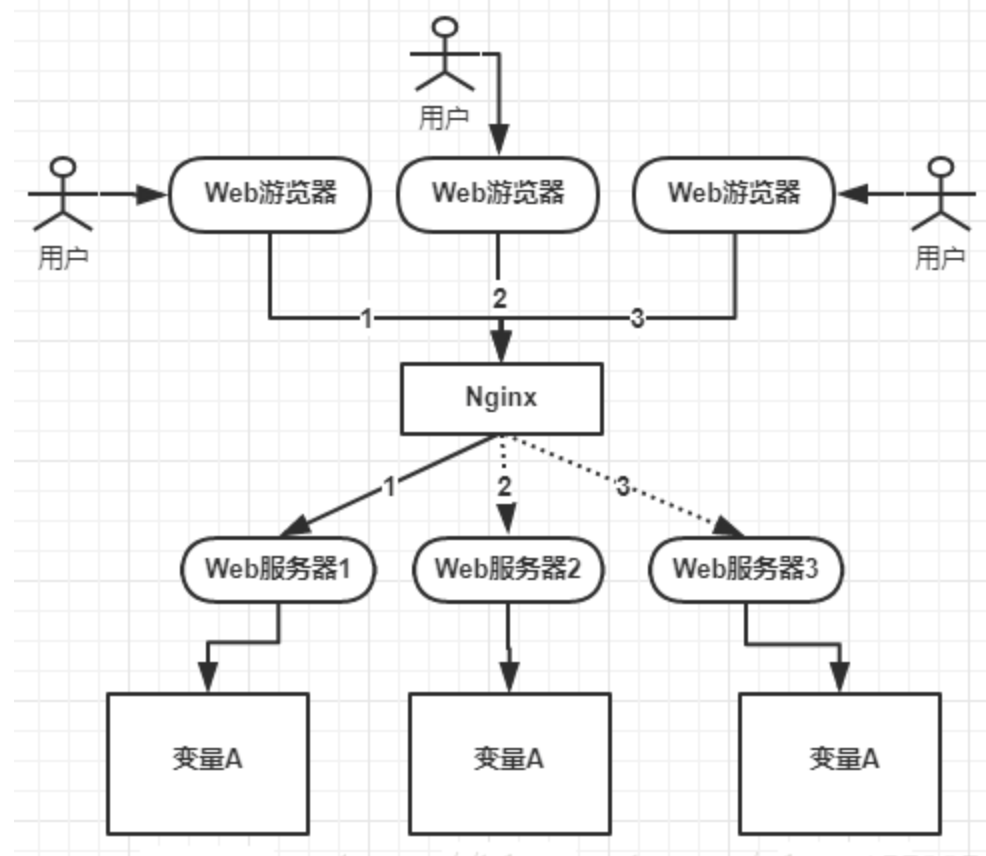
What is a distributed lock?Three ways of implementing distributed lock

CentOS7下mysql5.7.37的安装【完美方案】

JS 函数 this上下文 运行时点语法 圆括号 数组 IIFE 定时器 延时器 self.备份上下文 call apply
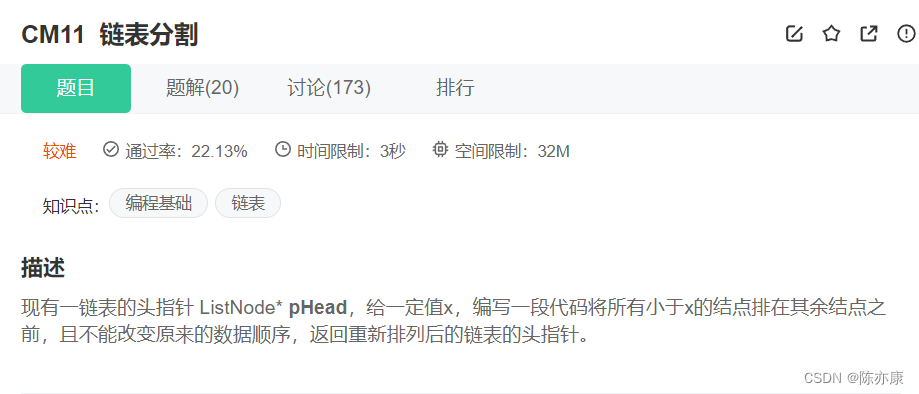
Classic linked list OJ strong training problem - fast and slow double pointer efficient solution

11. Redis implements follow, unfollow, and follow and follower lists

软件积累 -- 截图软件ScreenToGif
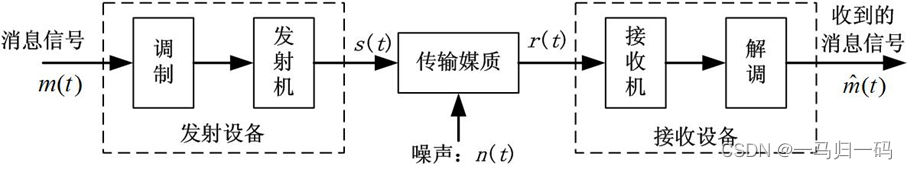
什么是系统?
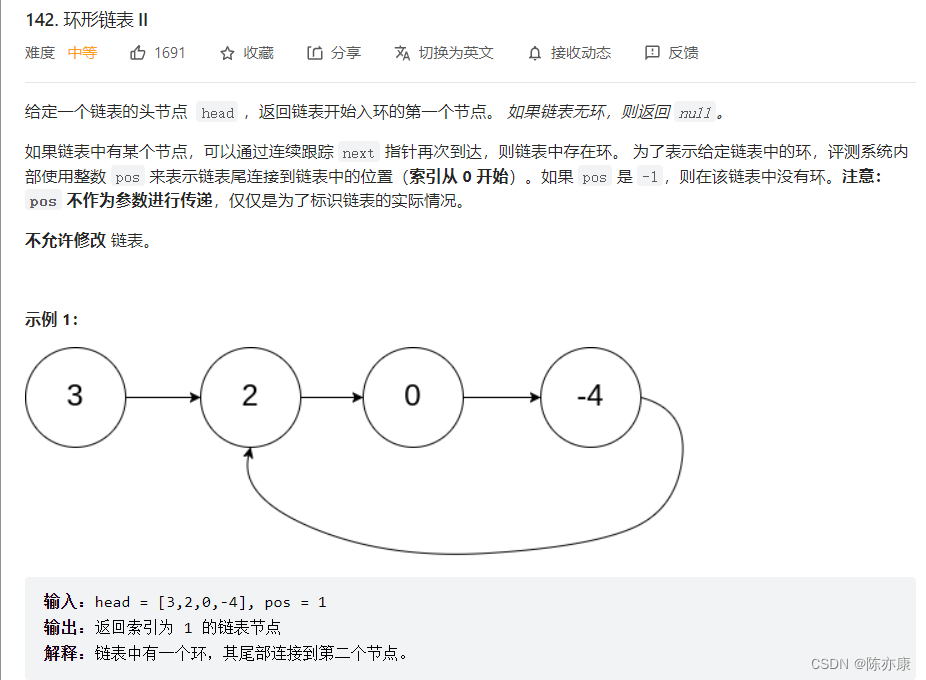
数学解决——环形链表问题

Ambiguous method call.both
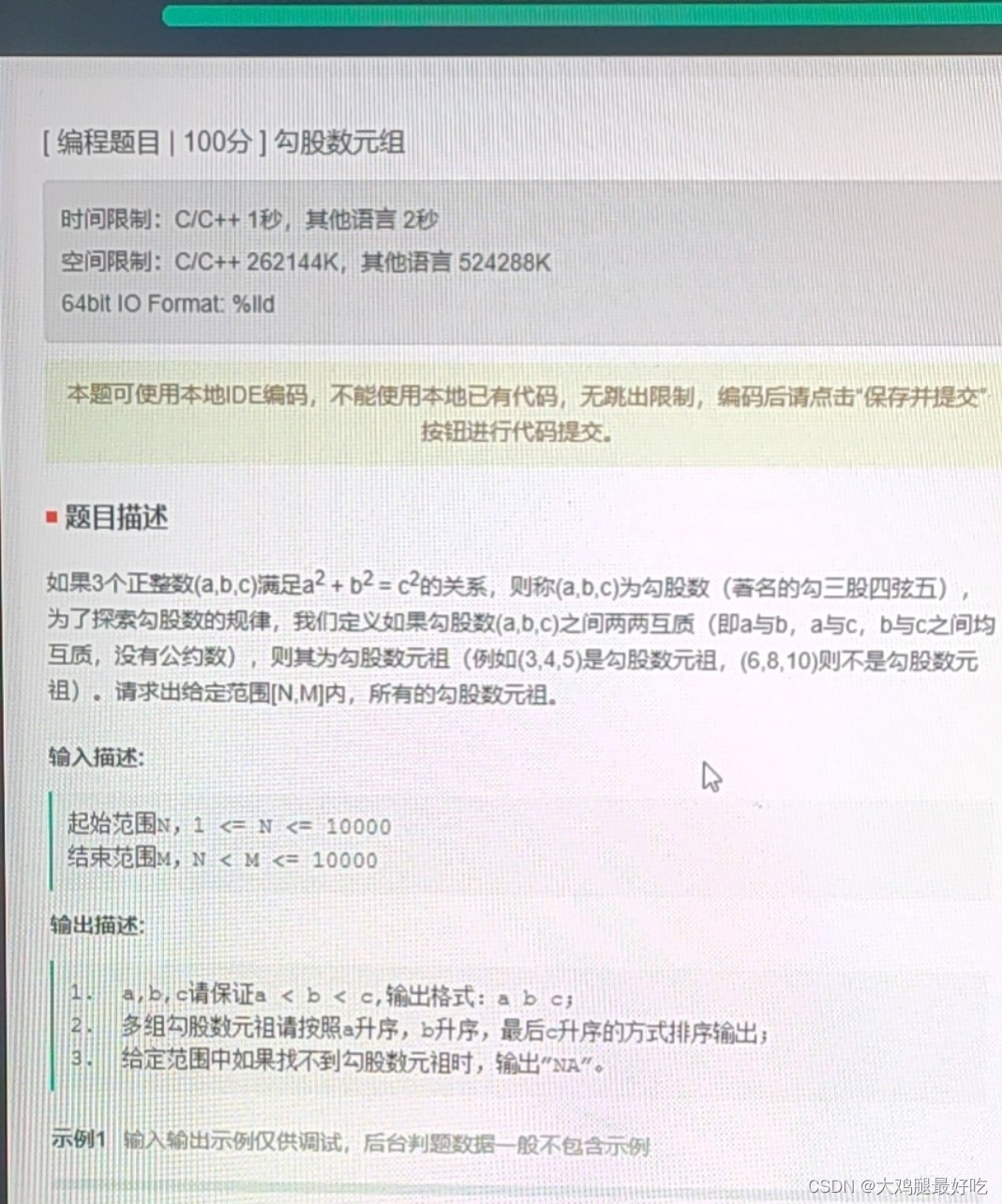
Pythagorean tuple od js
随机推荐
VS QT——ui不显示新添加成员(控件)||代码无提示
Mysql 45讲学习笔记(二十四)MYSQL主从一致
Intel's software and hardware optimization empowers Neusoft to accelerate the arrival of the era of smart medical care
JetPack组件Databinding
原子操作 CAS
下载jar包的好地方
LeetCode 每日一题 2022/7/25-2022/7/31
公司官网建站笔记(六):域名进行公安备案并将备案号显示在网页底部
Mathematics to solve the problem - circular linked list
11. Redis implements follow, unfollow, and follow and follower lists
Number 16, top posts
10 Permission introduction
测试中的误报和漏报同样的值得反复修正
编译Hudi
12 磁盘相关命令
华为分布式存储FusionStorage知识点总结【面试篇】
【C语言】进制转换一般方法
12 Disk related commands
The simulation application of common mode inductance is here, full of dry goods for everyone
开题报告之论文框架