当前位置:网站首页>Actual combat simulation │ JWT login authentication
Actual combat simulation │ JWT login authentication
2022-07-05 12:58:00 【51CTO】
Catalog
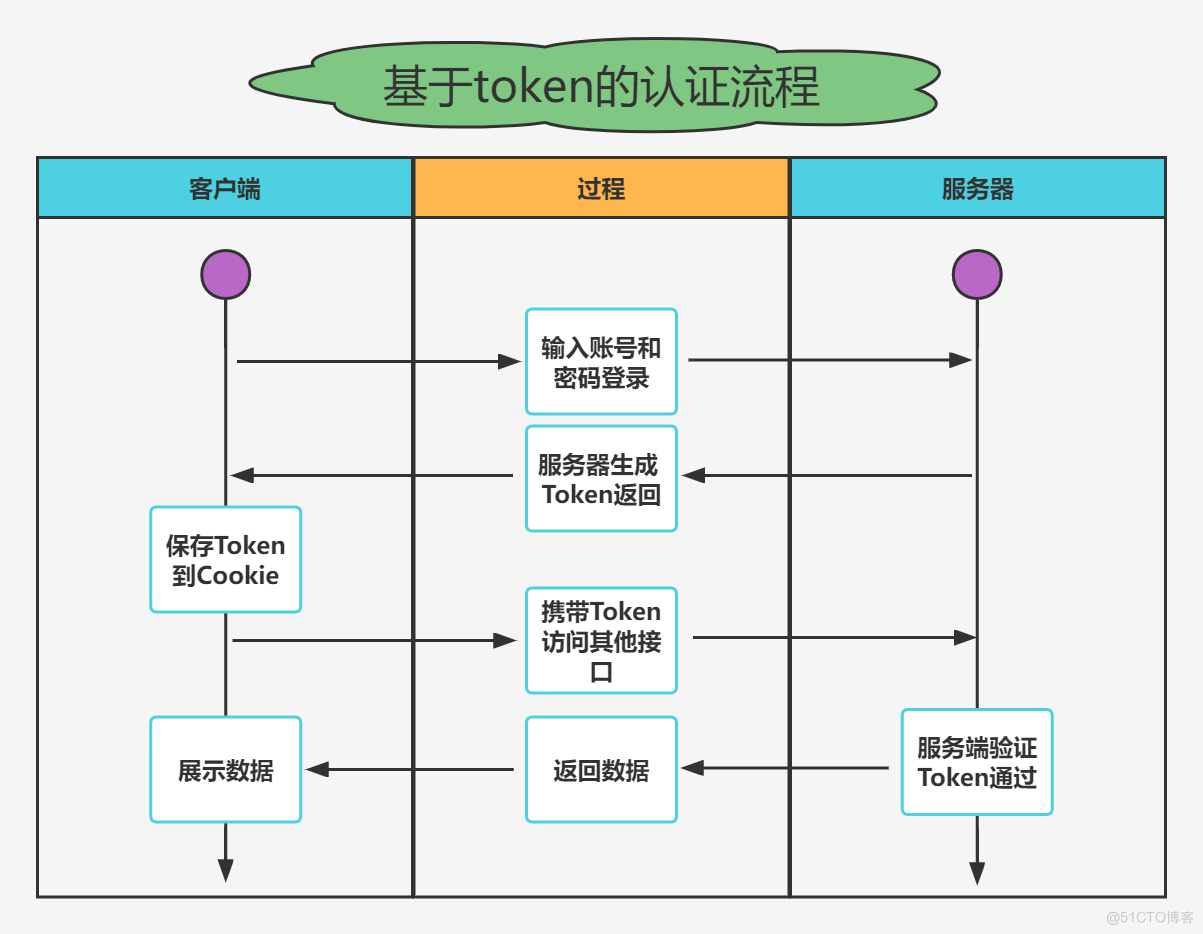
Token The certification process
- As the most popular cross domain authentication solution ,
JWT(JSON Web Token)Loved by developers , The main process is as follows : - The client sends an account and password to request login
- The server receives the request , Verify whether the account and password pass
- After successful verification , The server will generate a unique
token, And return it to the client - Client received
token, Store it incookieperhapslocalStrogein - After that, every time the client sends a request to the server , Will pass
cookieperhapsheaderTake with youtoken - Server side validation
tokenThe effectiveness of the , The data of the response is returned only after passing
Token Certification benefits
- Support cross domain access :
CookieCross domain access is not allowed , That's rightTokenThere is no mechanism , The premise is that the transmitted user authentication information passesHTTPHead transmission - No state :
TokenThe mechanism does not need storage on the serversessionInformation , becauseTokenIt contains the information of all users who log in , Just on the client sidecookieOr local media storage status information - More applicable : As long as it's support
httpProtocol client , You can usetokenauthentication . - Don't need to consider CSRF: Because no longer rely on
cookie, So usingtokenThe authentication method will not happenCSRF, So there is no need to considerCSRFDefense
JWT structure
- One
JWTIt's actually a string , It consists of three parts :Head、loadAndSignature. Middle point.Divided into three parts . Be carefulJWTThere is no line break inside .
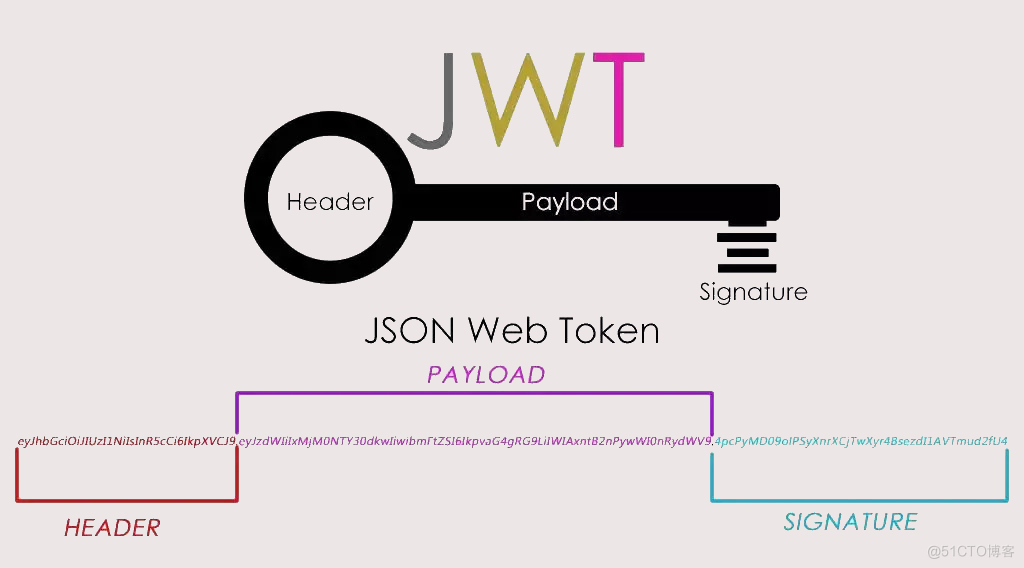
- Head / header
headerIt's made up of two parts :tokenThe type ofJWTAnd algorithm name :HMAC、SHA256、RSA
- load / Payload
PayloadPart of it is also aJSONobject , It is used to store the data that needs to be transferred .JWTSpecify seven default fields to choose from .- In addition to the default fields , You can add any field you want , Generally, after the user logs in successfully , Store user information here
- Signature / Signature
- The signature part is on the above Head 、 load Data signature with two parts of data
- To ensure that the data is not tampered with , You need to specify a key , And this key is usually only known by you , And stored on the server
- The code to generate the signature is generally as follows :
JWT Basic use
- The client receives the
JWT, Can be stored inCookieInside , It can also be stored inlocalStorage - then Every time the client communicates with the server , Take this with you
JWT - hold
JWTSave inCookieSend request inside , It can't beCross domain - It's better to put it in
HTTPRequested header informationAuthorizationIn the field
actual combat : Use JWT Login authentication
Use here
ThinkPHP6IntegrateJWTLogin and authenticate for actual combat simulationinstall JWT Expand
- Package generation JWT And decryption methods
- After the user logs in , Generate JWT identification
- Middleware verifies whether the user logs in
- stay
middleware.phpRegister middleware
- After registering middleware , Improve the verification logic in the permission verification middleware
边栏推荐
- 上午面了个腾讯拿 38K 出来的,让我见识到了基础的天花
- NLP engineer learning summary and index
- Introduction to sap ui5 dynamicpage control
- Talk about my drawing skills in my writing career
- SAP SEGW 事物码里的 Association 建模方式
- SAP UI5 DynamicPage 控件介紹
- 自然语言处理从小白到精通(四):用机器学习做中文邮件内容分类
- Introduction to the principle of DNS
- Comprehensive upgrade of Taobao short video photosynthetic platform
- 10 minute fitness method reading notes (3/5)
猜你喜欢
From the perspective of technology and risk control, it is analyzed that wechat Alipay restricts the remote collection of personal collection code
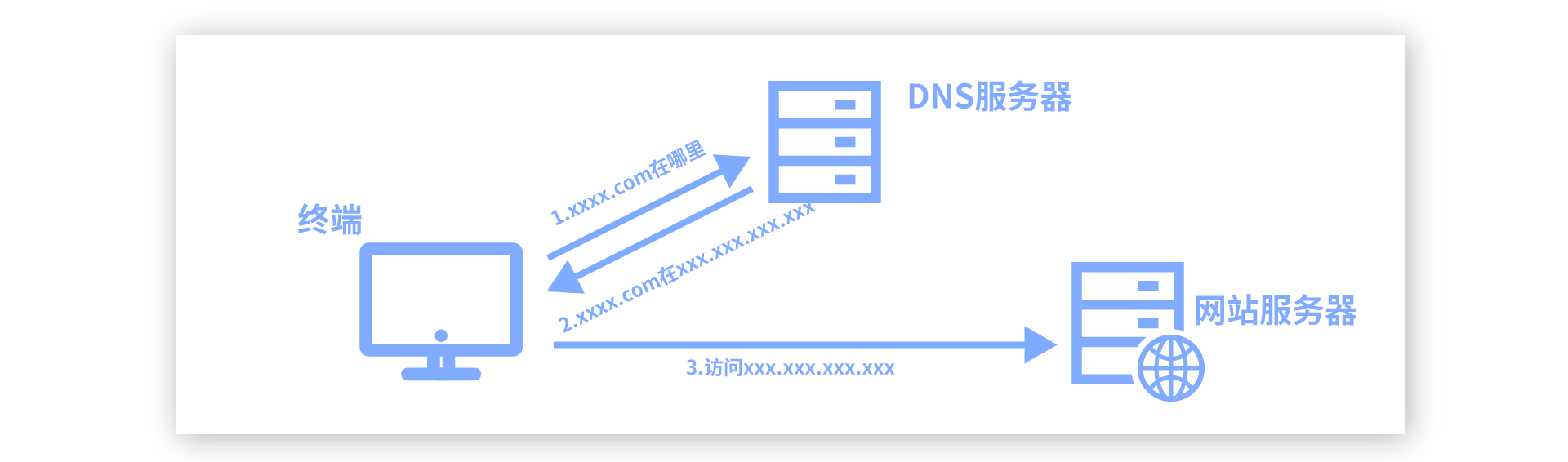
DNS的原理介绍

滴滴开源DELTA:AI开发者可轻松训练自然语言模型
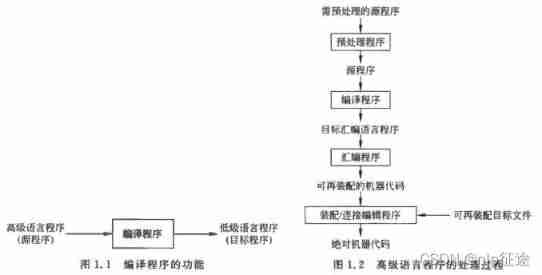
Compilation principle reading notes (1/12)

Transactions from January 14 to 19, 2022
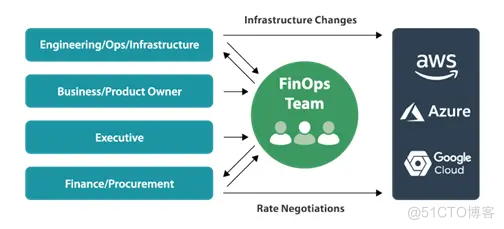
非技术部门,如何参与 DevOps?

2021-12-21 transaction record
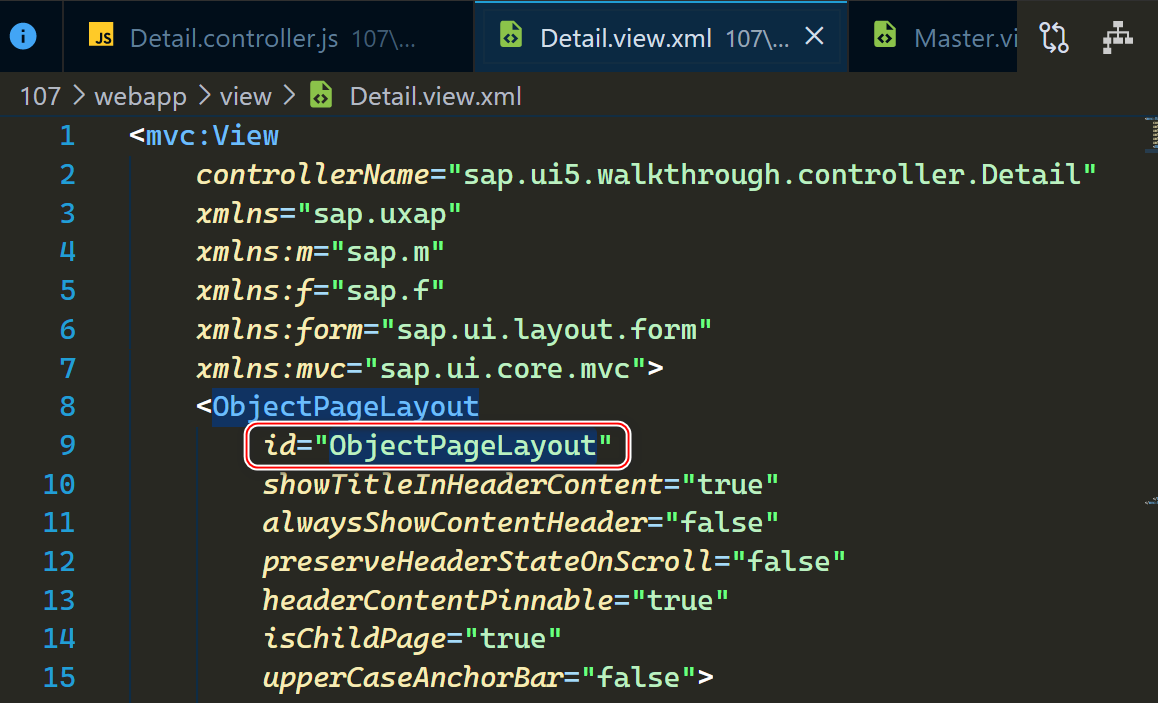
About the single step debugging of whether SAP ui5 floating footer is displayed or not and the benefits of using SAP ui5
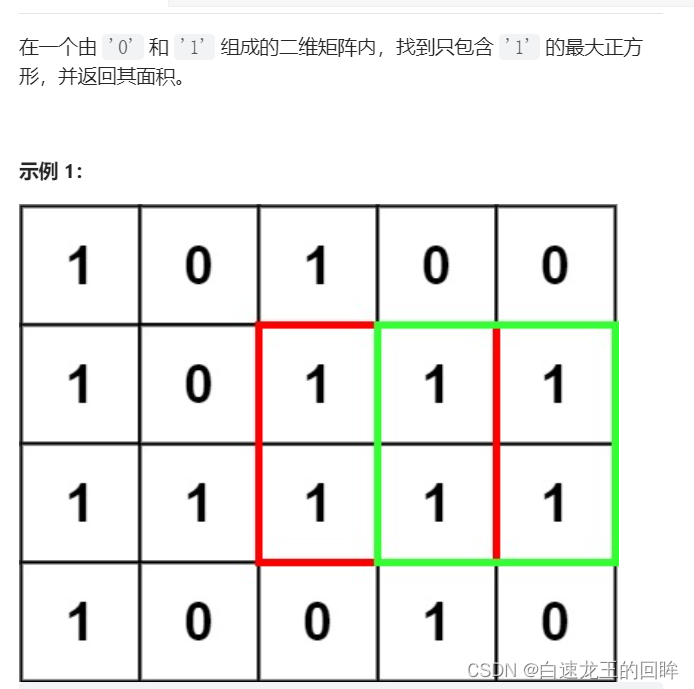
leetcode:221. 最大正方形【dp状态转移的精髓】
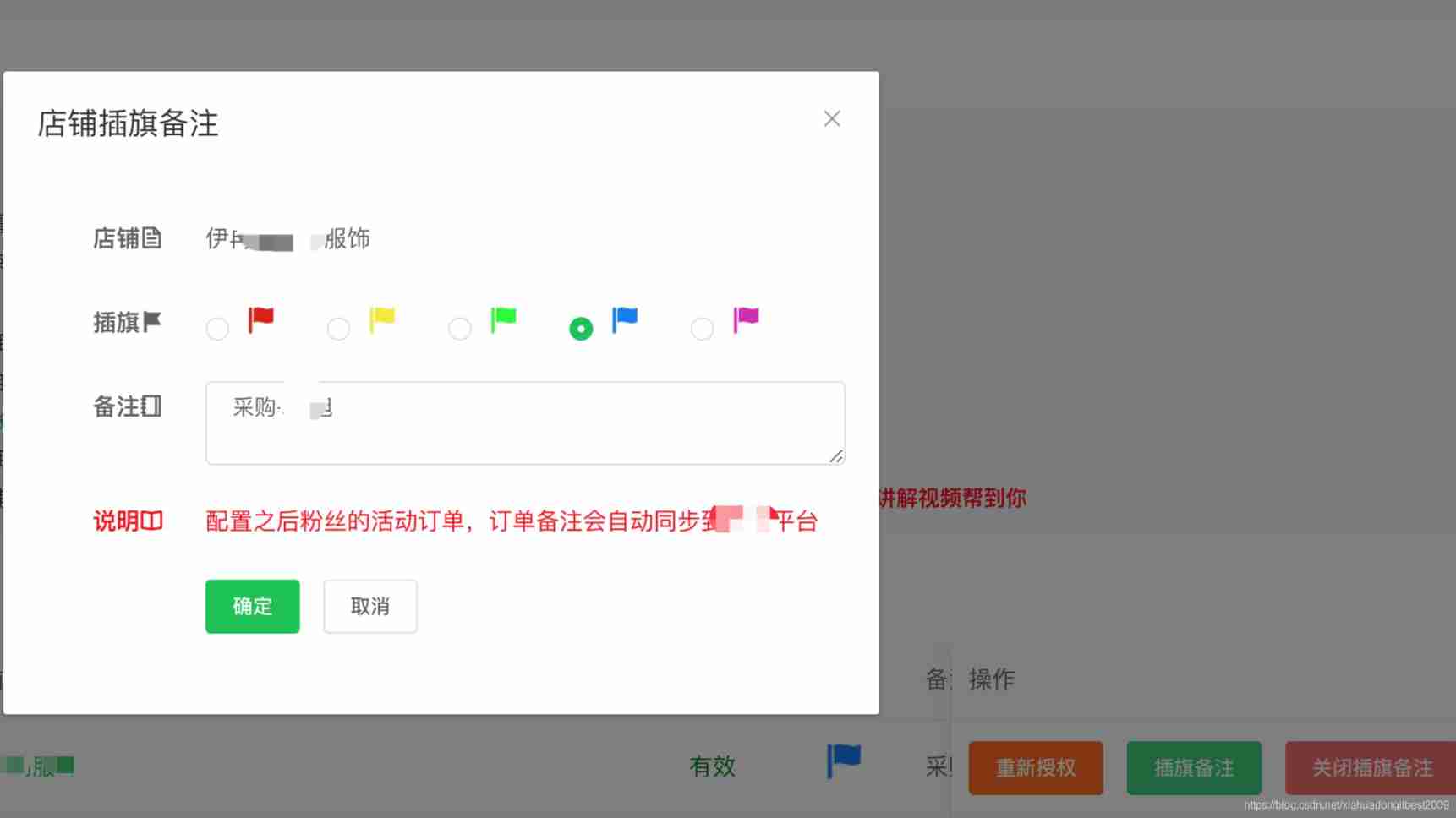
Pinduoduo flag insertion remarks API
随机推荐
SAP UI5 ObjectPageLayout 控件使用方法分享
Halcon template matching actual code (I)
Setting up sqli lab environment
初识Linkerd项目
SAP SEGW 事物码里的 ABAP Editor
Tips and tricks of image segmentation summarized from 39 Kabul competitions
JSON parsing error special character processing (really speechless... Troubleshooting for a long time)
A deep long article on the simplification and acceleration of join operation
Comprehensive upgrade of Taobao short video photosynthetic platform
使用 jMeter 对 SAP Spartacus 进行并发性能测试
OPPO小布推出预训练大模型OBERT,晋升KgCLUE榜首
stm32和电机开发(从架构图到文档编写)
奔跑,开路
CVPR 2022 | single step 3D target recognizer based on sparse transformer
[cloud native] use of Nacos taskmanager task management
##无监控,不运维,以下是监控里常用的脚本监控
Time conversion error
Taobao, pinduoduo, jd.com, Doudian order & Flag insertion remarks API solution
stirring! 2022 open atom global open source summit registration is hot!
Neural network of PRML reading notes (1)