当前位置:网站首页>[try to hack] active detection and concealment technology
[try to hack] active detection and concealment technology
2022-07-03 16:56:00 【Happy star】
https://www.bilibili.com/video/BV1bt4y1874s?p=79
Blog home page : Happy star The blog home page of
Series column :Try to Hack
Welcome to focus on the likes collection ️ Leaving a message.
Starting time :2022 year 7 month 3 Japan
The author's level is very limited , If an error is found , Please let me know , thank !
Active reconnaissance is based on OSNT Open source passive reconnaissance , Get more information about the goal , In order to find more places where there may be safety problems . But active reconnaissance will have a lot of interaction with the target , It is more likely to be detected by the target .
technology
1、 Camouflage tool signature
2、 Hide traffic from legitimate traffic
3、 Modify source and type
Adjust source IP Stack and tool identification settings
Common is to change User-Agent
Here we use msf To demonstrate msfconsoleuse auxiliary/fuzzers/http/http_form_field 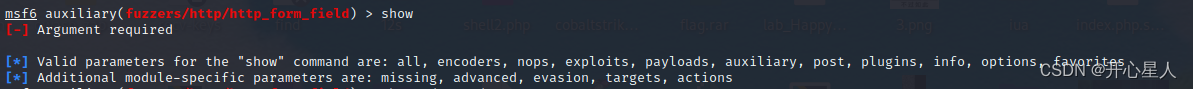
There is one advancedshow advanced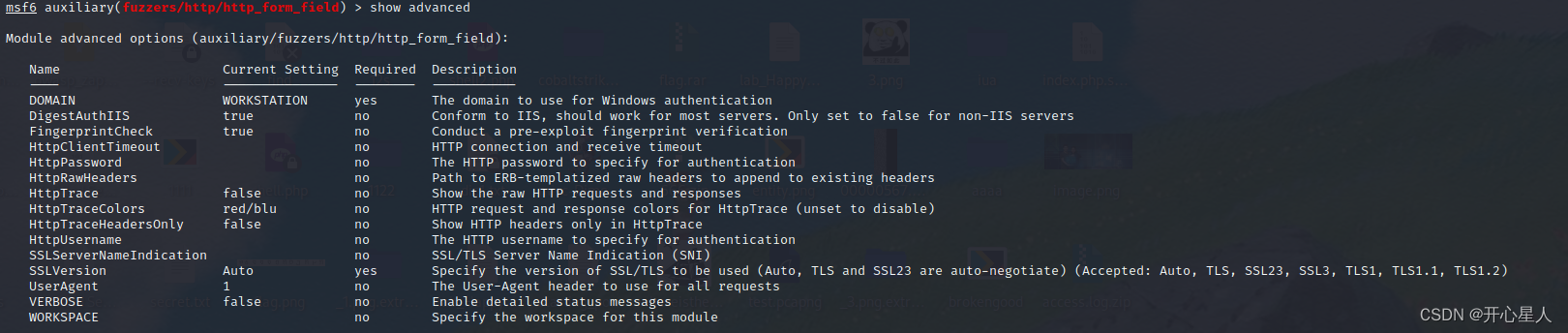
Yes useragentset useragent BaiduSpider // Search engine crawlers are generally not filtered set rhost 192.168.0.1 Set to route , Send... To route http Data packets run
wireshark Grab the bag and have a look
Filtering rules http&&ip.dst==192.168.0.1&&ip.src==192.168.0.106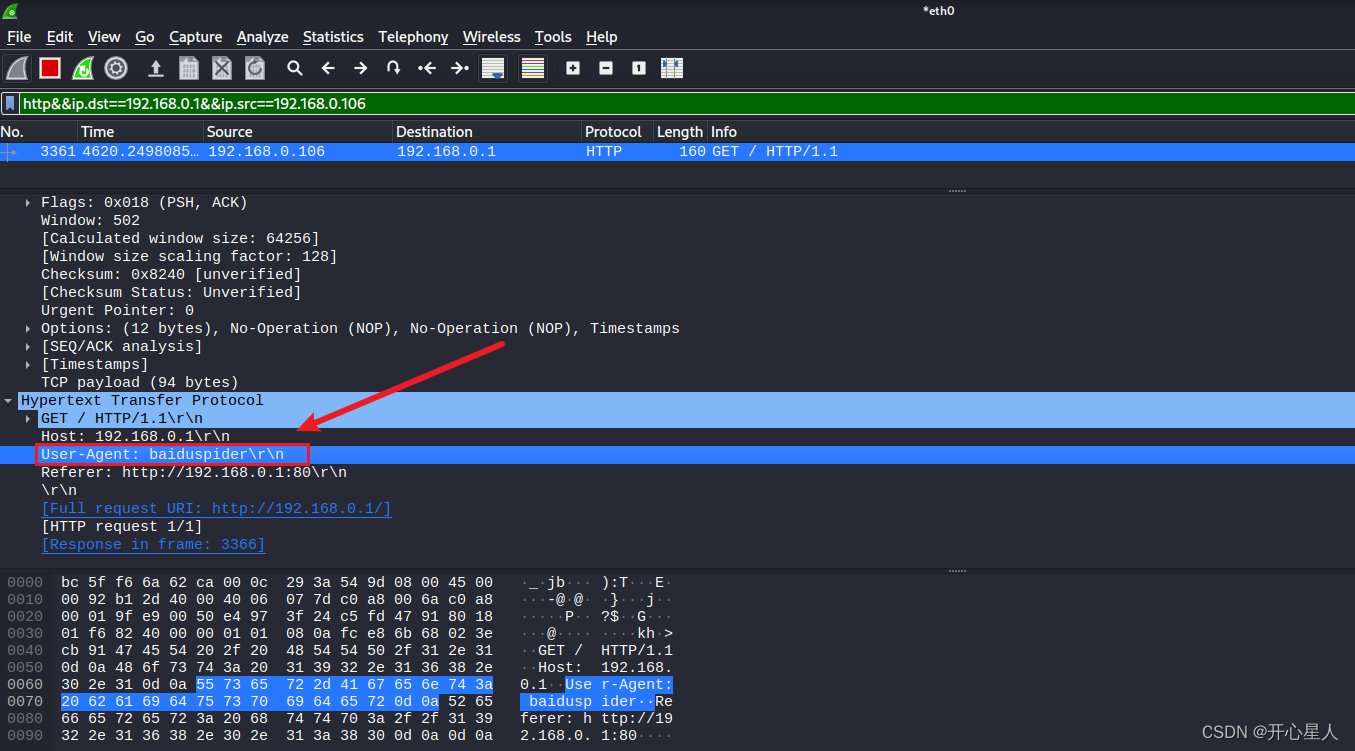
Modify packet parameters
Nmap Modify the original parameters nmap --spoof-mac 11:11:11:11:11:11 26 -sS -Pn -p80 192.168.0.1
It's really disguised mac Address , But why Destination yes 0.0.0.26, I don't know
Many other tools have similar functions to modify packet parameters
Such as masscan Of –adapter-mac、–adapter-ip
Use proxy anonymous Networks tor
When using Tor When the client , Your Internet Communication will be through Tor The network routing . Leaving Tor Before the network reaches its destination , The traffic will pass through several randomly selected relay stations ( Run by volunteers ). This will prevent Internet Service providers and people who monitor your local network view the websites you visit . It also prevents the website itself from knowing your actual location or IP Address - They will see the exit node IP Address and location . Even the relay station doesn't know who requested the traffic they passed . Tor All traffic in the network is encrypted .
apt install torservice tor start start-up torservice tor status see tor Whether to start 
Configure through installation proxychains4, Is to integrate any program and agent tools proxy Establishing a connection , The principle is similar to that of browser proxy .apt install proxychains4gedit /etc/proxychains4.conf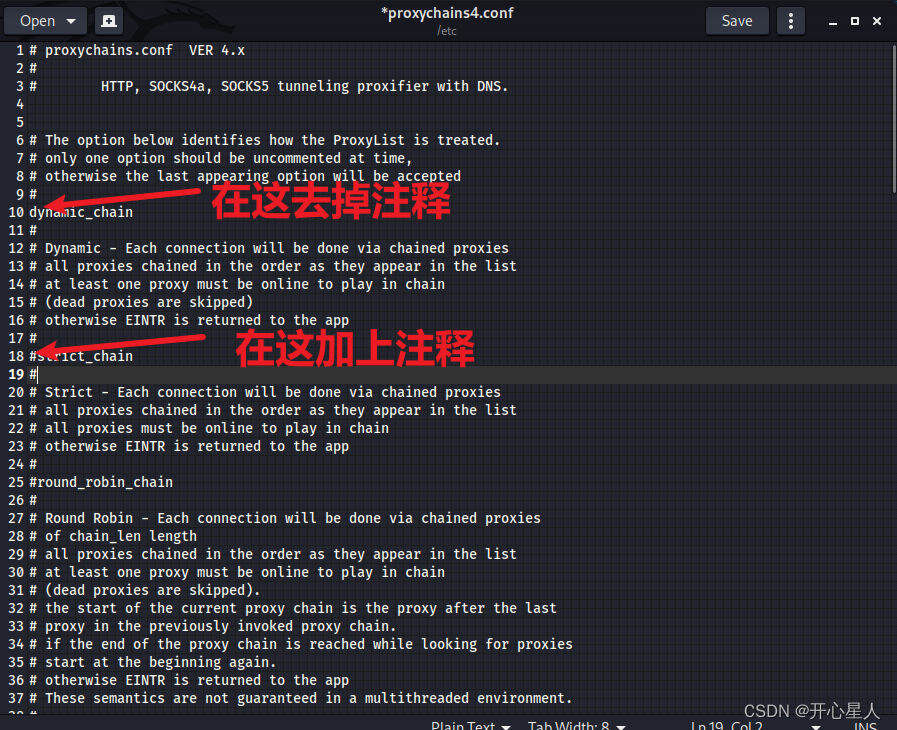

firefox www.whatismyip.com
I saw it , This is the truth that no proxy is used ip, It's really my public network ip
proxychains firefox www.whatismyip.com Modify agent
边栏推荐
- Atom QT 16_ audiorecorder
- A survey of state of the art on visual slam
- CC2530 common registers
- Learn from me about the enterprise flutter project: simplified framework demo reference
- 中南大学|通过探索理解: 发现具有深度强化学习的可解释特征
- [combinatorics] recursive equation (characteristic equation and characteristic root | example of characteristic equation | root formula of monadic quadratic equation)
- Build your own website (23)
- 深入理解 SQL 中的 Grouping Sets 语句
- 定义一个结构体Fraction,表示分数,用于表示 2/3, 5/6这样的分数
- Deep understanding of grouping sets statements in SQL
猜你喜欢
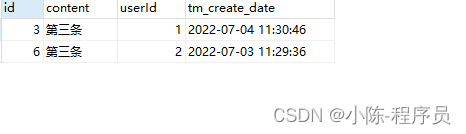
Mysql 单表字段重复数据取最新一条sql语句
![[combinatorics] polynomial theorem (polynomial theorem | polynomial theorem proof | polynomial theorem inference 1 item number is the number of non negative integer solutions | polynomial theorem infe](/img/9d/6118b699c0d90810638f9b08d4f80a.jpg)
[combinatorics] polynomial theorem (polynomial theorem | polynomial theorem proof | polynomial theorem inference 1 item number is the number of non negative integer solutions | polynomial theorem infe

Why is WPA3 security of enterprise business so important?

Two sides of the evening: tell me about the bloom filter and cuckoo filter? Application scenario? I'm confused..

Kotlin learning quick start (7) -- wonderful use of expansion
MySQL single table field duplicate data takes the latest SQL statement

线程池执行定时任务

Unreal_ Datatable implements ID self increment and sets rowname
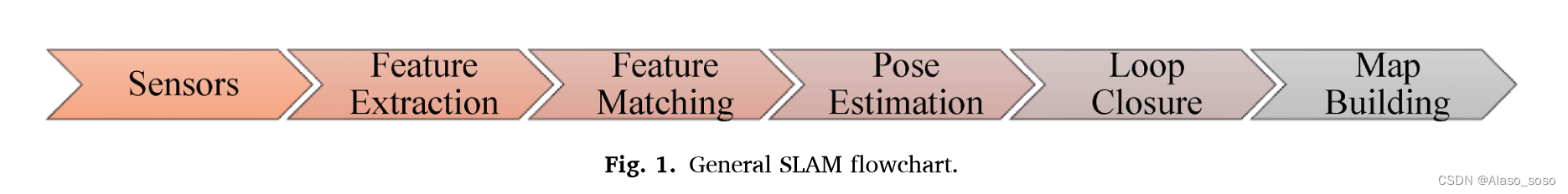
A survey of state of the art on visual slam

arduino-esp32:LVGL项目(一)整体框架
随机推荐
[combinatorics] recursive equation (the relationship theorem between the solution of the recursive equation and the characteristic root | the linear property theorem of the solution of the recursive e
PHP CI (CodeIgniter) log level setting
Svn usage specification
utfwry. Dat PHP, about ThinkPHP's method of IP location using utfwry address Library
中南大学|通过探索理解: 发现具有深度强化学习的可解释特征
[combinatorics] recursive equation (outline of recursive equation content | definition of recursive equation | example description of recursive equation | Fibonacci Series)
[combinatorics] recursive equation (characteristic equation and characteristic root | example of characteristic equation | root formula of monadic quadratic equation)
建立自己的网站(23)
Simulink oscilloscope data is imported into Matlab and drawn
LeetCode 1658. Minimum operand to reduce x to 0
汇编实例解析--实模式下屏幕显示
Prepare for the golden three silver four, 100+ software test interview questions (function / interface / Automation) interview questions. win victory the moment one raises one 's standard
Mysql database -dql
"The NTP socket is in use, exiting" appears when ntpdate synchronizes the time
[Jianzhi offer] 58 - ii Rotate string left
The most complete postman interface test tutorial in the whole network, API interface test
Why is WPA3 security of enterprise business so important?
[combinatorics] polynomial theorem (polynomial coefficients | full arrangement of multiple sets | number of schemes corresponding to the ball sub model | polynomial coefficient correlation identity)
数据分析必备的能力
MySQL user management