当前位置:网站首页>Nuclei (2) Advanced - In-depth understanding of workflows, Matchers and Extractors
Nuclei (2) Advanced - In-depth understanding of workflows, Matchers and Extractors
2022-08-04 23:19:00 【Test Dev Kevin】
前面的文章中介绍了nuclei的基础使用方法,可以参考文章:
POCSimulated attack weapon——Nuclei入门(一)
Next, I will focus on explainingnuclei中的三个概念,Workflows、Mathcer和Extractors.These will help you write more complex and efficient detection scripts!
workflows
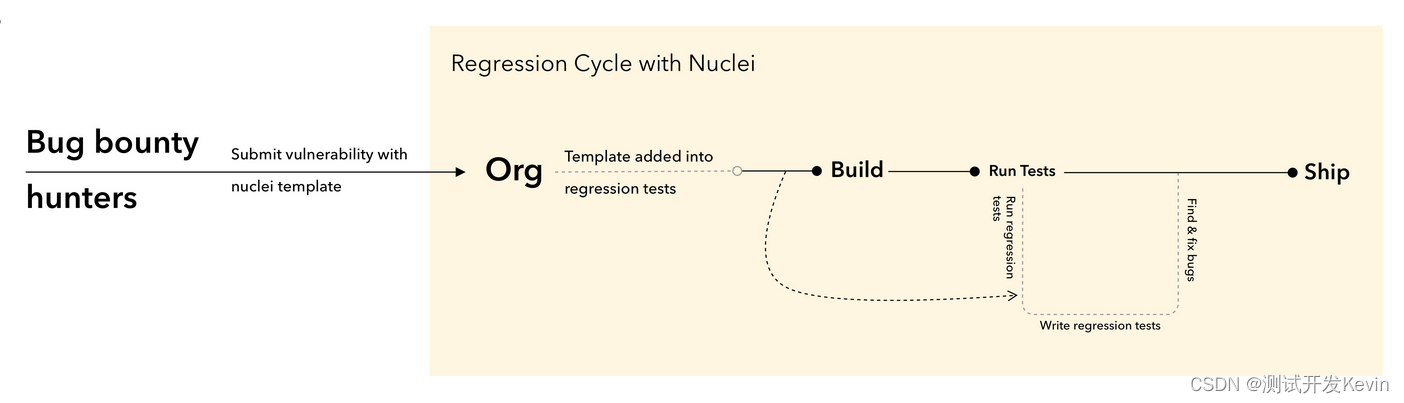
WorkflowsAllows users to customize the execution order of templates,这是使用nuclei最高效的方式,It is officially recommended that users use customWorkflowsThis reduces scan time,提升扫描效率!
- Basic Workflow
例如,定义workflow 扫描files目录下如下yaml
workflows:
- template: files/git-config.yaml
- template: files/svn-config.yaml
- template: files/env-file.yaml
- template: files/backup-files.yaml
- tags: xss,ssrf,cve,lfi- 条件工作流
首先确认springboot-detect.yaml是否正确执行,如果OK,则运行subtemplates下的template,实例如下:
id: springboot-workflow
info:
name: Springboot Security Checks
author: dwisiswant0
workflows:
- template: security-misconfiguration/springboot-detect.yaml
subtemplates:
- template: cves/CVE-2018-1271.yaml
- template: cves/CVE-2018-1271.yaml
- template: cves/CVE-2020-5410.yaml
- template: vulnerabilities/springboot-actuators-jolokia-xxe.yaml
- template: vulnerabilities/springboot-h2-db-rce.yaml运行workflows
nuclei -list http_urls.txt -w workflows/my-workflow.yaml
Matchers
Mathcer顾明思议,Just provide some rules,to compare and match the response results!There are six types in common use
mathcer,如下所示:
- status Integer Comparisons of Part
- size Content Length of Part
- word Part for a protocol
- regex Part for a protocol
- binary Part for a protocol
- dsl Part for a protocol
For example, you want to compare and match the response code,写法如下:
matchers:
# Match the status codes
- type: status
# Some status codes we want to match
status:
- 200When you want to do complex matching of response codes,可以使用dsl
matchers:
- type: dsl
dsl:
- "len(body)<1024 && status_code==200"
- "contains(toupper(body), md5(cookie))"The meaning of the previous example is that the length of the matching response body is less than1024 并且状态码是200
Judge capitalizedbody中是否包括cookie的md5sum
使用condition: and\or Multiple conditions can be matched,Default multiple conditions areand的关系
官方实例如下:
matchers:
# Match the body word
- type: word
# Some words we want to match
words:
- "[core]"
- "[config]"
# Both words must be found in the response body
condition: and
# We want to match request body (default)
part: body详情请参考 https://nuclei.projectdiscovery.io/templating-guide/operators/matchers/
Extractors
Extractors Also check the results,与matchers相比,It can display the content that satisfies the rules,Also he has different typesExtractors,如下所示:
1. regex - Extract data from response based on a Regular Expression.
2. kval - Extract key: value/key=value formatted data from Response Header/Cookie
3. json - Extract data from JSON based response in JQ like syntax.
4. xpath - Extract xpath based data from HTML Response
例如:
extractors:
- type: xpath # type of the extractor
attribute: href # attribute value to extract (optional)
xpath:
- "/html/body/div/p[2]/a" # xpath value for extraction5. dsl - Extract data from the response based on a DSL expressions.
详情请参考https://nuclei.projectdiscovery.io/templating-guide/operators/extractors/
由于使用nuclei时间尚浅,关于Extractors和Matchers,Personally, I don't think there's a big difference in usage!
Both are verifications of the results,与matchers相比,ExtractorsIt can display the content that satisfies the rules!If you need to write complex response validation,Then it takes time to researchdsl了.
如何从nuclei中受益
当使用了nuclei一段时间后,Personally I think it is actually usednucleiThe most valuable is the variety insidetemplate,We can look at eachtemplatescript to learn attack methods,And also according to the insidereference to view the details of the vulnerability,This is particularly helpful for the relevant accumulation of safety knowledge!As for the sending of the attack request,This is actually a lot easier,我们是否使用nuclei其实都无所谓的,举个简单的例子,关于CVE-2020-9484的 yaml脚本定义如下:
id: CVE-2020-9484
info:
name: Apache Tomcat Remote Command Execution
author: dwisiswant0
severity: high
description: |
When using Apache Tomcat versions 10.0.0-M1 to 10.0.0-M4, 9.0.0.M1 to 9.0.34, 8.5.0 to 8.5.54 and 7.0.0 to 7.0.103 if
a) an attacker is able to control the contents and name of a file on the server; and
b) the server is configured to use the PersistenceManager with a FileStore; and
c) the PersistenceManager is configured with sessionAttributeValueClassNameFilter="null" (the default unless a SecurityManager is used) or a sufficiently lax filter to allow the attacker provided object to be deserialized; and
d) the attacker knows the relative file path from the storage location used by FileStore to the file the attacker has control over; then, using a specifically crafted request, the attacker will be able to trigger remote code execution via deserialization of the file under their control.
Note that all of conditions a) to d) must be true for the attack to succeed.
reference:
- http://packetstormsecurity.com/files/157924/Apache-Tomcat-CVE-2020-9484-Proof-Of-Concept.html
- https://nvd.nist.gov/vuln/detail/CVE-2020-9484
- https://lists.apache.org/thread.html/r77eae567ed829da9012cadb29af17f2df8fa23bf66faf88229857bb1%40%3Cannounce.tomcat.apache.org%3E
- https://lists.apache.org/thread.html/[email protected]%3Cusers.tomcat.apache.org%3E
classification:
cvss-metrics: CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H
cvss-score: 7
cve-id: CVE-2020-9484
cwe-id: CWE-502
tags: cve,cve2020,apache,tomcat,rce
requests:
- method: GET
headers:
Cookie: "JSESSIONID=../../../../../usr/local/tomcat/groovy"
path:
- "{
{BaseURL}}/index.jsp"
matchers-condition: and
matchers:
- type: status
status:
- 500
- type: word
part: body
words:
- "Exception"
- "ObjectInputStream"
- "PersistentManagerBase"
condition: and这个脚本中,The easiest is probablyrequests:Part of the attack script code,我们用jmeter Or the way you write your own code can be easily simulated!而description:部分以及reference:Parts are what we need to focus on!It is also our deep understandingpocBest example of an attack!
边栏推荐
- ClickHouse 二级索引
- 安全软件 Avast 与赛门铁克诺顿 NortonLifeLock 合并案获英国批准,市值暴涨 43%
- Since a new byte of 20K came out, I have seen what the ceiling is
- 深度|医疗行业勒索病毒防治解决方案
- 【3D建模制作技巧分享】Maya模型如何导入zbrush
- PID Controller Improvement Notes No. 7: Improve the anti-overshoot setting of the PID controller
- 【游戏建模模型制作全流程】在ZBrush中雕刻恶魔城男性角色模型
- 文献阅读十——Detect Rumors on Twitter by Promoting Information Campaigns with Generative Adversarial Learn
- 容联云发送短信验证码
- MySQL的安装与卸载
猜你喜欢
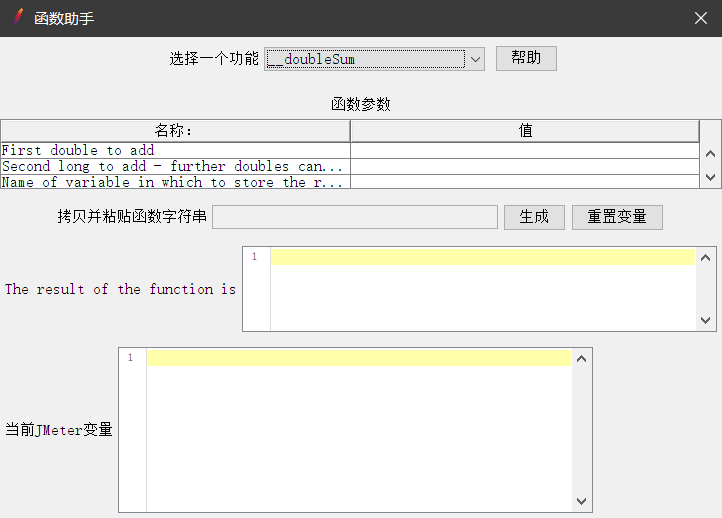
年薪50W+的测试工程师都在用这个:Jmeter 脚本开发之——扩展函数

正则表达式绕过
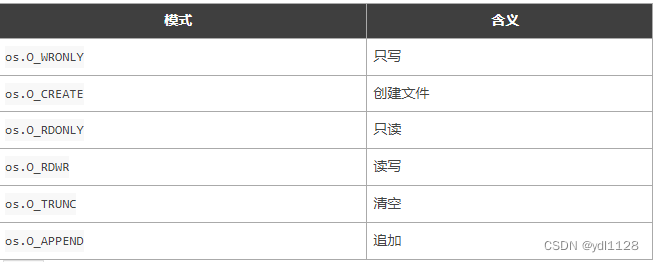
golang打开文件和读写文件
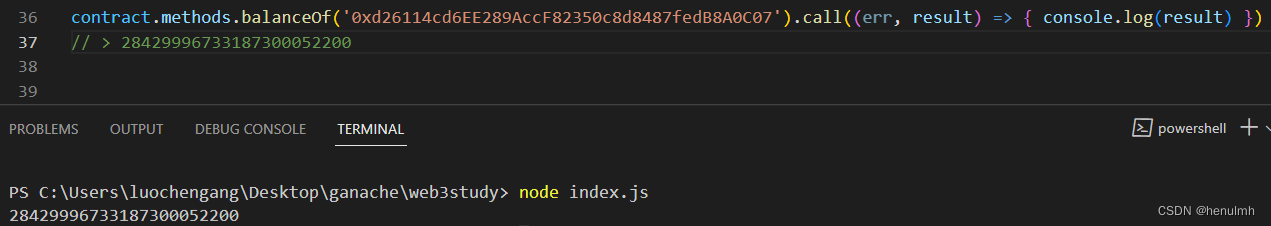
web3.js
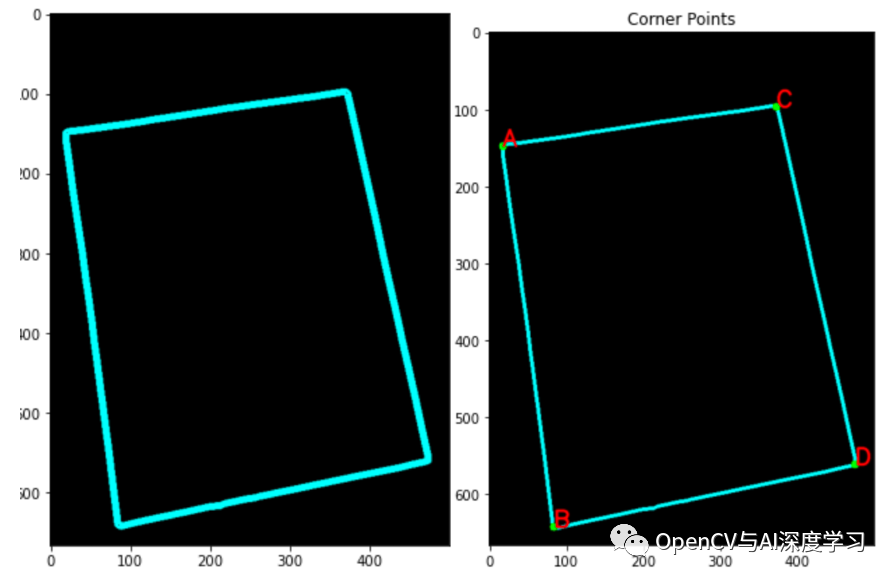
使用OpenCV实现一个文档自动扫描仪

轮播图动态渲染
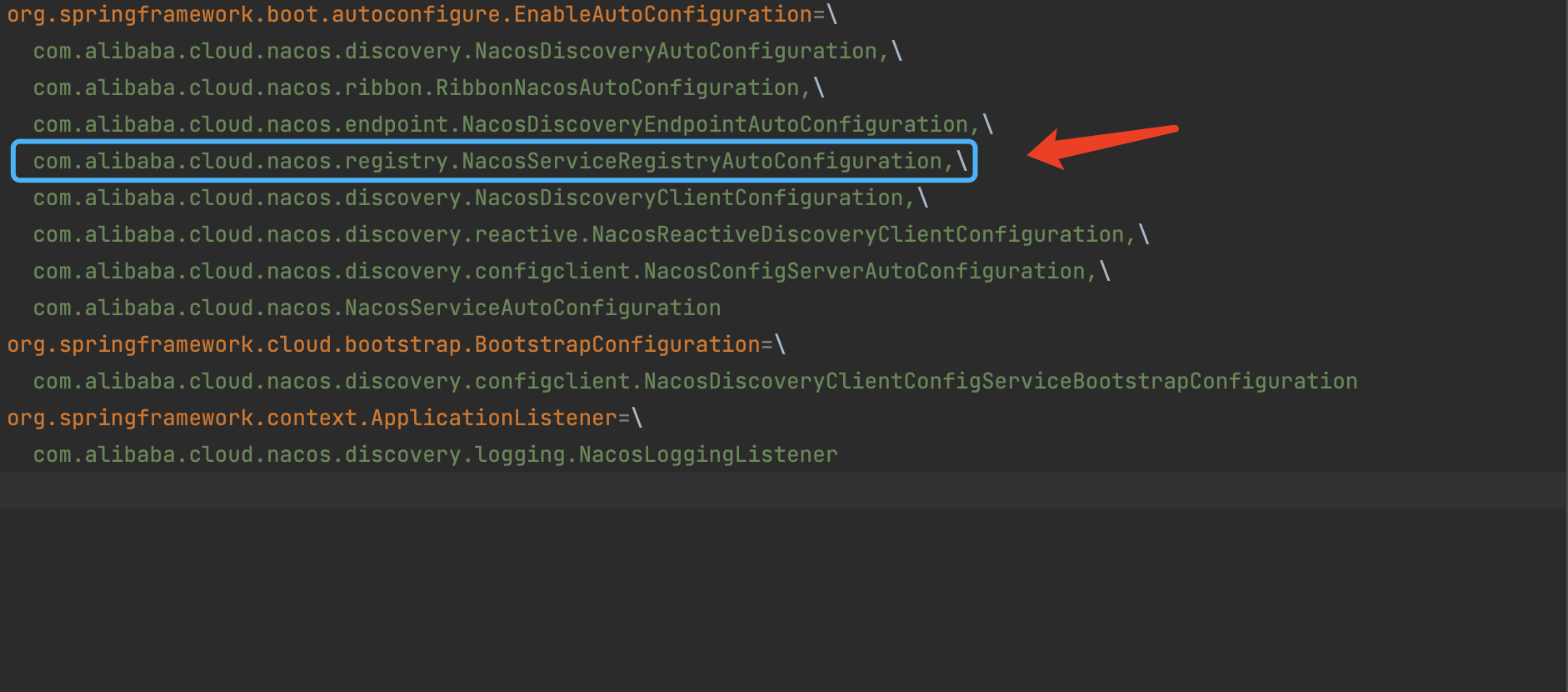
【七夕快乐篇】Nacos是如何实现服务注册功能的?
![[Cultivation of internal skills of string functions] strlen + strstr + strtok + strerror (3)](/img/96/946bbef52bd017ac6142c6b7485a86.png)
[Cultivation of internal skills of string functions] strlen + strstr + strtok + strerror (3)
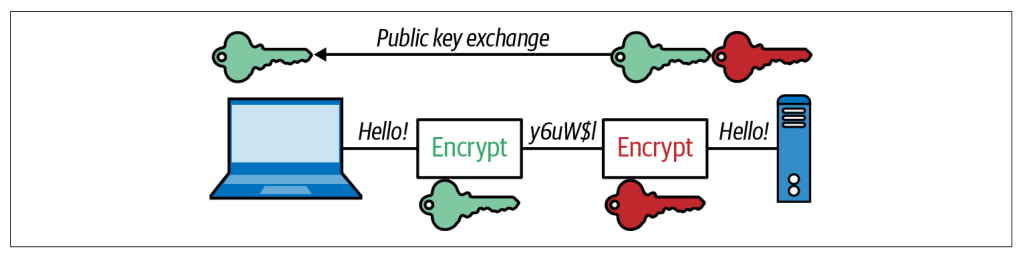
Go 语言快速入门指南:什么是 TSL 安全传输层
The market value of 360 has evaporated by 390 billion in four years. Can government and enterprise security save lives?
随机推荐
[QNX Hypervisor 2.2用户手册]10.6 vdev mc146818
【3D建模制作技巧分享】在zbrush中如何雕刻头发 ZBrush头发雕刻小技巧
temp7777
956. 最高的广告牌
【游戏建模模型制作全流程】ZBrush蜥蜴模型雕刻教程
Service Mesh landing path
【手撕AHB-APB Bridge】~ AMBA总线 之 AHB
一点点读懂regulator(四)
typeScript-promise
Controller层代码这么写,简洁又优雅!
The market value of 360 has evaporated by 390 billion in four years. Can government and enterprise security save lives?
node中package解析、npm 命令行npm详解,node中的common模块化,npm、nrm两种方式查看源和切换镜像
NebulaGraph v3.2.0 Release Note,对查询最短路径的性能等多处优化
深度|医疗行业勒索病毒防治解决方案
小黑leetcode冲浪:94. 二叉树的中序遍历
【SSR服务端渲染+CSR客户端渲染+post请求+get请求+总结】
kernel问题定位手段总结
应用联合、体系化推进。集团型化工企业数字化转型路径
【字符串函数内功修炼】strlen + strstr + strtok + strerror(三)
TypeScript - the use of closure functions