当前位置:网站首页>深度学习笔记(持续更新中。。。)
深度学习笔记(持续更新中。。。)
2022-07-03 01:29:00 【北村南】
数据预处理之One-Hot - 知乎 (zhihu.com)
一个人在不接触对方的情况下,通过一种特殊的方式,和对方进行一系列的问答.如果在相当长时间内,他无法根据这些问题判断对方是人还是计算机,那么就可以认为这个计算机是智能的。
——阿兰·图灵(Alan Turing)
《Computing Machinery and Intelligence 》
知识体系
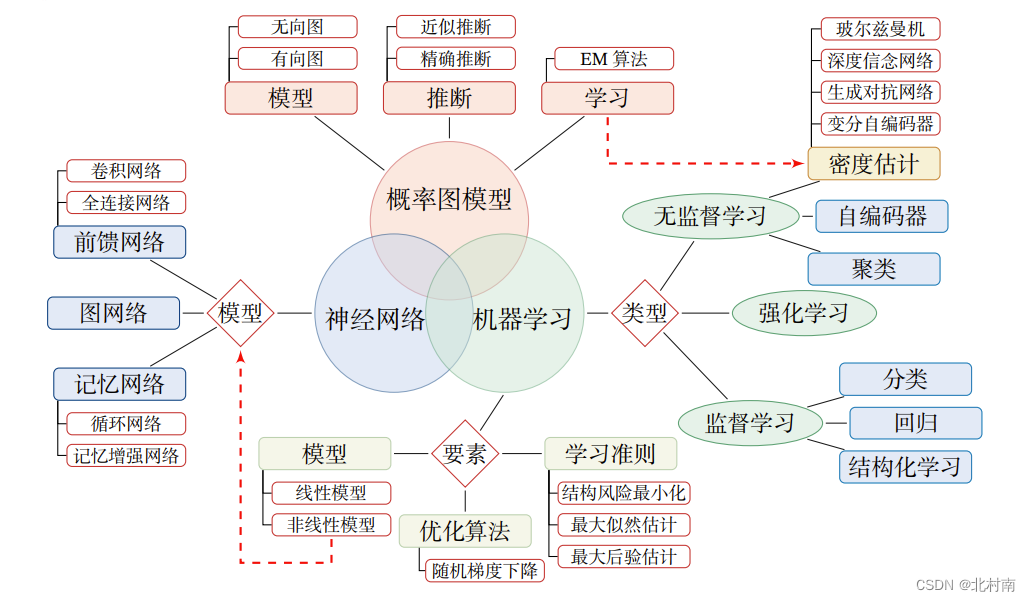
深度学习为什么主要使用神经网络呢?
其主要原因是神经网络模型可以使用误差反向传播BP算法,从而可以比较好地解决贡献度分配问题
神经网络需要学习的内容:各个神经元之间连接的权重参数
为什么要使用激活函数:如果不使用激活函数,那么每一层的输出为上一层输入的线性函数,那么最终导致整个网络是线性的,即最原始的感知机(Perceptron),其表示能力较差
神经元
神经网路是由一个个神经元组成的,每个神经元的结构如下

激活函数
其中f为激活函数,常见的激活函数如下
Sigmoid函数

ReLu函数

Swish函数

网络结构
常见的有三种网络结构,前馈网络FNN类似于一个有向无环图,信息只能朝一个方向传播,较为简单。记忆网络MN类似一个有向循环图,信息可以单向也可以双向传播,较为复杂。图网络GN是前馈网络和记忆网络的泛化,其中每个方格为一个或一组神经元

参考资料
《神经网络与深度学习》--邱锡鹏教授
《动手学深度学习》Pytorch版开源--李沐
《2022深度学习与机器学习》--吴恩达
边栏推荐
- [data mining] task 3: decision tree classification
- 【數據挖掘】任務6:DBSCAN聚類
- Analyzing several common string library functions in C language
- Sweet talk generator, regular greeting email machine... Open source programmers pay too much for this Valentine's day
- "Jetpack - livedata parsing"
- Network security - DNS spoofing and phishing websites
- His experience in choosing a startup company or a big Internet company may give you some inspiration
- [keil5 debugging] debug is stuck in reset_ Handler solution
- 网络安全-NAT网络地址转换
- 【数据挖掘】任务4:20Newsgroups聚类
猜你喜欢
![[North Asia data recovery] data recovery case of raid crash caused by hard disk disconnection during data synchronization of hot spare disk of RAID5 disk array](/img/2a/98400b0d0b5eda1e52abae30746f2b.jpg)
[North Asia data recovery] data recovery case of raid crash caused by hard disk disconnection during data synchronization of hot spare disk of RAID5 disk array
![[data mining] task 4:20newsgroups clustering](/img/76/af1d1338c468ec4825fe12816b84ff.png)
[data mining] task 4:20newsgroups clustering

PS remove watermark details

Main features of transport layer TCP and TCP connection
¢ growth path and experience sharing of getting an offer
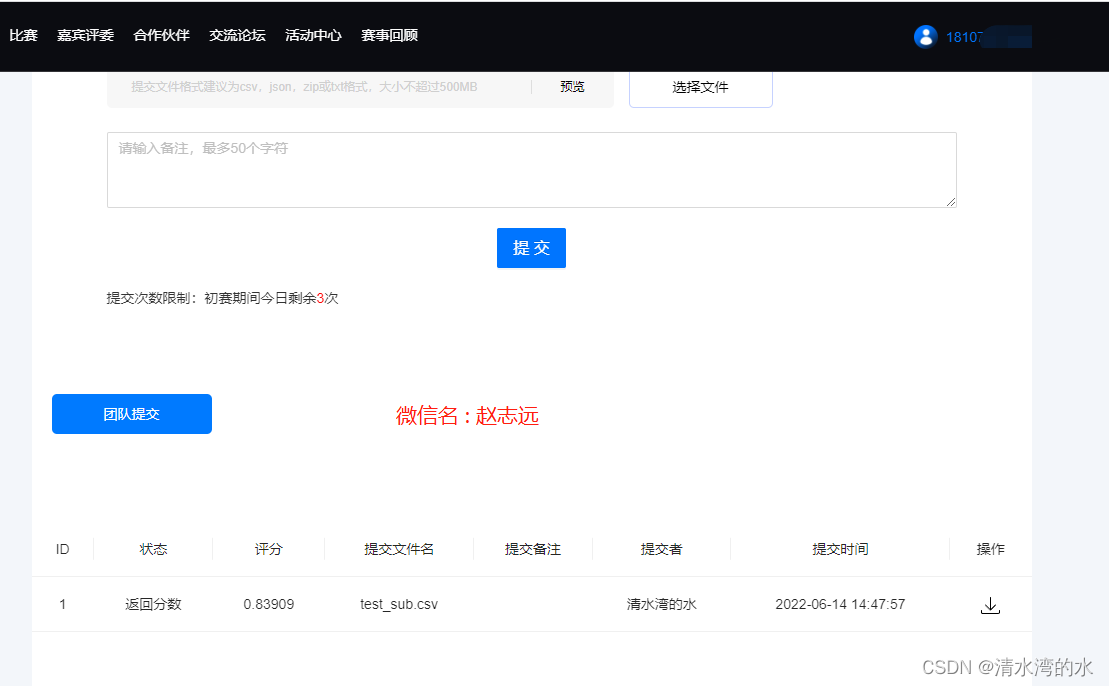
Telecom Customer Churn Prediction challenge
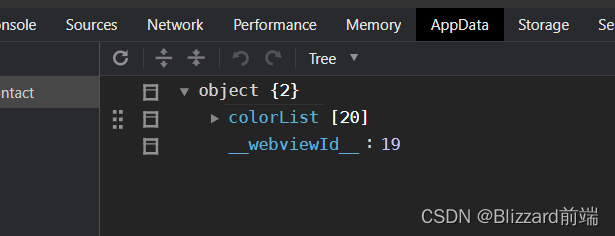
Some functions of applet development

The testing process that software testers should know
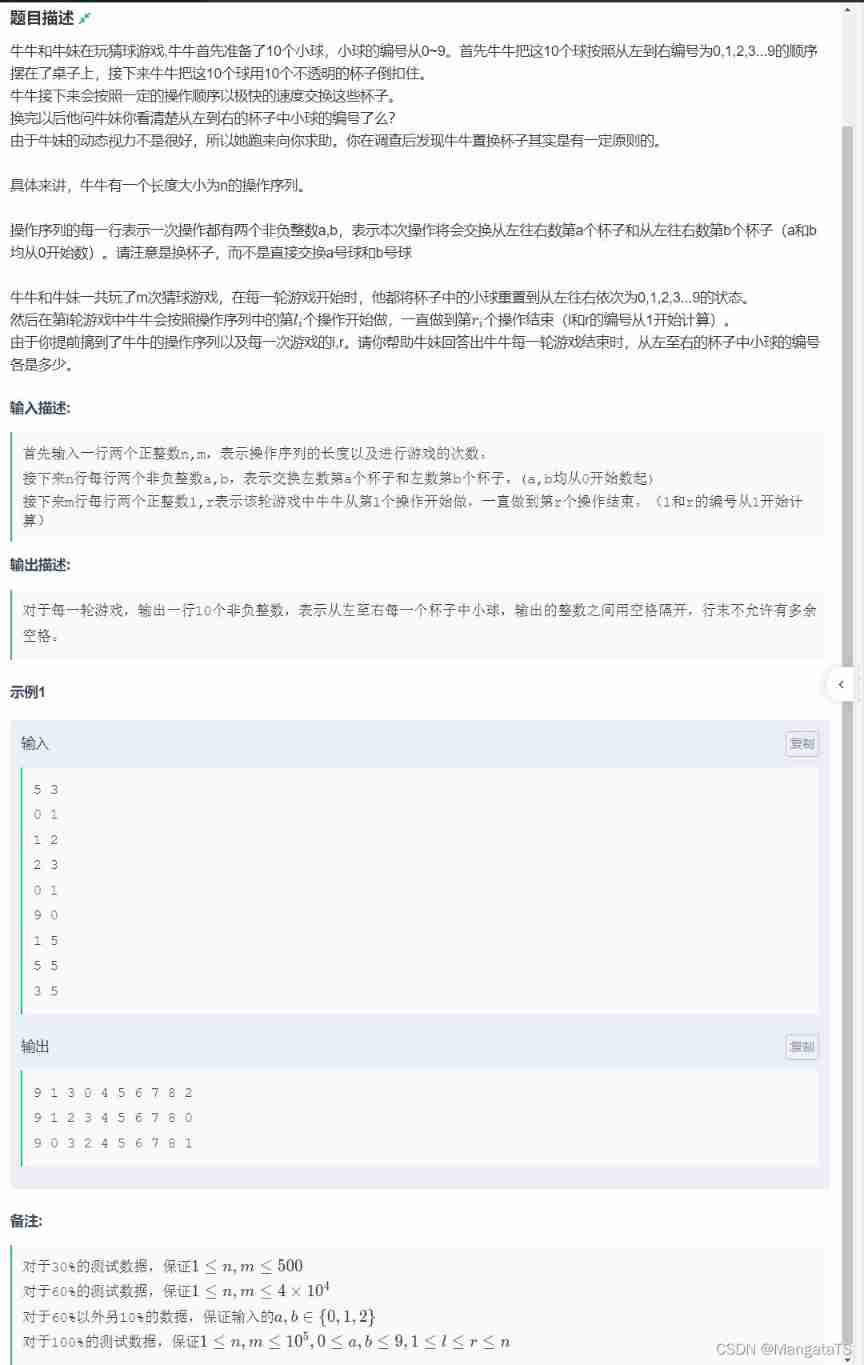
Niuniu's ball guessing game (dynamic planning + prefix influence)
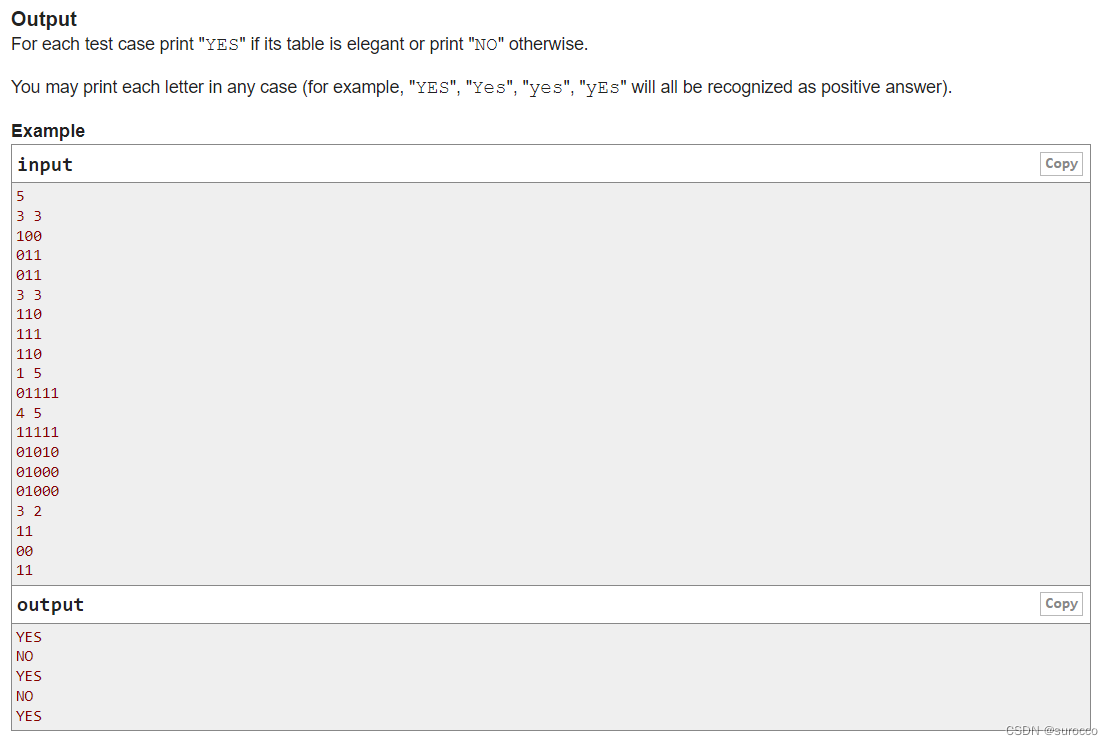
CF1617B Madoka and the Elegant Gift、CF1654C Alice and the Cake、 CF1696C Fishingprince Plays With Arr
随机推荐
STM32 - switch of relay control lamp
全链路数字化转型下,零售企业如何打开第二增长曲线
String splicing function of MySQL
Network security - man in the middle attack
DML Foundation
网络安全-病毒
转载收录6.5大侠写的部分Qt开发经验
[data mining] task 6: DBSCAN clustering
Button button adaptive size of wechat applet
Reprint some Qt development experience written by great Xia 6.5
[QT] encapsulation of custom controls
[shutter] animation animation (basic process of shutter animation | create animation controller | create animation | set value listener | set state listener | use animation values in layout | animatio
Internal connection query and external connection
Analysis, use and extension of open source API gateway apisex
[Appendix 6 Application of reflection] Application of reflection: dynamic agent
[data mining] task 2: mimic-iii data processing of medical database
Network security - phishing
Network security - cracking system passwords
When the epidemic comes, how to manage the team as a leader| Community essay solicitation
[fluent] hero animation (hero animation use process | create hero animation core components | create source page | create destination page | page Jump)