当前位置:网站首页>New Questions in Module B of Secondary Vocational Network Security Competition
New Questions in Module B of Secondary Vocational Network Security Competition
2022-08-04 07:32:00 【Wangzai Sec】
Environment private message blogger
Competition group: 421865857
Trojan information acquisition
Task environment description:
- Download 0077.pcap from the FTP of the target server, analyze the file, find out the protocol used by hackers, and submit the protocol name.
- Analyze the file, find out the zip archive file obtained by hackers, and submit the archive file name.
- Analyze the file, find out the sensitive files obtained by hackers, and submit the file name of the sensitive file
- Analyze the file, find out the sensitive file obtained by hackers, and submit the time when the sensitive file was leaked.
- Analyze the file, find out the sensitive file obtained by hackers, and submit the name of the leaked folder in the sensitive file.
Weak password blasting
1. Download 0064.py from the FTP of the target server, edit the Python program, make the program implement weak password blasting, and fill in the vacant F1 string in the file, generate a password list
2. Edit the Python program 0064.py to make the program implement weak password blasting, fill in the vacant F2 string in the file, and fill in the connected host;
3. Edit the Python program 0064.py to make the program implement weak password blasting, fill in the vacant F3 string in the file, and fill in the connection password;
4. Edit the Python program 0064.py to make the program implement weak password blasting, fill in the vacant F4 string in the file, and write out the processing logic for connection failure /span> 5. Edit the Python program 0064.py to make the program implement weak password blasting, fill in the vacant F5 string in the file, and write the processing logic for successful connection; 6. Edit the Python program 0064.py to make the program implement weak password blasting, fill in the vacant F6 string in the file, and write the value of the judgment result.Know if the blasting is successful; Encoding information acquisition redisUnauthorized accessp> 1.Download 0062.py from the FTP of the target server, edit the Python program, and make the program based onThe socket's redis is not authorized to identify, fill in the vacant F1 string in the file, and generate a socket object 2. Edit the Python program 0062.py to enable the program to implement socket-based redis unauthorized identification, fill in the vacant F2 string in the file, and connect to the target machine; 3. Edit the Python program 0062.py to enable the program to implement socket-based redis unauthorized identification, fill in the vacant F3 string in the file, and send the data; /span> 4. Edit the Python program 0062.py to enable the program to implement socket-based redis unauthorized identification, fill in the vacant F4 string in the file, and receive data 5. Edit the Python program 0062.py to implement socket-based redis unauthorized identification, fill in the vacant F5 string in the file, and close the connection object; 6. Edit the Python program 0062.py to enable the program to implement socket-based redis unauthorized identification, fill in the vacant F6 string in the file, and write if trueThe execution statement;
边栏推荐
猜你喜欢
随机推荐
两日总结六
Mac安装PHP开发环境
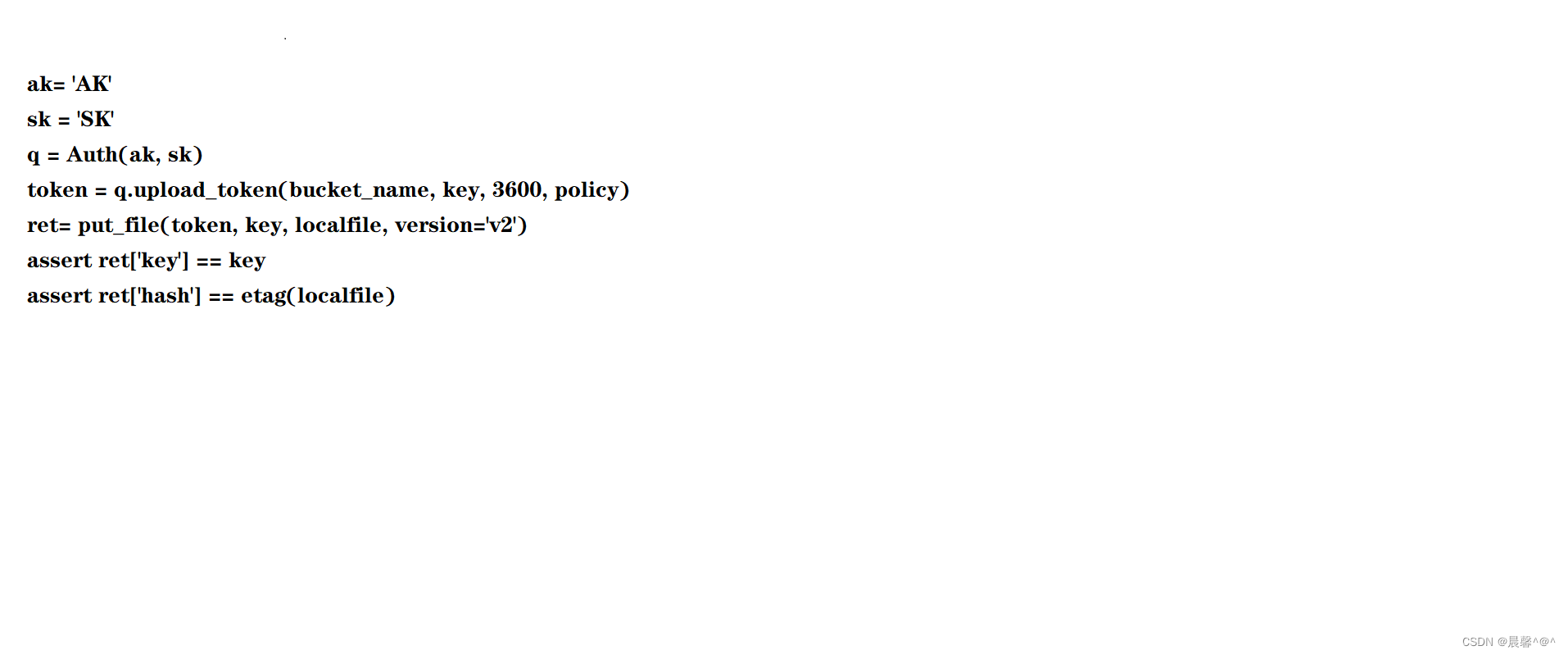
七牛云上传图片和本地上传
关于我写的循环遍历
entity、domain、vo、pojo的区别与联系
Promise.all 使用方法
90多款matlab工具箱打包放送
将回调函数转为Flow
Amazon亚马逊 Vendor Central Label详解
科研绘图图表类型种类繁多,本文告诉你如何选择!
西门子PLC1200与fanuc机器人进行profibus通讯
中职网络安全竞赛B模块新题
CAN协议详解-01
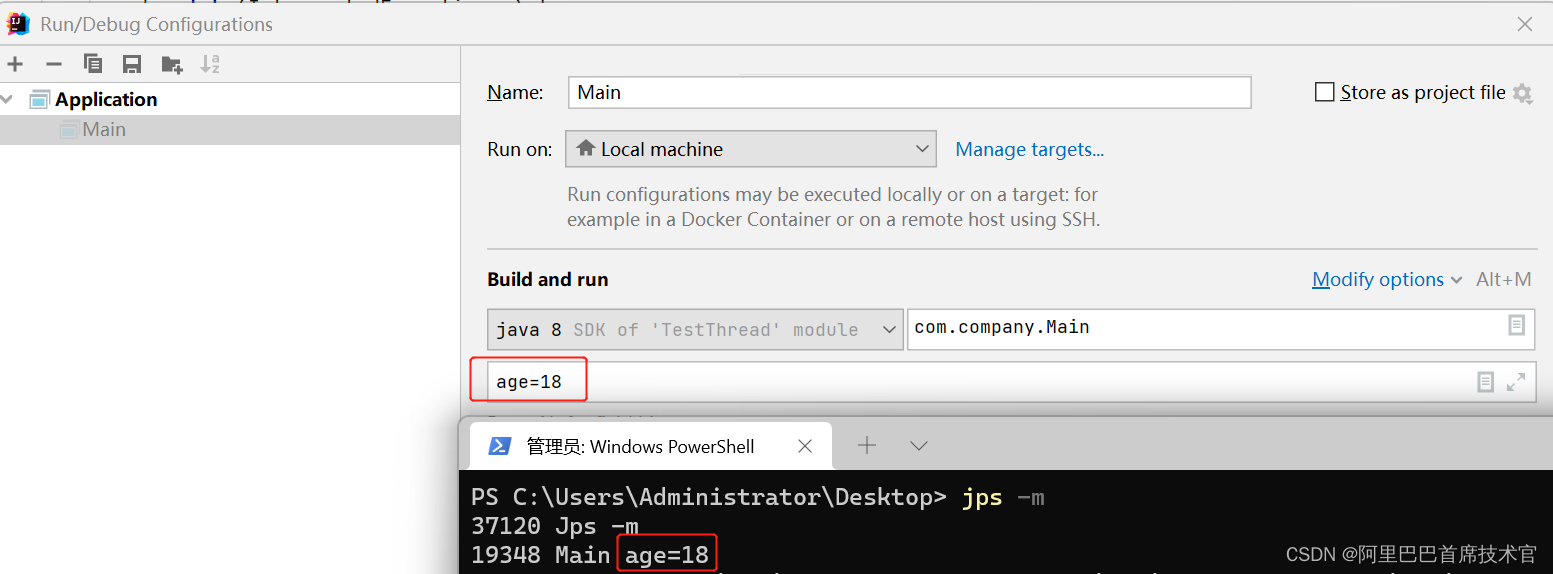
JVM工具之 JPS
分布式计算实验1 负载均衡
data:image/jpg;base64格式数据转化为图片
TCP协议详解
SQL存储过程详解
C语言指针
分布式计算MapReduce | Spark实验