当前位置:网站首页>Web security -- Logical ultra vires
Web security -- Logical ultra vires
2022-07-02 08:27:00 【Defeat of Fujiwara Qianhua】
Attack access control
From the technical point of view, logical ultra vires means that there are defects in access control . The following attacks on access control are logical ultra vires .
Request from client ,Web The application should recognize the following two points :
- Verify user identity
- The confirmation request sequence is proposed by the user
Based on these two points ,web The server decides whether to allow a request to perform a specific operation or access the resources it requests . Access control is an important defense mechanism for applications , Because it is responsible for making these key decisions . If there are defects in visiting Confucius , Attackers can often break through the entire application , Control its management functions and access sensitive data belonging to other users .
Concept
Access control vulnerability : The application allows an attacker to perform an operation that the attacker is not qualified to perform
The differences between various vulnerabilities can actually be attributed to the differences in the way these core vulnerabilities are expressed , And the difference between the skills they need to use .
classification
Access control can be divided into three categories :
- Vertical access control
- Horizontal access control
- Context sensitive access control
Vertical access control allows different users to access different functions of the application . For example, you are CSDN Check out my article , If you don't like it , You can't take my article off the shelf , This is the authority of the administrator . In this case , Applications define ordinary users and administrators through this control
Horizontal access control allows users to access a group of the same type 、 Extremely extensive resources . You are a CSDN user , I am also CSDN user ,, What we can do on this is the same .
Context sensitive access control ensures that it is based on the current state of the application , Restrict user access to only allowed content . For example, in a certain process , Users need to complete multiple stages of operation , Context sensitive access control can prevent users from accessing these stages in a specified order .
If the user can access the functions or resources he does not have permission to access , It means that there are defects in access control , That is, there is a logical ultra vires loophole . There are mainly three types of attacks targeting access control , They correspond to three kinds of access control respectively :
- Vertical permission promotion : A user can perform a function , But the role assigned to him does not have this permission . That is, ordinary users perform the actions of administrators
- Increase the level of authority : A user can view or modify resources of the same level that he is not qualified to view or modify . If you can edit my article
- Business logic loopholes : Users can take advantage of vulnerabilities in the application state machine to gain access to key resources . For example, users can avoid the payment steps in the shopping settlement sequence
actual combat
pikachu The level is beyond authority
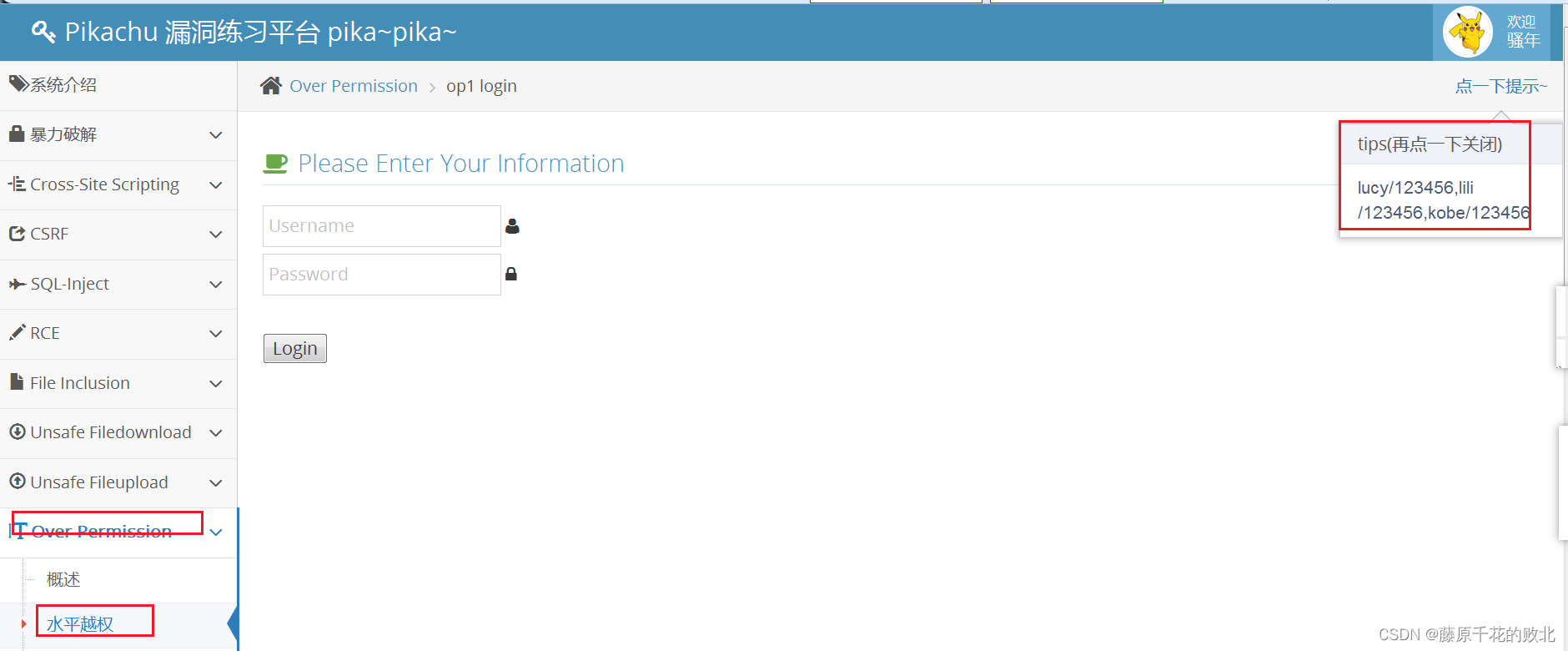
The level is beyond authority , That is to use my account , Check the learning resources of your account . See Tips , A user kobe、lucy.
- Sign in kobe account number

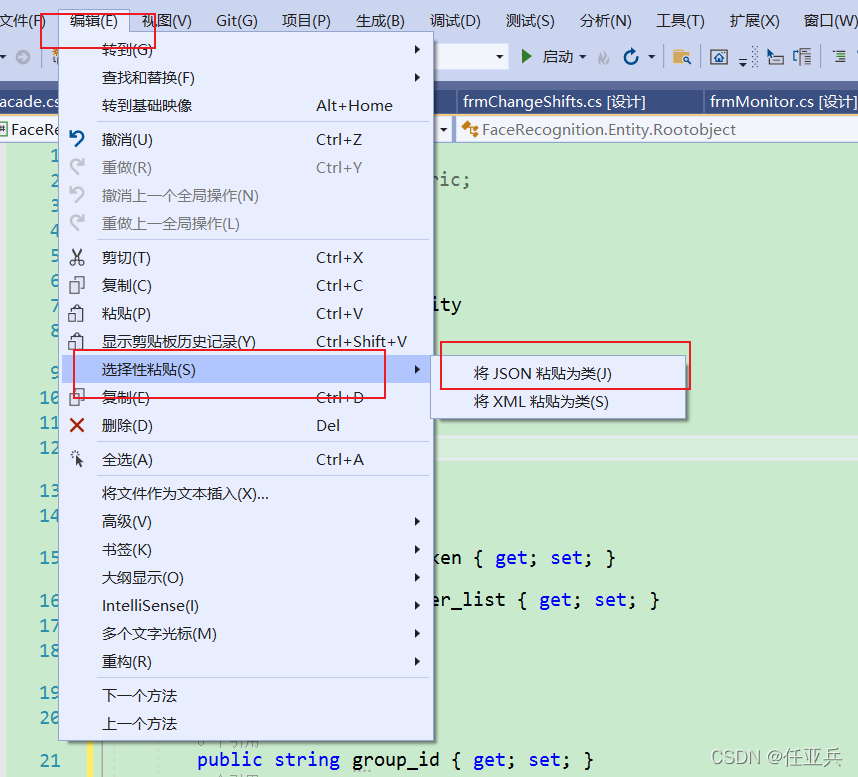
- As shown in the figure above , use burpsuite Grab the bag “ Check the information ”

- take kobe Change it to lucy, return lucy Information about

Reference resources
Almost copy 《 The classic of hacker attack and Defense Technology Web Actual combat 》
边栏推荐
猜你喜欢
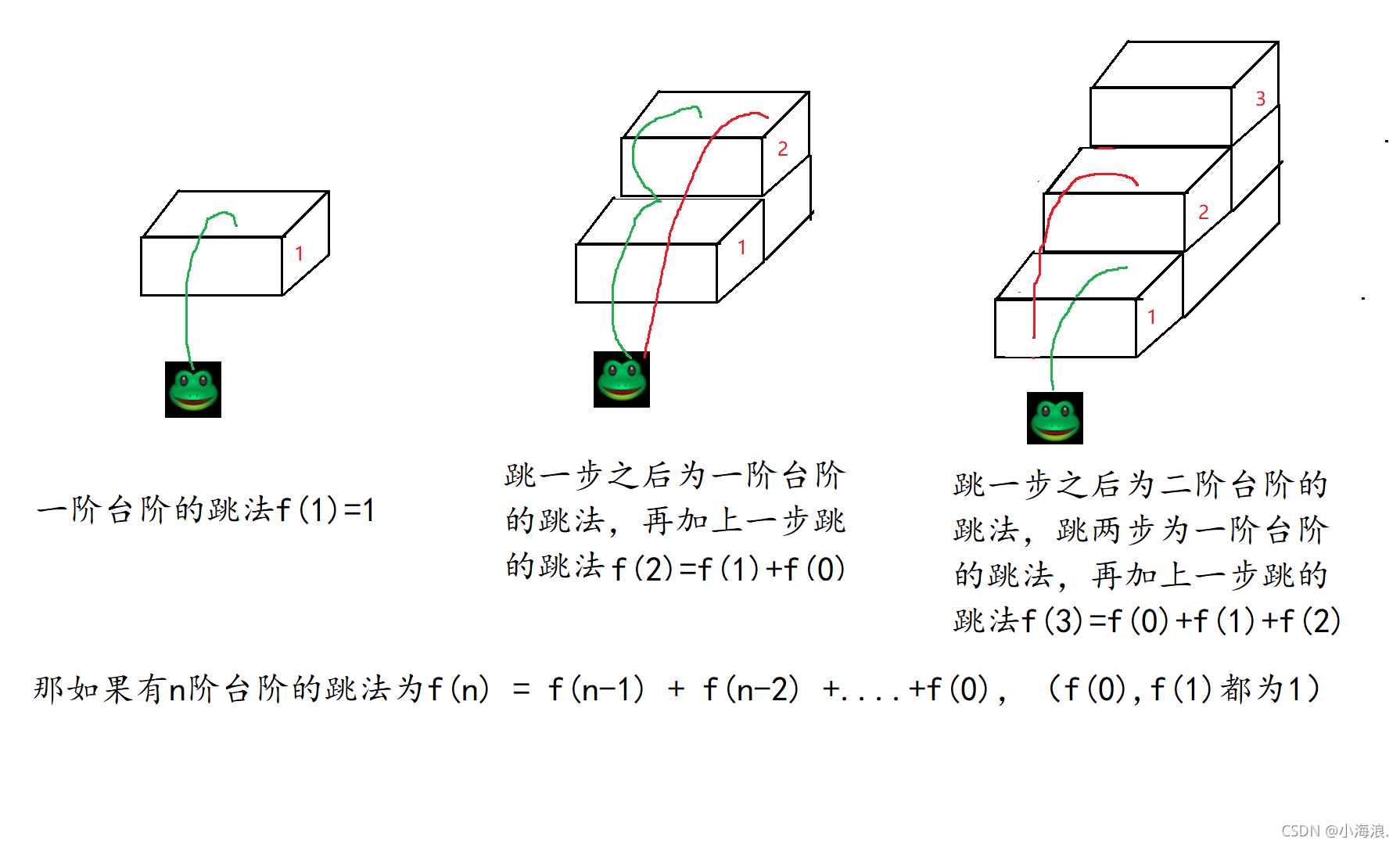
方法递归(斐波那契数列,青蛙跳台阶,汉诺塔问题)

HCIA - application layer
Installation and use of simple packaging tools

Introduction to parameters of CarSim pavement 3D shape file
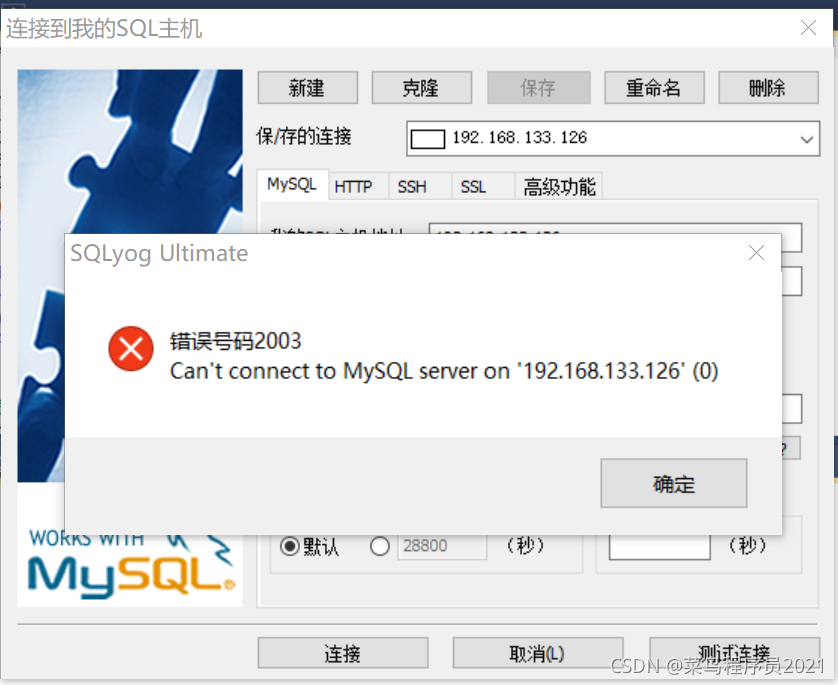
Sqlyog remote connection to MySQL database under centos7 system

c语言自定义类型枚举,联合(枚举的巧妙使用,联合体大小的计算)

Generate database documents with one click, which can be called swagger in the database industry

Don't know mock test yet? An article to familiarize you with mock

ARP及ARP欺骗
Use C language to receive JSON strings
随机推荐
HCIA—應用層
Multi site high availability deployment
深入理解JVM
2022 Heilongjiang latest construction eight members (materialman) simulated examination questions and answers
CarSim learning experience - rough translation 1
The source code of the live app. When the verification method is mailbox verification, the verification code is automatically sent to the entered mailbox
Carsim-路面3D形状文件参数介绍
力扣每日一题刷题总结:二叉树篇(持续更新)
The best blog to explain the basics of compilation (share)
Use of OpenCV 6.4 median filter
力扣方法总结:滑动窗口
Introduction to parameters of CarSim pavement 3D shape file
Animation synchronization of CarSim real-time simulation
乐理基础(简述)
Opencv common method source link (continuous update)
Data reverse attack under federated learning -- gradinversion
c语言将字符串中的空格替换成%20
OpenCV3 6.3 用滤波器进行缩减像素采样
Get the width and height of the screen in real time (adaptive)
2022 Heilongjiang's latest eight member (Safety Officer) simulated test question bank and answers