当前位置:网站首页>To prevent "activation" photos from being muddled through, databao "live detection + face recognition" makes face brushing safer
To prevent "activation" photos from being muddled through, databao "live detection + face recognition" makes face brushing safer
2022-07-01 08:14:00 【? Anita Zhang】
With the development of face recognition technology , More and more commercial applications , Face login 、 Face payment 、 Face lift 、 Face gate, etc , In security 、 Finance 、 education 、 Widely used in medical and other fields , The intelligent and fast face recognition technology has developed rapidly in China .
But face recognition is easy to be photographed 、 video 、 Simulation mold and other ways to muddle through , The public security department has been in Shanghai in recent years 、 Zhejiang 、 anhui 、 Jiangsu and other places found , Several suspect use deep synthesis technology , Illegally stolen or paid for photos and audio “ activation ”、 Synthesize into dynamic video for illegal profit .
“ In vivo detection + Face recognition ” Become a confrontation “ activation ” Photo The key technology
To prevent “ activation ” Your photos muddle through , Data treasure is providing “ Face recognition ” Data service , It provides customers with “ In vivo detection ” Algorithm .
Based on data treasure " In vivo detection " The algorithm can judge the face captured by the camera , Is it a real face or a fake face , Generally, it is used in application scenarios with high security requirements , Can use face recognition + The method of combining living body detection to carry out identity verification , After using in vivo detection , It makes up for the deficiency of single face recognition , Can effectively identify photos 、 video 、 Mask and other fake human faces , Avoid fraud to the greatest extent .
Data treasure as “ Internet +” Trusted authentication platform (CTID platform ) Our first tier partner , Data resources are directly connected to the public security database , After obtaining the user's authorization , By name 、 ID number 、 Portrait photos 、 In vivo detection can verify the authenticity of user identity information in real time . Identity verification as a more secure standard , Data treasure “ Face recognition comparison interface + In vivo detection SDK” The verification process is as follows :
- Portrait information collection
adopt SDK、H5 page 、 Wechat applet and other application scenarios obtain the verified face information 、 ID information , Users upload ID photos , System use certificate OCR Recognition technology automatically extracts information , Users take live video and upload it for comparison and verification .
2. Living determination
By using speech recognition 、 Lip recognition 、 Technologies such as living body judgment automatically detect video , Judge whether you are a real living body and upload the human image in the video with high quality .
3. Public security big data verification
be based on https+MD5 Signature authentication + Symmetric encryption technology will portrait image 、 full name 、 The ID number information is encrypted and transmitted to the interface authorized by the Public Security Bureau , And then automatically connect with the portrait image in the public security big data 、 full name 、 Carry out authoritative comparison and verification of ID number .
4. Output verification results
After the verification of public security big data interface , Return the verification result , If the verification is consistent, it will be approved by default , If not, return to the certification homepage , Let the user re operate .
边栏推荐
- Office365 - how to use stream app to watch offline files at any time
- Provincial election + noi part I dynamic planning DP
- [force deduction 10 days SQL introduction] Day10 control flow
- [getting started] intercepting strings
- [untitled]
- Aardio - 自己构造的getIconHandle的方法
- Codeworks round 803 (Div. 2) VP supplement
- Anddroid 文本合成语音TTS实现
- Provincial selection + noi Part II string
- Aardio - Method of self constructed geticonhandle
猜你喜欢
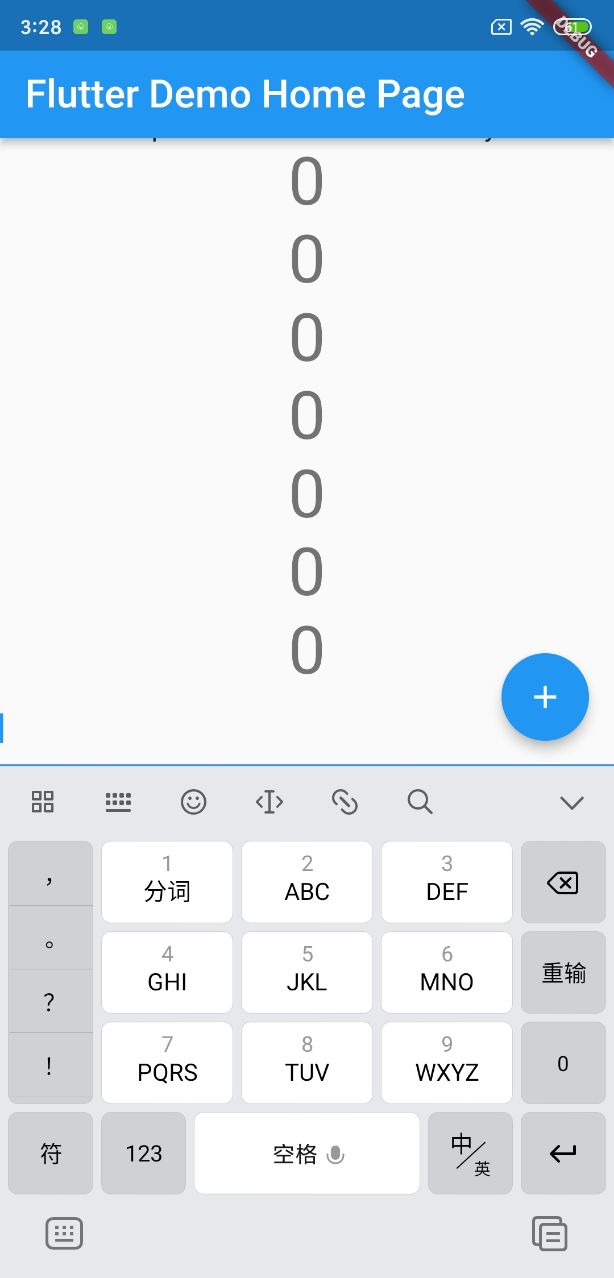
软键盘高度报错

P4 安装bmv2 详细教程

如何使用layui将数据库中的数据以表格的形式展现出来

SQL number injection and character injection

Learn the knowledge you need to know about the communication protocol I2C bus

SharePoint - modify web application authentication using PowerShell

凸印的印刷原理及工艺介绍

Office365 - how to use stream app to watch offline files at any time
![[getting started] intercepting strings](/img/16/363baa4982408f55493057200bcba5.png)
[getting started] intercepting strings

【无标题】
随机推荐
OJ输入输出练习
数字转excel的字符串坐标
EDA开源仿真工具verilator入门6:调试实例
軟鍵盤高度報錯
Provincial election + noi part I dynamic planning DP
[getting started] extract non repeating integers
力扣每日一题-第31天-202.快乐数
Book of quantitative trading - reading notes of the man who conquers the market
Access report realizes subtotal function
力扣每日一题-第32天-1822.数组元素积的符号
Two expressions of string
Soft keyboard height error
凸印的印刷原理及工艺介绍
XX attack - reflective XSS attack hijacking user browser
String coordinates of number to excel
Airsim雷达相机融合生成彩色点云
Serial port oscilloscope software ns-scope
When using charts to display data, the time field in the database is repeated. How to display the value at this time?
Learn the knowledge you need to know about the communication protocol I2C bus
Aardio - Shadow Gradient Text