当前位置:网站首页>buffer overflow protection
buffer overflow protection
2022-07-07 14:49:00 【fpcc】
One 、 Memory safety
c/c++ One of the key issues criticized by satiety is the security of memory , A typical example is memory out of bounds . stay c/c++ in , It does not check memory out of bounds , Like an array , The programmer can still use the pointer that has crossed its bounds . But once used up, release , The program will crash fall . out of buffer (buffer overflow), It is aimed at program design flaws or application defects of the language itself , Write data that can overflow the buffer to the data buffer of the program ( That is, the memory mentioned above is out of bounds ), Cause the program to run abnormally, so as to obtain the control of the program and even the system .
Have you noticed OpenSSL Provided in SM2 Buffer overflow vulnerability in the algorithm , This vulnerability can allow illegal users to get more data, leading to program denial of service or change the behavior of the program . If you are interested, you can search online . Not only the buffer vulnerability of this software , Historically , Basically, all well-known software has encountered this security problem more or less , On some white hat forums , These questions are often raised .
Memory problems , As a result, the security problems of the whole program emerge in endlessly , As big as Microsoft 、 Google and other large companies , As small as some individual developers , Failure of memory management , This kind of memory security problem is often caused or triggered . Generally speaking , Memory is the buffer to put data , So the memory security problem is also called buffer overflow problem .
Two 、 Buffer overflow protection
that , Since buffer overflow is so important , This has become an important issue of computer security . Generally speaking , Computer memory is divided into heap and stack ( Registers and the like are not considered for the time being ). The buffer security of the program can be protected from the level of software writing 、 Compilation level 、 Protection at the operation level ; At the operational level, it can be divided into OS The protection of the system and the protection of the application itself .
1、 Language level security control
a、 When writing a program , Pay attention to checking and controlling the length of the array 、 Pointer size and other boundary control , That is, integrity inspection .
b、 Use some safe libraries to replace the original arrays and pointers .
c、 Add security control code .
d、 Use the memory static checking tool
2、 Compile level security control
a、 Use development tools that support compile time memory checking, such as visual studio, Yes by default GS Options ,GCC A similar mechanism is provided .
b、 Boundary check during compilation .
c、 Stack mark control , Used to manage the location in memory .
d、 Use the runtime memory detection tool .
3、 Security control during operation
a、 Preventive memory security control in operating system , Such as accessing illegal addresses .
b、 Security check of memory and data , Including cross-border management .
c、 Sandbox hosting operation .
Here we talk about adding marker bits in memory to control buffer overflow , There are generally three ways , One is to add the ending character , such as C/C++ Medium \0 character ; One is to randomly distribute some control characters in memory, such as canary ; Finally, do XOR .
3、 ... and 、 application
In practical applications ,GNU Compiler Collection、LLVM、Microsoft Visual Studio also Intel、IBM And other compilers support security checks at compile time . Of course, there are static tools that can check memory problems during the coding phase, such as Lint etc. , In the run-time, the general operating system provides memory security control , For example, set some symbolic checks on the stack space , Protect the stack from being overwritten . stay Linux On , There are similar behaviors called canary.
and StackGhost It is to protect from the level of hardware , This is relatively rare . So let's see Linux How to check memory security in :
1、CANNARY( Stack protection )
gcc stay 4.2 Version with -fstack-protector and -fstack-protector-all Compile parameters to support stack protection ,4.9 Added -fstack-protector-strong Compiling parameters makes the scope of protection wider .
2、FORTIFY
Using parameter -U_FORTIFY_SOURCE Compile to protect buffer overflow .
3、NX(DEP)
Default on , In case of overflow , Automatically throw an exception , Instead of executing .
4、PIE(ASLR)
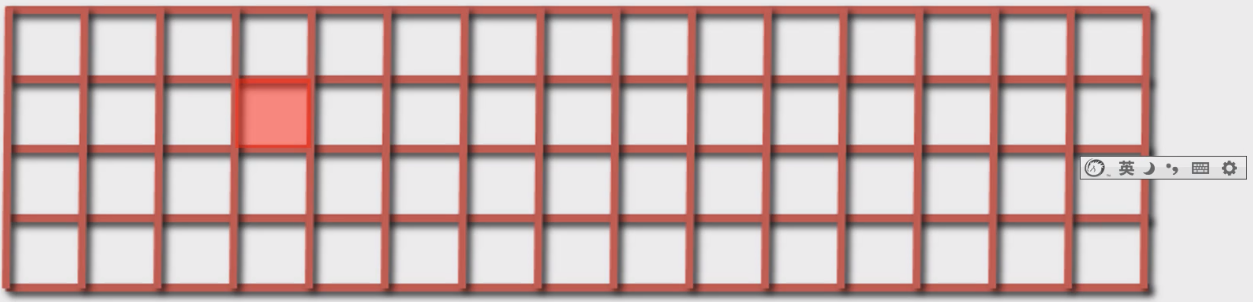
Memory address randomization mechanism (address space layout randomization), It is divided into images 、 Stack and PEB And TEB Randomize three .
5、RELRO
Set the symbol redirection table to read-only or parse and bind all dynamic symbols when the program starts , So as to reduce the right to GOT(Global Offset Table) attack .GOT You can take a look at the loading related content of the dynamic library .
Four 、 summary
Here's an explanation , This article will not teach you how to do buffer overflow, let alone how to attack , That's illegal . If anyone wants to learn safety knowledge , You can go to see snow and other safe websites to learn . This article focuses on how to protect the security of memory . Now the problem of computer security has risen to the national level , There is a vague shadow of hackers behind the war between Russia and Ukraine . The program is big , More people are involved in programming , People's programming level and ability are uneven, as well as their awareness and attention to security issues , All determine the overall safety of the program . Buffer overflow is a security problem that comes with the emergence of computers , It is almost essential , Speaking of this , Just remind me , A good programmer , You must have a deep understanding of the memory model of the language , Operating system memory management mechanism and program compilation and operation mechanism, etc . It can be said that there is one unexpected , It means that problems may occur , It depends on the price .
A thousand Li dike , Collapse in ant nest ! It's not alarmist .
边栏推荐
- Reading and understanding of eventbus source code
- Delete a whole page in word
- Pandora IOT development board learning (HAL Library) - Experiment 12 RTC real-time clock experiment (learning notes)
- PLC: automatically correct the data set noise, wash the data set | ICLR 2021 spotlight
- 多商戶商城系統功能拆解01講-產品架構
- Cocos creator direction and angle conversion
- JSON解析实例(Qt含源码)
- 属性关键字ServerOnly,SqlColumnNumber,SqlComputeCode,SqlComputed
- "July 2022" Wukong editor update record
- 寺岗电子称修改IP简易步骤
猜你喜欢
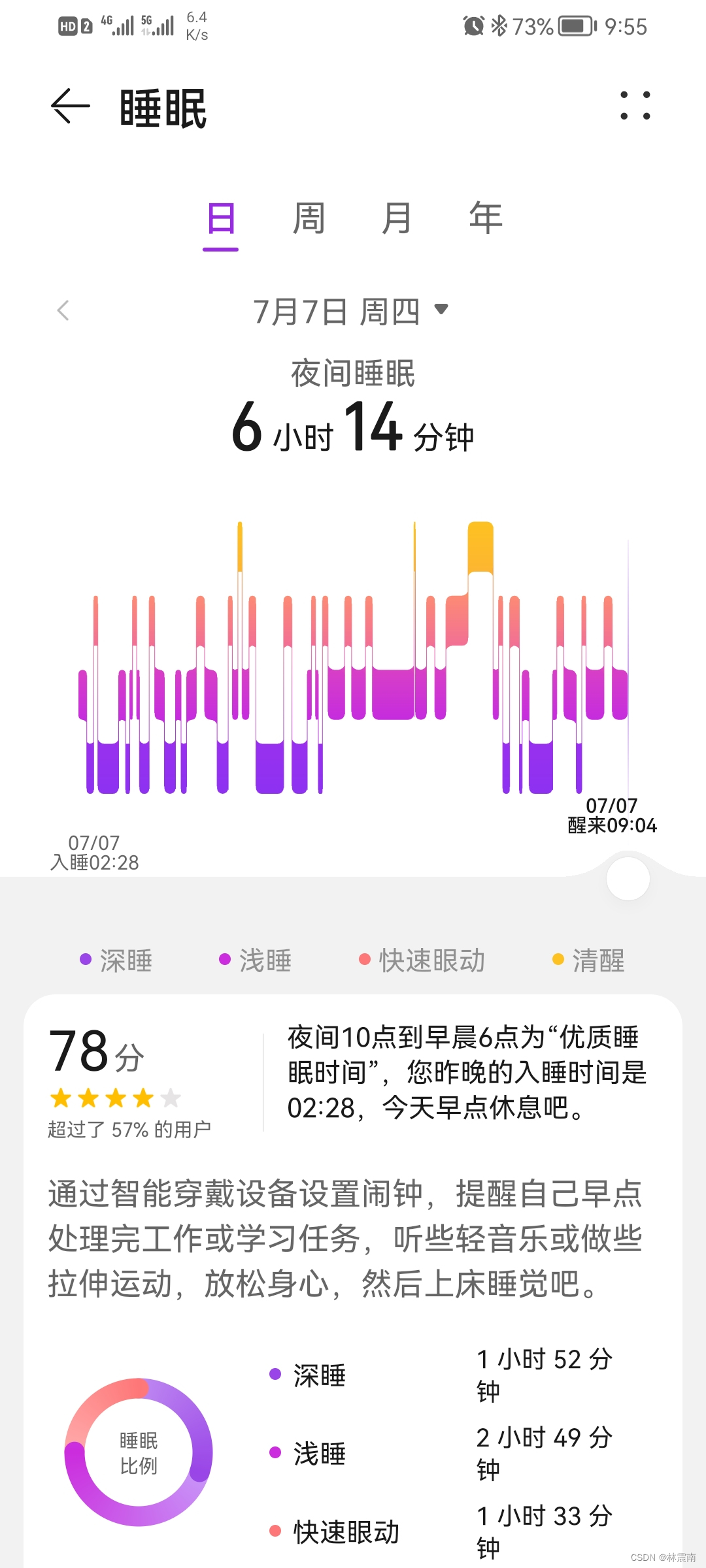
Today's sleep quality record 78 points
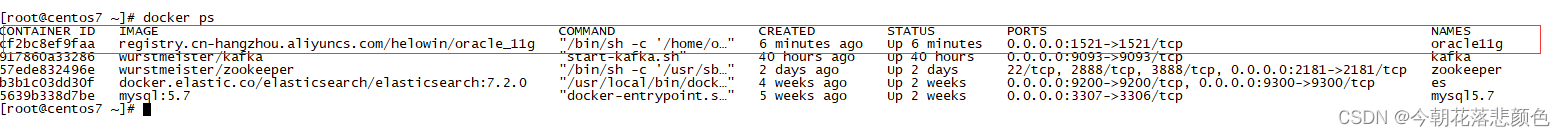
Docker deploy Oracle
Navigation - are you sure you want to take a look at such an easy-to-use navigation framework?

GAN发明者Ian Goodfellow正式加入DeepMind,任Research Scientist

「2022年7月」WuKong编辑器更版记录
【愚公系列】2022年7月 Go教学课程 005-变量
![[server data recovery] a case of RAID data recovery of a brand StorageWorks server](/img/8c/77f0cbea54730de36ce7b625308d2f.png)
[server data recovery] a case of RAID data recovery of a brand StorageWorks server
WebRTC 音频抗弱网技术(上)
![leetcode:648. Word replacement [dictionary tree board + find the shortest matching prefix among several prefixes]](/img/3e/cdde4b436821af8700eb65d35e8f59.png)
leetcode:648. Word replacement [dictionary tree board + find the shortest matching prefix among several prefixes]

Equipment failure prediction machine failure early warning mechanical equipment vibration monitoring machine failure early warning CNC vibration wireless monitoring equipment abnormal early warning
随机推荐
属性关键字ServerOnly,SqlColumnNumber,SqlComputeCode,SqlComputed
#yyds干货盘点# 解决名企真题:交叉线
Stm32cubemx, 68 sets of components, following 10 open source protocols
AWS学习笔记(三)
缓冲区溢出保护
2022 cloud consulting technology series high availability special sharing meeting
安恒堡垒机如何启用Radius双因素/双因子(2FA)身份认证
Leetcode - Sword finger offer 05 Replace spaces
PD virtual machine tutorial: how to set the available shortcut keys in the parallelsdesktop virtual machine?
Small game design framework
How bad can a programmer be? Nima, they are all talents
一款你不容错过的Laravel后台管理扩展包 —— Voyager
Ffmpeg --- image processing
Navigation - are you sure you want to take a look at such an easy-to-use navigation framework?
潘多拉 IOT 开发板学习(HAL 库)—— 实验12 RTC实时时钟实验(学习笔记)
防火墙基础之服务器区的防护策略
Es log error appreciation -maximum shards open
Notes de l'imprimante substance: paramètres pour les affichages Multi - écrans et multi - Résolutions
Demis Hassabis谈AlphaFold未来目标
智汀不用Home Assistant让小米智能家居接入HomeKit