当前位置:网站首页>Different operating with different locks, rounding
Different operating with different locks, rounding
2022-08-01 20:00:00 【dog studying hard】
- A read operation performed by a transaction using MVCC is called a consistent read (or snapshot read).All ordinary SELECT statements are snapshot reads under the RC (read committed) and RR (repeatable read) isolation levels. Consistent reads will not lock any records in the table, and other transactions can freely access the table.Make changes to records in
select * from table_nameselect * from table_name t1 Inner Join table_name_name t2 on t2.id = t1.id- The lock read of the shared lock, if the current transaction executes the lock read, then the S lock (shared) will be added, and other transactions can continue to obtain the S lock of these records, but cannot obtain these records.The X lock cannot directly change these records.If other transactions want to acquire the corresponding X lock, they will be blocked and wait until the current transaction's S lock is released
select * from table_name LOCK IN SHARE MODE- Exclusive lock lock read, if the statement is executed, X lock will be added to the record, other transactions cannot obtain the S lock of these records, nor can they obtain the X lock of these records, direct modification of these records is not allowed.If other transactions want to acquire the corresponding X lock or, they will be blocked until the corresponding record X lock is released after the current transaction is committed.
SELECT * FROM UPDATE - DELETE operation: The process of performing a DELETE operation on a record is actually to first locate the position of the record in the B+ tree, then acquire the X lock of this record, and then perform the DELETE Mark operation (It can be simply understood as a lock read that acquires an X lock)
- UPDATE operation: UPDATE operation on a record is divided into 3 cases
- If the key value of the record has not been modified and the storage space occupied by the updated column has not changed before and after the modification, locate in the B+ tree firstGo to the location of this record, then obtain the X lock of the record, and finally modify it at the location of the original record.(The process of locating the record to be modified in the B+ tree first, and then acquiring the X lock of the record can be regarded as a lock read that acquires the X lock)
- If the key value of the record has not been modified and the storage space occupied by at least one updated column has changed before and after modification, locate this record in the B+ tree first.The location of the record, then obtain the X lock of the record, then delete the record completely (move the record into the garbage list completely), and finally insert a new record.(First locate the record to be modified and then the position in the B+ tree, and then then acquire the X lock of the record. It can be seen as a locked read that acquires the X lock, strong>The lock on the record associated with the completely deleted record will also be transferred to the newly inserted record)
- If the key value of the record is modified, it is equivalent to performing an INSERT operation after the DELETE operation on the original record, and the locking operation needs to be performed according to the rules of DELETE and INSETR
- INSERT operation: Under normal circumstances, a newly inserted record is protected by an implicit lock, and there is no need to generate a corresponding lock structure for it in memory.
边栏推荐
- WhatsApp群发实战分享——WhatsApp Business API账号
- 9月备考PMP,应该从哪里备考?
- BN BatchNorm + BatchNorm的替代新方法KNConvNets
- Compse编排微服务实战
- 使用Huggingface在矩池云快速加载预训练模型和数据集
- 手撸代码,Redis发布订阅机制实现
- 部署zabbix
- 58: Chapter 5: Develop admin management services: 11: Develop [admin face login, interface]; (not measured) (using Ali AI face recognition) (demonstrated, using RestTemplate to implement interface cal
- Redis 做网页UV统计
- latex论文神器--服务器部署overleaf
猜你喜欢
![58: Chapter 5: Develop admin management services: 11: Develop [admin face login, interface]; (not measured) (using Ali AI face recognition) (demonstrated, using RestTemplate to implement interface cal](/img/ab/1c0adeb344329e28010b6ffda5389d.png)
58: Chapter 5: Develop admin management services: 11: Develop [admin face login, interface]; (not measured) (using Ali AI face recognition) (demonstrated, using RestTemplate to implement interface cal
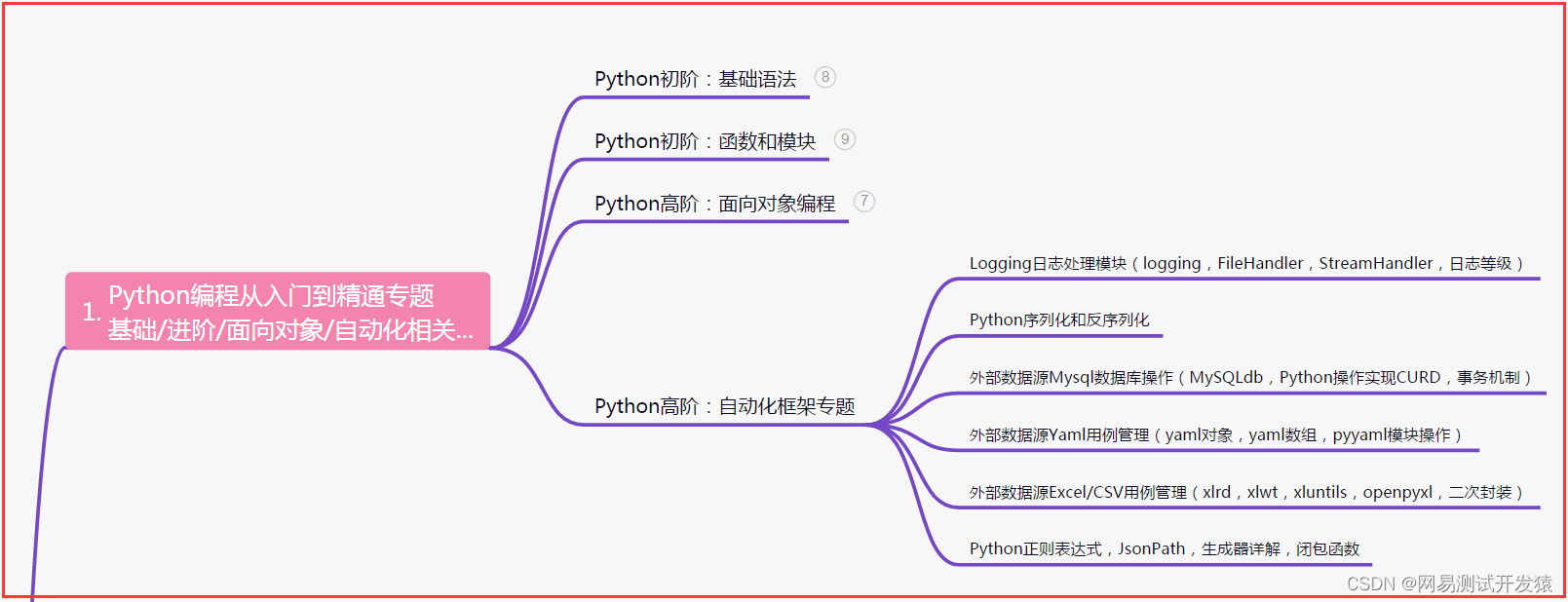
From ordinary advanced to excellent test/development programmer, all the way through

安装win32gui失败,解决问题

【多任务学习】Modeling Task Relationships in Multi-task Learning with Multi-gate Mixture-of-Experts KDD18

【多任务优化】DWA、DTP、Gradnorm(CVPR 2019、ECCV 2018、 ICML 2018)

openresty 动态黑白名单
【无标题】
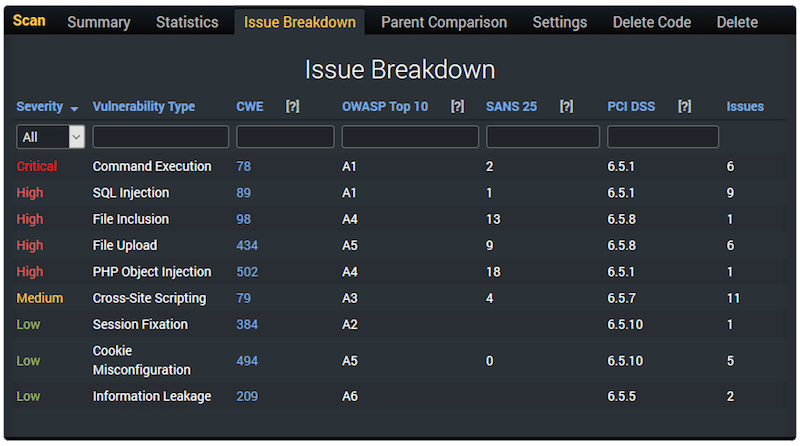
10 个 PHP 代码安全漏洞扫描程序

面试突击70:什么是粘包和半包?怎么解决?
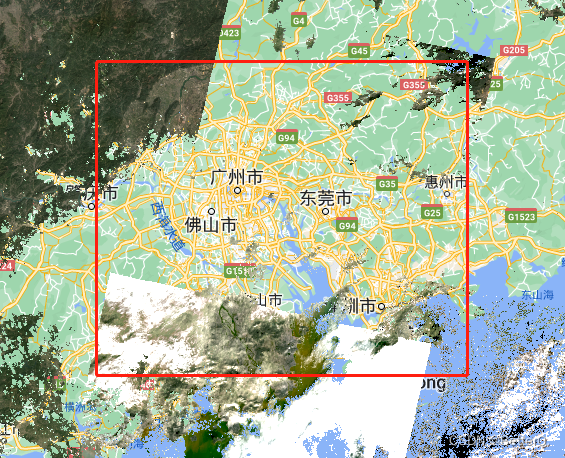
GEE(8):使用MODIS填补由去云后的Landsat影像计算得到的NDVI数据
随机推荐
JS数组过滤
Does LabVIEW really close the COM port using VISA Close?
使用Huggingface在矩池云快速加载预训练模型和数据集
PHP 安全最佳实践
正则表达式
Pytorch模型训练实用教程学习笔记:三、损失函数汇总
大整数相加,相减,相乘,大整数与普通整数的相乘,相除
【nn.Parameter()】生成和为什么要初始化
openresty 动态黑白名单
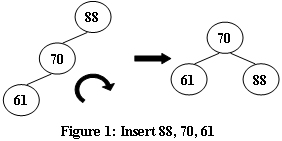
Determine a binary tree given inorder traversal and another traversal method
第59章 ApplicationPart内置依赖注入中间件
第60章 ApplicationPart自动集成整体性和独立性插件项
deploy zabbix
用户体验好的Button,在手机上不应该有Hover态
面试突击70:什么是粘包和半包?怎么解决?
第56章 业务逻辑之物流/配送实体定义
终于有人把AB实验讲明白了
nacos安装与配置
【kali-信息收集】(1.4)识别活跃的主机/查看打开的端口:Nmap(网络映射器工具)
部署zabbix