当前位置:网站首页>Heavy cover special | intercept 99% malicious traffic, reveal WAF offensive and defensive drills best practices
Heavy cover special | intercept 99% malicious traffic, reveal WAF offensive and defensive drills best practices
2022-08-01 19:02:00 【Tencent Cloud Security Center】
If the major events are guaranteed before“安全加固”Work likened to“防御工事”的构建,How to build and reinforce layers、A combined defense line that can be combined,It is the top priority for effective defense.
安全“防御工事”The builds are available from the web、边界、Start at all levels such as the host,Deploy complete security tools to reinforce defense lines,and through the Cloud Security Center、Threat intelligence, etc. to achieve a secure one-stop linkage control,As well as functional interoperability and data collaboration.
In the last article we talked about best practices for building the first line of defense,In this article we focus on how to protect the coreWebApp security deployment,In-depth analysis of offensive and defensive drillsWebBest practices for application protection.
知攻懂防,First find out the blue army attack method
一般来说,There is only time left for the Blues in the offense-defense drill scenario2-3周,And need to attack multiple targets at the same time,This also determines that the attacking characteristics of the Blue Army are often faster、更准、更狠,They tend to utilize a plethora of automated tools、商业化IPProxy tools to detect and bypass,For exposed assets、The service quickly attacked.
常见的WebThere are several types of application attack methods:
- 分布式扫描器:Use distributed scanners to frequently change attack sourcesIP,from a free agent、IDC、VPS 、Internet toll proxy、再到 4g 基站、物联网、家宽、秒拨IP、Cloud function proxy、serverless代理、worker 代理等等,By transforming a huge number of sourcesIPContinuous scanning attacks on services,Routine discovery1个IPban1个IPThe response measures are often delayed.
- API Fuzzer:利用Fuzzer 对业务的APICarry out risk detection,Including but not limited to permission vulnerability discovery、Business logic vulnerability discovery、Weaknesses in security measures are found and bypassed、用户遍历、数据遍历等Web Weak point of protection,Attack sniffing, which requires tools to quickly find such non-basic security vulnerabilities of attackers、尝试.
- Malicious terminal connectors that can obfuscate traffic:The traditional landing is through file uploadWebshellOr the malicious backdoor that needs to persist in the form of a file on the target server gradually fails,The attack difficulty gradually increases,Attackers are starting to use fileless memorywebshell进行攻击.
由点及面,Then analyze the status quo of application security governance
With the continuous exploration and wide application of cloud computing technology in the industry,More enterprises have begun to implement cloud-native architecture transformation to improve the overall resource utilization efficiency of the enterprise,实现降本增效.与此同时,The boundaries of application security governance and the key issues that need to be addressed also vary:
- Open source software is widely used:There are more and more applications of open source software,The resulting open source software vulnerabilities have also increased,如:Log4j2、shiro、fastjson ……
- Cloud-native environment changes:The cloud-native environment brings convenience at the same time,It also brings about the problem of environment configuration,There are application security risk items that occur due to improper environment configuration,如:容器逃逸、API配置不当、file resides、命令执行……
- App security is gradually shifted to the left:In the process of security operations governance,will join fromSAST、DAST、IASTand other related safe left shift capabilities.Although the convergence of basic security vulnerabilities.But it will inevitably bring the attacker's sight to the business/Combined with data security,如:业务逻辑、API问题、越权……
- 多端接入:Client access methods are more variable,It also leads to multiple clients accessing the same service at the same time.It will cause protection granularity on different ends/The phenomenon of inconsistent treatment strategies appears,It is also easy to be targeted by attackers for disguise.
- Traffic attacks increase:Business traffic attacks increase,如:CC攻击流量、多源低频CC、BOT爬虫、Sniper Bot ,Fuzzer……Increased security operating costs,Security operational rules require rapid update iterations to address attacker countermeasures.
Armed for the situation,全方位保护Web应用安全
Combined with the actual governance difficulties,Tencent Security summarizes the following breakthroughs in application security governance,For corporate defense team reference:
- 注重WebAttack identification and defense,如 OWASP 定义的十大 Web 安全威胁攻击
- 结合 0day 漏洞虚拟补丁,Protection against emergency vulnerabilities
- Multi-terminal access security control,And configure fine-grained disposal policies
- Pay attention to business terminals、Abnormal identification of accounts,Combine intelligence to discover and block malicious access to sources
- 通过BOTBehavior management realizes rapid perception of malicious traffic and automatic evolution of disposal strategies,automated confrontationBOT及CC攻击
而腾讯WebApplication Firewall is based on AI的一站式Web业务运营风险防护方案,沉淀了腾讯20多年业务安全运营及黑灰产对抗经验,can be efficiently improvedWebApply safety guard water level,Combined with client risk identification、Inbound threat intelligence、Big data analysis and other capabilities systematically combat malicious traffic from multiple dimensions and at multiple levels,拦截率99%以上.
使用腾讯WebUsers of the application firewall can pass the following6Check yourself for best practice stepsWeb安全防护配置,Ensure that effective security protections are enabled while converging security risks:
其中,BOTProtection is forWebAn effective means of special governance for business assets,In the configuration process, we can pay attention to the following points:
- Enable client risk identification:Configure protection paths to implement site-wide protection,Turn on automated tool recognition、Page anti-debugging switch,and enable block mode.
- Configure the intelligent analysis module:Open the threat intelligence module,Configure smart statistics and set to loose mode,Configure action settings and set relatively tight score ranges and take actions.
- 配置会话管理:Custom policies support intercepting abnormal access sources,如BOT机器人、代理、IDC、网络攻击、扫描器、Account takeover, etc;Support interception of abnormal clients,Such as games or TV terminals, 公开BOT类型, 未公开BOT类型, 自动化工具, Unknown type, etc;Supports interception of exception parametersFuzz、Intercept abnormal access rate and abnormal access duration、拦截 FakeUA Abuse of reptiles、拦截 Referer 滥用、拦截 未登录用户、Intercept directory scanners, etc.
以上是我们在攻防演练期间针对Web应用防护的治理思考和最佳实践,欢迎关注服务号持续交流.
边栏推荐
- XML配置
- 暑假第一周总结博客
- MySQL数据库————流程控制
- 生命周期和作用域
- Choosing the right DevOps tool starts with understanding DevOps
- LeetCode 0152. 乘积最大子数组:dp + 原地滚动
- ExcelPatternTool: Excel表格-数据库互导工具
- Become a Contributor in 30 minutes | How to participate in OpenHarmony's open source contributions in multiple ways?
- 【LeetCode】Day109-the longest palindrome string
- C#/VB.NET: extracted from the PDF document all form
猜你喜欢
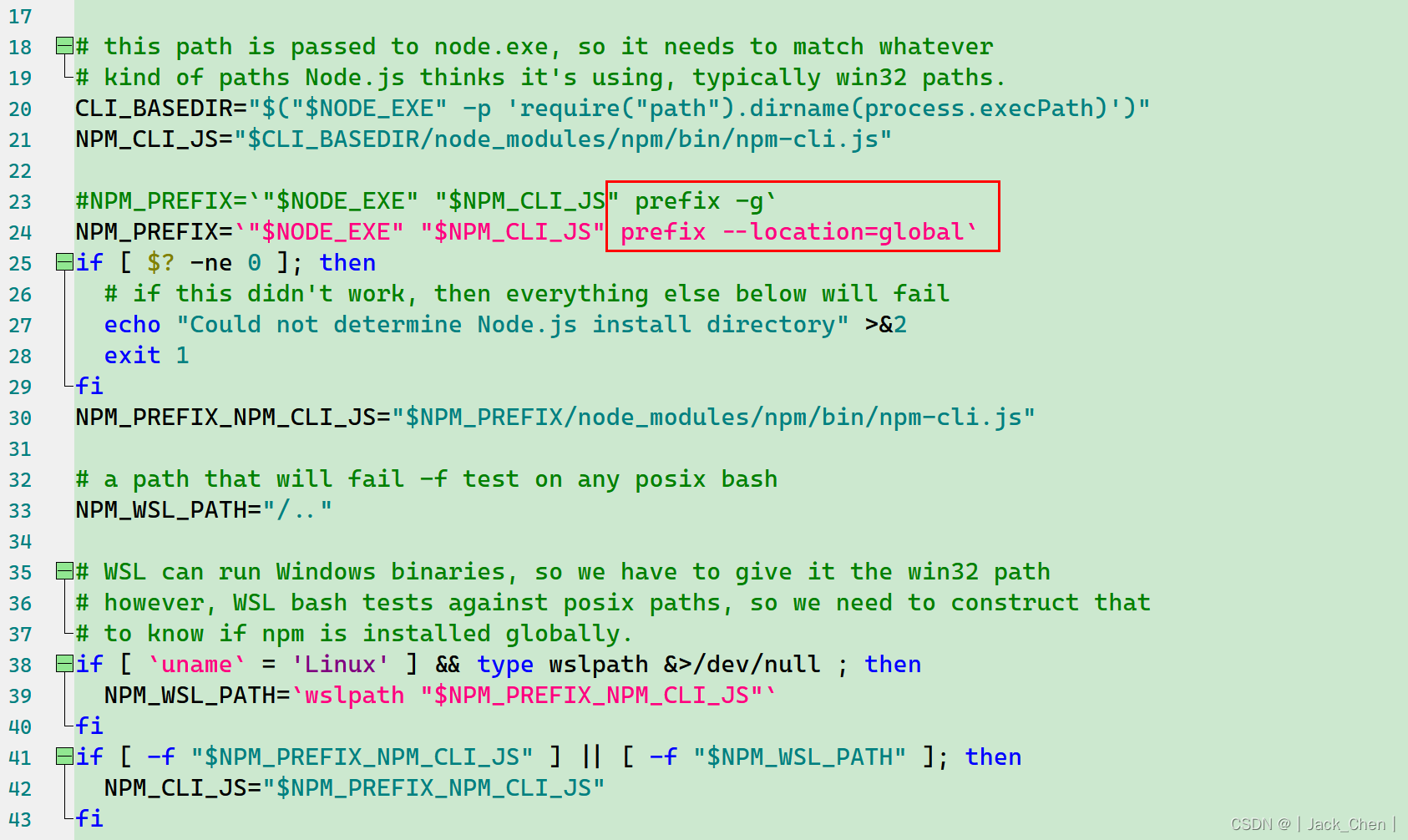
三种方案解决:npm WARN config global --global, --local are deprecated. Use --location=global instead.

How to install voice pack in Win11?Win11 Voice Pack Installation Tutorial

明尼苏达大学团队结合高通量实验与机器学习,实现有效可预测的特定位点重组过程,可调节基因编辑速度
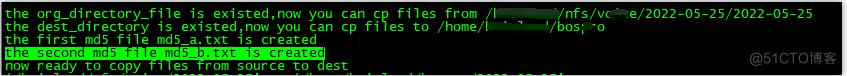
Shell script topic (07): file from cfs to bos
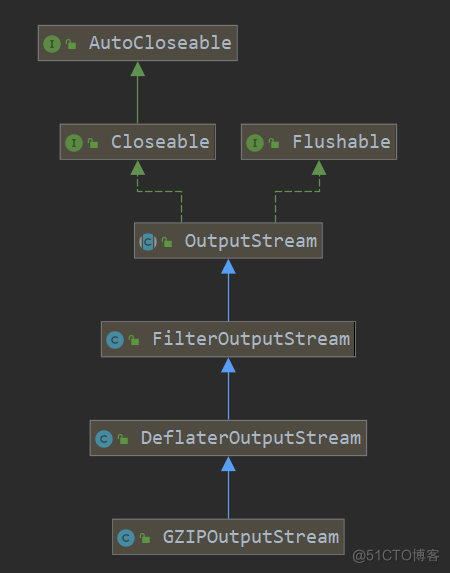
Source code analysis of GZIPOutputStream class

屏:全贴合工艺之GFF、OGS、Oncell、Incell

Screen: GFF, OGS, Oncell, Incell of full lamination process
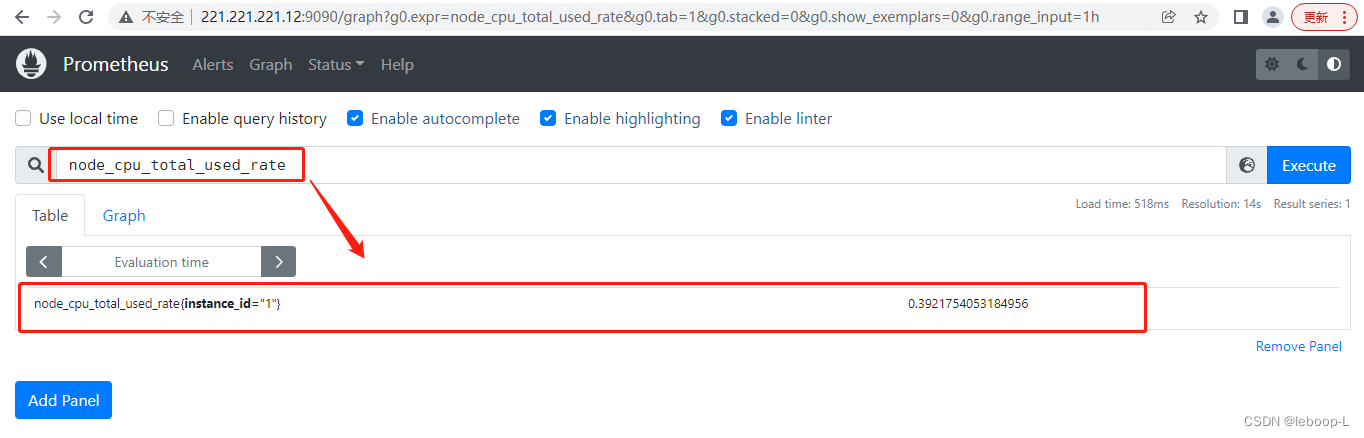
Prometheus's Recording rules practice

Fuzzy query in Map pass-by-value and object pass-by-value
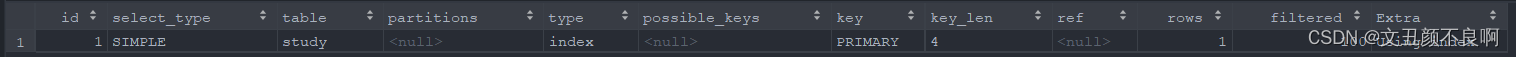
explain 各字段介绍
随机推荐
Industry Salon Phase II丨How to enable chemical companies to reduce costs and increase efficiency through supply chain digital business collaboration?
【服务器数据恢复】服务器Raid5阵列mdisk组中多块磁盘离线的数据恢复案例
Library website construction source code sharing
Keras deep learning practice - traffic sign recognition
odoo+物联网
COS User Practice Call for Papers
XML配置
面试必问的HashCode技术内幕
How to make the fixed-point monitoring equipment display the geographic location on the EasyCVR platform GIS electronic map?
Clip-on multimeter use method, how to measure the voltage, current, resistance?
kubernetes-部署nfs存储类
SaaS管理系统的应用优势在哪里?如何高效提升食品制造业数智化发展水平?
安徽建筑大学&杭州电子科技大学|基于机器学习方法的建筑可再生能源优化控制
Prometheus的Recording rules实践
Screen: GFF, OGS, Oncell, Incell of full lamination process
WinRAR | 将多个安装程序生成一个安装程序
ExcelPatternTool: Excel form-database mutual import tool
英国伦敦大学|眼科强化学习:潜在应用和实施挑战
GZIPOutputStream 类源码分析
LeetCode 0151.颠倒字符串中的单词