当前位置:网站首页>Find the maximum inscribed circle of the contour
Find the maximum inscribed circle of the contour
2022-07-02 14:36:00 【thequitesunshine007】
1 Principle introduction
1.1 The whole principle
For binary images S Some outline of C for . Every pixel in the image Point(col, row),col<S.cols, row<S.rows.
Calculation Every Point(col, row) To contour C Distance of , Then store each distance value in ⼀ And the original image ruler ⼨ same Mat In the object , This Mat Every element of an object is ⼀ Distance value . Calculate all Point(col, row) To contour C After the distance value of , Get the most ⼤ And the corresponding point coordinates , This distance value is the radius of the maximum inscribed circle , Point coordinates (col, row) Is the center of the largest inscribed circle . Then we can pass through the circle ⼼ And the radius will be the most ⼤ The inscribed circle is drawn .
1.2 Point polygon detection pointPolygonTest explain
/** @brief Conduct contour point test .
This function determines that the point is within the contour 、 Outside , Or on the edge ( Or coincide with a vertex ). It returns positive ( Inside ), negative ( Outside ), Or zero ( edge )
When measureDist=false when , The return values are +1,-1 and 0.
otherwise , The return value is the nearest symbolic distance between the point and the nearest contour edge ( Distinguish between positive and negative values ).
@param InputArray Enter the profile .
@param pt spot .
@param measureDist If it is true ÿ
边栏推荐
- ONNX+TensorRT:将预处理操作写入ONNX并完成TRT部署
- Certik released the defi security report in 2021, disclosing key data of industry development (PDF download link attached)
- Default slot, named slot, scope slot
- <口算练习机 方案开发原理图>口算练习机/口算宝/儿童数学宝/儿童计算器 LCD液晶显示驱动IC-VK1621B,提供技术支持
- 4、数组指针和指针数组
- fatal: unsafe repository is owned by someone else 的解决方法
- Methods of software testing
- threejs的控制器 立方体空间 基本控制器+惯性控制+飞行控制
- What is erdma? Popular science cartoon illustration
- The evolution process of the correct implementation principle of redis distributed lock and the summary of redison's actual combat
猜你喜欢
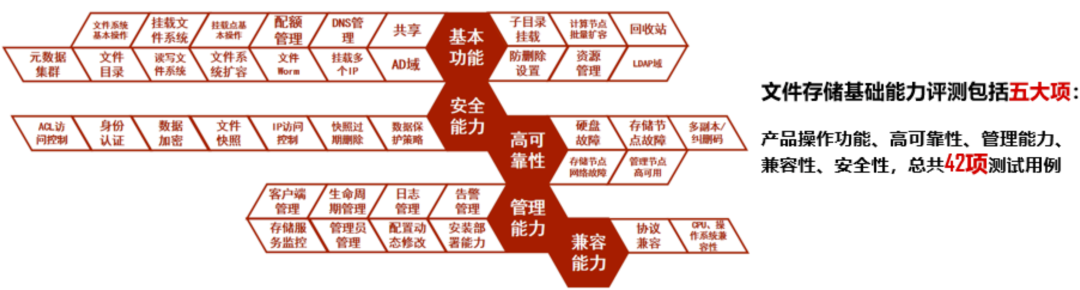
Tencent cloud tstor unified storage passed the evaluation of the first batch of basic file storage capabilities of the ICT Institute
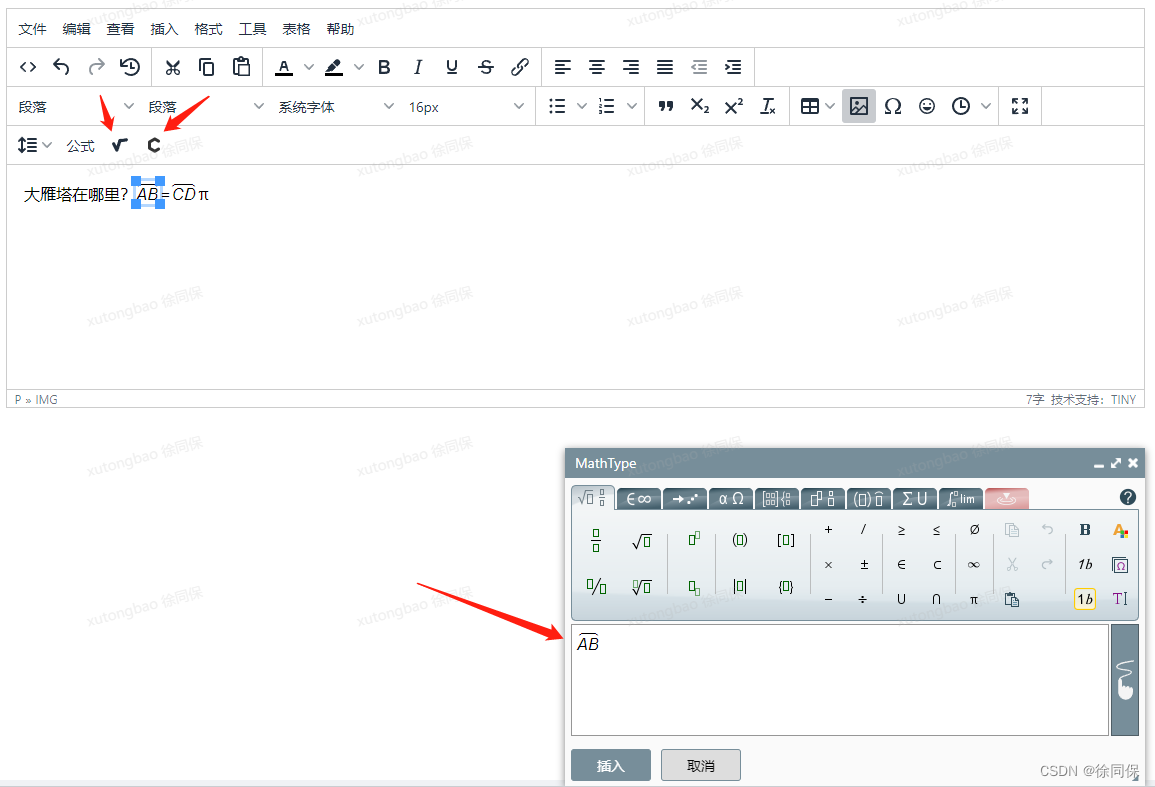
富文本编辑器添加矢量公式(MathType for TinyMCE ,可视化添加)
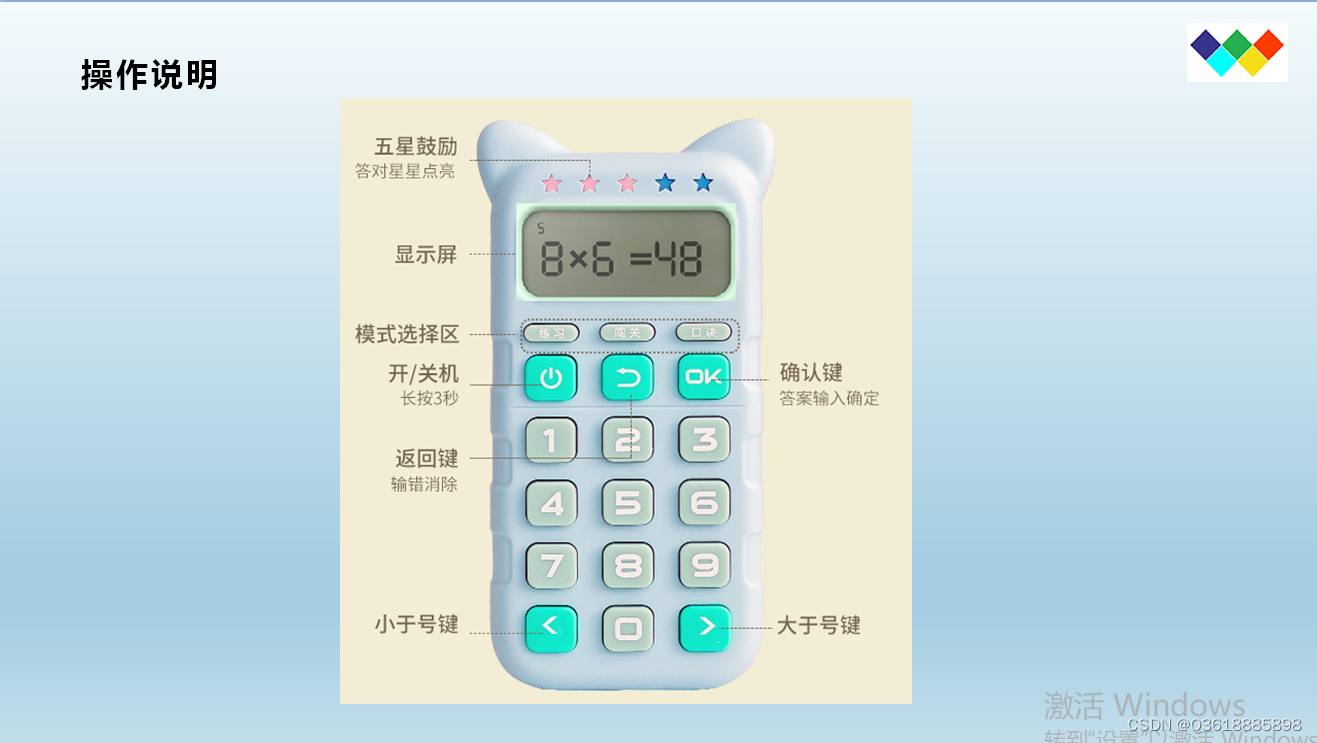
< schematic diagram of oral arithmetic exercise machine program development> oral arithmetic exercise machine / oral arithmetic treasure / children's math treasure / children's calculator LCD LCD driv

Quick analysis: easy to share the Internet

C crystal report printing

Teamtalk source code analysis win client
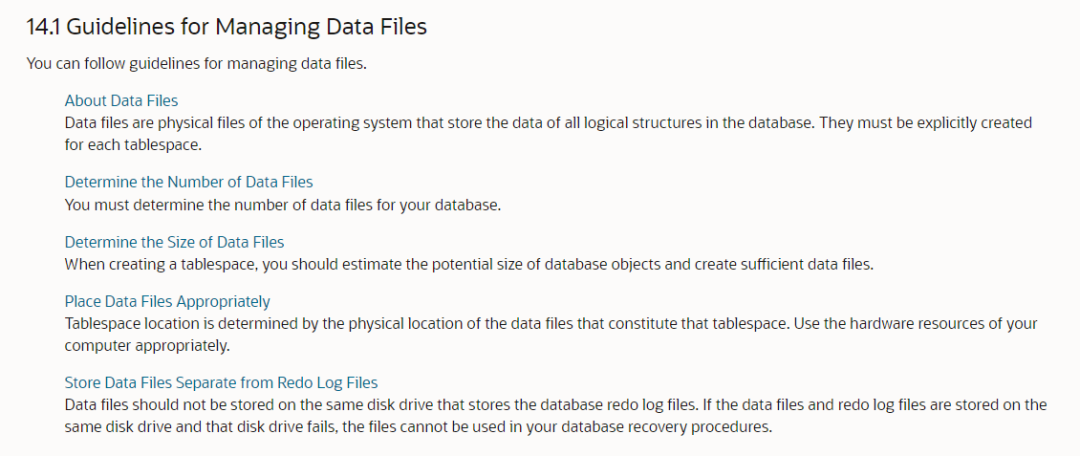
Do you know that there is an upper limit on the size of Oracle data files?
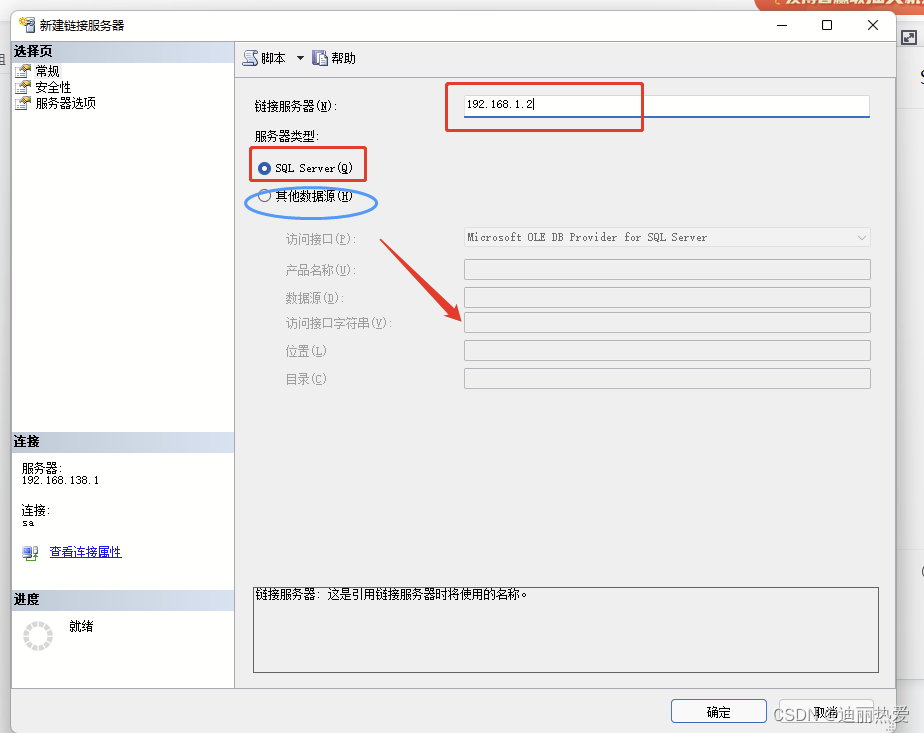
跨服务器数据访问的创建链接服务器方法

ONNX+TensorRT:将预处理操作写入ONNX并完成TRT部署

Yyds dry goods inventory software encryption lock function
随机推荐
Solving the longest subsequence with linear DP -- three questions
Use of freemaker
Data Lake (11): Iceberg table data organization and query
YoloV6训练:训练自己数据集遇到的各种问题
Tujia muniao meituan has a discount match in summer. Will it be fragrant if the threshold is low?
Adhere to the foundation of 20 minutes go every day II
Use of swagger
obsidian安装第三方插件——无法加载插件
Factal: Unsafe repository is owned by someone else Solution
富文本编辑器添加矢量公式(MathType for TinyMCE ,可视化添加)
Federated Search: all requirements in search
OpenHarmony笔记-----------(四)
STM32标准固件库函数名(一)
微信小程序使用towxml显示公式
taobao.trade.memo.add( 对一笔交易添加备注 )接口,淘宝店铺插旗接口,淘宝订单插旗API接口,oAuth2.0接口
Daily learning 3
字符串匹配问题
Makefile separates file names and suffixes
uniapp自动化测试学习
3、函数指针和指针函数