当前位置:网站首页>2021 software security report: open source code, happiness and disaster depend on each other?
2021 software security report: open source code, happiness and disaster depend on each other?
2022-07-02 20:33:00 【Tengyuanhui】
In the near future , A report from a safety testing company shows , The application security situation in the open source field has improved as a whole , But there are still problems , Vulnerabilities including open source code are exploited , And the risks of the third-party code base itself .
The above findings come from Veracode released 《 Software security report ( The first 12 edition )》, The millions of different types of data used in the report come from Veracode Server and client of , And static analysis of these data 、 dynamic analysis 、 Software composition analysis and penetration testing .
PART ONE
Open source code has fewer defects , Faster vulnerability repair
According to the report :「 Open source libraries are still a worrying security factor 」, This is a long-standing , And the hidden danger that continues to this day , The reason lies in the bad habits of developers .
A large number of developers use the same code base year after year , Facts and experience have proved , This will cause us to encounter the same security vulnerabilities year after year
For all that , The report still believes , Third party open source code libraries have many advantages , There are fewer defects , And the problem can be solved faster :
The good news is , Security vulnerabilities caused by third-party code , There is a significant improvement in the timeliness of repair . stay 2017 year , A security vulnerability has never been found , To 50 % The repair point where the defect is solved , It will take more than three years , Now it only takes about a year .
besides , The report also studies the repair process of security vulnerabilities , And the future of security application is prospected :「 On the whole , The application security situation has improved , The impact scope of the vulnerability is also declining .」
meanwhile ,Veracode Also pointed out , The closer the connection between the codes , And the rise of distributed microservices , Makes application security more complex :
「 The reason for this is , In addition to the closer relationship between the codes , There is also the impact of intensified competition and continuous innovation 」. In order to speed up the progress , Many development teams turn to cloud native technology 、 Microservice architecture and open source code to optimize their workflow .
Besides , More and more development teams are adopting agile development , And use automation as much as possible in the development process .
Although this evolution has shortened the software development life cycle , But it also brings new complexities and risks .
PART TWO
More and more people use security scanning
In the report , There are some data worthy of our attention :
- Microservices : stay 2018 year , There are about 20% The application of includes many languages . Now , Only less than 5% Our application uses many languages , More are small 、 Monolingual applications or microservices .
- The number of applications using security scanning has tripled : The average quarterly scan is more than 17 A new application , This figure is more than three times that of ten years .
- More organizations use multiple types of security scanning : stay 2018 to 2021 During the year , The number of users using multiple scanning types has increased 31%, Most of this growth comes from the use of a full set of static 、 Dynamic and SCA Scanned organization .
- Most developers insist on using the same code base year after year : Developers insist on using proven libraries , Rarely willing to try to choose 「 Coolest 」 or 「 The most popular 」 To refactor their code base .
PART THREE
agile development 「 Devour 」 The world
Data based ,Veracode Draw four conclusions :
- small 、 Modular agile development has 「 Devour 」 The world . The number of applications using security scanning has exploded ; Developers have changed from scanning their applications once a quarter to once a day , And use more different scanning techniques .
- Free and open source code will continue to be a blessing and a hidden danger for developers . The use trend of third-party code base has not changed significantly , Code bases with obvious defects are less used , This is very positive .
- The application is slowly developing towards a safer direction . This is the most exciting part of the whole analysis . Although over time , The prevalence of some security vulnerabilities has increased , But the trend is generally downward . Because the ability and speed of vulnerability repair are not necessarily increased , So I hope this trend can continue , The future will also remain bright .
- The emergence of new scanning tools will continue to improve the application security environment . Using different types of security scanning means that developers will be faster 、 Repair all types of defects more completely . These different types of scanning tools are built into the integrated pipeline and IDE in , It will speed up the use of developers .
PART FOUR
Small junction
At the end of the report ,Veracode In conclusion :
Security holes are like bills , Accumulated over time , Settle as soon as possible , It can reduce the workload in the future . Use many types of security scanning —— static state 、 Dynamic or software combination analysis , You can have a more comprehensive understanding of application security , And help speed up 、 Solve security problems more thoroughly .■
English links :App Security Report: Open Source Code Still 'Blessing and a Curse' -- Virtualization Review
Backstage reply key words 「 Software security report 」, You can download the full version of the report PDF.
Tengyuan club is a convergence open source project established by Tencent cloud 、 Open source enthusiasts 、 The open community of open source leaders , Committed to helping open source projects grow healthily 、 Open source enthusiasts can communicate and assist 、 Open source leaders can play leadership value , Make the global open source ecosystem more prosperous .
Welcome to your attention 「 Tengyuan Club 」 official account , Looking forward to your 「 Looking at 」 Oh ~
边栏推荐
- [fluent] dart function (function composition | private function | anonymous function | function summary)
- 【871. 最低加油次数】
- 什么叫在线开户?现在网上开户安全么?
- At compilation environment setup -win
- Google Earth Engine(GEE)——Landsat 9影像全波段影像下载(北京市为例)
- Research Report on the overall scale, major manufacturers, major regions, products and applications of micro hydraulic cylinders in the global market in 2022
- Spark source code compilation, cluster deployment and SBT development environment integration in idea
- AcWing 340. Solution to communication line problem (binary + double ended queue BFS for the shortest circuit)
- What are the preferential account opening policies of securities companies now? Is it actually safe to open an account online?
- After eight years of test experience and interview with 28K company, hematemesis sorted out high-frequency interview questions and answers
猜你喜欢
Jetson XAVIER NX上ResUnet-TensorRT8.2速度與顯存記錄錶(後續不斷補充)
![[internship] solve the problem of too long request parameters](/img/42/413cf867f0cb34eeaf999f654bf02f.png)
[internship] solve the problem of too long request parameters

Why do I have a passion for process?

Complete example of pytorch model saving +does pytorch model saving only save trainable parameters? Yes (+ solution)

AMD's largest transaction ever, the successful acquisition of Xilinx with us $35billion

ROS learning (10): ROS records multiple topic scripts

勵志!大凉山小夥全獎直博!論文致謝看哭網友

【NLP】一文详解生成式文本摘要经典论文Pointer-Generator

JASMINER X4 1U deep disassembly reveals the secret behind high efficiency and power saving
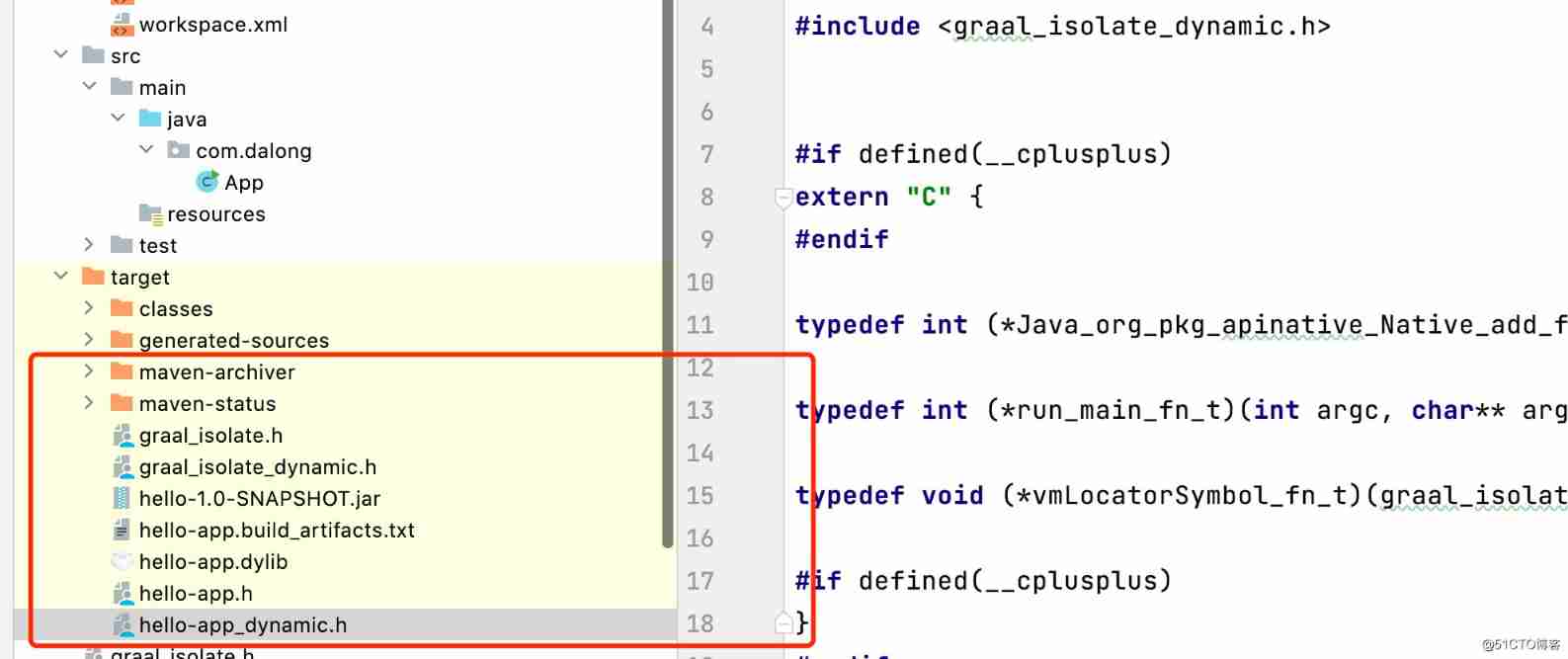
Use graalvm native image to quickly expose jar code as a native shared library
随机推荐
[NLP] a detailed generative text Abstract classic paper pointer generator
Research and Analysis on the current situation of China's clamping device market and forecast report on its development prospect
Spark source code compilation, cluster deployment and SBT development environment integration in idea
API documentation tool knife4j usage details
[cloud native topic -50]:kubesphere cloud Governance - operation - step by step deployment of microservice based business applications - database middleware MySQL microservice deployment process
Sometimes only one line of statements are queried, and the execution is slow
Attack and defense world PWN question: Echo
Cron表达式(七子表达式)
esp32c3 crash分析
Jetson XAVIER NX上ResUnet-TensorRT8.2速度與顯存記錄錶(後續不斷補充)
upload-labs
Google Earth Engine(GEE)——Landsat 9影像全波段影像下载(北京市为例)
[real case] trap of program design - beware of large data
I did a craniotomy experiment: talk about macromolecule coding theory and Lao Wang's fallacy from corpus callosum and frontal leukotomy
【Hot100】22. bracket-generating
After 65 days of closure and control of the epidemic, my home office experience sharing | community essay solicitation
c语言链表--待补充
sql-labs
【871. 最低加油次数】
Codeforces round 651 (Div. 2) (a thinking, B thinking, C game, D dichotomy, e thinking)