当前位置:网站首页>Embedded UC (UNIX System Advanced Programming) -1
Embedded UC (UNIX System Advanced Programming) -1
2022-07-05 17:03:00 【Orange peel does not stop school】
One 、 But first, let me say GCC
We all know , One .c When the document is finished , It needs a series of processing to be executed by the computer , The events that happened are as follows :
Source code (.c)- precompile -> Header files and macro extensions - compile -> Sink code (.s)- assembly -> Object code (.o)- link -> Executable code (a.out)
I believe everyone can basically write the code , Now let's take a look at the code processing
Use the command to simply write a .c file :vi hello.c
You can directly gcc helloworld.c then ./a.out Run directly and get results , But this is too detailed , We are completely unaware of this .c What happened to the file , And when we want to merge multiple tasks later , I don't know where to start .
You can use the following command , To explore the processing of code step by step , And improve it in time .
gcc -E hello.c -o hello.i precompile ( Compile preprocessing )
-o: Output , Followed by a new file generated by output .
-E: Preprocessing options .
Meaning of using this command : Yes hello.c Preprocess the source file , take stdio.h Copy all contents of the file to hello.c in , Or for some defined macros After doing things like macro replacement A new file generated hello.i file .
gcc -S hello.i Get assembly code (hello.s)
-S: Compile high-level language files into assembly language files , namely Will preprocess the output file hello.i Assemble into hello.s file , Generate assembly code , Assembly language can be regarded as a low-level language , Very close to the implementation of machine code , Conversion to machine instructions by assembly process , Assembly process is actually translating assembly language into machine code , The computer can read .
gcc -c hello.s Get the object code (hello.o)
-c: assembly , Translate your own source files into executable programs that the computer can recognize , Assemble the assembly language file of the previous step into a machine language file .
gcc hello.o -o hello Get executable code (hello)
./hello Run executable code
./ Represents... In the current directory
thus , You wrote it. C The language code , Finally, it is transformed into a form that the computer can understand , Then execute the effect of your command .
Here are some commands for development , To avoid some mistakes , And make some assignments
gcc -Wall xxx.c
-Wall: Generate all warnings .
Sometimes you may forget to assign data types to functions , After such a function is written , The compiler may not generate warnings , Because he will add int type .
But in actual development , Such code is extremely unstable , Because the type returned by this function may not be int type , It will lead to big mistakes later , At this point, you need to feed back this warning to you , So that it can be revised in time , So we can use -Wall.
gcc -Werror xxx.c
-Werror: Treat warnings as errors .
Basically the same as , such as , You apply for a local variable in a function, and the function is to return the address of this local variable , But at this time, this local variable has disappeared at the time of function return call , Then a wild pointer will be returned .
Later, it will be very wrong because of this wild pointer , And for this operation , The compiler will only warn , Or will the program be generated , It can also be executed , But the execution result at this time is likely to deviate from the correct result .
use -Werror after , Such warnings will become errors , As a result, the executable file cannot be generated at all , This error must be corrected before it can be generated normally .
gcc -x c++ cpp.c -lstdc++ -o cpp ( Even if the suffix is .c, But because of being designated c++, Will be in accordance with the c++ The rules of )
-x: Specify the language of the source code ( The extension of the file to be executed is ignored , Execute in the specified language )
-O0/O1/O2/O3: Specify the optimization level
O0 No optimization , default O1 Optimize ,O2 Emphasize speed , Sacrifice space ( Big ) Change time ( short ),O3 Emphasize volume , Sacrifice time ( Long ) Change space ( Small )
Two 、 Say the header file
1. Head file guard
for example :
#ifndef __XXX_
#define __XXX_
...
#endif
The effect is to prevent redefinition .
A header file may be contained by multiple source files , The function definitions written in the header file will therefore be extended by the preprocessor to multiple source files containing the header file , And in the compilation stage, it is compiled into many different object files , This will cause link errors :multiple definition, Multiple definitions .
gcc -I< Additional search paths for header files >
This command is used to find header files , such as , You wrote some header files yourself , Such as :#include"my.h", At this time, you can quote , But if you write it carelessly #include<my.h>, You need to specify the path of your header file to the compiler , Otherwise, the compiler will only look for the default path .
Header file , The difference between angle brackets and quotation marks :
#include <my.h>
Look for the -I Specified directory , Then find the system directory .
#include "my.h"
Look for the -I Specified directory , Find the current directory , Finally, find the system directory .
2. Preprocessing instruction
#include - Insert the specified file contents into this directive
#define - Defining macro
#undef - remove macros
#if - If
#ifdef - If the macro is defined
#ifndef - If the macro is undefined
#else - otherwise , And #if/#ifdef/#ifndef In combination with
#elif - Otherwise, if , And #if/#ifdef/#ifndef In combination with
#endif - End judgment , And #if/#ifdef/#ifndef In combination with
#error - Make a mistake , End preprocessing
#warning - Generate a warning , Continue preprocessing
#line - Specify line number
#pragma - Set the state of the compiler or indicate the operation of the compiler
#pragma GCC dependency Dependent files
#pragma GCC poison Grammatical taboos
#pragma pack( Align by a few bytes :1/2/4/8)
#pragma pack() - Align by default bytes The default four byte alignment
Realize self experiment , Need more code experience
3. Predefined macros
There is no need to define , The preprocessor will expand these macros to their corresponding values according to the preset rules .
__BASE_FILE__: The name of the source file being processed
__FILE__: The file name
__LINE__: The line number of the line
__FUNCTION__: The function name of the function
__func__: Same as __FUNCTION__
__DATE__: Processing date
__TIME__: The processing time
__INCLUDE_LEVEL__: Including layers , from 0 Start
8. environment variable
Some data saved in the process to the following : key ( function , What is it? )= value ( Content ).
env
C_INCLUDE_PATH
C Additional search paths for language header files , amount to -I Options .
CPATH
Same as C_INCLUDE_PATH
CPLUS_INCLUDE_PATH
C++ Additional search paths for language header files , amount to -I Options .
LIBRARY_PATH
Link library path
LD_LIBRARY_PATH
Load library path
The next article is about Library , You can understand these first and then continue .
边栏推荐
- Jarvis OJ Webshell分析
- [js] skill simplification if empty judgment
- 中国广电正式推出5G服务,中国移动赶紧推出免费服务挽留用户
- 【机器人坐标系第一讲】
- Wechat official account web page authorization login is so simple
- Benji Bananas 会员通行证持有人第二季奖励活动更新一览
- Learnopongl notes (I)
- The difference between searching forward index and inverted index
- Get ready for the pre-season card game MotoGP ignition champions!
- 【 brosser le titre 】 chemise culturelle de l'usine d'oies
猜你喜欢

Global Data Center released DC brain system, enabling intelligent operation and management through science and technology
Basic introduction to the control of the row component displaying its children in the horizontal array (tutorial includes source code)
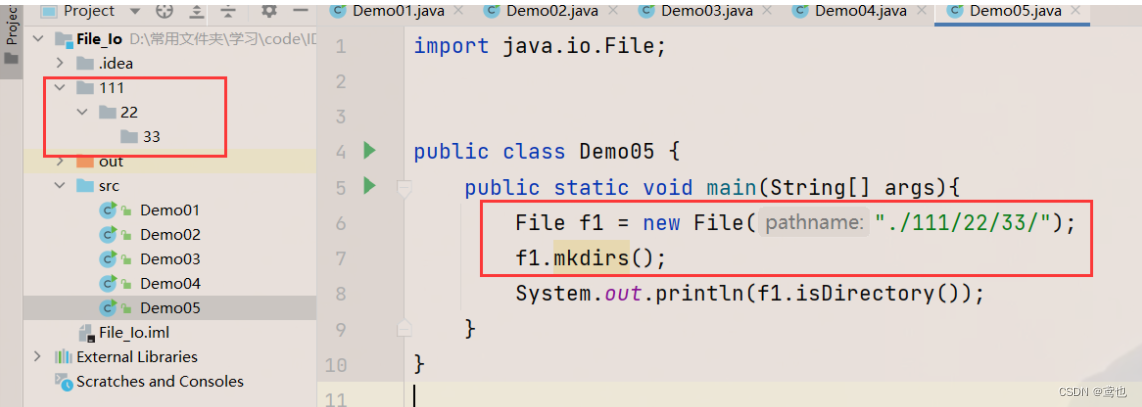
File operation --i/o

采用药丸屏的iPhone14或引发中国消费者的热烈抢购
Hiengine: comparable to the local cloud native memory database engine

国产芯片产业链两条路齐头并进,ASML真慌了而大举加大合作力度
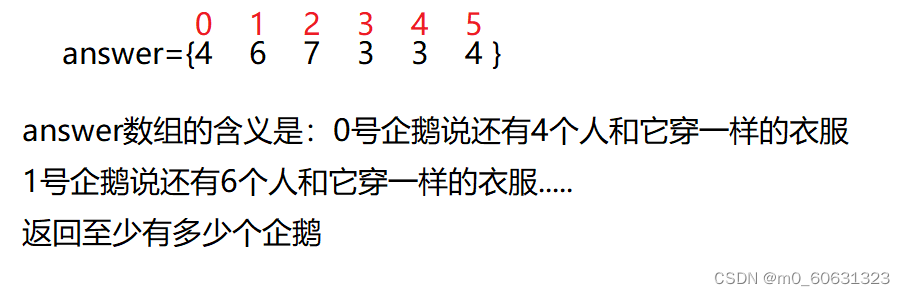
【刷題篇】鹅廠文化衫問題
Benji Bananas 会员通行证持有人第二季奖励活动更新一览
Enter a command with the keyboard
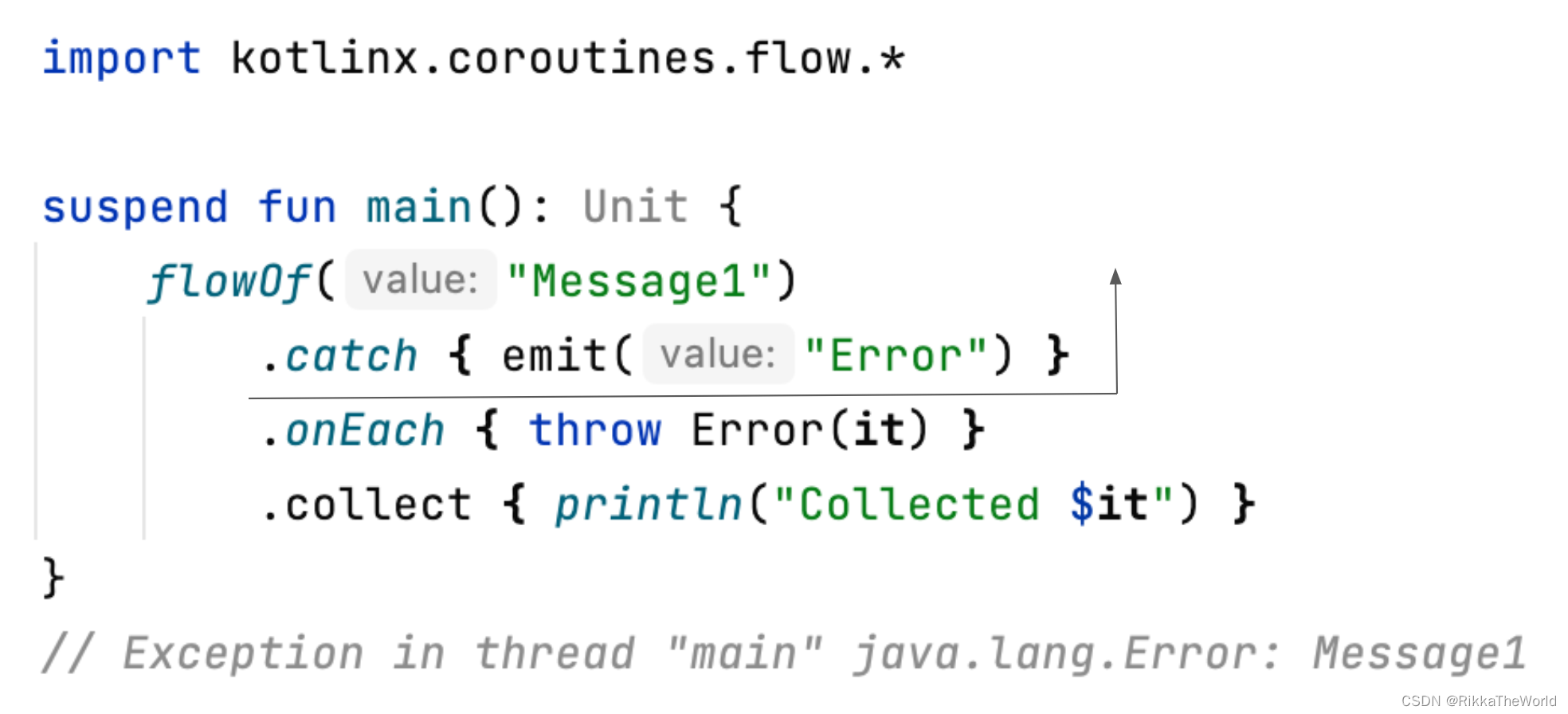
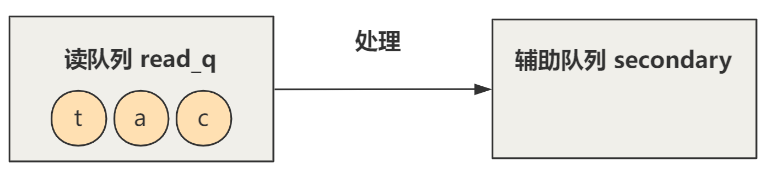
Deep dive kotlin synergy (XXI): flow life cycle function
随机推荐
American chips are no longer proud, and Chinese chips have successfully won the first place in emerging fields
Sentinel-流量防卫兵
Do sqlserver have any requirements for database performance when doing CDC
[Jianzhi offer] 62 The last remaining number in the circle
什么是ROM
Jarvis OJ shell traffic analysis
[brush title] goose factory shirt problem
How can C TCP set heartbeat packets to be elegant?
深潜Kotlin协程(二十一):Flow 生命周期函数
如何安装mysql
【testlink】TestLink1.9.18常见问题解决方法
[wechat applet] read the life cycle and route jump of the applet
Browser rendering principle and rearrangement and redrawing
帮忙看看是什么问题可以吗?[ERROR] Could not execute SQL stateme
Summary of PHP pseudo protocol of cisp-pte
DenseNet
How does win11 change icons for applications? Win11 method of changing icons for applications
国内首家 EMQ 加入亚马逊云科技「初创加速-全球合作伙伴网络计划」
Timestamp strtotime the day before or after the date
Allusions of King Xuan of Qi Dynasty